Multiple clients on same VPN IP?
-
I am playing around with having both of my iOS devices (an iPhone and an iPad) connect to my OpenVPN via the OpenVPN Connect client app.
I did not expect both clients to report the same private IP:
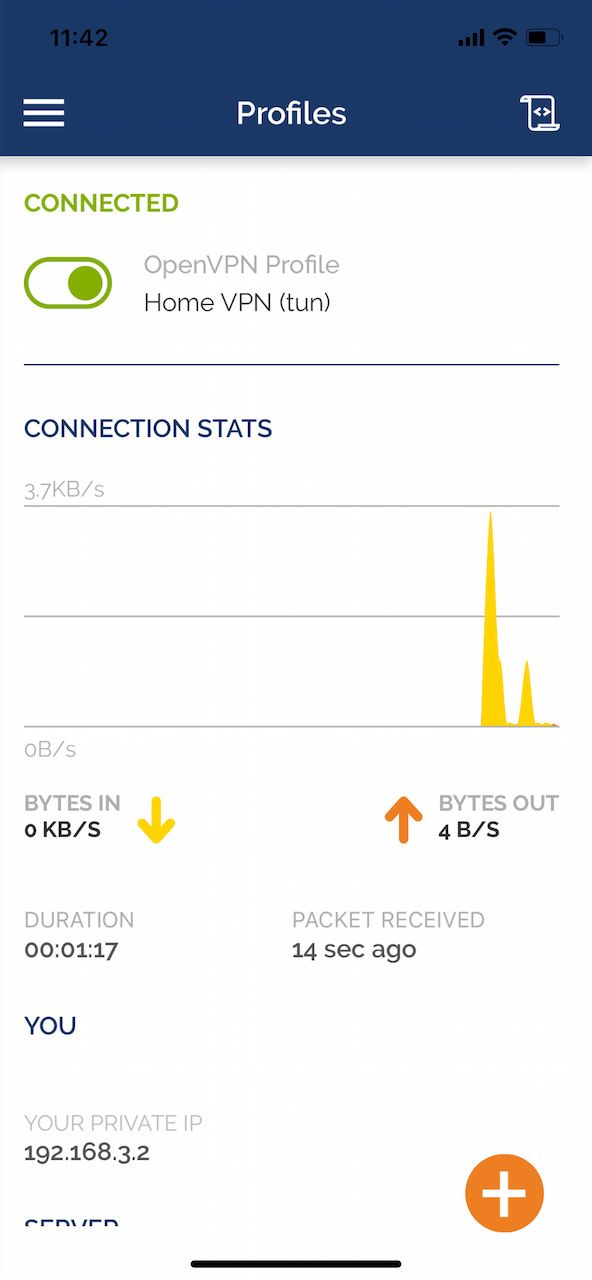

Both are at 192.168.3.2. Are these spoofed, only local, IP addresses? I guess, I don’t fully understand how OpenVPN works.
-
Assuming they're both connected at the same time, they should have different addresses. Otherwise, neither will work. When you set up OpenVPN, you provide a network for remote users and can specify how many are allowed to connect. Perhaps you could show your OpenVPN config.
-
Here is the client config file:
persist-tun persist-key data-ciphers AES-128-GCM:AES-256-CBC data-ciphers-fallback AES-256-CBC auth SHA256 tls-client client remote ***.***.***.*** 1194 udp4 verify-x509-name "server" name remote-cert-tls server compress explicit-exit-notify <ca> -----BEGIN CERTIFICATE----- (…) -----END CERTIFICATE----- </ca> <cert> -----BEGIN CERTIFICATE----- (…) -----END CERTIFICATE----- </cert> <key> -----BEGIN PRIVATE KEY----- (…) -----END PRIVATE KEY----- </key>And the server config:
ovpn dev ovpns2 verb 1 dev-type tun dev-node /dev/tun2 writepid /var/run/openvpn_server2.pid #user nobody #group nobody script-security 3 daemon keepalive 10 60 ping-timer-rem persist-tun persist-key proto udp4 auth SHA256 up /usr/local/sbin/ovpn-linkup down /usr/local/sbin/ovpn-linkdown local ***.***.***.*** tls-server server 192.168.3.0 255.255.255.0 client-config-dir /var/etc/openvpn/server2/csc tls-verify "/usr/local/sbin/ovpn_auth_verify tls 'server' 1" lport 1194 management /var/etc/openvpn/server2/sock unix max-clients 3 push "route 192.168.1.0 255.255.255.0" push "route 192.168.2.0 255.255.255.0" push "route 192.168.4.0 255.255.255.0" push "dhcp-option DOMAIN hoffmann.homeunix.net" push "dhcp-option DNS 192.168.3.1" client-to-client capath /var/etc/openvpn/server2/ca cert /var/etc/openvpn/server2/cert key /var/etc/openvpn/server2/key dh /etc/dh-parameters.2048 data-ciphers AES-128-GCM:AES-256-CBC data-ciphers-fallback AES-256-CBC allow-compression asym compress persist-remote-ip float topology subnetI do not see a hard-coded 192.168.3.2 anywhere.
-
@dominikhoffmann
Ensure that you use a different SSL certificate on each client. -
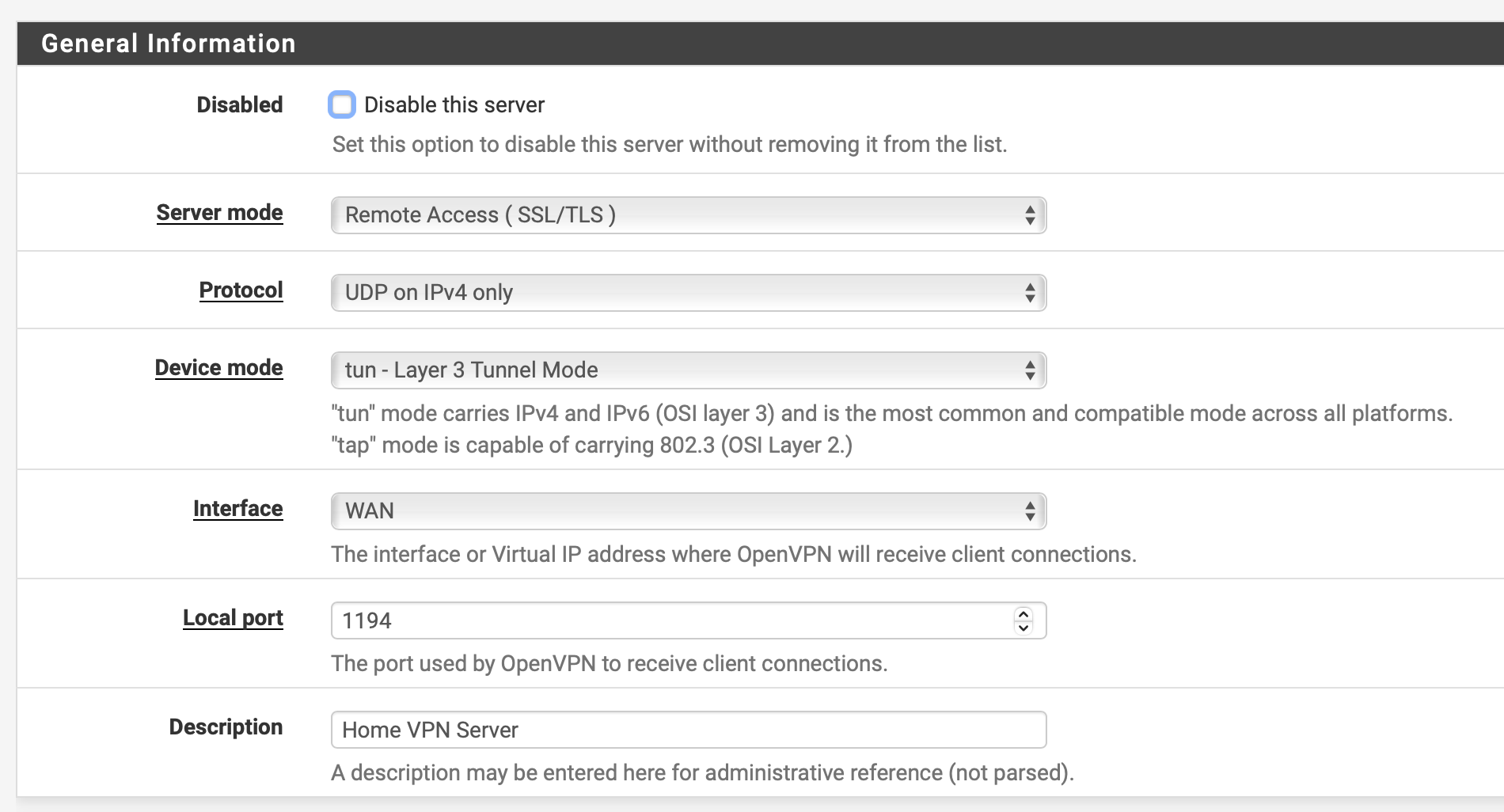
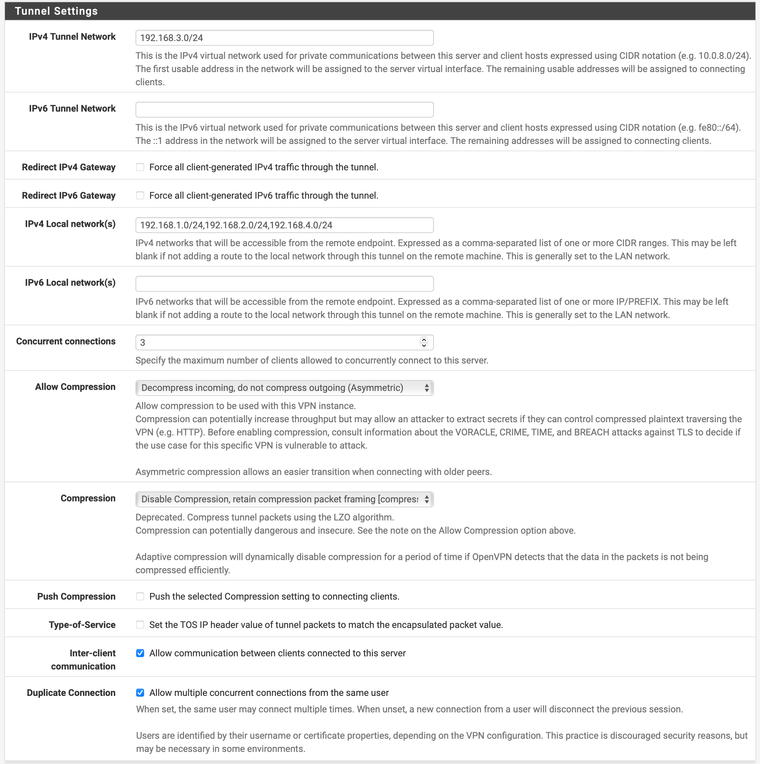
I was thinking screen shots of the area where you configure your VPN network on the server page.
-
-
Are you connecting these devices at the same time ??
I'd expect the asigned client ip address to be returned to the "pool" , a bit after the client has disconected from the server./Bingo
-
@bingo600 said in Multiple clients on same VPN IP?:
Are you connecting these devices at the same time ??
Yes, those screenshots in the original post are concurrent.
-
I turned on the “Allow multiple concurrent connections from the same user” option only after the original post in this thread. With that checked, two concurrent clients using the same certificates get distinct IP addresses.
That option turns on a configuration line in
/var/etc/openvpn/server*that says
duplicate-cnA post on ServerFault had pointed me in that direction.