Block no log multicast noise on WAN
-
Hello,
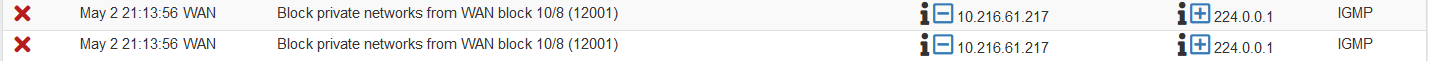
since I changed my ISP last week, there is a lot of noise on the WAN. Every 30 sec. there is a IGMP v2 query form IP 10.216.61.217 > 224.0.0.1
My internal network is 192.168.0.0 and my WAN IP is DHCP provided - 94.155.x.x. So that host of type 10.x.x.x is something living in the ISP's segment above me. Do not know anything about it.
19:49:25.890571 80:fb:06:d6:ea:0d > 01:00:5e:00:00:01, ethertype IPv4 (0x0800), length 60: (tos 0xc0, ttl 1, id 7516, offset 0, flags [DF], proto IGMP (2), length 32, options (RA)) 10.216.61.217 > 224.0.0.1: igmp query v2I do not want so much spam in my firewall log, so I tried to block it with no log, with hope that spam will stop.

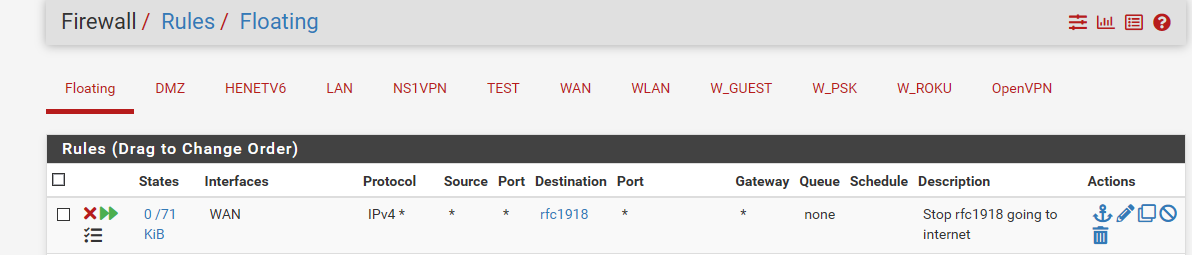
After couple of unsuccessful attempts, while thinking on the issue, I came to the idea that the default WAN block rule for RFC1918 network ranges is already blocking this address (10.216.61.217),
but it is logging it!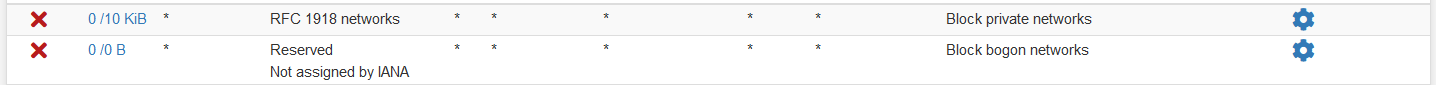
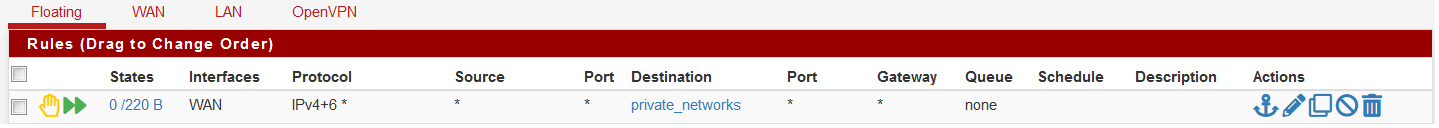
So, I tried to create my own RFC1918 networks alias, a blocking rule and after that to disable the default WAN rule. I was hoping that way I'll have the option to say "do not log these garbage please!"
Surprisingly that didn't work at all - same multicast query continues to pop up at my log every 30 seconds sharp.I am out of ideas right now...How to deal with that spam generator? :)
-
if you want to create your own rfc1918 rule, you would hae to disable the auto rule. Floating doesn't go in front of those rules.
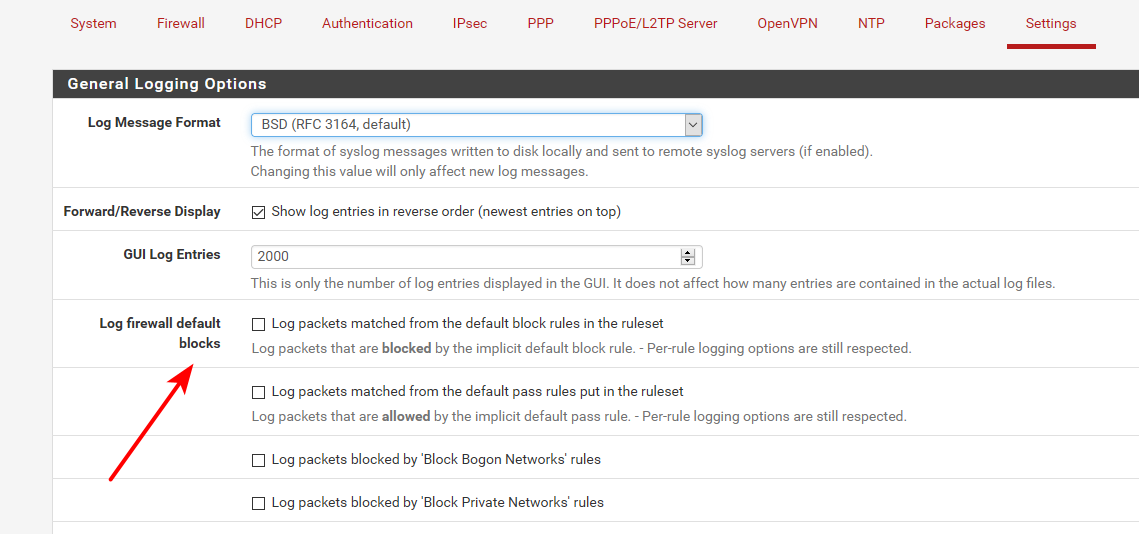
You could just tell the rfc1918 and bogon rules not to log ;)
And sure wouldn't want a reject rule!! You would want inbound and not log.. And just drop. And the source would be rfc1918, not the destination.
BTW - what version of pfsense are you running - that gui looks pretty dated..
-
Oh, come on...that's a bit embarrassing, I should've seen that option :))) Thank you so much - it worked like a charm of course! Thanks for the prompt reply!
The Pfsense version is 2.5.1-RELEASE but it is the Compact-Red web config theme. Personally, I find it very suitable for bigger screens. The red color is a bit irritating so I am planning to work on the CSS someday...before Christmas :)
All Best,
NG -
And sure wouldn't want a reject rule!! You would want inbound and not log.. And just drop. And the source would be rfc1918, not the destination.
btw, I am reading this: [https://docs.netgate.com/pfsense/en/latest/recipes/rfc1918-egress.html](link url)
and it's saying basically that blocking out RFC1918 brings some benefits. I have a openvpn site-to-site config and I was wondering if blocking in and out would be beneficial at the end.
I am asking since you mention I need inbound, so I am wondering if there are some other considerations to do in this case? -
You can block outbound if you want.. But that wouldn't of stopped it from showing up in your logs. Was my point trying to make.
I block outbound rfc1918.. But just to be a good netizen, nothing more.. There really should never be any hits on it.. Unless you tried to go to some rfc1918 address, that did not exist on your local network... If pfsense has no route to where your trying to go, then it would send it out your default route, ie your isp. Your isp not going to be able to route some rfc1918 address anywhere, other then their own internal network, etc.
Really the only reason you see hits on that - is there was a thread around here I do believe, or maybe it was over on reddit? Where someone was trying to figure out why he was seeing logs to some like 10.x.8 address.. So I using that rule showed him how it would log, and how to track down what was creating the traffic via the state table. Before that is was 0/0
He had created a sim rule - but didn't bother to label it or show his rule descriptions in his firewall log.. He had his work laptop trying to talk to some work hard coded IP for antivirus updates or something..
-
I see...thank you for guiding me through this, I learned a lot today :)
Created custom RFC1918 blocking alias/rule, no logging, only inbound, block/drop instead of reject, source - RFC1918.
Everything seems to be fine - no more multicast spam at the logs! -
If you notice from my screenshot I have all the default logging of - I have my own clean rules that only log what I want to see.. I only log traffic to tcp that is syn. And only some well known udp ports.
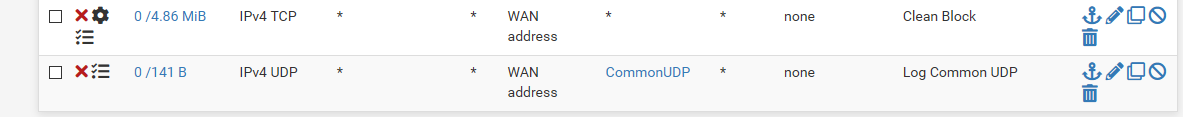
For lan side, I log the stuff I want as well. But if troubleshooting something not work for example - its just a click to turn on default deny logging..
This cuts way down on log spam, and lets me see just the stuff that is interesting to me.
There is a lot of noise out there - that just doesn't interest me to fill up my logs with. I know its blocked, but no need to log all the noise.
-
I really appreciate the insides you gave me here. You need to write a guides or something :)
I'll have to sit down and read more in order to create my own aliases, rules and the required logging as well.
The practical point of view says that I am not a pro and pfsense is just working for me. But there is another strong point - I am thereby curious and willing to learn, even though I know it going to be a lot of time/research.Best,
NG