PfBlockerNG GEOIP for open ports.
-
@nogbadthebad,
Thanks for the input and i agree that VPN is a better alternative for most cases but it's not the right solution for every environment.For instance, we host a cloud service which we use to distribute big files with customers via public links shared via email.
Implementing a VPN for our cloud service would be impractical as it would involve creating VPN users for each customer, explain them how to install a VPN client on their system and only then they could access our cloud service. As you can see this is just not achievable on a day by day operation with non-recurrent clients and defeats the purpose of having a cloud to begin with.
In any event, i tried to do what you did for your SSH service as follows:
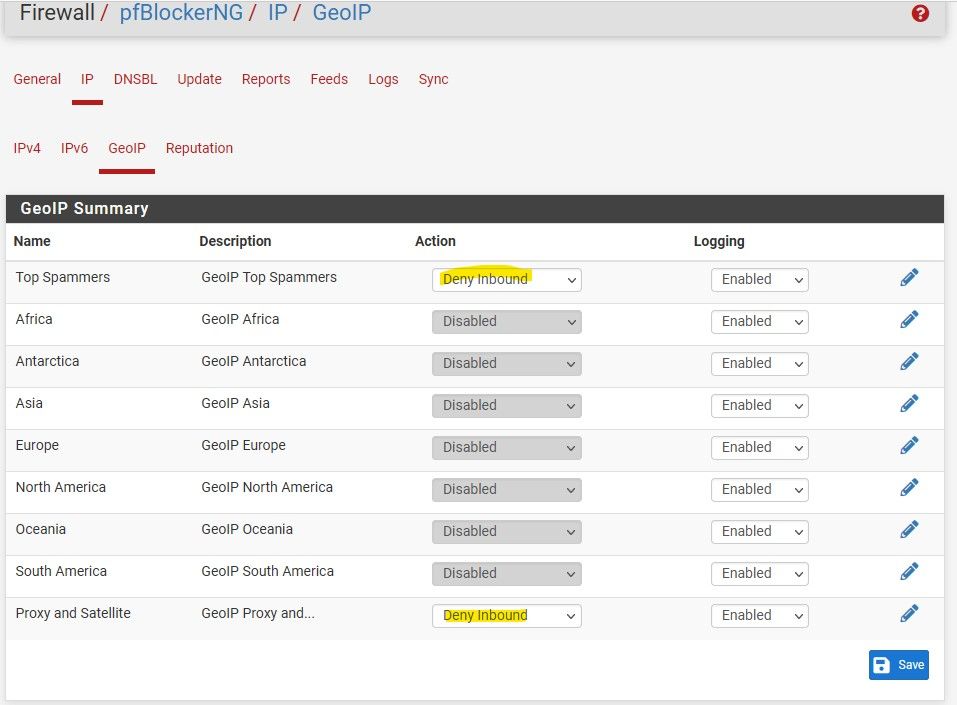
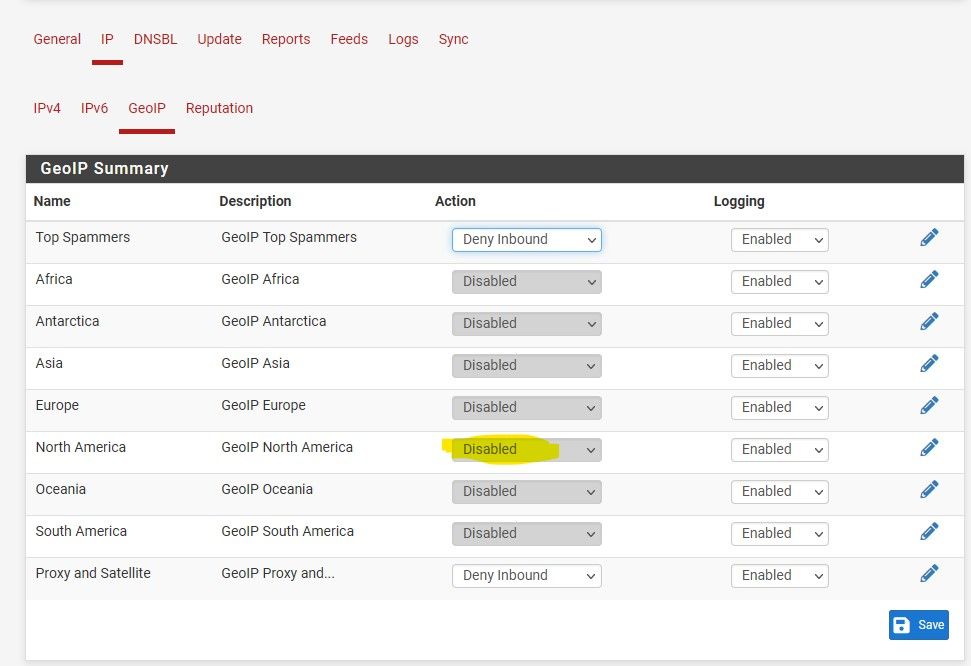
1- I disabled all the previous GEOIP lists, except for the Top spammets and the Proxy one.
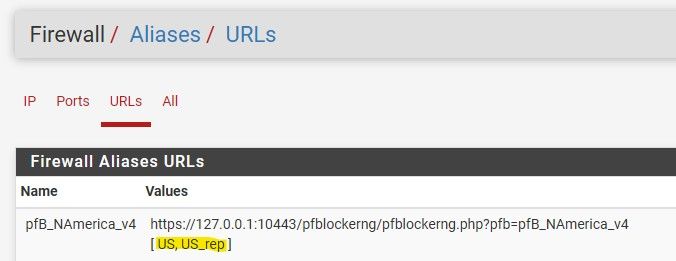
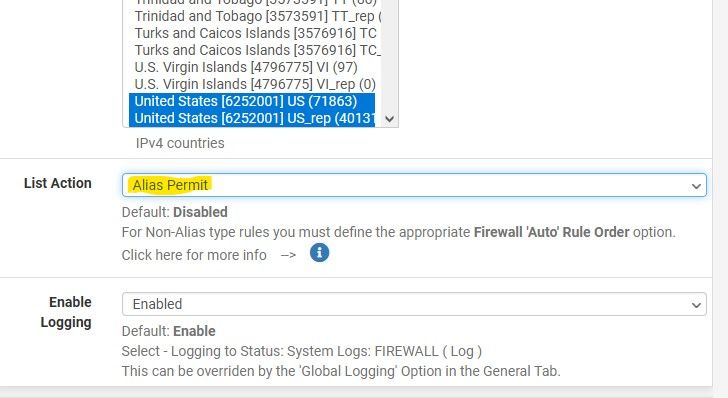
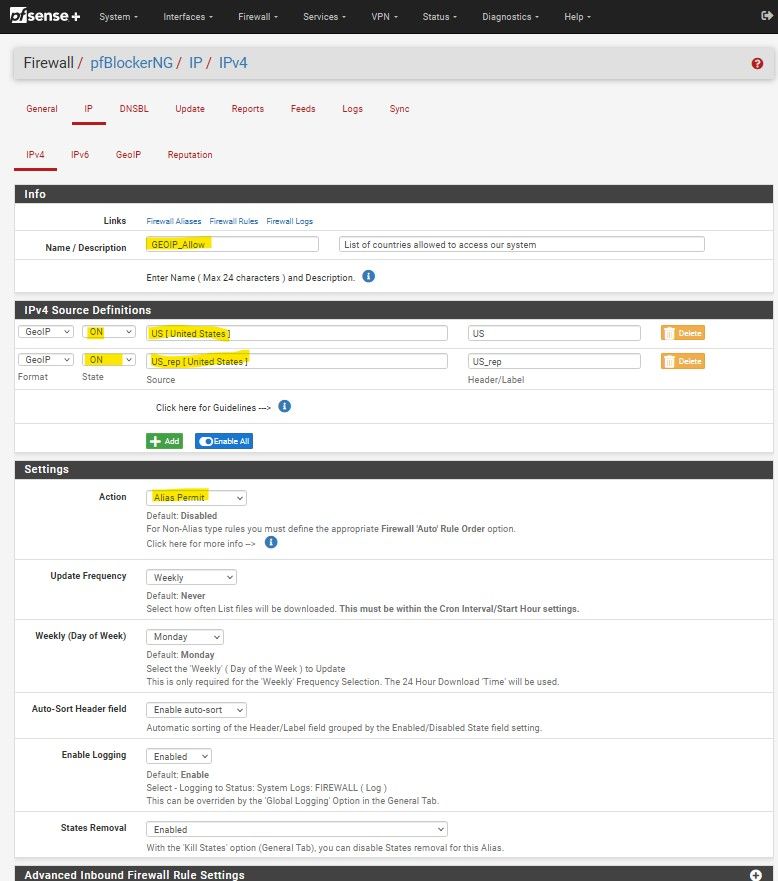
2- I went to Firewall-->PFBlocker-->IP-->IPv4 and created a new list named “GEOIP_Allow” which hat the 2 GEOIP entries for the US, defined their state as “ON” and selected “Alias Permit” as the action drop down setting.
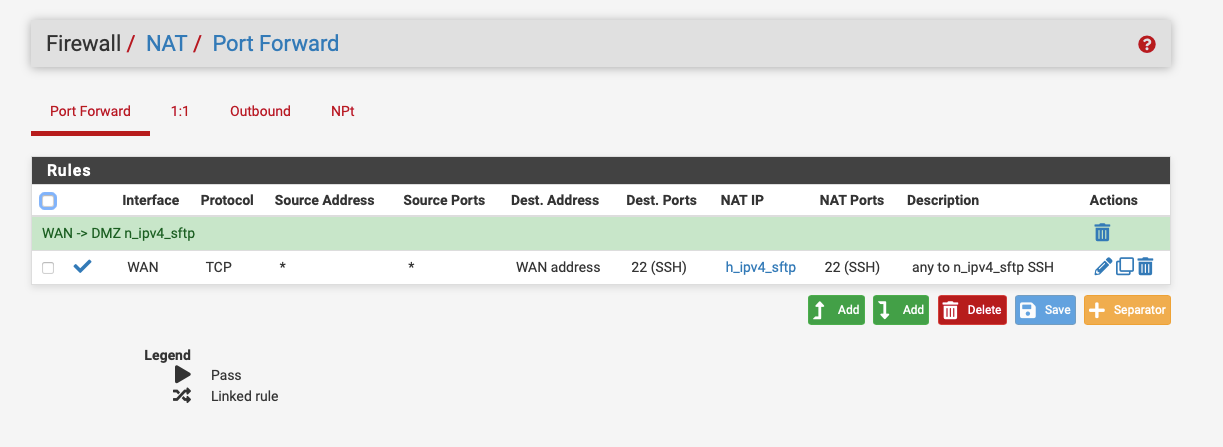
3- Then, Firewall-->PFblocker-->Update-->Reload-->IP4- Then, i changed my rules to use the new “GEOIP Allow” list as the source
And...... no access. No clue why it’s working for you and not for me but here we are.
I'm open to any other ideas.
-
@lrossi You are NATing aren't you, your rules mention it.
Try doing a packet capture on the WAN then the LAN interface and see where the traffic is stopping.
-
I think i solved this but i would like to know your opinion.
Analysis of the problem
PfSense blocks all unrequested incoming traffic unless we setup a specific rules allowing such traffic.This is why everyone recommends that when using GEOIP, instead of blocking the world, it is best to implement a “Pass” rule to allow the incoming connections only from the countries that we expect to receive traffic.
However, by opening ports i’m bypassing such default behavior and allowing all incoming connections to the open ports. A passing rule, say for the US, will not necessarily block traffic from Russia since the default block was overridden by the NAT rule.
Solution #1 (Failed)
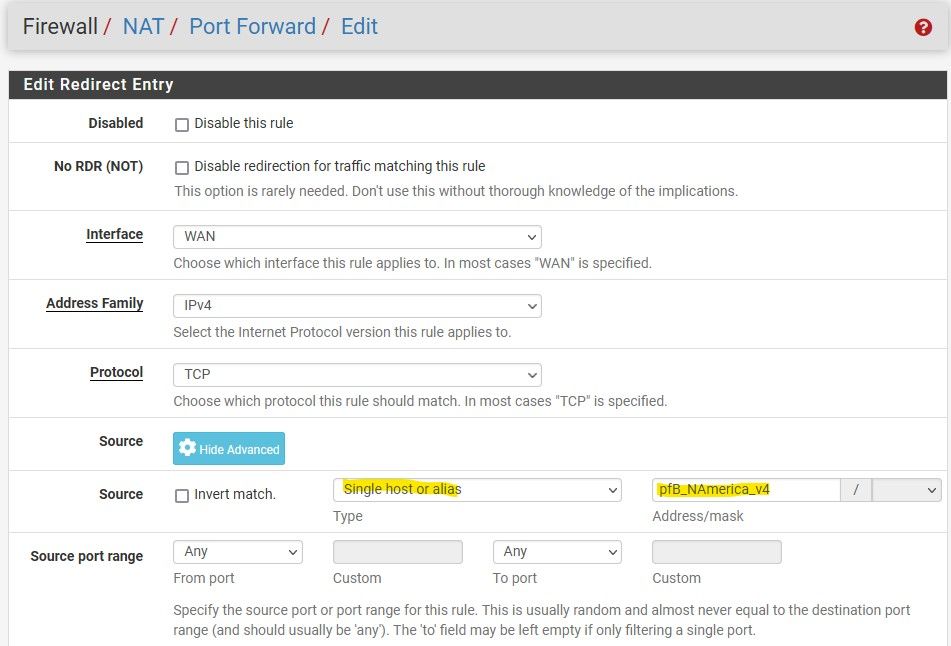
The solution i wanted to implement was to create an alias in PFBLockerNG with just the countries i want to allow and use that as the source for my port forward rules, but for some reason that solution completely blocked access to that port (i have no clue why).Solution #2
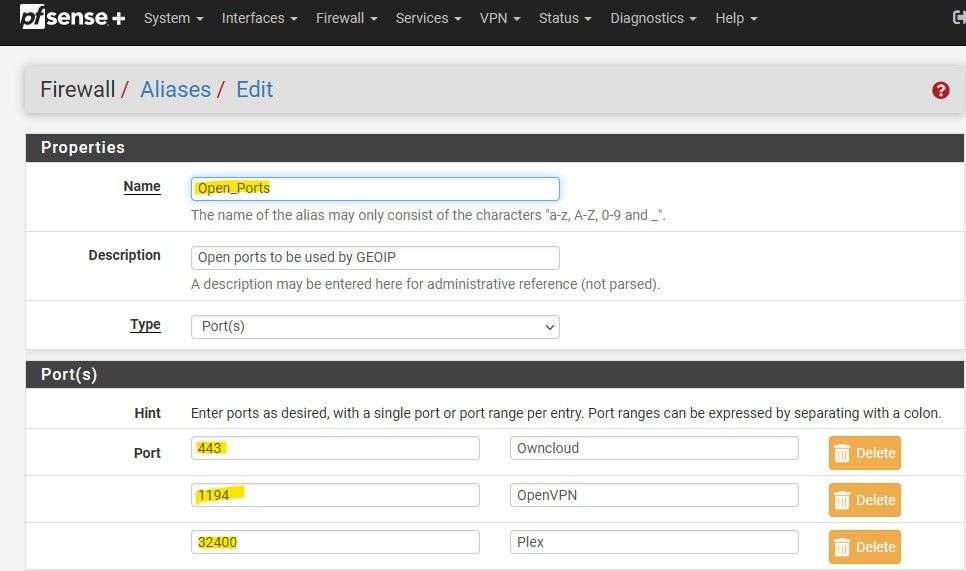
I went back to pfblockerNG and created an IPv4 list of allowed countries with an action “Alias Native”.
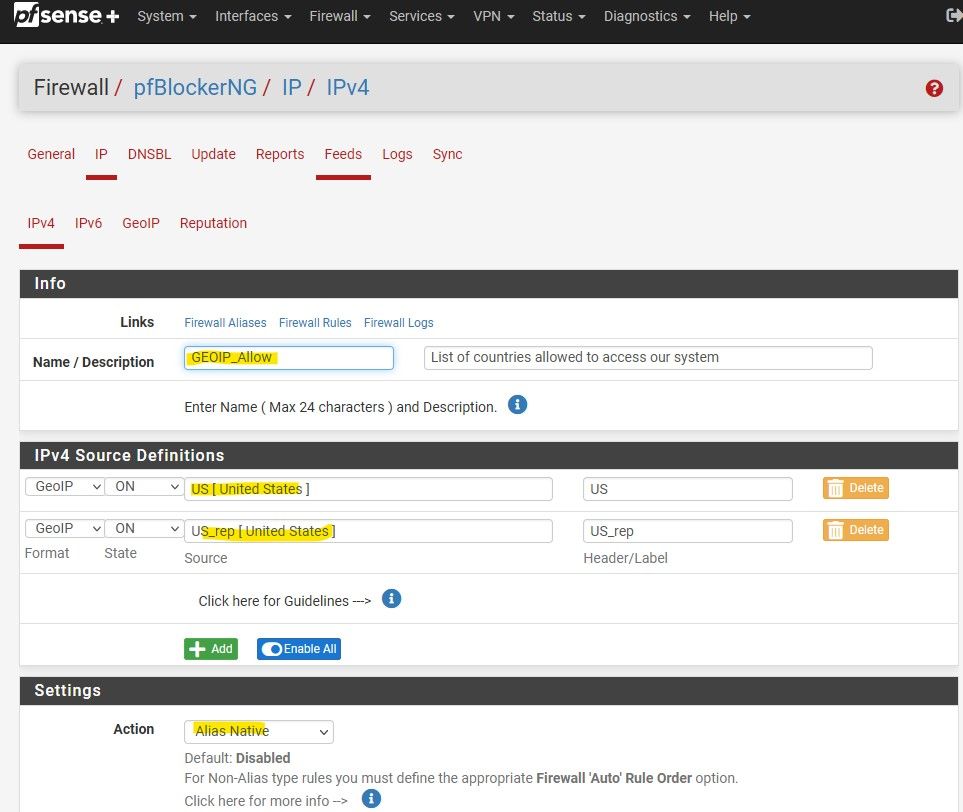
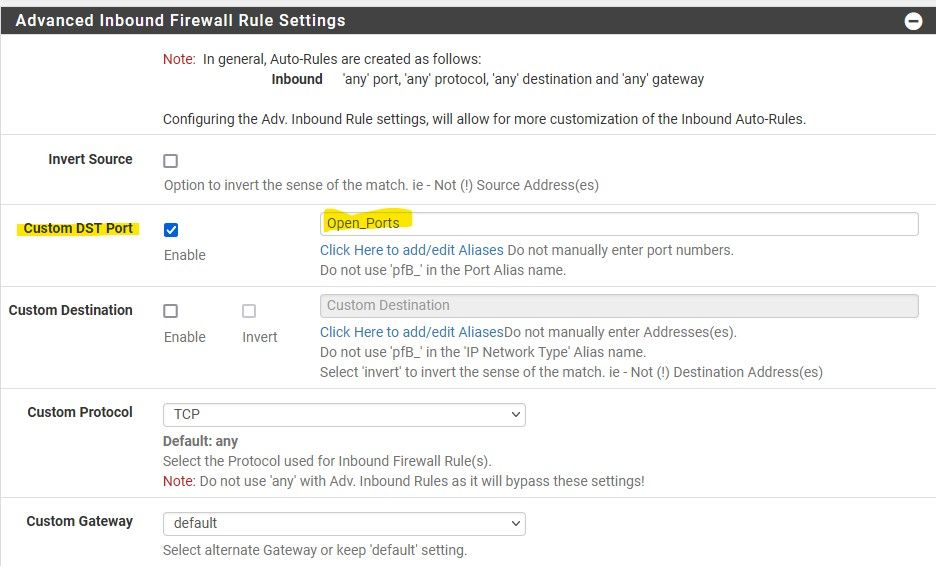
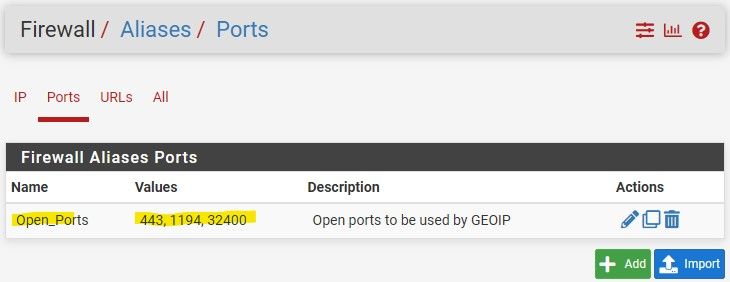
I also limited these countries to connect only to the specific ports that were opened via a new alias called Open_Ports.
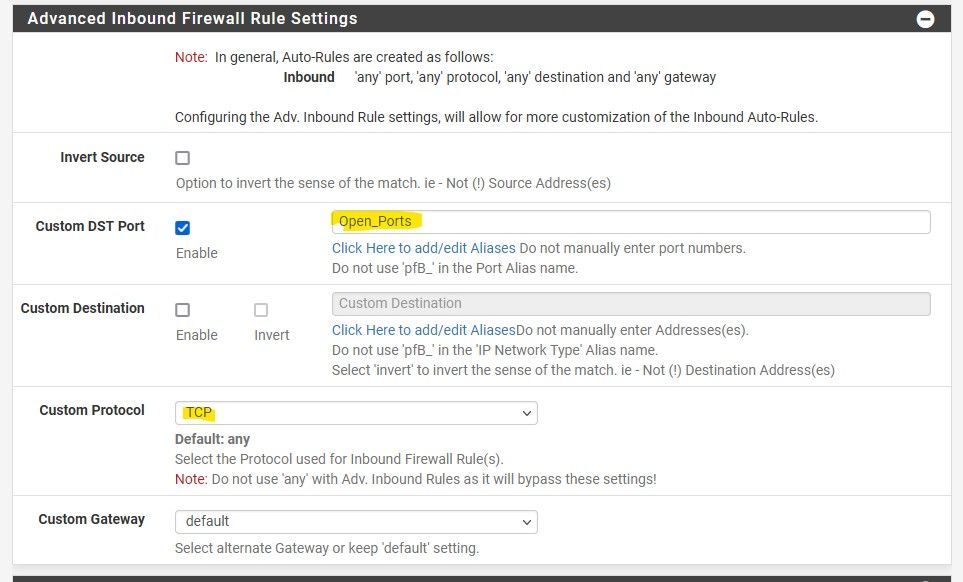
Then i created a new blocking rule and used the “Allowed_countries” alias as the source. This sounds counterintuitive since by default this would block incoming connections from the countries in that list (which are the ones i actually want).
So I checked the “invert match” option. Now the rule should block ALL incoming connections EXCEPT for the ones in the “GEOIP_Allow” lists.
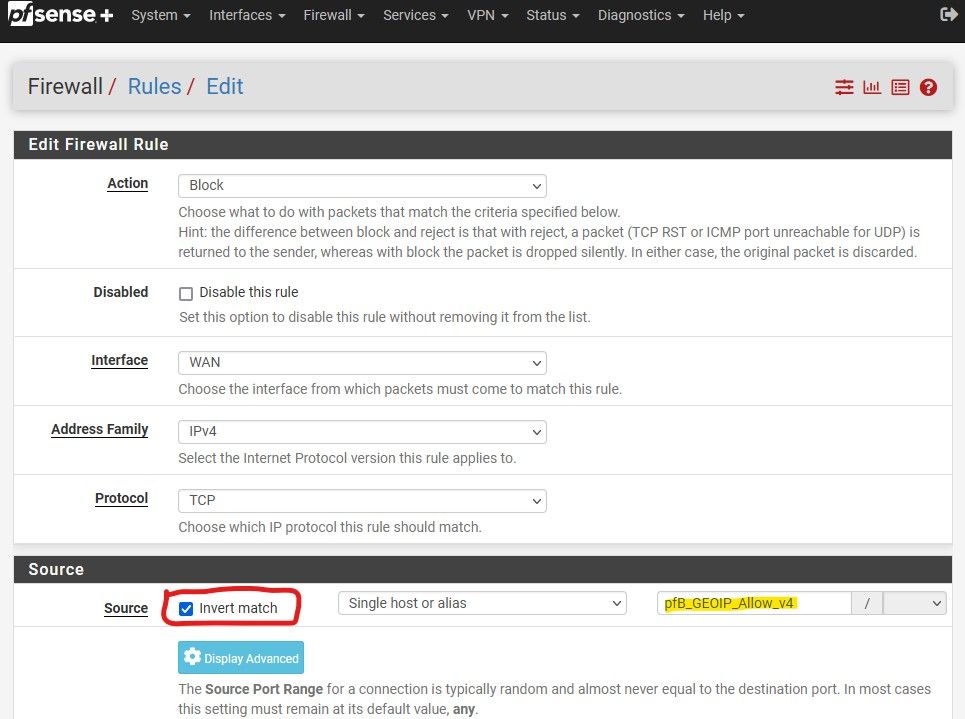
Since pfsense process rules from top to bottom, i placed this block rule on top of my NATing rules.
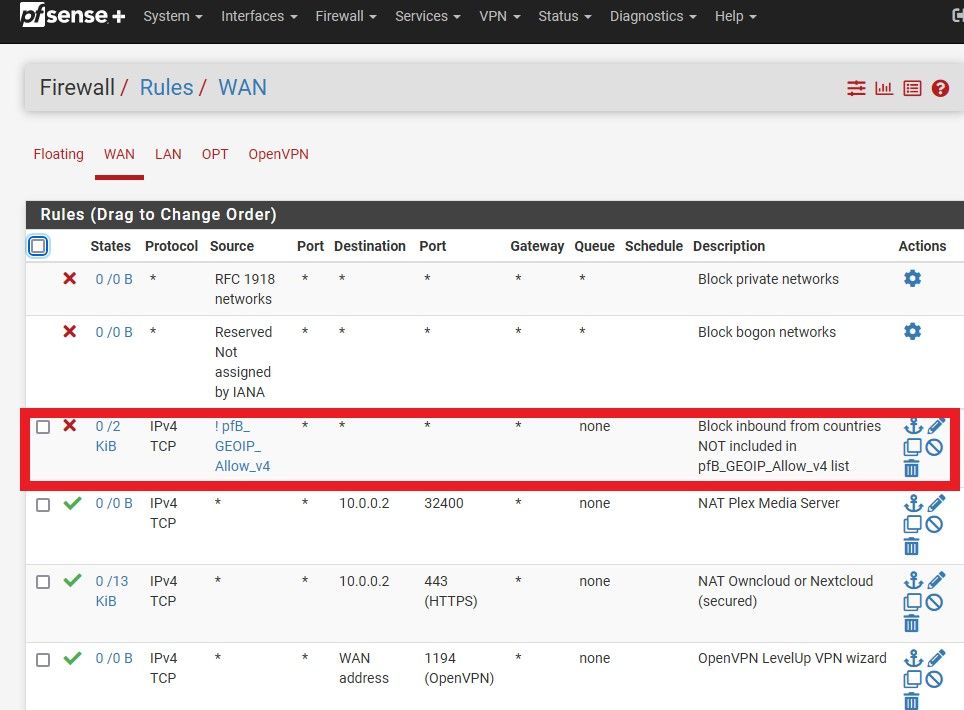
Now, logic tells me that this should work. Question is, how do i test that PFsense is indeed blocking traffic from outside the US?
Opinions? comments? suggestions?
-
@lrossi search the internet for a non us port scanner.
-
Not sure why you think this is so complicated. If you only want to allow countries xyz into your port forward.
Then only allow that alias you created in pfblocker, as source in your port forward..
There is nothing more too it.
There is no need for ! rules blocking above..
-
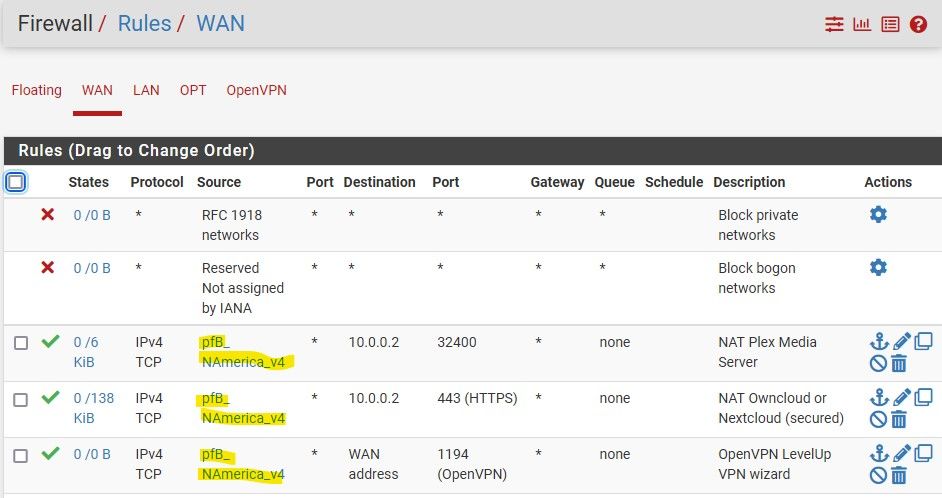
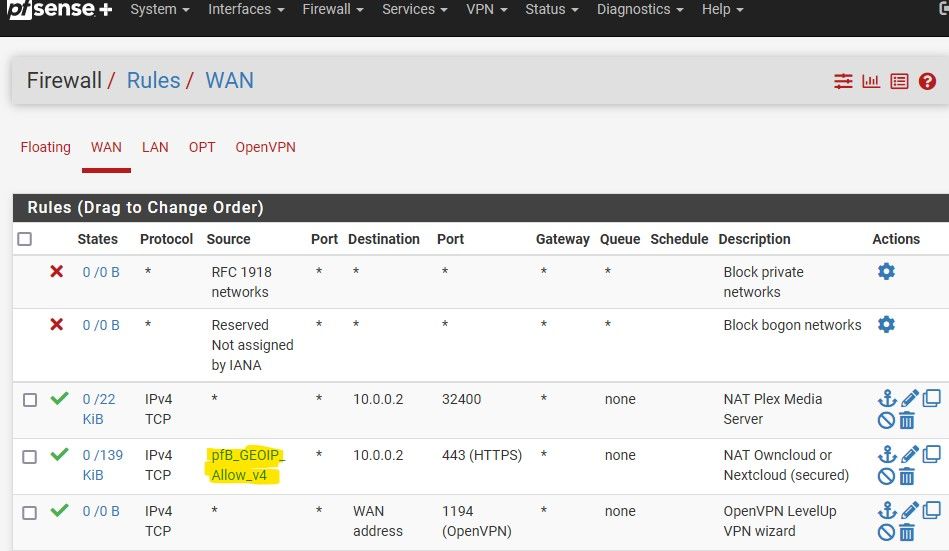
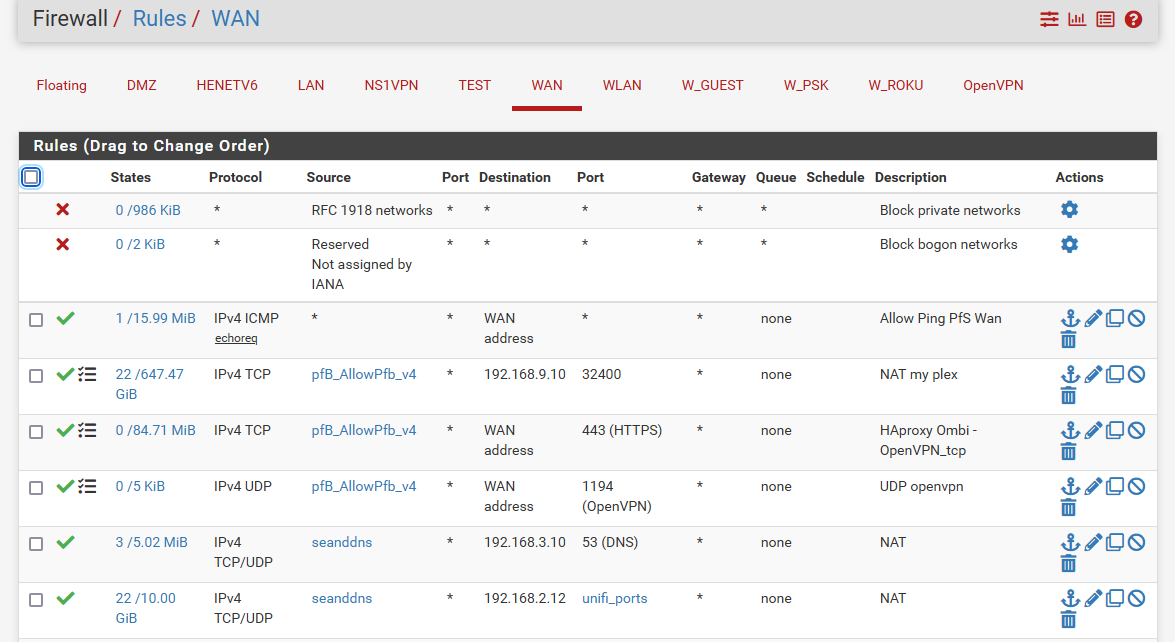
@johnpoz , your suggestion is more straight forward simple and elegant but when i try to implement it I just cannot access my services. This is how my rules looked when i tried:
I don't understand why that didn't work.
But then the advisement from @NogBadTheBad made me think that maybe my problem is that services were not accessible from within my network but they are from outside.
So i went to https://www.whatsmyip.org/port-scanner/ to do a port scan and it confirmed that my ports were indeed accessible from outside my network.
So, this is the situation, when i put the list of allowed countries as the source for my NAT rules, i cannot access my services from within the network. When i set that source to "any" and i create a block rule as described in my previous post, then my services are accessible from inside and outside the network.
Ideas? suggestions? on how to use my list of allowed countries as the source for my NAT rules AND have those ports available to clients within the LAN?
-
@lrossi said in PfBlockerNG GEOIP for open ports.:
i cannot access my services from within the network
Well that really has nothing to do with what is allowed or not allowed really - you can have that issue with wide open rules. You either need to setup nat reflection or setup just local dns resolution to your services.
Your plex server for example should always just hit its local IP..
-
@johnpoz, your comment made me check what i had set for NAT reflection in my NAT rules. They were set to “Use system defaults”.
The system defaults in System--> Advanced --> Firewall & NAT--> NAT Reflection mode for port forwards, was already set to “Pure NAT”.
OK, this should work now. I went back to my NAT rules and set them to use my “GEOIP_Allow” countries list as their source. Clicked save and apply changes and, just like before, my services were available to the world but not from within the LAN.
So, i went to the PFSense documentation to learn more about NAT reflection and, in there, i saw that they recommend to use a split DNS entry instead of NAT reflection. I followed their instructions and set up a Host override pointing my DDNS URL to the local LAN IP of the machine serving the services on the forwarded ports.
Like magic, everything worked.
Thank you so much to you and @NogBadTheBad for helping me identify that my GEOIP blocking problem was actually a DNS problem.
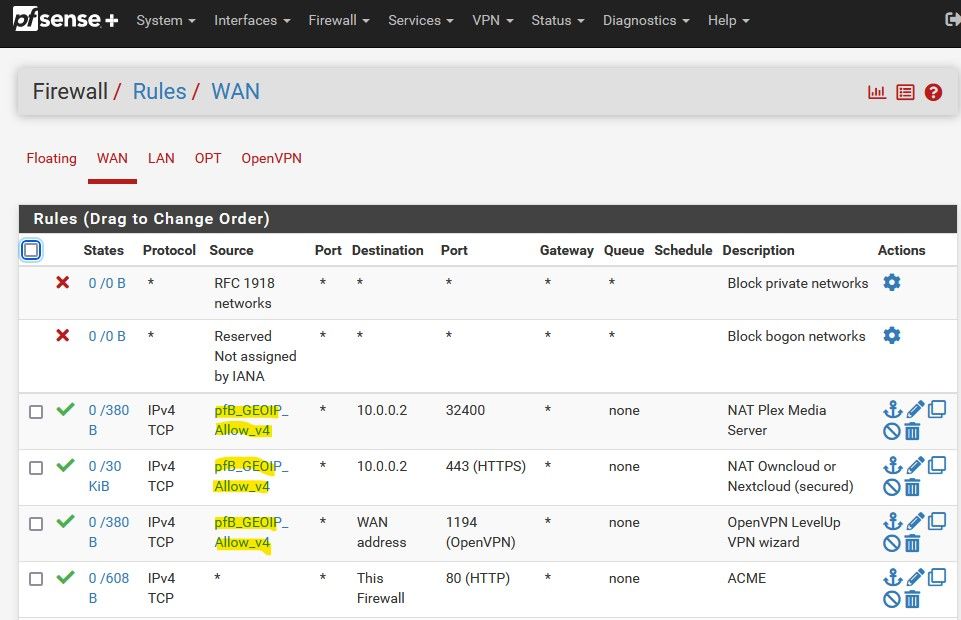
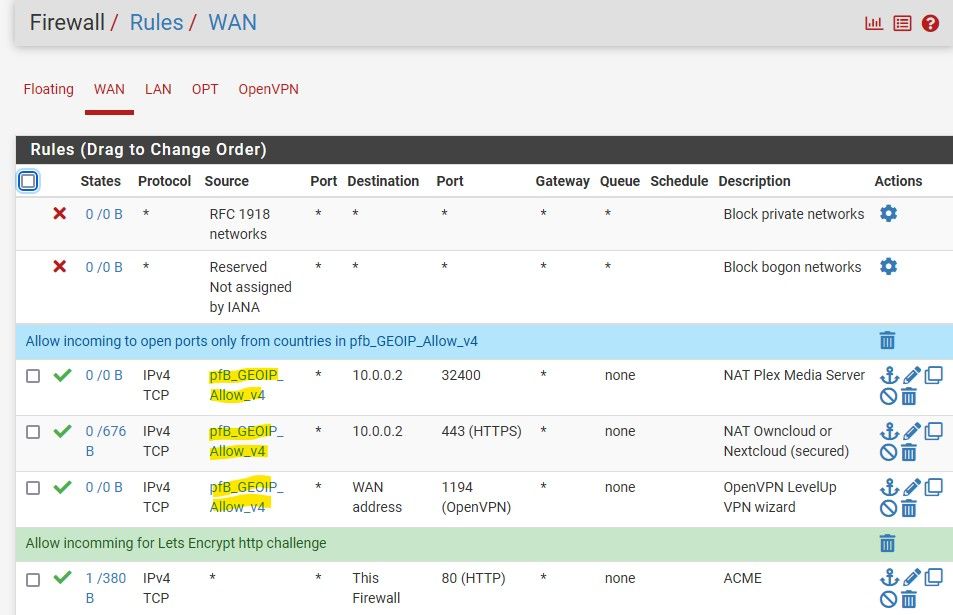
Now my firewall rules looks very simple and are easy to understand.
-
I sure wouldn't allow 80 to pfsense wan.. Did you disable pfsense redirection of 80 to your https port?
Better option for acme is prob dns vs http check.
-
@johnpoz, yes i disabled the redirection of port 80 and set my TCP port to 10443 in order to get my webconfigurator out of ports 80 and 443.
Please note that this particular rule is not pointing to the WAN address, it is pointing to "this firewall". Since the webconfigurator is not available at port 80 and i have no services available at this port either, the incoming traffic has nowhere to go.
I did this because I tried to use ACME with the DNS method but i couldn't find a way to make it work with my DDNS provider (duckdns).
-
@lrossi said in PfBlockerNG GEOIP for open ports.:
it is pointing to "this firewall"
Which includes ALL ips setup on the firewall = your wan being one of them ;)
with my DDNS provider (duckdns).
huh? You would create the record in your authoritative ns.. I was not aware that duckdns allowed you create such records. Thought you just point a cname to whatever your duckdns fqdn is..
-
@johnpoz, I wasn't aware. Ignorance is bliss.
Regardless, do you think my network is still exposed when i have no services on port 80? -
If you have nothing running on 80, it shouldn't be a problem - but that alias is every IP on your firewall. For such a rule it would be bad practice to use such an alias.
Would you mind PM the domain your using for acme - curious to see who the SOA is for this domain.