Permit Windows Update
-
@kom Thanks.
Dang. Seems like a lot of effort when all we need is a simple wildcard allow rule. Strange that isn't a native feature of the pfsense device.
Regards,
Adam Tyler -
@adamthemantyler Aliases using hostnames are updated periodically by pfSense. A wildcard *.windowsupdate.com doesn't necessarily mean that a.windowsupdate.com has the same IP as b.windowsupdate.com, as I think MS means to allow anyname.windowsupdate.com (it would be entered in IE using the *, for example).
Brainstorming, could you accomplish this by using domain overrides in DNS to allow DNS lookups only for those hostnames?
-
@steveits Yea, I get it. for a traditional fqdn alias, the firewall is basically just resolving the url periodically and adding the IPs proactively.
The wildcard alias could be anything and can't work the same way. The firewall would have to watch for DNS queries and on the fly add resolved IPs that were returned for any query matching *.windowsupdate.com for example. This gets further complicated if your client is using the DoH protocol and DNS queries are encrypted making them invisible to the firewall. Thank you Firefox and Chrome.
It's crazy to me that Microsoft can't provide a static list of IP addresses associated with their update service. The further introduction of CDNs makes it even more impossible.
Regards,
Adam Tyler -
Have you considered setting up an internal update site for Windows?
-
@andyrh WSUS? We actually run it already, but all clients are directed to the public internet for the downloads. We only leverage WSUS for policy. Ie.. update approvals. Our environment is laid out in such a way that going to the internet makes more sense compared with hosting the update repository ourselves.
-
@adamthemantyler said in Permit Windows Update:
It's crazy to me that Microsoft can't provide a static list of IP addresses associated with their update service
Really ?
The day they, Microsoft, publish such a list, you'll assist at the beginning of the end of Microsoft.
Stockholders and half planet earth (the Windows users) will get very angry.
These IP's will get DOOSsed by some 'anti' (MS) group, so they are inaccessible, so PC's don't get updated any more. Do you see where this goes ?So, not crazy.
You're just missing bit of info that explains the (a possible) situation ;)
And yes, of course, I also would love to see a firewall rule that permits something like "*.whatever.tld" as a literal, but you already mentioned that this is not gona happen soon.
This is not a "pfSense" issue, it's how firewall work. -
@gertjan A company like Microsoft with an unlimited budget is capable of dealing with distributed denial of service attacks. The fact that *.domain.com isn't available on the pfsense platform is specific to pfsense. It is only how this firewall works until the pfsense development team changes it. I work with other firewall devices that do this all day long.
You seem very sure of yourself, wonder how many other folks think you're an a** hat like I do...
Oh wait, make sure I put the winky face in here so you feel like I was just kidding. ;)
-
an unlimited budget
That's why I threw in the "share holders" word : they have something to say - if not everything.
Sure, they can publish these IPs. For some reason, they don't.
The "DOS" phrase was just an example, as I don't work for them.The fact that *.domain.com isn't available on the pfsense platform is specific to pfsense.
At a firewall level, that is, right ? To be used in a firewall rule.
All it has, is the somewhat limited Aliases.Be : I'm curious : what firewall can handle "*.domain.com" ? Not using some Squid or other proxy approach, but at a firewall level ?
pfSense can't. Maybe it's a budget thing.You seem very sure of yourself
I was actually citing the manual. I do not (want to) pretend knowing more then that.
This is a user to user forum. Not a tech support chat.
So, yes, until I know more, I'm pretty sure of what I know now. I'll keep on learning.
What other people think wasn't an issue, and is actually a good thing : I want them to think.You seem very sure of yourself
Then that makes us 2 (winky)
-
@adamthemantyler said in Permit Windows Update:
"The fact that *.domain.com isn't available on the pfsense platform is specific to pfsense."
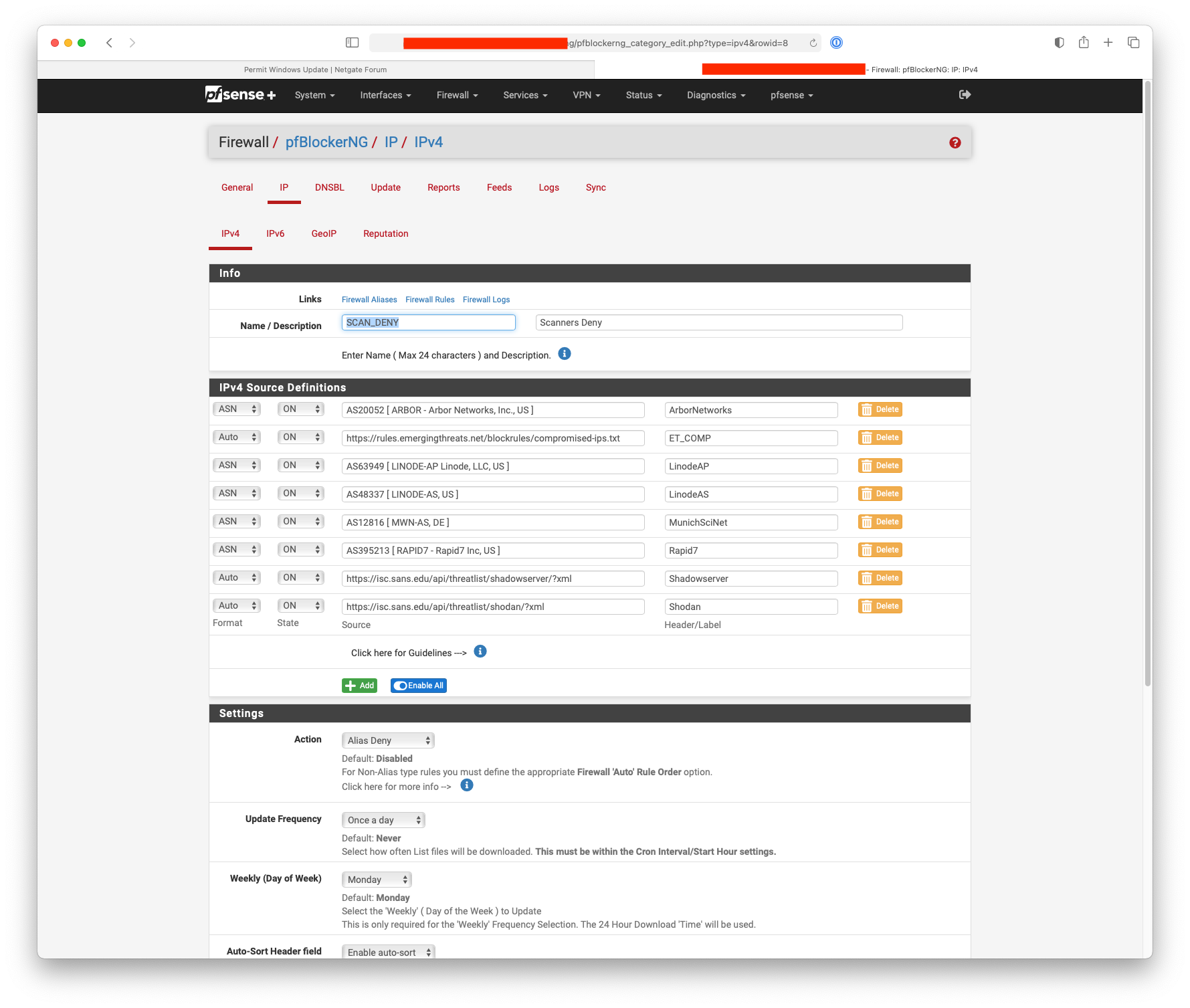
You could use pfBlocker-NG and create an alias permit using the Microsoft ASN numbers.
-
@nogbadthebad Hello! Crafting firewall policy around an organizations AS isn't something I've thought of before, clever. Based on M$s AS, I should be able to deduce what public networks they own. Couple of issues I can think of right away though.
-
Would pfBlocker-NG automatically poll subnets related to a particular AS and update on the fly? Or would this be something that would have to be manually babysat?
-
This is all for not if Microsoft is using a 3rd party CDN to redistribute updates. Those destinations would no longer be owned by Microsoft.
Regards,
Adam Tyler -
-
-
You can configure pfBlocker-NG to pull the new list every hour up to Weekly automatically, the ASN contents wouldn't change too often.
-
Yup correct, you may need to add Akamai, etc ... if stuff stops.
-
-
@nogbadthebad Cool..
Only pain point is adding a service like Akamai to this blanket whitelist rule. Doing that would allow much more access than intended. T completely unrelated IP blocks used by other entities for any purpose.. Hmm..
Regards,
Adam Tyler -
@adamthemantyler I'm a Mac guy, does the M$ update use non 80/433 ports, you could only allow the update ports through the alias / firewall rule.
-
@adamthemantyler You might want to revisit your policy of not using your WSUS server to update your clients. Seems like that would be the simplest solution for you.
-
@KOM this is not a good solution as wsus needs to be allowed internet access as well
-
here's a list that can be imported as an alias of supernets microsoft update uses/owns
used https://geo-lookup.ipify.org/ to look up blocked IP's and then correlate to a block/asn owned by m$windowsupdate.microsoft.com Entry added Mon, 21 Mar 2022 14:36:24 -0700 download.windowsupdate.com Entry added Mon, 21 Mar 2022 14:36:24 -0700 go.microsoft.com Entry added Mon, 21 Mar 2022 14:36:24 -0700 dl.delivery.mp.microsoft.com Entry added Mon, 21 Mar 2022 14:36:24 -0700 wustat.windows.com Entry added Mon, 21 Mar 2022 14:36:24 -0700 download.microsoft.com Entry added Mon, 21 Mar 2022 14:36:24 -0700 67.24.0.0/13 Entry added Tue, 28 Nov 2023 00:22:34 -0800 8.240.0.0/12 Entry added Tue, 28 Nov 2023 00:23:48 -0800 51.10.0.0/15 MICROSOFT-CORP-MSN-AS-BLOCK 104.40.0.0/13 MICROSOFT-CORP-MSN-AS-BLOCK 52.160.0.0/11 MICROSOFT-CORP-MSN-AS-BLOCK 13.64.0.0/11 Entry added Thu, 25 Jan 2024 14:26:53 -0800 172.160.0.0/11 Entry added Thu, 25 Jan 2024 14:38:23 -0800 20.160.0.0/12 Entry added Thu, 25 Jan 2024 14:43:38 -0800 40.76.0.0/14 Entry added Thu, 25 Jan 2024 14:44:19 -0800 20.64.0.0/10 Entry added Thu, 25 Jan 2024 14:45:14 -0800 40.127.0.0/16 Entry added Thu, 25 Jan 2024 14:50:01 -0800 51.140.0.0/14 Entry added Mon, 21 Mar 2022 14:31:36 -0700 52.160.0.0/11 Entry added Mon, 21 Mar 2022 14:31:36 -0700 20.48.0.0/12 Entry added Mon, 21 Mar 2022 14:31:36 -0700 52.136.0.0/13 Entry added Mon, 21 Mar 2022 14:31:36 -0700 104.107.104.0/22 Entry added Mon, 21 Mar 2022 14:31:36 -0700 40.80.0.0/12 Entry added Mon, 21 Mar 2022 14:31:36 -0700 52.136.0.0/13 microsoft 20.48.0.0/12 Entry added Sat, 02 Apr 2022 18:27:56 -0700 52.160.0.0/11 Entry added Sat, 02 Apr 2022 18:27:56 -0700 51.140.0.0/14 microsoft 20.184.0.0/13 Entry added Fri, 08 Apr 2022 10:02:16 -0700 40.126.0.0/18 Entry added Fri, 08 Apr 2022 10:03:26 -0700 20.40.0.0/13 Entry added Fri, 08 Apr 2022 14:57:24 -0700 52.242.97.97/11 Entry added Fri, 08 Apr 2022 14:58:28 -0700 13.91.16.69/11 Entry added Fri, 08 Apr 2022 14:59:38 -0700 51.10.0.0/15 Entry added Fri, 27 May 2022 18:10:58 -0700 13.107.4.0/24 Entry added Fri, 27 May 2022 18:12:13 -0700 40.112.0.0/13 Entry added Fri, 27 May 2022 18:20:55 -0700 40.125.0.0/17 Entry added Fri, 27 May 2022 18:28:46 -0700 52.224.0.0/11 Entry added Fri, 27 May 2022 18:35:24 -0700 13.107.42.0/24 Entry added Fri, 27 May 2022 18:53:55 -0700 52.152.0.0/13 Entry added Fri, 27 May 2022 18:59:37 -0700 104.40.0.0/13 Entry added Fri, 27 May 2022 19:01:05 -0700 204.79.197.0/24 Entry added Fri, 27 May 2022 19:18:44 -0700 40.74.0.0/15 Entry added Fri, 27 May 2022 19:26:09 -0700 104.84.224.0/22 Entry added Fri, 27 May 2022 19:36:17 -0700 51.116.0.0/16 Entry added Fri, 27 May 2022 19:48:04 -0700 13.64.0.0/11 Entry added Fri, 27 May 2022 20:04:08 -0700 20.64.0.0/10 Entry added Fri, 27 May 2022 20:06:22 -0700 96.7.232.0/22 Entry added Fri, 27 May 2022 20:08:21 -0700 184.30.160.0/19 Entry added Fri, 27 May 2022 20:14:38 -0700 40.127.0.0/16 Entry added Sat, 28 May 2022 10:02:46 -0700 8.240.0.0/12 Entry added Sun, 21 Aug 2022 16:44:27 -0700 54.192.80.0/22 Entry added Sun, 21 Aug 2022 16:45:10 -0700