Log action is unkn(11)
-
Hi, i'm having a weird issue with a pfsense since yesterday.
I could not connect one of my remote site using RDP, any protocol seems to work except RDP. I tried on some server on the remote network same issue. Seems nobody edit the configuration of the firewall.
In the firewall log I noticed this :
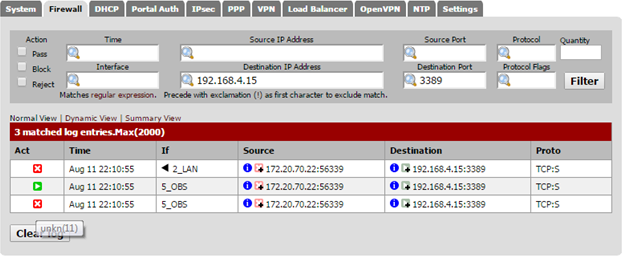
Action is unkn(11)
The action is so sudden and apply to all the server so i really think the pfsense is the problem here. the pfsense is running the following version : 2.1.5-RELEASE (amd64)
Any idea ?
-
More information :
I saw this unkn(11) one time; the issue was about asymmetrical routing.
For my actual problem i double checked, and there is no routing problem.
Any idea ?
-
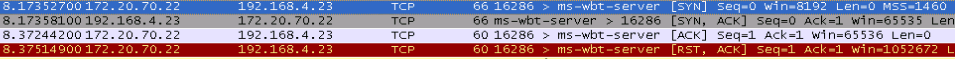
Here is a packet trace :
(172.20 is the local site and 192.168 is the remote site)
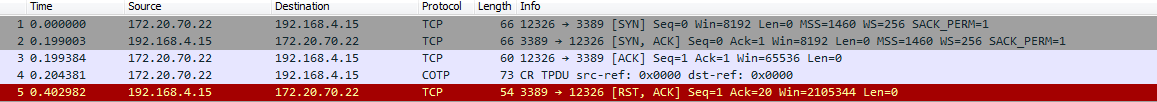
Every time i tried a connection to the remote site i get a RST.
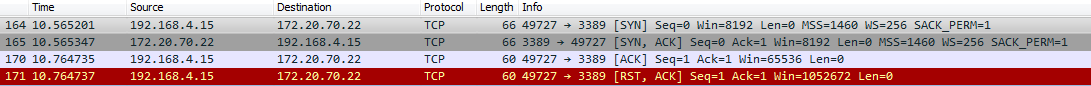
If i try a a connection from the remote site to my site i get the same issue. The server on the remote site send me an RST packet.
May be not a pfsense issue, someone have an idea ?
-
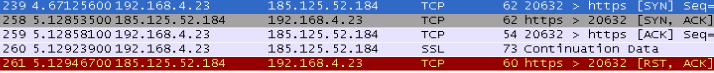
Ok I ran the same test with wireshark on the remote site and that's weird. I start the connection on my site to the remote site. the following two screenshot are from the same TCP session
From my site (172.20.70.22) :
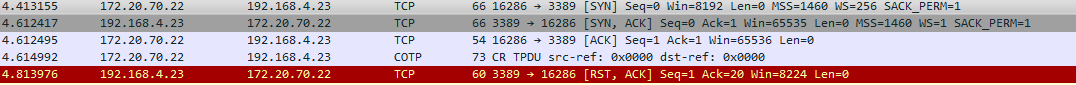
From remote site (192.168.4.23)
We don't have the same thing:
From my site perspective the remote site send the RST flag.
From the remote site perspective, my site sent the RST flag.Maybe a pfsense issue after all ?
If anyone have an idea that would be nice.
-
I'm still struggling with that.
Is it possible that pfSense create those RST packets and send them to both device ?
-
Another test :
From the remote site I tried to connect to RDP to another computer (out of the company, out of the domain) using another port.
Same issue, i received a RST packet and the connection closed again.
I would really appreciate any help with that.
-
Side question : the pfsense version is kinda outdated - Is that issue have been resolved by an update ?
Can i update it easily to the latest version using manual update (can't autoupdate from China it seems but DNS&Internet is working at)
Is it "safe" (no known error?) ?I just found an option in System > Advanced > System Tunables :
net.inet.tcp.blackhole set to 2. Here is the description : "Drop packets to closed TCP ports without returning a RST "
Seems to be my issue, looks like the pfsense is closing all RDP session with a RST, is there a way to disable that "functionnality" ?
Thanks.
-
In the end pfsense start to work properly again without any modification ….........