Managing Wired + Wireless IP Cameras (blocking access explicitly?)
-
Hi all. I'm running pfSense at home on a pretty basic network but in light of recent activity involving poorly secured devices starting to be exploited I think it may be time to add some additional layers of security.
Info:
I've got UPnP disabled.Network Setup:
WAN/LAN interfaces only
LAN 192.168.1.1/24DHCP pool 192.168.1.100 -> .245
WiFi Access points and IP Cams (15 cameras) have static mappings to IP's below the pool (192.168.1.2/3/4 etc)
I manage my cameras through a PC on the LAN, so I need Cams <-> LAN activity passed obviously.
My cameras do use NTP, though it appears I can setup pfSense to handle that job by simply setting a few Time servers in the Services -> NTP tab.
Should I then create rules to block any CAM < - > WAN traffic? Since they're in the same subnet as my LAN do I need a rule for each? Should I put them in their own subnet to make managing this easier?
Any suggestions/tips are much appreciated. These are basically the only "Smart Devices" on my network and many of them are cheap units with likely insecure firmware. Short of replacing them with very very expensive ones I'd like to do what I can to avoid issues.
TIA!!
-
I would create an alias that holds all of the camera's IP addresses and then have a block on LAN for that alias.
-
Hi all. I'm running pfSense at home on a pretty basic network but in light of recent activity involving poorly secured devices starting to be exploited I think it may be time to add some additional layers of security.
Info:
I've got UPnP disabled.Good. That was never a good idea which is why it is disabled by default.
Network Setup:
WAN/LAN interfaces only
LAN 192.168.1.1/24DHCP pool 192.168.1.100 -> .245
WiFi Access points and IP Cams (15 cameras) have static mappings to IP's below the pool (192.168.1.2/3/4 etc)
I manage my cameras through a PC on the LAN, so I need Cams <-> LAN activity passed obviously.
The firewall/router has nothing to do with passing traffic between hosts on the same subnet. If you wanted to block that traffic you would have to do it in your switch, not your router.
My cameras do use NTP, though it appears I can setup pfSense to handle that job by simply setting a few Time servers in the Services -> NTP tab.
As long as your cameras are not responding to NTP requests from the general internet, they likely will not be used in an amplification attack. The spoofed traffic would have to come from inside your network.
Should I then create rules to block any CAM < - > WAN traffic? Since they're in the same subnet as my LAN do I need a rule for each? Should I put them in their own subnet to make managing this easier?
Doing so might just keep them from getting updates. In all likelihood it was not outbound traffic that was the problem. It was inbound. See below.
Any suggestions/tips are much appreciated. These are basically the only "Smart Devices" on my network and many of them are cheap units with likely insecure firmware. Short of replacing them with very very expensive ones I'd like to do what I can to avoid issues.
TIA!!
Here's the deal. People are lazy. They can be told again and again and again how insecure it is to simply port forward to their DVR/CAM/RDP/etc but they do it anyway. Often without even limiting the traffic to specific source IP addresses. You can tell them they should use a VPN instead until you are blue in the face and they will refuse. This forum is chock-full of examples of this phenomenon.
As long as you are not directly passing unsolicited connections FROM THE INTERNET to these devices you are probably OK.
That said, a segmented LAN for this sort of device also makes good sense. You can pass connections from LAN to IOT for management purposes and easily block connections from IOT to LAN.
Unfortunately, setting up/maintaining such a networking scheme up is understandably beyond the grasp of 99% (maybe higher) of consumers. It also requires gear such as multi-ssid wi-fi, smart switches, etc.
Have some popcorn on-hand. This show's just getting started.
-
Thanks Derelict for the comprehensive response. I can support multiple SSID's but I recently retired my old DDWRT powered AP's in favor of some D-Link DAP-1650 which have "Guest SSIDs" but not just raw control over SSID creation/managment or VLAN tagging for them. I may opt to simply add an OPT1 and have that be the "CAM" network.
I currently do not allow any outside access to any of the cams, nor do I allow VPNing to the network as one of the cam's is a baby monitor. I may relent and allow a VPN of some sort into the network so I can check in while traveling. I am very rusty on OPEN VPN options but I think that appears to still be the best option and it has viable options for Android and Windows clients.
Thank you again, the overview is much appreciated and allows me to say I'm OK going forward with the cameras in my main network and using VPN For remote access as needed. I will look to eventually put cam's on their own segment via an OPT interface or VLAN's and add some additional controls that way.
-
Wow didn't take much to get OpenVPN going with Cert + Login authentication. The client export package makes getting it going on Android and Windows a breeze. I remember distinctly paying Chris to walk me through step by step connecting a site to site open VPN a few years ago and thinking it seemed more complex than it needed to be. Sure is slick now with the wizard.
-
Yup. EZPZ. And pretty secure with SSL/TLS + User Auth with TLS authentication enabled. You pretty much only have to worry about the key getting compromised. Lots of luck to anyone without it.
-
Yup. EZPZ. And pretty secure with SSL/TLS + User Auth with TLS authentication enabled. You pretty much only have to worry about the key getting compromised. Lots of luck to anyone without it.
Yea, I went with SSL/TLS + USER and it was a breeze. Sure makes me feel better vs poking holes. Now to get some sort of Dynamic DNS setup since my cable company decided to start moving IP's on me after 10 years of the same IP.
-
Sorry for the noob here, but I see traffic going from Cams to WAN. This is apparently a known "Feature" of some of the cameras I have. Will this firewall rule (assuming IP_CAMS is an alias of cameras) block any access from the cameras to the outside world:
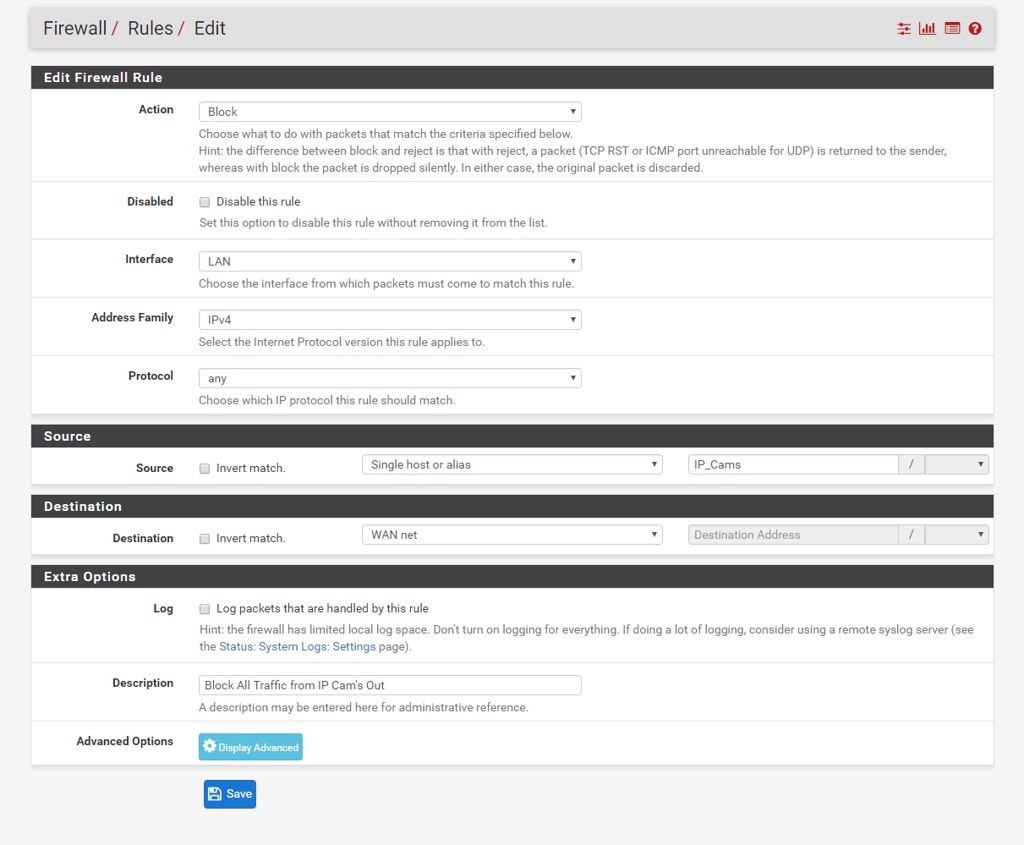
?
I am always on the LAN network when connecting to the cameras thanks to the VPN set up above.
-
Change the Destination from WAN Net to Any. WAN Net is not "The Internet", it's just the actual network your WAN IP is part of.
-
@KOM:
Change the Destination from WAN Net to Any. WAN Net is not "The Internet", it's just the actual network your WAN IP is part of.
That won't block traffic to LAN? This is why I ask I guess.
-
Of course it won't, this iscontrolling traffic coming FROM the LAN going anywhere else (thus the any) thanks for the patience ;)
-
this iscontrolling traffic coming FROM the LAN going anywhere else
Now you're getting it. Rules apply to traffic entering an interface and control where that traffic is allowed to go to.
-
@KOM:
this iscontrolling traffic coming FROM the LAN going anywhere else
Now you're getting it. Rules apply to traffic entering an interface and control where that traffic is allowed to go to.
I was CISCO CCNA Certified 14 years ago, you'd think this wouldn't be this foreign to me but that's what you get when you become a middle-manager stooge. Thank you again for your patience and answers this community has always been so helpful.