Need help with rules
-
Hi,
I just build my first pfsense box and I'm trying to make firewall rules to work without any luck.
I'm totally newbie with firewall rules.I have PIA VPN installed succesfully.
What I want:
All LAN traffic forced to use VPN only, except few LAN ip's (TV's) and websites (twitch.tv example) need to use WAN because they don't work with VPN.Any helps with rules? :-[
-
This would be a simple policy route. Tell your vpn client not to pull routes - since this will normally grab default route sending traffic out the vpn.
Then just create rules on your lan that send allow the IPs you want to use wan as source out without gateway set. Your other devices or all other create a rule that sets gateway to your vpn interface.
Remember rules are evaluated top down, first rule to trigger wins and no other rules are evaluated.
If you want an example I can post up a screen shot.
-
Thanks for your reply.
It would be amazing if you could give screenshot of rules/settings which I'm trying to do!
Hope it's not too much to asked. :) -
So on your vpn client settings in pfsense, make sure it does not pull routes.
Then on your lan rules create use an alias that has the IPs of the devices you do not want to use the vpn. Do not set a gateway on this rule just leave the default.
Then on your rule just below that use any any rule but under advance set the gateway to use your vpn interface you created. See attached example
So the ips I put into the NOvpn alias would just use the normal wan connection. But other ips that are not in the alias would hit the next rule and be forced out the vpn connection.
Remember rules are evaluated top down, first rule to trigger wins no other rules are evaluated.

-
I have been messing around with firewall rules, are these at even close what I'm trying to achieve? ;D
VPN_VPNV4 is set to default gateway
Floating rules:
No rules
WAN
(Default rules)RFC 1918 networks (description: Block private networks)
Reserved Not assigned ny IANA (description: Block bogon networks)LAN
From top to bottom
Rule to pass spesific lan IP to WAN
Action: Pass
Disabled: unchecked
Interface: LAN
Address Family: IPv4
Protocol: Any
Source: Single host or alias - 192.168.1.10
Destination: Any
Gateway: WAN_DHCP - xx.xxx.xx.x - Interface WAN_DHCP Gateway–--------------------------------------------------------------------------
Rule to pass spesific websites to WAN
Action: Pass
Disabled: unchecked
Interface: LAN
Address Family: IPv4
Protocol: Any
Source: Any
Destination: Single host or alias - Twitch.tv
Gateway: WAN_DHCP - xx.xxx.xx.x - Interface WAN_DHCP Gateway–--------------------------------------------------------------------------
Rule to route all other traffic trough VPN only
Action: Pass
Disabled: unchecked
Interface: LAN
Address Family: IPv4
Protocol: Any
Source: Any
Destination: Any
Gateway: VPN_VPNV4 - xx.x.xx.x - Interface VPN_VPNV4 GatewayVPN
No rules
OpenVPN
No rules
EDIT:
oh, you replied while I was writing this postWill these rules act like "kill switch" for devices which uses VPN?
-
You mean if vpn is down? If vpn is down then clients that are not in the allow rule to use the wan would have no way to get out.. So yeah they would be killed.
-
With "Kill Switch" I mean if VPN goes down, all traffic (except those WAN rules) will be stopped and IP or anything else will be not leaked.
How does those rules look, what changes would yo do?
Any improvements for security?Example for VPN rule, if change protocol to UDP and destination for PIA server port 1198?
Would these make rule more secure? -
Huh? The rule that sends traffic out the vpn gateway - how would internet work if you limited that to 1198 and udp only?
But your rules look fine - other than there is no reason to call out gateway on you rules to allow access out your wan.. Which would be default anyway. Your rule for twitch.tv would be an alias that you put in whatever sites you want to be allowed. Keep in mind that sometimes these can be problematic if the IPs of these sites change all the time with short ttls, etc.
-
heh, have to say I'm totally noob at networking.
I have had only some "plug in wall and forget" routers before this pfsense router ;D
But everyday is possible to learn something new, right?In this "kill switch" topic all traffic is forced for UDP and port 1198 if I understand correctly?
https://forum.pfsense.org/index.php?topic=74911.0
I have changed VPN_VPNV4 to default gateway. Should I switch it back to WAN and set those WAN getaways to default?
Will it make difference?By the way,
Is there any way to block webRTC leaks via pfsense?
I found a way to block leaks via browser addon, but it would be nice if it could do easy in router level.
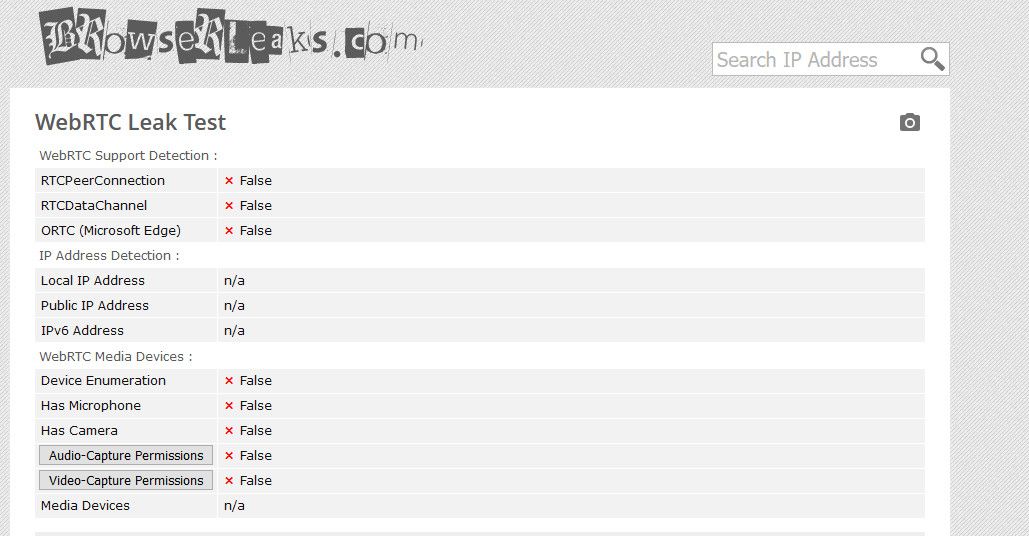
Without browser addon, those leak test sites show my lan ip in webRTC leak. -
@johnpoz hi there. why i dont see your sample attachment? best regards santo
-
Most likely because this is from 2017, and when they moved forum software some attachments got lost.. Can put up another one.
What exactly are you wanting to do - best to start you own thread with your own rules and your own questions vs this old thread from 2017
-
thank you for your fast reply - of course your are right.
I can not expect somone to help me in my particular situation (ip-leak by using vpn) and as i am new to pfsense and do not have a deep understanding of network and firewall rules yet, it is not gruanted that i would understand the suggestions made.To your question: what exactly am i wanting:
My problem is dns-leak of my ISP-IP while using vpn-provider. But i dont understand why i can not prevent webrtc-leak with pfsense. Eventhough i understand it is primarly a browser issue i would have expected to find a why to answer the WebRTC-request through the firewall-rules and send it to the vpn-provider to make sure the response is not the IP i got from my ISP.i tried guides from three big vpn-provider to setup pfsense with my vpn-provider. Which is going well, but leaks with certain test my IP i got from my ISP.
the only difference i can find is that i am using a gateway group to manage 5 vpn connections at tier1 (to "load-balance" them) and the default gateway on tier2 as fallback if all vpn-connections would be down. But even if it set it up with one vpn-connection only and therefore without a gateway group it still leaks my ip-adress with tests like this:
https://ip8.com/webrtc-test
and
https://browserleaks.com/webrtc -
If you want to block webrtc - you disable it at the browser.. Not sure how you think a layer3 firewall would stop traffic that is between where your at and your browser inside the protocol that was allowed..
Not using a vpn - and that test doesn't work, because I disabled webrtc in the browser.. If its working for you - then you have not actually disabled it
To your other test... So no vpn - shows public
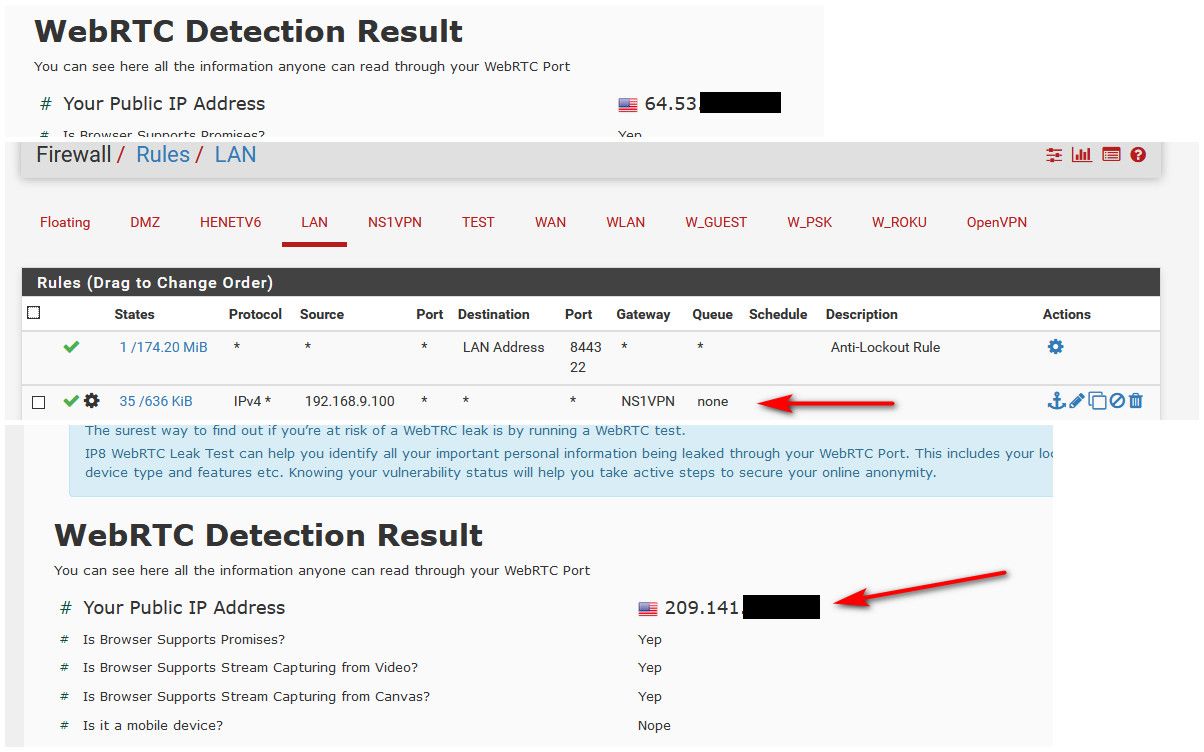
Then send that client out a vpn - shows vpn IP..
Nothing can do to help you without you showing what your doing..
-
@johnpoz thx a lot. Seeing your rule, i realised i had a "tiny" mistake in my lan-rule with vpn gateway within the protocol typ i had tcp and had lower a rule to any without vpn. now i changed it and all is fine. thx. a lot.
-
Keep in mind as well when you create a rule - there could be states already that would be evaluated first.. Whenever you edit your rules that there could be states there from your previous rules evaluation that could be allowing something you are now blocking.
-
@johnpoz yes, from now on i will keep in mind this :-)