Bypassing DNSBL for specific IPs
-
I have followed your recommended steps, but for some reasons, clients on my DMZ are not resolving (example Chrome says "DNS_PROBE_FINISHED_BAD_CONFIG")
- I have unselected DMZ interface from Unbound's Network Interfaces.
- There are no NAT or port forward applied to DMZ (as far as I know).
- The DNS servers fields under DHCP server settings for DMZ are all empty. AFAIK, when empty it will use the general DNS servers under System > General Setup which are 1.1.1.1 & 1.0.0.1 for me.
- There are 3 firewall rules on DMZ
-> Block any traffic from DMZ subnet to LAN subnet
-> Block any traffic from DMZ subnet to "This firewall"
-> Allow any traffic from DMZ to * . *Since rules are processed top-down, I'd expect the DNS requests on DMZ clients to match the last rule??? I must be missing something! If I suppress (deactivate) the second rule (block to this FW), same problem occurs.
EDIT: In order to keep the setup as straight FW as possible, and since I do not need local host resolution, I have no issue completely bypassing Unbound and using pfsense's DNS servers directly. I just want to avoid having to configure each client manually (most of the clients on DMZ are mobile devices that I will see only once....)
-
Have you tried specifying the public DNS servers in the DMZ DHCP pool config. i.e. don't leave that field blank?
I suspect that because unbound is enabled on pfSense, the DMZ DHCP server is still providing the DMZ Interface address for DNS, I don't think its aware you are not actually listening on that interface. Not able to double check at the moment.Check one of your DMZ hosts and see what DNS IP address they are using. Is it the same as the gateway?
Just a thought . . . .
-
@horse2370 : Yeah you are right.
From pfsense:
Leave blank to use the system default DNS servers: **this interface's IP** if DNS Forwarder or Resolver is enabled, otherwise the servers configured on the System / General Setup page.Unbound being enabled, the interface's IP is forwarded as DNS server on clients, this is what I see from ipconfig on my work laptop running windows 10.
I will google how to keep unbound active for other interfaces and have the DNS servers forwarded to DMZ. I tried restarting Unbound but didnt help.
EDIT: Yeah... DNS Forward was disabled in Unbound's options..... I may slap myself behind the head. I now understand that I can revert Unbound's Advanced options to simply "server:include: /var/unbound/pfb_dnsbl.conf" and delete everything else since I no longer need views?
-
I think the help text means unbound is enabled on pfSense, not specifically the interface. i.e. globally.
I would just add the DNS servers to the DHCP server configuration for the DMZ. Keep it really simple. This is the same kind of recommendation used in Enterprise networks for Wireless Guest. That way, guest bypass corporate DNS and just get public.
You LAN clients uses unbound (with forwarding to Google) and DNSBL filters, DMZ clients use Google directly, etc.
-
@horse2370
I added the DNS servers (1.1.1.1 + 1.0.0.1) to DMZ's and the clients are now seeing the DNS servers with "ipconfig".Seems its all working fine for now! There is still a little issue with random skype call drops when connected to DMZ, I will investigate then open a separate thread if need be.
Thanks to all for the help and patience, especially you @horse2370 !
-
@horse2370 said in Bypassing DNSBL for specific IPs:
the same kind of recommendation used in Enterprise networks for Wireless Guest. That way, guest bypass corporate DNS and just get public.
Right !!

@horse2370 said in Bypassing DNSBL for specific IPs:
You LAN clients uses unbound (with forwarding to Google)
Euh .... Corporate clients networks forwarding to Google ??
Wrong
At least in Europe, that's not a recommendation thing, one could get fired for that. Maybe in the States other rules or reasons exist, I can't tell.
For me, "8.8.8.8" is at maximum a soHO thing.
(I really guess because our society fabricated a lot of people that are trained to "have to enter a DNS" because our ISP's trained us to do so in the past. They had their reasons, but these do not exist any more).But if someone can tell me ones and for all what the benefits are, I'll adopt "8.8.8.8" myself, promised.
Btw : don't get me wrong : I'm using gmail (just perfect for automated notification systems).
I do like their search engine a lot - it works for me
I'm not against Google as a company (how could I). -
Great! Your Welcome
Thanks for clarifying in case others also thought I recommended Enterprise customers forward to Google from their internal DNS. What I thought I wrote was ONLY referring to Guest network recommendation.
My last sentence in that post was specific to pftdm007's environment, although it should have started with "Your" and not "You" :-)
To clarify - The general recommendation is to keep guest traffic isolated from internal resources, i.e use the internal DHCP servers on the network infrastructure, such as the WLAN controllers as typically that is where the capture portal is anyway, and have them use an ISP or Public DNS (i.e. non-enterprise), instead of letting the guest traffic roam around the datacenter/datacentre servers before being routed (you can pronounce "routed" correctly :-) ) out the Internet gateway.
For the Enterprise's own DNS, it should follow standard best practices, which as you correctly point out would not typically include forwarding all your DNS traffic to Google's Public server to data mine.
As always the answer is never quite that simple and it always depends. Some smaller companies may choose to utilize a Public/Cloud DNS service as part of their security posture, but that would be an authoritative name service. Hence, one of the reasons Cisco acquired openDNS, or you could even use Google Cloud DNS among many others.Like you, I use Google, however when it comes to privacy. . . . . . not so much. Yes I'm in the states, but originally from the UK and deal with customers World Wide and am exposed to all kinds of regulations. Most good, some just plain political and a PIA. The amount of time spent on training for compliance is getting beyond a joke. Soon I won't have time to do actual work that might contravene a regulation.
My home DNS used to resolve from root severs and I have a managed provider for my personal domains for simplicity and resiliance. I certainly avoid forwarding to my ISP's DNS and even using root servers when my ISP started hijacking DNS on UDP 53.
Quick Google for a supporting article provides some details Comcast hijacking DNS
I switched to encrypted DNS on community supported DNS servers, until Cloudfare rolled out their free public service for people like me.I could see one benefit of using Google for your DNS, they would mine those requests and know what you needed to buy before you did

As with anything, there are exceptions to every rule, your mileage may vary and it will always depend!
Stay safe
-
I just realized... DNSBL can be bypassed by passing different DNS servers to my DMZ clients (so they do not go thru Unbound), but what about pfBlockerNG?
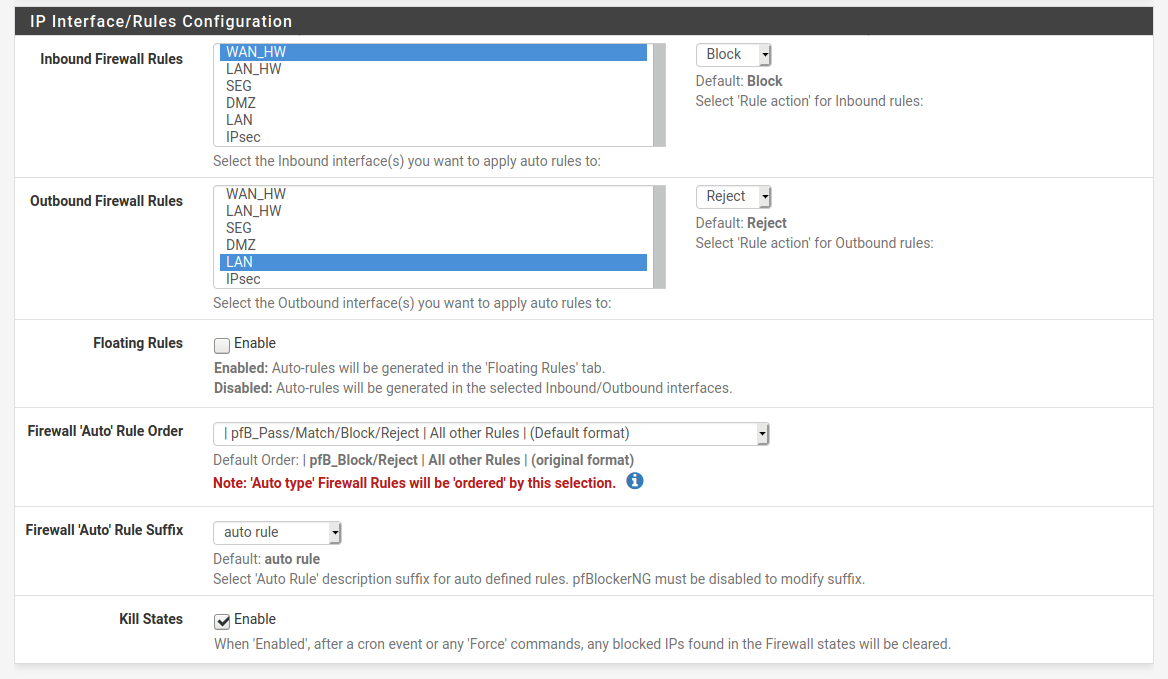
WAN is selected in Inbound, and LAN is selected for outbound, but not DMZ (so not to have pfblocker block traffic on DMZ).
In pfsense's FW logs, I see entries showing blocked traffic on WAN that is going to DMZ. This is my understanding: DMZ client sends traffic to the internet, nothing is blocked (pfblocker & DNSBL are not running on DMZ). Request gets sent to the internet, the response comes back, it is blocked by pfblocker on WAN.
I had Snort running on LAN and WAN, but not on DMZ. It kept blocking incoming traffic on WAN that was coming back to DMZ. User @bmeeks kindly explained that it was unnecessary to have Snort run on WAN. The logic is that all unsolicited inbound traffic is blocked by FW rules so only stateful responses are allowed, and since the initial traffic had gone thru Snort on LAN, it is considered "safe". Sorry for the gross over-simplification......
Is it the same logic for pfblockerNG??? How do you guys run these packages? I'm slowly realizing that I have made several mistakes in setting up my pfsense box....
-
Correct, if any client can bypass unbound on the pfSense, it will not benefit from the pfBlockNG functionality. Hence on my pfSense deployment at home, I have a FW rule on the LAN, DMZ and VPN interfaces that only allow UDP 53 (DNS) to pass if the destination is the local interface address. I have another rule that denies and logs any other requests going to other DNS addresses which I can see in the logs and my splunk setup. (Allow/Permit rule is before the deny and log rule) This shows Amazon and Google assistants trying their hardest along with my Roku's, same is true for them trying to track and report usage statistics.
Regarding you other question about pfBlockerNG, I'm going to over simplify as that is the other function of pfBlockerNG. (i.e. it does DNS filtering and the other function is IP address filtering) If you have setup the feeds, you should see "auto rule" in the Firewall Rules admin page.
Again on my setup, I am blocking Banned Hosts, Emerging threat hosts inbound on the WAN and outbound on all other interfaces. In addition I only allow inbound connection from specific countries that have family or other services that need access to the DMZ to pass. (i.e. Mail Relay and Plex) If I travel outside these normal countries I do have to modify this rule so I can still VPN and access my DMZ services. This is all done via the GeoIP admin pages.
Your other question about inbound traffic being blocked to the DMZ, I will again over simplify, but the basic premise of the FW functionality is, any session that is initiated from a "trusted" interface (LAN, DMZ) will be allowed and the inbound traffic for that session will also be allowed back through the WAN interface. For TCP, this is tracked my SYN's and FIN's for when to allow that port and when to close it. UDP relies on the same ports being used (src/dst flipped) for the return traffic and typically timers. Therefore if you are seeing blocked traffic ( and assuming you have a fairly out of the box config) those are typically from session you have not initiated or unsolicited There are many exception to this oversimplification, mainly with Video and voice protocols.
In summary, my setup uses pfBlockerNG's DNS functionality to block ads, tracking, malware and phishing sites. My logs show the PiHole feed block 95% of them. Side effect is faster page loading and a significant drop in downloaded traffic which is good as I have a 1TB cap per month.
pfBlockerNG's IP functionality keeps bad hosts and restricts countries that should not be connecting, out of my DMZ. And stops inside hosts from accidentally connecting to bad hosts. The GeoIP/Country filter does not apply outbound obviously. The Firehol feed does most of the heavy lifting based on the reports and splunk dashboards.For me, this strikes a balance between family usability of the Internet and keeping it reasonably safe and secure.
Side note, I do have Snort installed, however it is is IDS (monitor) mode with a couple of http SID's suppressed as they caused many false positives, end result, I very few alerts and check for unusual alerts every few days.
Snort is enabled on my WAN, along with a number of FW rules that log, this is only so I can see what kind of attacks are occurring for research purposes and track the percentage of encrypted IPv4 and IPv6 traffic. This is captured in dashboards that I have configured in splunk and I use for work.
Encrypted traffic continues to rise as does the split between IPv4 and IPv6. The later being significantly offset to IPv4 when the family is streaming more as the Roku's are v4 only.Hope that helps . . . . .
-
I still wonder if I am chasing a ghost or something real... Here's an actual real life example:
My work laptop is connected to DMZ. Connection straight to the outside, no DNSBL running on DMZ, no pfblocker running on DMZ, no Snort, nothing. Straight out with the exception of a few FW rules blocking anything nasty (connecting to pfsense, communicating with other subnets, etc).
This laptop is totally dysfunctional. Intermittently, web pages dont load, stuff breaks and crashes, proxy app keeps re-creating new connections to its mother ship, etc. My employer's IT support are blaming my "home network". This laptop runs a proxy service that connects to "gateway.zscalertwo.com" on port 18000.
In pfsense's FW logs, I see hundreds and hundreds of entries showing blocked traffic on DMZ. All of these have "Default deny rule IPv4" as description. That doesnt say much....
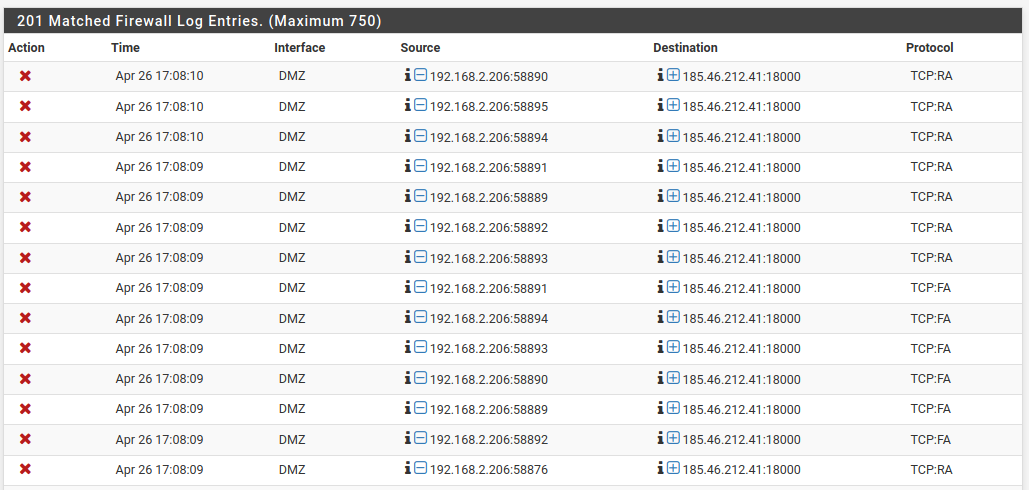
Since the FW rules on DMZ are very basic and pretty much allow anything, I started searching for an explanation somewhere else... I found in pfBlockerNG > Reports > IP Block Stats:
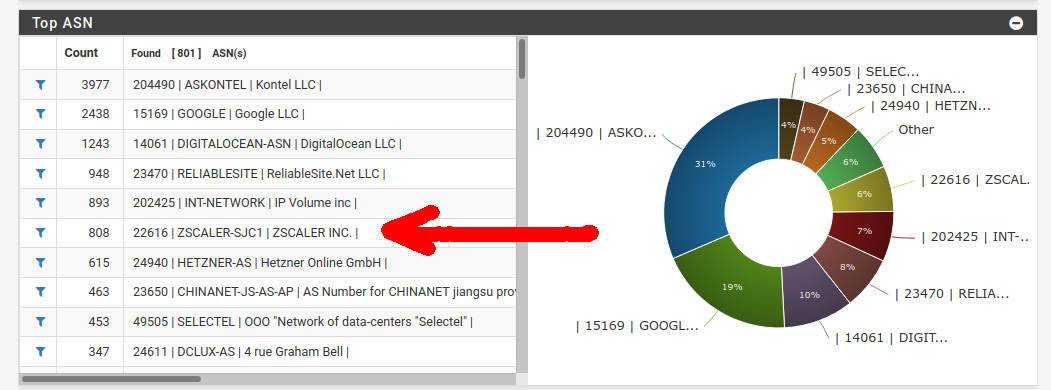
Clicking on the filter icon:
So I'm going back to my original thought. To me pfblockerNG interferes with traffic on DMZ. How can I disable this without whitelisting stuff???
-
Nope, your not chasing ghosts, but if you were, you know who to call!
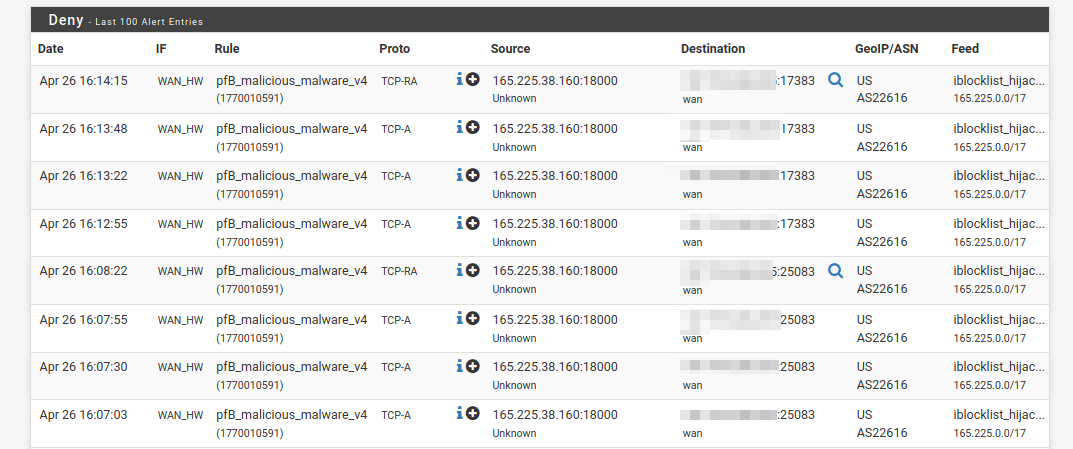
That looks like you have pfBlockerNG's IP block rules enabled on the DMZ outbound interface.The clue is the list name is "pfb_malicious_malware_v4"
You have a number of things you can do to either remove it completely, or fine tune it to remove this functionality on the DMZ interface only.
To prove it using the sledgehammer approach, disable pfBlockerNG in the Global Tab, this will turn of DNSBL and the IP Block functions on ALL interfaces. Your work laptop should then function normally.
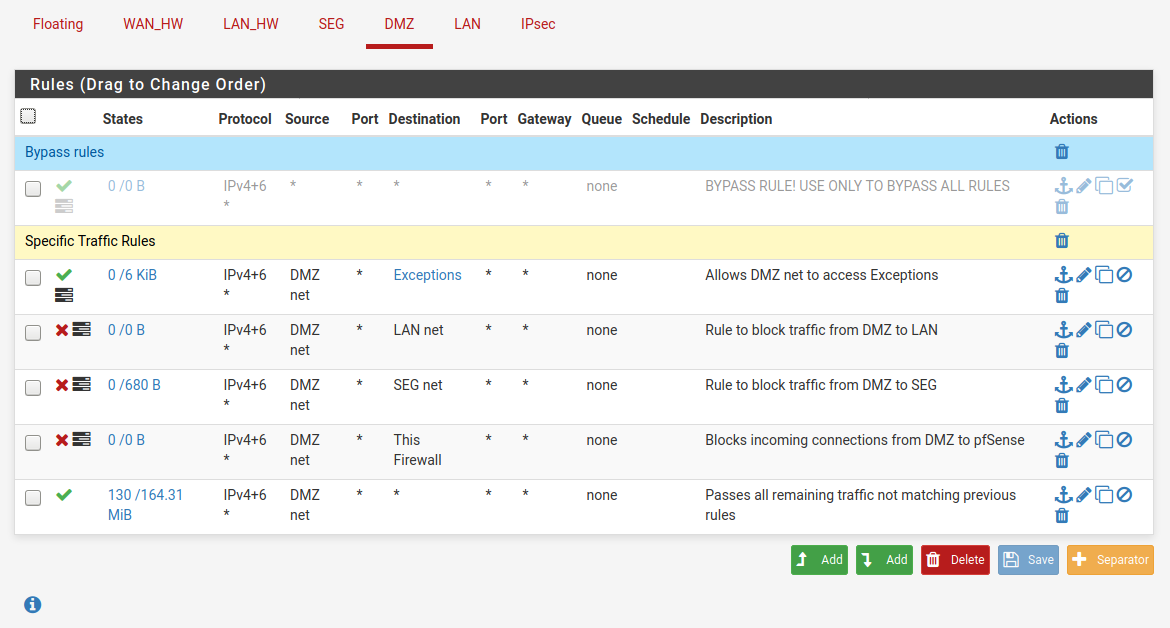
To remove this from just the DMZ, first check on the Firewall > Rules > DMZ tab and you should see something like this: -
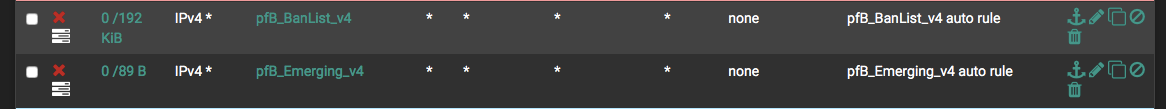
The name will be different, but it will have a "pfb" prefix and a "v4" suffix and the description will indicate it is an auto rule.
Assuming there is a rule on your DMZ, you can remove it using the Firewall > pfBlockerNG > IP page under "Outbound Firewall Rules. Deselect the DMZ. My guess is you have LAN and DMZ selected currently.If you want to keep the IP Blocks enabled in the DMZ to protect your other devices not using the zscaler service, which protects your work laptop from malicious web sites. You will need to figure out which list has the zscaler ip address tagged as a malicious malware site. That will be in the "Feeds" tab within pfBlockerNG's pages.
You can check that the 185.46.212.41 is in the pfb_malicious_malware_v4 list, by using the Diagnostic > Tables option and selecting the list name from the drop down and scrolling through the table.Some of the lists in the feeds are somewhat aggressive, like one I enabled stopped my son from doing his school work on google docs. He was quite happy about it, but I soon solved that problem and had to get back to his school work.
Hopefully this points you in the right direction. I work in the industry and everything works just fine, until you enable security, the more you enable, the more it becomes a house of cards. Its a balance between safety and security and it just not being useful anymore. Finding the balance is key. Everyone is different.
-
Hey @horse2370 , thanks for the reply!
Okay I took some more screenshots of my setup. As they say "The plot thickens".
Before all of that, I had taken the precaution to make sure pfblocker was disabled on DMZ, here's a screenshot of the IP configuration page. As you can see, pfblocker is selected only on LAN (my main home network). DMZ is not selected :
Also under Rules > DMZ I do not see any pfblocker rules (as expected!):
But still, this morning, the FW logs are filled with blocked connections on DMZ. Today, however, there's all kind of destination IP's in there (WAN, Amazon servers, Zscaler, etc...):
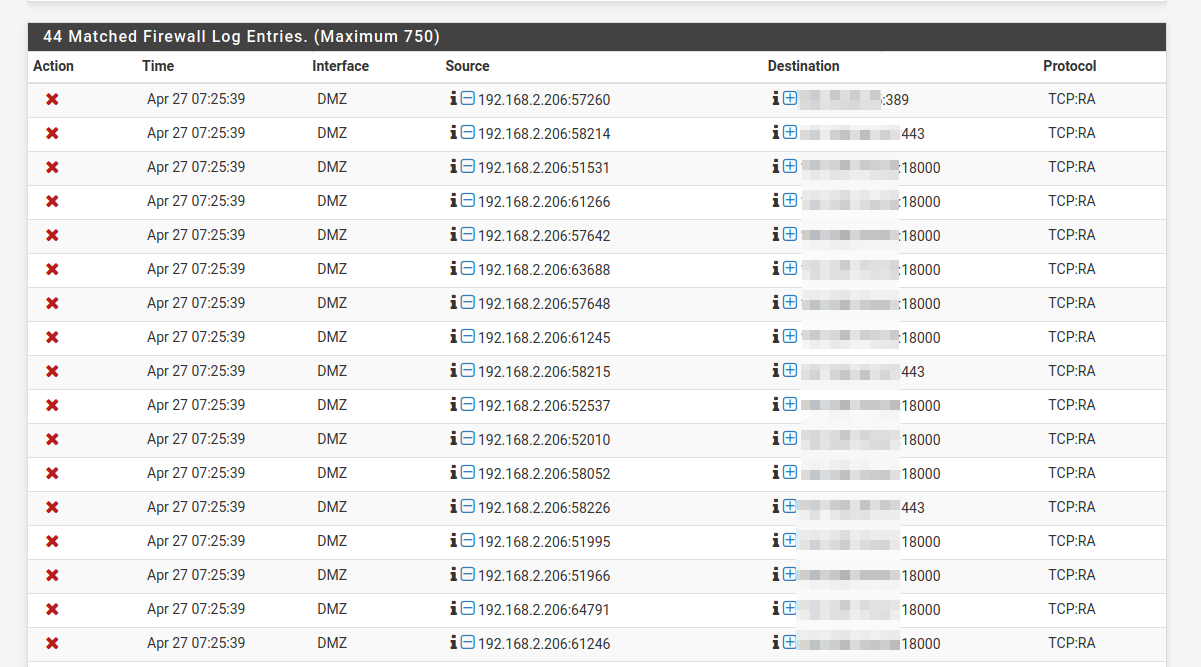
All (literally ALL) of these blocked connections have the following reason:
The rule that triggered this action is: @9(1000000103) block drop in log inet all label "Default deny rule IPv4"Until I sort this mess out, I will have to either commute to my office or physically bypass pfsense completely and connect the laptop directly to the cable modem.
Any idea of what's going on? I know these "TCP:RA" or "TCP:PA" could be asymetrical packets.... I am 99.9% sure I never had this before. Could my ISP be doing some sort of f*ckery with my connection?
-
@pftdm007 said in Bypassing DNSBL for specific IPs:
The rule that triggered this action is:
@9(1000000103) block drop in log inet all label "Default deny rule IPv4"Most easy solution : stop login the hits on the default block rules. (see Log > Settings )
Your 192.168.2.206 is a device that lives on DMZ, a VLAN.
Take it out of the VLAN to bypass "smart switch issues".
On the device, find why these "TCP:RA" or "TCP:PA" are send .... Is it a Wifi connected device ?Probably not a pfBlockerNG-devel issue. Disable pfBlockerNG-devel and these hits continue ?
-
@Gertjan said in Bypassing DNSBL for specific IPs:
Your 192.168.2.206 is a device that lives on DMZ, a VLAN.
Correct. So is my work cell phone. Same issue with my cell phone.
@Gertjan said in Bypassing DNSBL for specific IPs:
Take it out of the VLAN to bypass "smart switch issues".
OK will try to connect the laptop to a non-VLAN subnet, but in the meantime, all of my other computers/servers/networked printers, are all on LAN which is also a VLAN, and I have absolutely zero issues with any of them. Side note: everything is a lot more severe on LAN (more pfB/DNSBL lists, Snort, etc...)
@Gertjan said in Bypassing DNSBL for specific IPs:
On the device, find why these "TCP:RA" or "TCP:PA" are send .... Is it a Wifi connected device ?
My employer's IT are investigating on the device to see if everything is properly setup & running.... In the meantime, yes the laptop & cell are wifi connected to DMZ, but I already tried connecting the laptop via wired connection, same issues. That kinda eliminates possibilities of issues with my WIfi access point.
@Gertjan said in Bypassing DNSBL for specific IPs:
Disable pfBlockerNG-devel and these hits continue ?
When they release the laptop, I will reconnect to DMZ, and try. I am pretty sure I already tried, but I've done so many things in the last few days I am getting a bit confused so I will retry to make sure.
-
guys what is wrong in my custom config since all LAN subnet 192.168.1.0/24 is being filtered by DNSBL ? I want some computers (192.168.0.1 and 192.168.0.2) to be excluded from DNSBL filtering.
server:
access-control-view: 192.168.0.1/32 bypass
access-control-view: 192.168.0.2/32 bypass
access-control-view: 192.168.0.0/24 dnsbl
view:
name: "bypass"
view-first: yes
view:
name: "dnsbl"
view-first: yes
server: include: /var/unbound/pfb_dnsbl.*conf -
These are 'clauses' in the (unbound) config file :
server: .... view: ...They are recognised by the terminating ':'.
"view:" clause can exists multiple times.
"server:" clause can't (there is only one server)Or, you have two of them.
This one is thrown in by the pfBlockerNG-devel package :
server: include: /var/unbound/pfb_dnsbl.*confThat is, you edited it. pfBlockerNG-devel package added this :
# Unbound custom options server:include: /var/unbound/pfb_dnsbl.*confThis is the same thing :
# Unbound custom options server: include: /var/unbound/pfb_dnsbl.*confSo, I guess this would work for you :
server: include: /var/unbound/pfb_dnsbl.*conf access-control-view: 192.168.0.1/32 bypass access-control-view: 192.168.0.2/32 bypass access-control-view: 192.168.0.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yesBtw : Use this when you start to add unbound specific manual settings. It's part of the RTFM concept ;)
Be careful : if
server: include: /var/unbound/pfb_dnsbl.*confcan't be found by pfBlockerNG-devel when it start, it will automatically add such a clause again into the unbound config file.
Remember, pfBlockerNG-devel parses as a program, not as a human ^^
Adding a seconds "server:" clause probably breaks the unbound config .... -
@Gertjan thanks. removing server: clause solved problem. I hope pfBlockerNG-deve won't add it again
-
Hi, been reading through this post but confused. I want to allow my IP 192.168.1.16 to bypass the blocker, is this correct?
Go to Services/DNS resolver/General Settings then in Custom options write:
server:include: /var/unbound/pfb_dnsbl.*conf access-control-view: 192.168.1.16/24 bypass access-control-view: 192.168.1.16/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes -
server: access-control-view: 192.168.1.16/32 bypass access-control-view: 192.168.1.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes include: /var/unbound/pfb_dnsbl.*confThe changes are: -
access-control-view: 192.168.1.16/32 bypassMatches the host you want to bypass with a /32 to make it ONLY match the single address.
access-control-view: 192.168.1.0/24 dnsblMatches the rest of the subnet, assuming a 255.255.255.0 mask.
Moved the include: to the "dnsbl" view
-
Thanks very much! Is it possible to something more fine grained. Like allow 192.168.1.16 to www.blockedwebsite.com?