Pfsense Block access external Public FTP
-
OMG... Dude did you edit the default lan rules away from any any?? If so then yeah your going to have problems. And your going to need more than just 21.. 20 would NEVER be used its a source port in active mode.
But the server in passive is going to give you some random high port to talk to... So post up a screen shot of your LAN rules!!!
I can not help you without some information.. How many times do I have to ask to see your logs? If your LAN rules are not any any then yes you need to show them.. I stated 3 days ago that if you had messed with your lan rules doing any blocking you could have problems with passive. If you would of read the link I gave you goes over what happens in the data channel... So if you are limiting lan to specific ports via rules other than any any then YES you going to have a bad day trying to ftp in passive mode.
That thread is from 2014... Yeah I will admit users have problems with ftp... Ftp should of been killed off 10 years ago.. It is NOT secure, it sucks through NAT, do I need to go on.. sftp is secure, its 1 port so no issues through nat. There are both free clients and servers for every OS.. There is ZERO reason to be still using ftp other than complete lack of caring on the point of the person running the server for security...
-
Hello
Here is my Lan Rules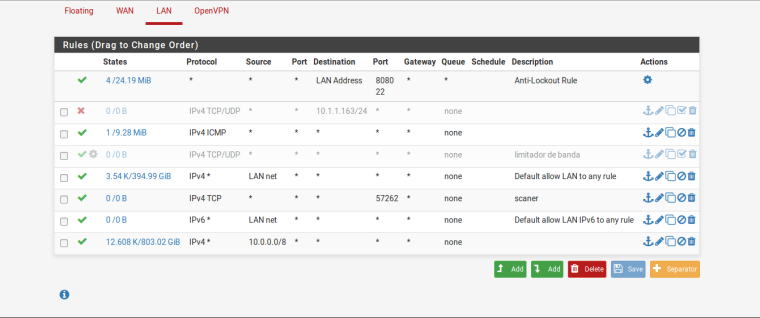
Yes, you right about sftp. I did read about it. But, I need to study how to server config and pfsense config. Then, enable sftp on our network.
But, remember, the Datasus FTP is external service that works with web service database. It is not our ftp server. Then, sad, but I need to do that works fine.I would like to thanks your patience and help until now.
Douglas
-
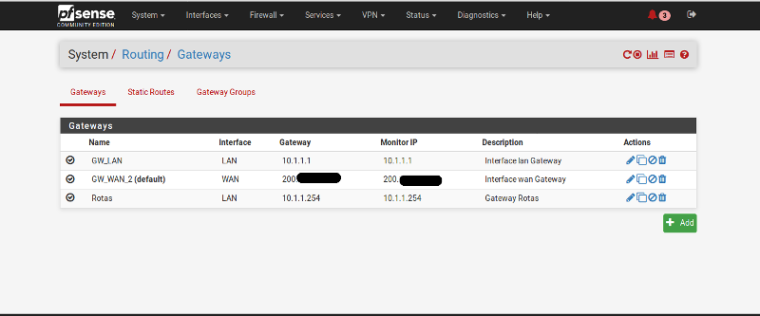
so you have downstream networks? Why do you have that 10/8 rule? And your icmp rule is any for source network would be pointless unless you have downstream networks.
And really is pointless anyway since you have 10/8 rule - unless you have other networks other than 10/8?
So if your client is on lan net or in 10/8 your rules are any any and should have no issues doing passive ftp to server outside.
Did you mess with outbound nat? Your using lan net as your transit to these downstream networks? Maybe you have a asymmetrical routing problem... Please draw up your network and where are you clients in your network that your trying to ftp with. Do they use pfsense as their gateway?
Your not routing any traffic through a vpn are you?
Do you have any rules in your floating tab?
BTW your scanner rule is pointless unless some downstream client is not in lan net or 10/8
-
@johnpoz said in Pfsense Block access external Public FTP:
hello
so you have downstream networks? Why do you have that 10/8 rule? And your icmp rule is any for source network would be pointless unless you have downstream networks.
We have 43 networks point route inside pfsense:
For exemple:
10.10.11.254
10.10.34.254
10.10.29.254
10.10.30.254
.......
the internet is provide by:
concentrator Internet MPLS
Dedicated InternetAnd really is pointless anyway since you have 10/8 rule - unless you have other networks other than 10/8?
So if your client is on lan net or in 10/8 your rules are any any and should have no issues doing passive ftp to server outside.
Did you mess with outbound nat? Your using lan net as your transit to these downstream networks?
Yes, we are using lan net to transit on these downstream
Maybe you have a asymmetrical routing problem... Please draw up your network and where are you clients in your network that your trying to ftp with. Do they use pfsense as their gateway?
Yes, they are using pfsense for gateway. Each sector have modem (or circuit point) route to pfsense
Your not routing any traffic through a vpn are you?
We have some users access vpn through our pfsense because we have a NAS.
Do you have any rules in your floating tab?
No, there are not rule floating tab.BTW your scanner rule is pointless unless some downstream client is not in lan net or 10/8
Thanks for now
-
@doguibnu said in Pfsense Block access external Public FTP:
Yes, they are using pfsense for gateway. Each sector have modem (or circuit point) route to pfsense
So there are client in lan net.. Do you have host routing on them, if not then your asymmetrical if they are talking to any downstream network.
So if client in lan wants to talk to 10.x network he sends traffic to his gateway pfsense in the lan net. Pfsense then sends the traffic to some downstream router, the return traffic will not go to pfsense.
Please DRAW your network, and what what is your outbound nat rules. Is lan net also a 10.x address?
And again please post a LOG of filezilla client behind pfsense failing to connect... So we can see what gets sent in the passive command.
-
Hello
@johnpoz said in Pfsense Block access external Public FTP:
So there are client in lan net… Do you have host routing on them, if not then your asymmetrical if they are talking to any downstream network.
So if client in lan wants to talk to 10.x network he sends traffic to his gateway pfsense in the lan net. Pfsense then sends the traffic to some downstream router, the return traffic will not go to pfsense.
Please DRAW your network, and what what is your outbound nat rules. Is lan net also a 10.x address?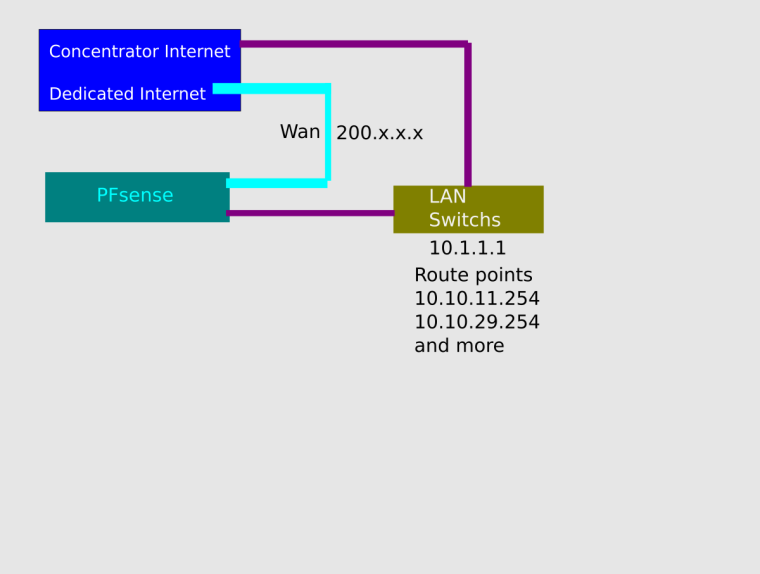
And again please post a LOG of filezilla client behind pfsense failing to connect… So we can see what gets sent in the passive command.
Here log of filezilla. I disabled that wrong wan rule that you tell me, and today now, look: (in grey text color)
Status: Resolving address of ftp.datasus.gov.br
Status: Connecting to 189.28.143.164:21...
Status: Connection established, waiting for welcome message...
Status: Insecure server, it does not support FTP over TLS.
Status: Logged in
Status: Retrieving directory listing...
Status: Directory listing of "/" successful........How today works?............
owwwww!!
Thanks
-
How it works today - because like I said there is NOTHING to do if your doing passive..
And you didn't show the detail log so can not see what the passive command was and or even if your doing active and the ftp helper package is doing the work for you.
So you have downstream networks. Then there should be NOTHING on your lan - it should just be a transit network.
edit: BTW these are normally never good news... What are you alerts/errors - looks like you have 3 of them.