How to generate a wildcard certificate with ACME and AWS Route53?
-
I am trying to create a wildcard certificate but somehow it seems that this is not documented well.
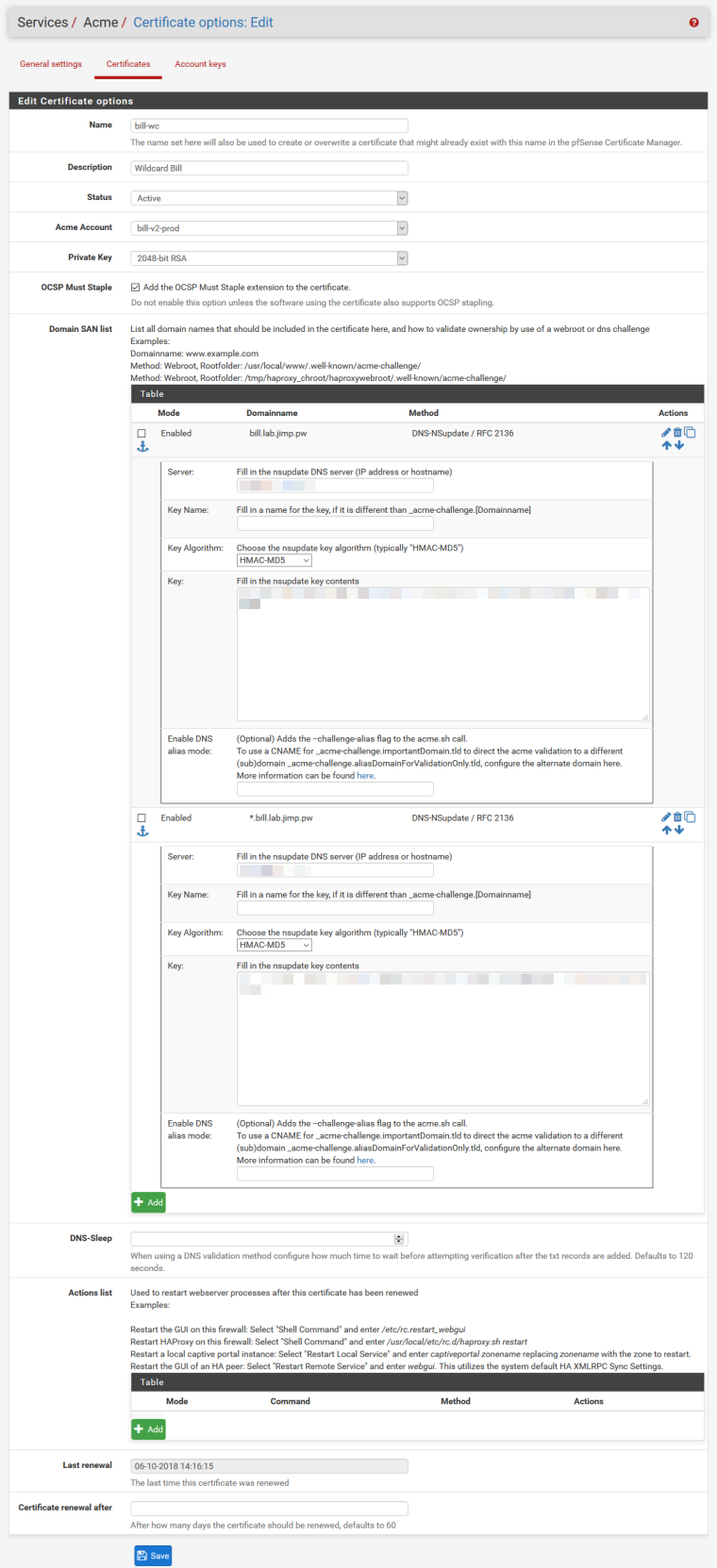
I read that I need to specify both example.com and *.example.com so I did at in http://s3.sbarnea.com/ss/q.sbarnea.com_-_Services_Acme_Certificate_options_Edit_2018-06-05_22-21-40.pngAll went find until the near end of the script, which have a bit cryptic error:
IMPORT CERT ...
update cert![Tue Jun 5 20:29:06 UTC 2018] Reload success
[Tue Jun 5 20:28:56 UTC 2018] Invalid domain
[Tue Jun 5 20:28:56 UTC 2018] invalid domain
[Tue Jun 5 20:28:56 UTC 2018] Error rm webroot api for domain:dns_aws
[Tue Jun 5 20:29:01 UTC 2018] Response error:
SenderSignatureDoesNotMatchThe request signature we calculated does not match the signature you provided. Check your AWS Secret Access Key and signing method. Consult the service documentation for details.
[Tue Jun 5 20:29:01 UTC 2018] Error rm webroot api for domain:dns_awsI have no idea what is the meaning of these errors.
-
Did it validate and import the certificate OK? Or did that stop it from working?
I don't have a way to test route53, only the nsupdate method, so I'm not sure if route53 does the right thing with the key names for the DNS check there. It should end up just using
example.comfor checking the DNS on both those entries. -
I was able to make it work by adding only one SNI: ".example.com". If both "example.com" and ".example.com" are present in the list, it will fail. I guess this is related to the fact that verification records are to be added and removed on the same domain for both, confusing the client.
I ended up doing this because this is what it was suggested in the the blog post I read. I hope docs will be updated to include clean info on how to deal with this, so it would save others time.
-
@jimp Clearly the documentation page from https://www.netgate.com/docs/pfsense/certificates/acme-wildcard.html is incorrect because the UI does not accept you to introduce *.example.com.
The doc states that you need to introduce two SNI entries which is not possible.I ended up creaing https://redmine.pfsense.org/issues/9020 -- Fell free to watch the bug and comment on it.
-
You have some kind of configuration error. I tried it again exactly as stated on the page and it works.
And stop spamming the same false information across multiple threads.
-
-
This post is deleted!