[Help] Open VPN Client to Site - force client's traffic through specific network
-
Hi everybody,
I'm Phuoc, I'm a newbie here and I'm glad to see you.
I need your help with my below diagram:
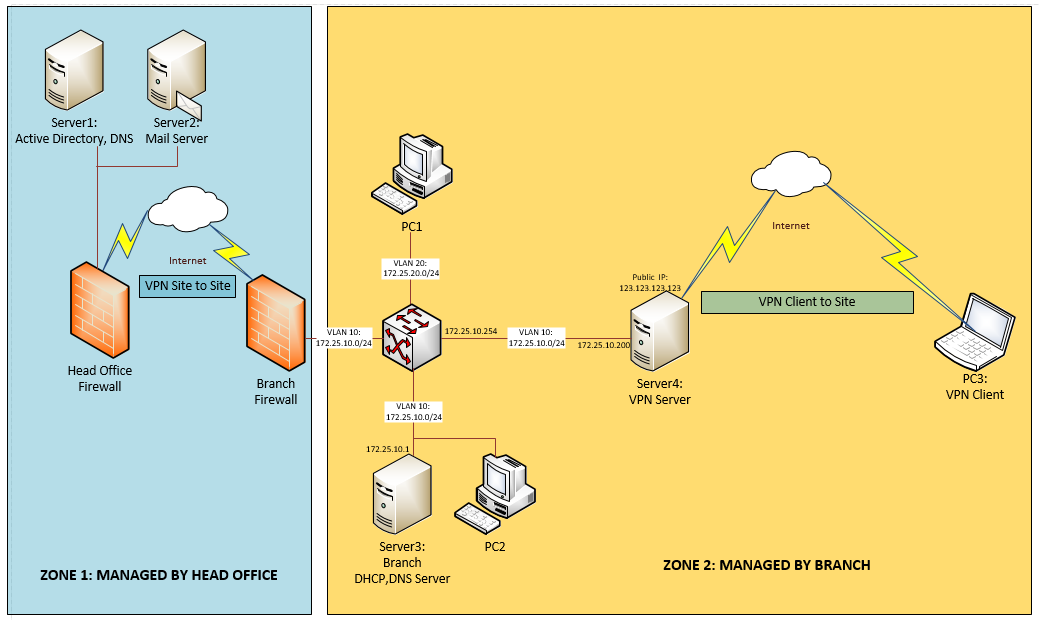
I have a branch network which connected to headquarter via VPN Site to Site. Both firewalls are managed by head office and branch office cannot access to configure anything. All server and PCs in VLAN 10 and VLAN 20 joined to Active Directory in head office and go to the internet, access the email server through VPN site to site.
I'm trying to build a VPN Remote Access Server for outside mobile client ( already joined to AD) can connect to the branch office and access the mail server like a branch office LAN's member.
Server 4 is VPN remote access server which I'm trying to build. It has two NICs, NIC01 is connected to VLAN 10, NIC02 has a public address and directly connected to the internet.
Last week, I was trying to build server 4 by installing windows server 2012 r2 and enabling remote access and routing service. Server 4 gave PC3 an address in VLAN 10 but both server and client could not access to head office because they did not have the gateway. I could not assign 2 default gateways to NIC1 and NIC2 on windows server. You know if I assigned a default gateway to NIC1, NIC2 could not access the internet to provide a VPN connection to PC3, if I assigned a default gateway to NIC2, NIC1 could not access to the head office network. So I was failed with windows server.
Today, I continued to try by installing pFsense on server 4. I already installed OpenVPN with tunnel network 192.168.100.0/24. PC3 was connected via VPN and got tunnel address 192.168.100.2/24. It could access the machines on VLAN10 but still could not access the head office network to use email. Is there any routing method to force PC3's traffic through the branch-head office's network or is there any way to force OpenVPN to assign VLAN 10 address to PC3 when it connected via OpenVPN?
Please give me any advice on this case. I'm sorry for my poor English.
Thanks in advance! -
If you are not able to modify the VPN between head quarter and branch you cannot solve that by routing.
So you have only two options:- Using NAT to translate the source address of packets from PC3 to the VLAN10 address of server4.
- Switching the OpenVPN access server into TAP mode and bridging VPN clients to VLAN10.
By using the first option, each client access the internal networks with the IP of pfSense.
The second option integrates VPN clients into VLAN10 and maybe works better in conjunction with AD, however it causes more overhead on the VPN and is more difficult to set up. -
@viragomann
Thank you for your help.
I would like to try the 2nd method first but with pFsense 2.4.3, I cannot find OpenVPN TAP mode and bridging package, is there a way to configure it manually? -
@viragomann
There is one thing I don't understand. Server4 has 2 gateways, 1 on WAN interface and 1 on LAN interface. But just WAN interface has default gateway, it means traffics through this interface will be routed to any network outsite WAN but I'm not sure about LAN interface, I cannot configure 2 default gateways at the same time. I don't know that traffic through LAN interface will be routed to any network behind LAN network or not? -
@ntphuoc1990
Do not add a gateway in the LAN interface settings.
The branch firewall is to be added as gateway in System > Routing. Then add a static route for the head office network using this gateway.In the OpenVPN server settings at "device mode" you can select "tap - Layer 2 Tap Mode".
As far as I know, you have to assign an interface to the OpenVPN server instance in Interfaces > Assignments additionally and also add a bridge where you add that ovpn interface and the LAN (VLAN10) interface as members.
I'm not familiar with the tap mode, maybe you can find a guide in the web. -
@viragomann said in [Help] Open VPN Client to Site - force client's traffic through specific network:
@ntphuoc1990
Do not add a gateway in the LAN interface settings.
The branch firewall is to be added as gateway in System > Routing. Then add a static route for the head office network using this gateway.In the OpenVPN server settings at "device mode" you can select "tap - Layer 2 Tap Mode".
As far as I know, you have to assign an interface to the OpenVPN server instance in Interfaces > Assignments additionally and also add a bridge where you add that ovpn interface and the LAN (VLAN10) interface as members.
I'm not familiar with the tap mode, maybe you can find a guide in the web.Dear Viragomann,
I aready added branch FW's address as gateway but I could not add a static route for the head office using that gateway because I don't know which specific networks or IP address are availlable behind the branch firewall.
In this situation, I think a default route to branch FW address makes traffics from LAN can reach all network behind the branch FW.
But if I add a default route to branch FW, how can OpenVPN go to the internet through the WAN interface? -
OpenVPN clients should go to internet via their own default gateway. Upstream traffic shouldn't be routed over the VPN, but only traffic destined for internal addresses.
You should know, which network are to be routed to the head office. If you have host names which you need access to use nslookup or dig to resolve them.