Isolation IPs from the wired network of the same subnet
-
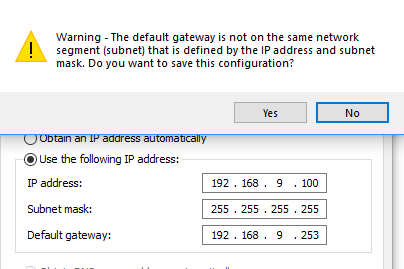
bullshit is a good word to describe such nonsense for sure. Shit windows and many os'es would bitch at you trying to set a gateway when you have a /32 bit mask. Since any gateway you set would be outside your mask.
That fact that you can use the internet, ie talk to your gateway which is outside your mask - shows you that you can talk to other devices ;)
So why would you think you could not talk to other devices on the same wire?
-
What device is actually providing the WiFi?
Even with most dumb switches (as many pass VLAN tags without messing with them) you should be able to tell the the WiFi AP to use a different network and VLAN for the traffic back to the pfSense box where you can ensure isolation. Or plug it into its own LAN port on the pfSense box.
-
As others have said, the proper way to do this is at layer 2. In the switch or in the wifi gear.
MikroTik might have some mechanism for this, considering their attempted penetration into the WISP markets but, in some form or another, it will boil down to layer 2 isolation.
If you have host A on 192.168.1.100/24 and host B on 192.168.1.101/24 and both are on the same local network, the only way they cannot communicate is isolation at layer 2.
If you can come back with more details about what Mikrotik is actually doing we might be able to help develop an alternative. But it will likely be in your switching layer, not at the firewall itself.
-
Indeed, I have a bit of an isolation hack on my own network as I share it with some friends.
All four ports on pfSense are bridged and I enabled packet filtering on that bridge. I then have a firewall rule that allows my friends static IPs to only talk to the firewall itself, so while some broadcast traffic might slip through (I only have it blocked in one direction) they can't accidentally ChromeCast to my TV like they did once.
But honestly, if all you need is full isolation then its just easier to have it on a completely different LAN. Although that will not isolate the WiFi clients from each other, that has to be done in the WiFi access point itself.
-
Depends. Layer 2 isolation is a valuable tool especially in public access environments such as hotels, etc.
That said, any leverage of a pfSense bridge to accomplish the task is likely pretty far from an optimal solution.
-
Agreed, it was just convenient for my setup as its not vitally important my friends are blocked from the LAN, it just prevents little mishaps like described.
After all, if they change devices they will still get an IP from the dynamic pool which will bypass my blocks (although I might add those to the list) or they specify a static IP which would almost DEFINITELY bypass the rules.
Although I have the added benefit of knowing not only that those people know sod-all about networking, they wouldn't even bother to try learning about it either. I can't even convince them to connect to 5Ghz over 2.4Ghz as the whole concept of it not "just working" freaks them out. ;)
For true isolation, VLANs or just having the AP into its own ethernet port with its own network range is key. There is in fact no logical reason to HAVE them on the same subnet in the first place.
-
But then you need isolation in the AP to keep them from each other.
We're not really talking about isolating subnets. That's done in the firewall.
We're talking about isolating hosts in the same subnet from each other, but not from the gateway or other necessary hosts.
-
Right, I got completely confused about what the OP was trying to achieve here.
-
He was/is trying to create isolation of devices on the same layer 2 by just telling them their mask is /32 - which as we all know is just borked.
-
A /32 mask is used by some routers to designate an interface, rather than a network.
@alex-atkin-uk said in Isolation IPs from the wired network of the same subnet:
Even with most dumb switches (as many pass VLAN tags without messing with them)
No switch should touch the VLAN tag, except a managed switch configured for that VLAN. Dumb switches should pass VLAN tags untouched. The exception would be ancient gear that's incapable of passing a frame with both a VLAN tag and full 1500 byte payload, as it would be too large for it to pass. In that case, the frame should be dropped entirely, not passed on with anything mangled.
-
@derelict said in Isolation IPs from the wired network of the same subnet:
We're talking about isolating hosts in the same subnet from each other, but not from the gateway or other necessary hosts.
The only way I'm aware of to do that is a firewall running on the device, that's capable of filtering on MAC addresses. The firewall on OpenSUSE is capable of that.
-
Some switches have a Protected / Private VLAN edge port as John previously mentioned.
Features of a protected port: Protected Ports provide Layer 2 isolation between interfaces (Ethernet ports and LAGs) that share the same VLAN. Packets received from protected ports can be forwarded only to unprotected egress ports. Protected port filtering rules are also applied to packets that are forwarded by software, such as snooping applications. Port protection is not subject to VLAN membership. Devices connected to protected ports are not allowed to communicate with each other, even if they are members of the same VLAN. Both ports and LAGs can be defined as protected or unprotected.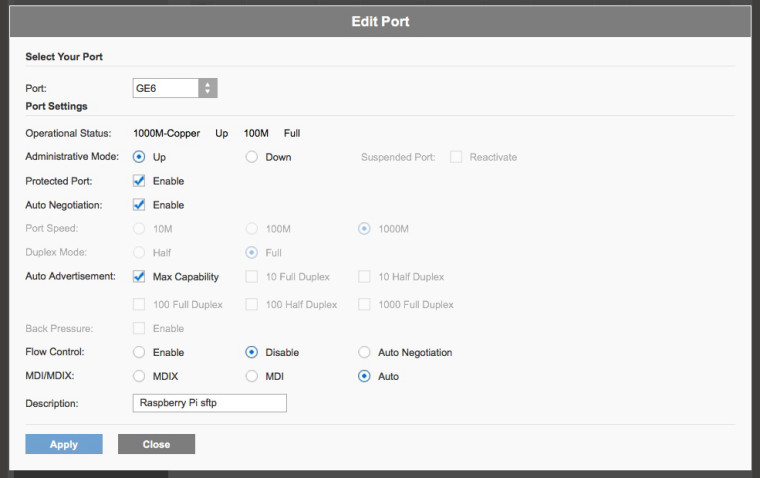
-
Right. That is Cisco's private vlan edge. Brocade calls it uplink ports which makes all non-uplink ports on a VLAN isolated from everything but the configured uplink ports. This can be more flexible than cisco's protected ports because it is configured per-VLAN. Some switches have port isolation built in. Some can do it with asymmetric VLANs. The SG-3100 and XG-7100 can do it (on the built in switch) using a similar method.
Then there are true private VLANs which are harder to implement because to fully support it everything has to support it on VLAN trunk ports (APs, etc). It gets really complicated when you start trunking switches/gear together.