Can't forward VPN traffic to web server running in LAN network
-
Hi,
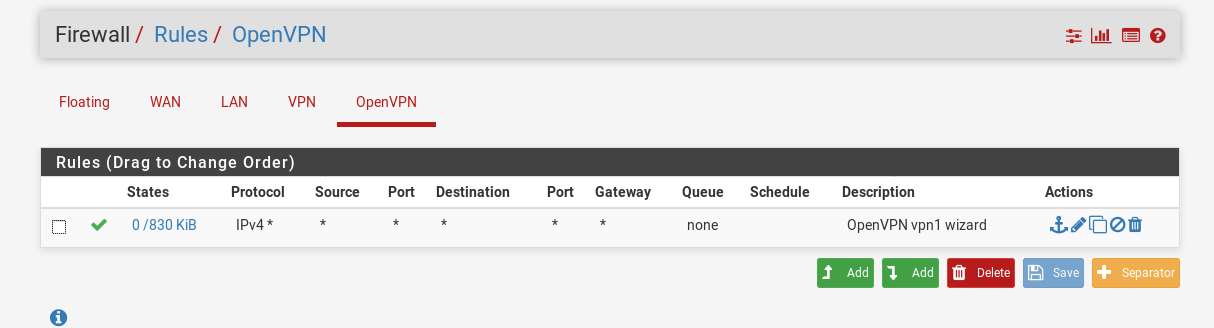
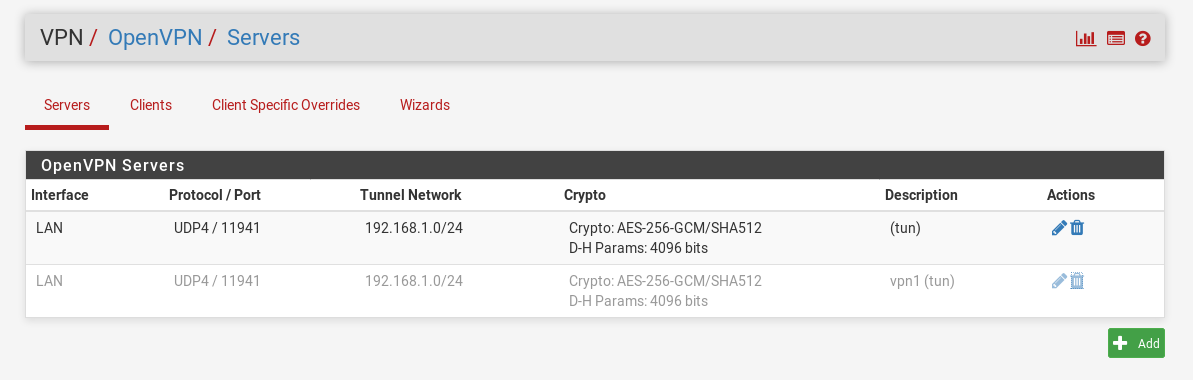
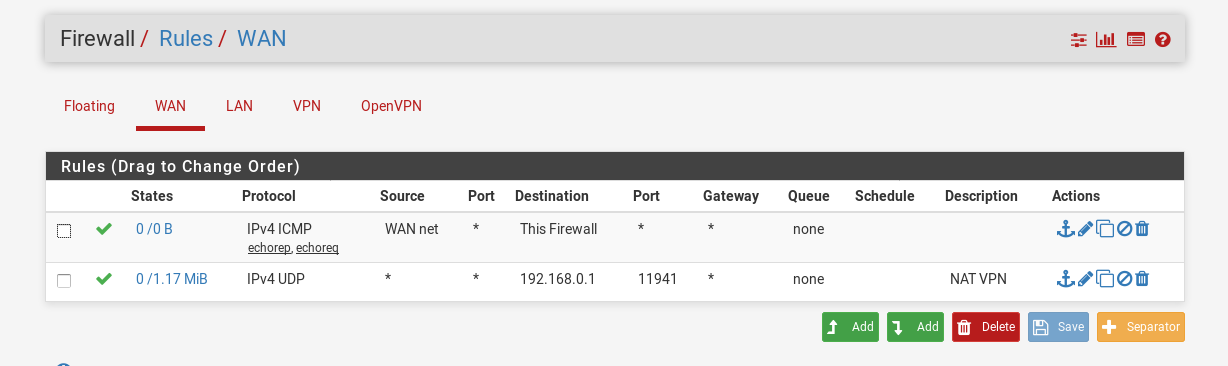
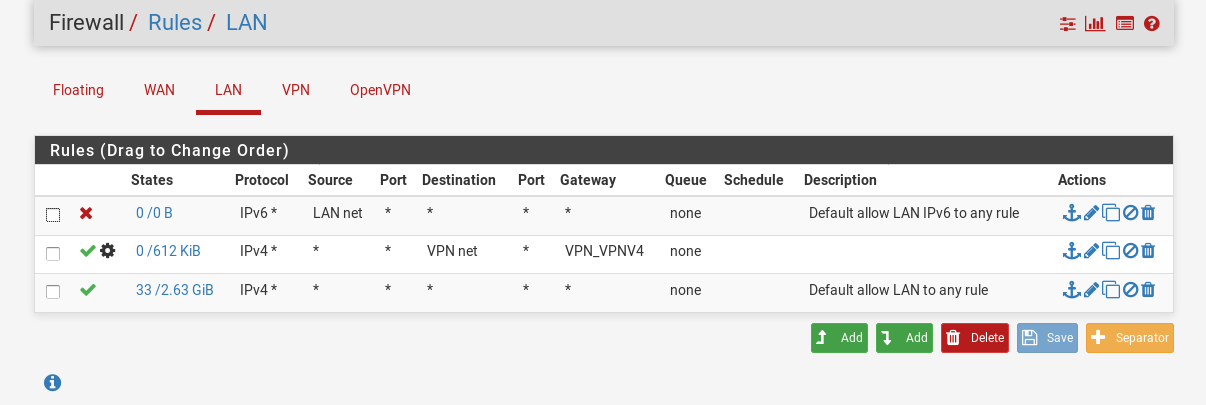
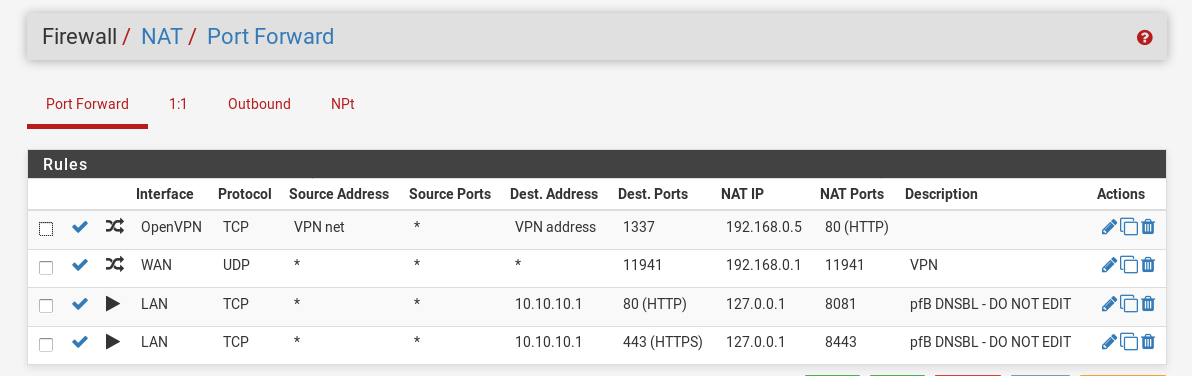
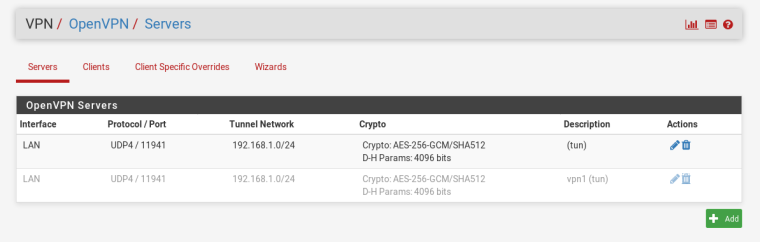
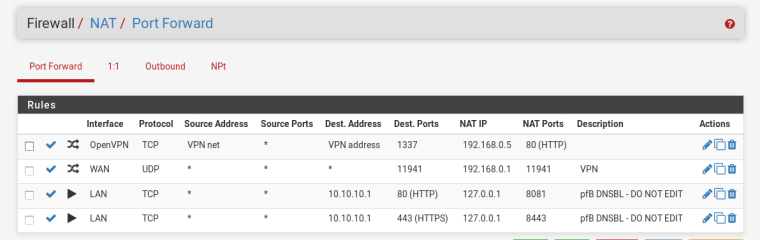
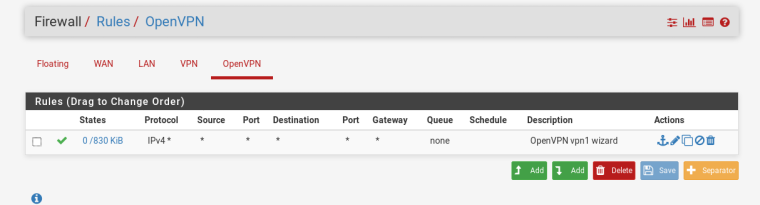
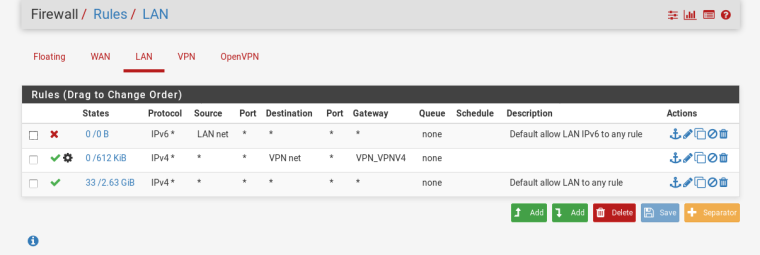
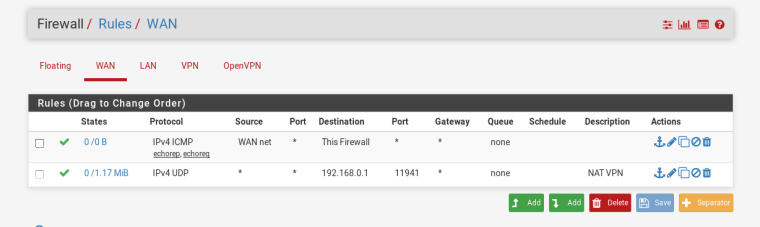
I'm running PfSense in a VirtualBox on my Debian host system and try to route traffic from my VPN to a web server running in my LAN network my goal is to access it over a specific port on my VPN Gateway and I can't find out what is wrong with my configuration. Another maybe corresponding problem is, that clients can reach each other by pinging inside my VPN network but streaming (for example with Iperf) doesn't work, but stream from PfSense to the clients does work fine.Here you can see my configuration:
And the clients view via ifconfig:
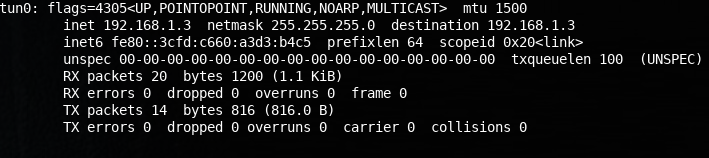
My clients are all manjaro linux systems tested with 416, 417 and 418 kernel.
Thanks in advance and ask me if you have any questions. -
I guess pfSense is not the default gateway in the LAN.
So assuming the virtual LAN interface is bridged to your LAN network, you can solve it by adding a static to the web server for the VPN tunnel network pointing to pfSense LAN address. -
I'm sorry but I don't really understand what you mean, I use pfsense as gateway for my lan network and I'm not using any VLAN. I've set the openVPN interface for the forward rule so I think pfsense should be able to route the requests. As additional information I should say the web server runs inside a container on the host system of my server and has the IP 192.168.0.5 my aim is to reach it inside my VPN network by calling 192.168.1.1:1337.
-
So the virtualized pfSense is the default gateway in the LAN and on the corresponding web server as well?
So why don't you access the web server directly?
If the route to LAN is pushed to the VPN client, there should be no need for port forwarding. -
@viragomann I've tried that before, but for any reason I can't find any lan device then, and this doesn't solve my problem that the clients can't stream data to each other.
-
What are addresses VPN net and VPN address If you assigned an interface to the OpenVPN instance then set addresses and gateways on that interface you did it wrong.
Why port forward at all? Why not just directly route to 192.168.0.5?