VPN blocked?
-
It seems I am having the same issue. I am currently using AIRVPN provider and I cannot open this forum.
Is it possible that the AirVpn ip addresses servers are blacklisted?
Thanks -
Spammers use VPNs....so they all get blacklisted bit by bit.
-Rico
-
Fair enough even if criminals use cars, mobile phones, computers but all of those can still be bought
 ... I am a newbie and i am wondering if someone would be able to tell me if (and how eventually) I can bypass the VPN connection to connect to the pfsense forum without having to change network.
... I am a newbie and i am wondering if someone would be able to tell me if (and how eventually) I can bypass the VPN connection to connect to the pfsense forum without having to change network.
Thank you very much -
Depending on your VPN Setup it should be no problem to policy route by setting destination IP to 208.123.73.199 (this forum) and choosing your default gateway (Advanced options in the Firewall Rule).
-Rico
-
@zapoteknico said in VPN blocked?:
Fair enough even if criminals use cars, mobile phones, computers but all of those can still be bought
 ...
...Right but if you choose to drive a car that was just used in a bank robbery you'll get pulled over.
-
Hello Rico.
Thank you very much.
I understand what you say however I have no understanding of how I would be able to achieve that in pfesense.
I understand i might be asking a lot but any help in pointing me to how to create thoae rules would really help -
@derelict indeed... However the difference here is the brand of the car, not exactly the same car...if a Mercedes is used in a bank robbery, not all Mercedes drivers will be stopped

-
You create this Firewall Rule for the Interface you want to bypass forum.netgate.com (typically LAN) and put on top of your Rules:
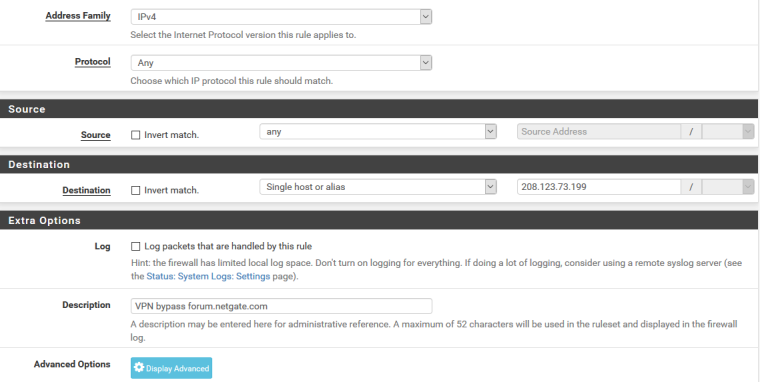
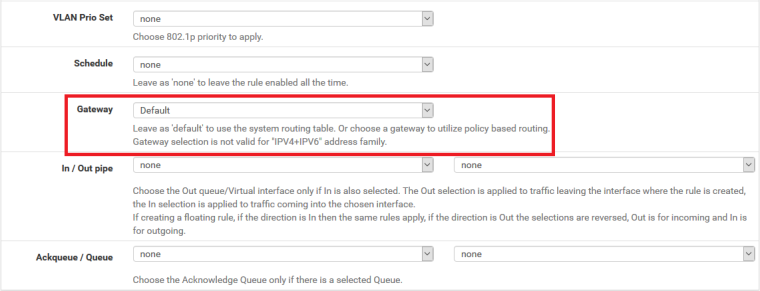
hit Display Advanced and set your ISP Gateway (or default if your ISP GW is still the system default):
-Rico
-
If your going to policy route, make sure your not pulling routes from your vpn service - most of their crap guides want you to pull their route so they are default, and most of them mistakenly tell you to do manual outbound nat, etc.
-
Thank you very much for the help but i am surrendering.
I understand half of the things you talk about and I think i have rules setup that makes impossibile to create those exemptions (followed the above suggestions but it didn't work)
I don't want to bother anyone more than needed as I am going to reconfigure everything tomorrow (getting a new mini pc)Thank you :)
-
This post is deleted!