Two gateways the same box
-
I’m a pfsense noob, so don’t beat me up too bad.
I have a situation where I have two gateways on one box. One for default and one for PIAVPN.
I have and alias for computers I want to go through PIA and have a rule at the top of my lan for the PIAalias to go through the PIA gateway.
All that works fine as intended, but the problem I’m having is that devices that go out the PIA gateway can’t access device on the default gateway. I don’t want to add those devices to the PIA because then it’s the opposite where the default can’t access the PIA.
I’m sure I’m missing something simple, I’m learning a lot and having fun doing it.
My entire network is set up with static ips accept for the wife and kids devices and a few iot devices if that means anything.I guess what I’m asking is there anyway for all of my device to communicate when using the two gateways.
Pfsense 2.4.4
-
huh?? What is your question.. This is just gibberish..
edit: Ok that is better than PIA LAN GATEWAYS ;)
You need a rule ABOVE your policy route rule sending traffic out your vpn to allow access to what you want to allow access through that will use default routing of pfsense, ie other local networks, or anything you want to use your normal gateway vs the vpn.
-
Thanks, it posted while I was still trying to type. Sorry about that.
-
see my edit ;)
-
So above the aliasvpn rule I would need
LAN
Pass
Source PIA net
Destination LAN net.
Default gateway or PIA gatewayThanks.
-
If you have a pia net, local ie lets say 192.168.2/24 and you want it to talk to your lan net lets say 192.168.1/24 then on the pia net interface you would have that rule.. And the gateway would be just *
-
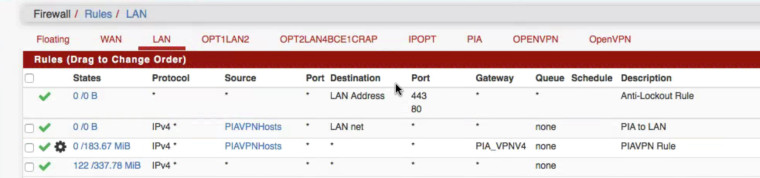
So basically these rules.

With the source and destination reversed on the PIA. -
If wondering about the setup LAN and LAN2 are bridged. 192.168.102.x/24
Crap is for internet of things and guests.
10.0.1.x/24
The rest are for up cameras and different OpenVPNs.
PIA is the interface for the PIAVPN client gateway. -
No!!!
When would PIA net ever be a source for traffic inbound into your LAN interface??
If you want device in your piavpnhosts to go elsewhere in your network, ie PIA net or ipopt, etc.. then you need a rule above the rule that sends them out your PIA_VPN4 gateway.,
-
If I put a rule above then the alias uses that rule, travels out the default gateway and bypasses the PIAVPN.
So I’m sure I’m just not following along closely enough.
Thanks for your patience. -
@johnpoz
I think Icgot you now. It’s taking me a while because I’m working remotely from my iPad with a poor signal.
But PIAAliashost (instead and PIAnet) to destination LANnet I think is what your telling me. I’ll try it. -
So this what I have and I think it I understand how it will work. The first rule will let the alias to lan net through the regular gateway. If it’s traveling outbound it will use the PIA gateway.
-
Thanks Jon,
I have set and applied similar rules on all the other interfaces and everything seems to be working as I had hoped.
I can now browse on my Mac while using a VPN and access my network devices that aren’t connected to the VPN.It was a lot simpler than every thing the big G kept pointing me towards. I was finding things referencing gateway groups which I new was wrong, gateway routes which I’m on the same router, and needing to set outbound NAT rules.
I new all of that wasn’t right though because it all resides in one box.I’m glad I asked here. Good response and also taught me a few things. If find anything not working I’ll let you know, but so far so good. But my virtual labs and NAS’s all connect fine.
Thanks again. -
So these PIAVPNHosts are in your LAN right?? They would never go through pfsense to get to other devices in LAN net.. Unless they are talking to stuff that is via the "bridge" you setup in pfsense? Between your lan and opt1lan2 interfaces?
Just at a complete and utter loss to why you would do this.. Do you really need to filter between these devices? If so why not just put them in a different network?
If you want them in the same layer 2 - then why would you just not connect them all to the same switch?
-
The problem I was having is some device on LAN are going through the VPN and some aren’t, the only way I could ping between them is if they were both either listed or not listed in the alias. It’s working now.
As far as my setup I know it’s probably a little over complicated, I seem to like over complicating things.
But LAN and LAN2 are bridged. LAN is going to the main switch for all of my LANs. LAN2 is going to a Time Capsule which is acting as my main wireless access point.
The Crap is a separate network completely going to an Airport Extereme providing another WiFi network access point for guests and the internet plug and play things. The guests Crap Network can’t access the Main network, but the main can access the Crap.I’m using a lot of my old equipment. My previous setup was a time capsule router in my office and an airport express in the center of the house. Using the Apple equipment was simple but a lot less was available. So I moved to pfsense because it seemed powerful and I’m a little familiar with FreeBSD I have FreeBSD and FreeNAS setups. With pfsense I’m able to do a lot more complicated networking stuff.
But besides that I just like to make things complicated :)..
-
Sounds more like a hodge podge of not knowing how to do something and having the wrong equipment for what you want to accomplish.
If you want to run multiple wireless networks on different vlans - then do that. Use a AP that supports vlans and switch that does as well.
I have multiple segments both wired and wireless, and have policy routing when I want it. Its simple straight forward and not overly complicated.. Bridging your routers interface to allow a connection that should just be connected to your switching infrastructure is a jury rig..
-
Sorry if I’m all over the place in my explanation, aside my setup I’ll just explain the issue I had.
Pfsense LAN 192.168.102.x connected to switch.
Switch connect to NAS and PC, worked perfect.
If I made the PC part of the PrivateInternetAccess alias I would lose the ability to connect to the NAS even though it was on the same network.
If I made the NAS Part of the PIA alias it would work but now the rest of my devices couldn’t connect to NAS.