pfsense behind a x3500 linksys modem-router [solved]
-
Hello,
My network cfg global string :
ADSL <> Modem-Router Linksys X3500 <> APU3C device with pfSense- behind the modem-router :
- APU3C device with pfSense
- D-Link DIR-655 router
- some ethernet devices
- some wireless devices
- (a) behind the pfSense device
- some ethernet devices
- some wireless devices
- (b) behind the DIR-655 device (just as info)
- some ethernet devices
- some wireless devices
My network settings :
-
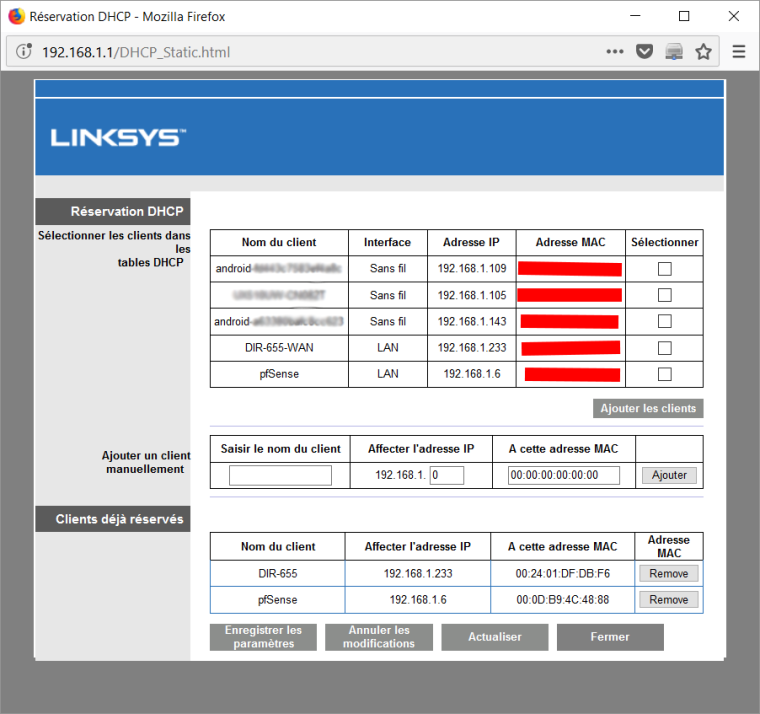
Modem-Router Linksys X3500 (LAN IP 192.168.1.x/24 + DHCP server On)
WAN IP address is reserved for the pfsense device (192.168.1.6)
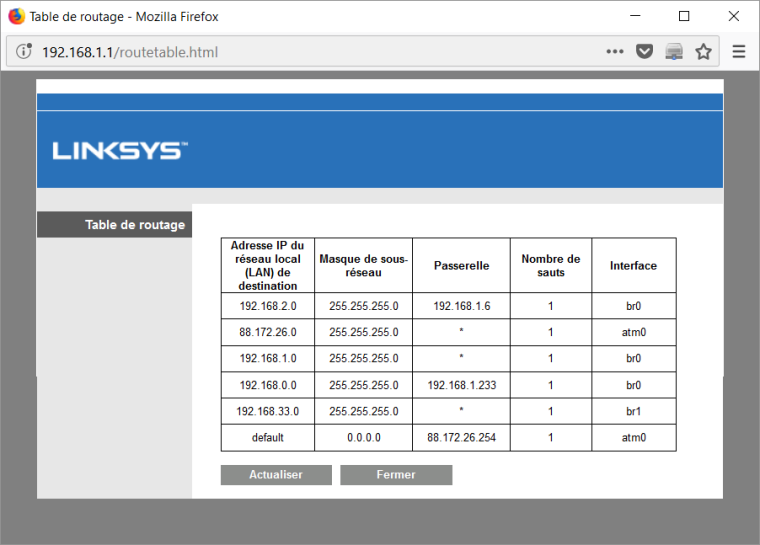
a route is set up to access on the LAN side of the pfsense device.
WAN IP address is reserved for the DIR-655 device (192.168.1.233)
a route is set up to access on the LAN side of the DIR-655 device. -
pfSense Device (LAN IP 192.168.2.x/24 + DHCP server On)
Gateway on LAN side IP : 192.168.2.1 -
Router DIR-655 (LAN IP 192.168.0.x/24 + DHCP server On)
Gateway on LAN side IP : 192.168.0.2
All that work :
- Internet Access : All devices (ethernet and wireless) from the 3 networks
- X3500 Web interface Access : All devices (ethernet and wireless) from the 3 networks
- pfSense Web interface Access : All devices (ethernet and wireless) from ONLY pfSense LAN network
- DIR-655 Web interface Access : All devices (ethernet and wireless) from ONLY DIR-655 LAN network
All that DOESN'T work (OBJECT of the post)
- pfSense Web interface Access : All devices from X3500 and DIR-655 LAN networks
- DIR-655 Web interface Access : All devices from X3500 and pFsense LAN networks
- All devices can't see them on All networks (Only inside their own LAN network) and ping fails.
I have tested by sending ping (as exemple from a device on the X3500 LAN side to the pfSense Gateway 192.168.2.1) and it doesn't work.
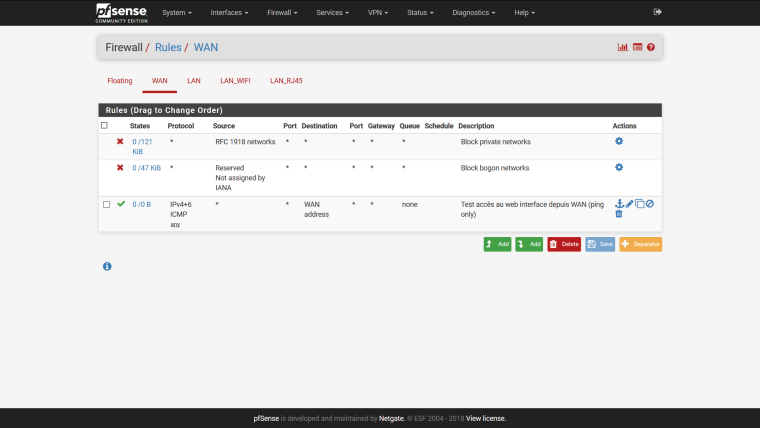
Rem. 1 : I have also added a Firewall rule (WAN) to Allow ICMP from any to the WAN address
Rem. 2 : Just for information, I can also access to a "web server device" behind the DIR-655 from internet.
My knowleges are a bit limited about network, so maybe there are some basic rules I don't understand well.
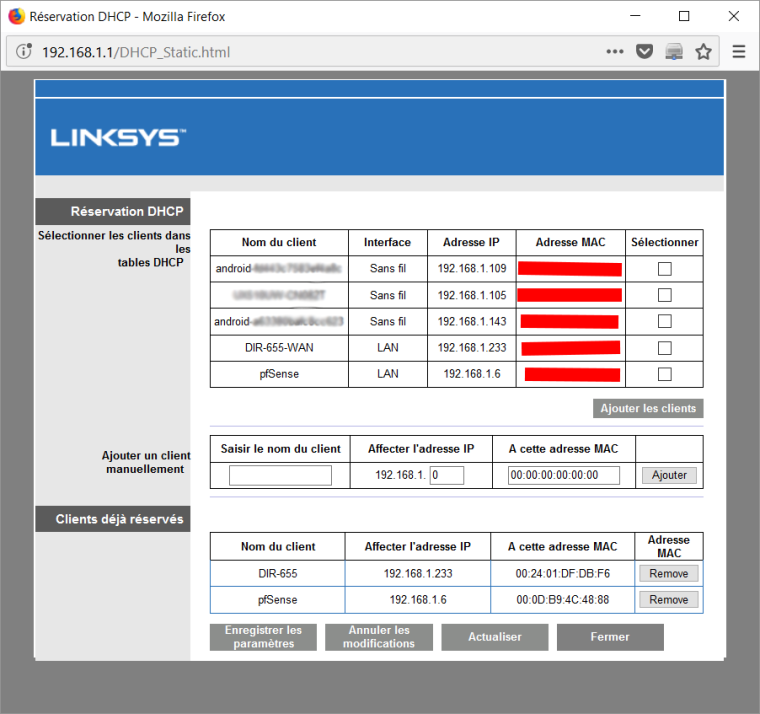
My X3500 settings - DHCP IP
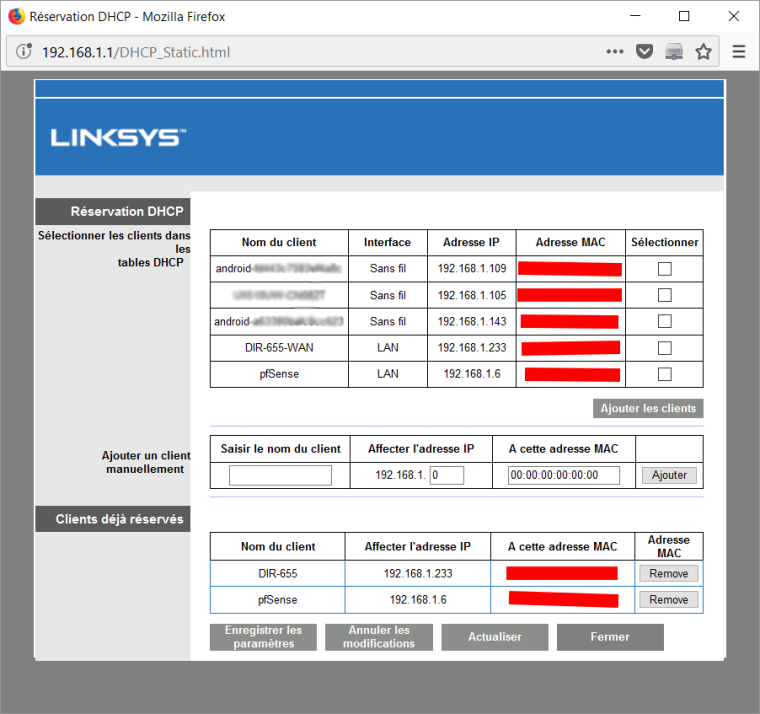
(bis) I can't remove the image file (Post content was flagged as spam by Akismet.com)
(bis bis) I can't remove the image file (Post content was flagged as spam by Akismet.com)
My X3500 settings - Routing Table
My initial goal was to replace the DIR-655 router (Only use as wireless Access Point) to solve the problem. But it seems I don't know how to do it, I have the same problems with the both router devices (DIR-655 & pfSense). I hope, I just need adding "some good setting".
Thanks in advance for your help.

-
The rule I have added (MAJ) In this first configuration, the RFC 1918 networks seems block the rule.
It seems I have solved my problem by applying the following rule instead of the first tentative above : Disable the RFC 1918 networks that prevent access by private IP from the WAN and allowing a 2nd rule to access to the pfSense web interface (and also ping) from WAN

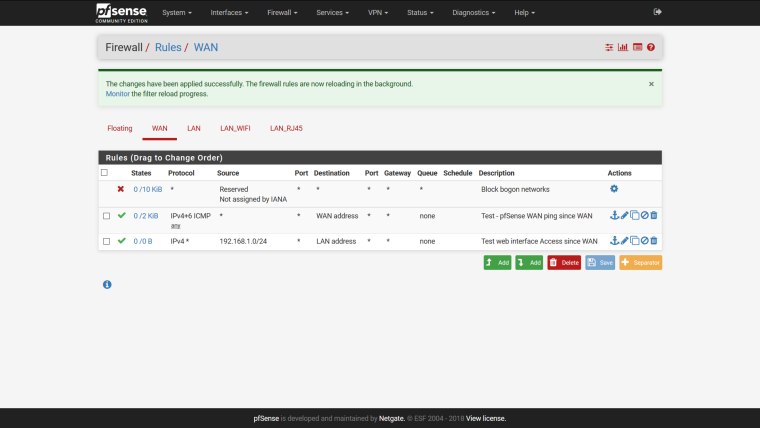
I don't know how to realize the same feature with my DIR-655 router but this is not the subject here.
A last question : Is it a security problem to remove the RFC 1918 networks rule ? -
"A last question : Is it a security problem to remove the RFC 1918 networks rule ?"
Yes. RFC 1918 networks are networks that should only be routed internally, so anyone trying to route them on the open internet is doing something they shouldn't be. While most ISPs should be filtering these out and not allowing anyone to even advertise them onto the internet, i have seen occasions where this happens. This is purely to protect the end users.
For example. you won't see 192.168.1.x/24 advertised by anyone on the internet, because its a RFC 1918 network.
-
@behemyth Thanks for your reply
 . So in my case, is there a workaround solution ? Is there a way to add a filter that specify that only client(s) on the modem-routeur LAN side (192.168.1.x) are allowed to access behind the psense device (throw WAN side) to access to the LAN side (192.168.2.x) ?
. So in my case, is there a workaround solution ? Is there a way to add a filter that specify that only client(s) on the modem-routeur LAN side (192.168.1.x) are allowed to access behind the psense device (throw WAN side) to access to the LAN side (192.168.2.x) ?