How to hide ipv6 entries in firewall logs?
-
Hello,
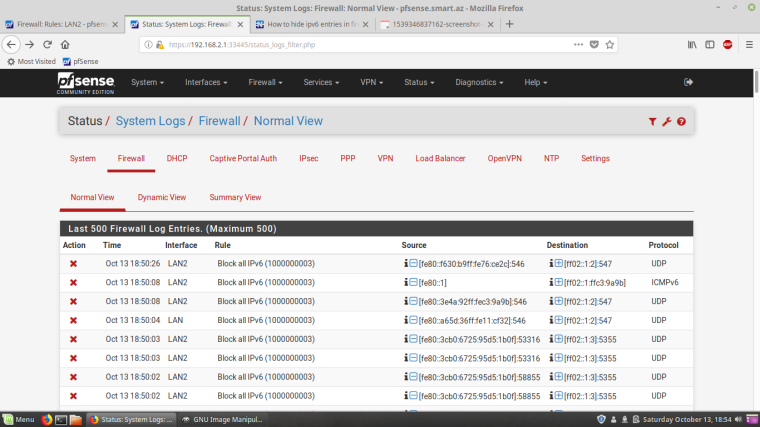
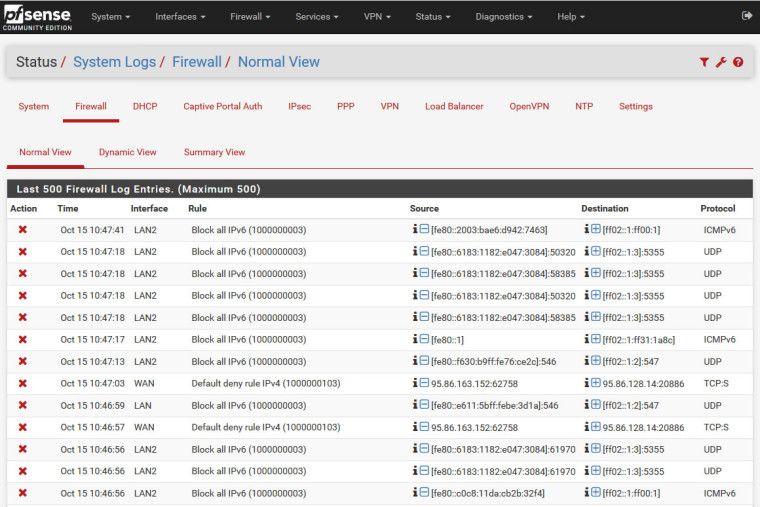
I frequently look at Status / System Logs / Firewall. There are many ipv6 logs there. How can I hide them and show only ipv4 logs? And by the way, there is not an option to select which interfaces logs to show (WAN or LAN).
-
There is a line above the log data that says Advanced Log Filter that when expanded allows you to filter the logs in a variety of ways. You can enter a specific interface, look for certain ports or IP addresses, and enter strings (I think some fields might even accept regex).
-
This post is deleted! -
Thank you very much.
-
@virgiliomi said in How to hide ipv6 entries in firewall logs?:
e is a line above the log data that says Advanced Log Filter that when expanded allows you to filter the logs in a variety of ways. You can enter a specific interface, look for certain ports or IP addresses, and enter strings (I think some fields might even accept regex).
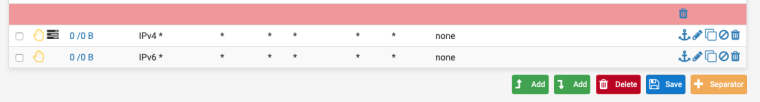
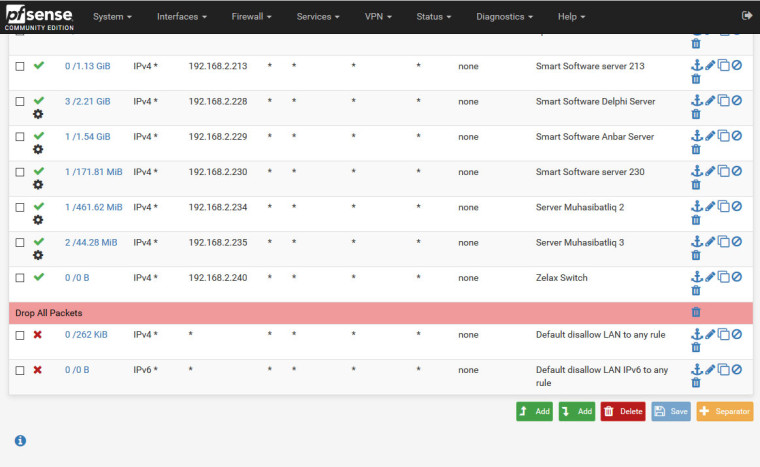
If you don't run IPv6 you could always create two drop rules at the bottom of your interface rules and don't log IPv6.
-
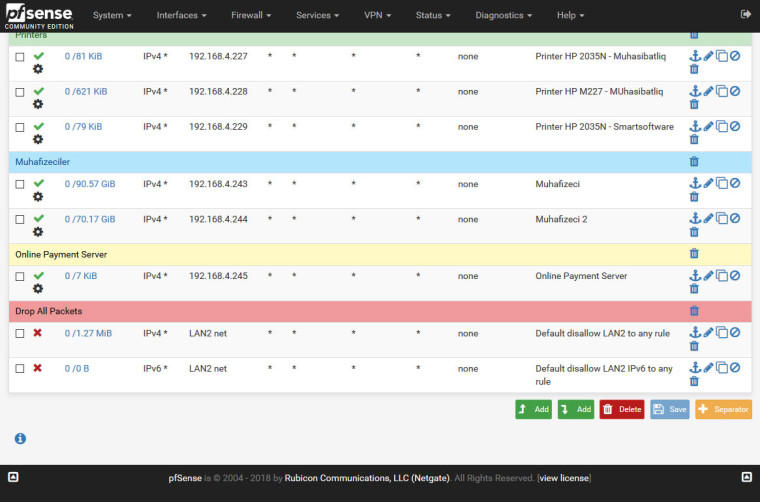
We don't use IPv6 in our network. We have this same rule in our pfsense. But I see these kind of logs in firewall logs.
-
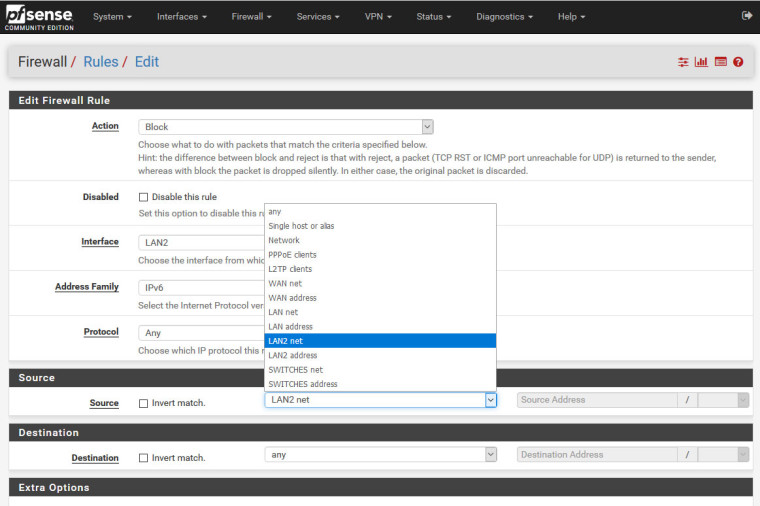
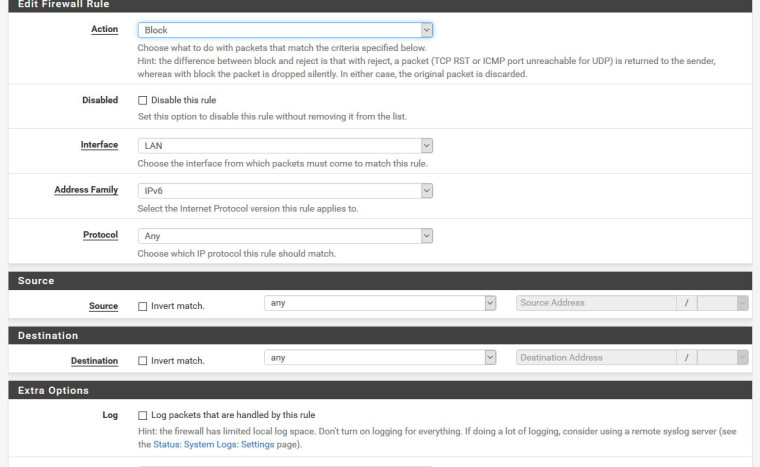
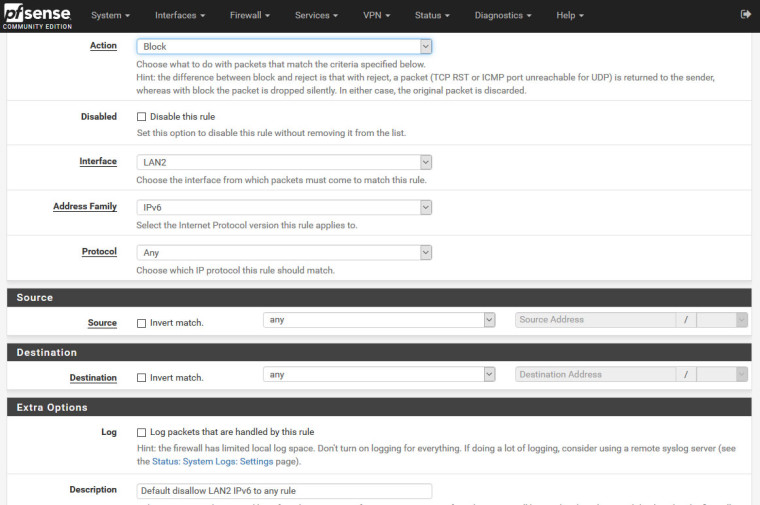
Try changing the IPv6 src to any rather than LAN2 net.
-
@nogbadthebad said in How to hide ipv6 entries in firewall logs?:
Try changing the IPv6 src to any rather than LAN2 net.
This will likely fix it as it’s likely that you’re seeing the logs with multicast addresses, which aren’t LAN2 addresses.
-
Which one should I choose?
-
Any
-
I did as you said. But it didn't help. There are ipv6 logs running in firewall logs.
Do I always have to choose "any" as source address by default?
-
Yes, you’ll need to choose “any” as the source. Link-local (fe80:) and multicast IPv6 addresses don’t meet the “LAN2 net” address range. That’s why those addresses still show up in the firewall logs for the LAN2 interface.
-
I have chosen "any" as the source. I am attaching photos. Please have a look and let me know where I am wrong. By the way, I have unchecked "Allow IPv6" and checked "Prefer IPv4 over IPv6" in System / Advanced / Networking.
-
Try doing the same from your other LAN interfaces.
-
Other interfaces has the same settings as others.
I have WAN, LAN, LAN2, LAN3, OPENVPN, IPSEC. -
Hmm should work, have you killed the firewall states ?
There aren't any hits against that firewall rule.
-
Doesn't matter what you put on your interfaces since its being blocked by the BLOCK ALL IPv6 rule you have enabled.
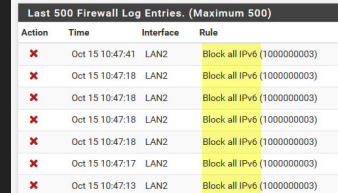
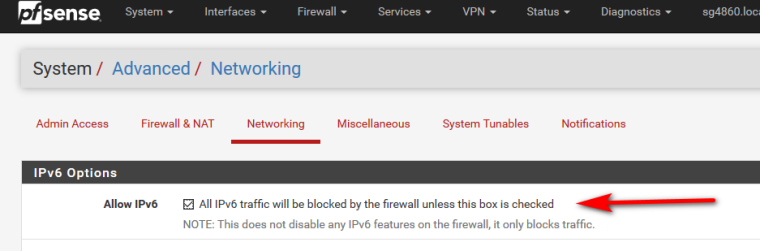
That is what is logging it - I do not believe you can enable that and not log off the top of my head.. if you don't want any logging blocked ipv6.. Just undo that setting.. Then don't allow it.. If your seeing stuff being blocked by the default log, then as stated create an IPv6 block rule for any IPv6 and don't log it.
-
@johnpoz said in How to hide ipv6 entries in firewall logs?:
That is what is logging it - I do not believe you can enable that and not log off the top of my head.. if you don't want any logging blocked ipv6.. Just undo that setting.. Then don't allow it.. If your seeing stuff being blocked by the default log, then as stated create an IPv6 block rule for any IPv6 and don't log it
Drat didn't notice 1000000003, good spot John
-
@emammadov said in How to hide ipv6 entries in firewall logs?:
We don't use IPv6 in our network.
Do you control all the devices in your network? If so and your not wanting to use IPv6 I would actually try and turn it off at the devices. Windows is one chatty kathy that when it comes to noise - out of the box it just doubles all that noise via IPv6. And if your not using it - its pointless to leave all that noise out there..
Simple reg entry or can be disabled in group policy.. Prob a good thing to see the noise so you can turn it off at the source ;)
Linux is not anywhere as chatty... You prob won't hear a peep out of it if you don't have IPv6 at the router.
547 is dhcpv6 - and 5355 is LLMNR, NOISE!!! if your not actually using it. You for sure can turn that off on ipv6.. And that screams windows clients ;)
-
I have checked "Allow IPv6", now I see this entries in firewall logs:
Oct 15 14:08:40 WAN Block ULA networks from WAN block fc00::/7 (12000) 10.128.0.2 my public ip ICMP
You said: if you don't want any logging blocked ipv6.. Just undo that setting.. Then don't allow it
It means, I have to check "Allow IPv6" and then uncheck "Allow IPv6"? I have rules in interfaces that block ipv6.