Redirecting all DNS traffic to pfSense not working
-
I have an IoT subnet. On this subnet I want the TVs, Roku's, thermostats, etc to all have their DNS traffic redirected to the DNS servers I have specified in pfSense (Cloudflare). I followed this document to set this up. I thought it was working fine but then noticed a device on this subnet was talking with 8.8.8.8.
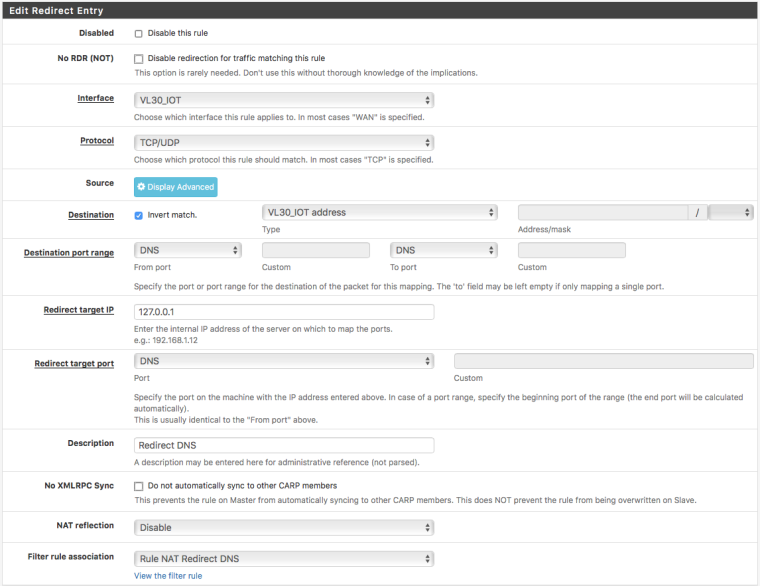
Here's the image of the NAT redirect setup.
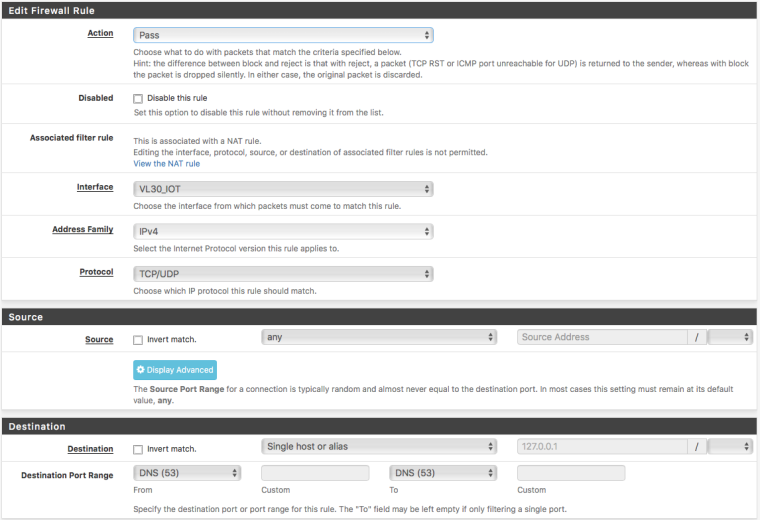
And the subsequent firewall rule on that interface;
As stated earlier, running packet capture, I see that at least one device on this subnet is successfully querying 8.8.8.8 and getting a response back. I have Cloudflare DNS setup in general settings.
Thanks for any help!
-
And they are doing that on udp/tcp 53 - or some other port?
-
The destination port is 53. It seems like the query first goes to the gateway, but then it immediately tries 8.8.8.8. Both the gateway and 8.8.8.8 reply. All over port 53.
-
The client can send query to 8.8.8.8 all it wants - you sniffed on the wan and saw this go out?
-
Well, it's weird but on the WAN I don't see traffic over 53 or to 8.8.8.8 - I do DNS over TLS on port 853 so that makes sense to not see anything over port 53. The source IP for the query response is 8.8.8.8. I see states for 8.8.8.8 on the IoT interface but not on the WAN interface. When I capture traffic on the IoT interface, it shows that the query response source IP is 8.8.8.8.
I'm guessing when 8.8.8.8 is queried, the traffic is translated and the state is built, but the interface is none the wiser whether or not the return traffic is actually from 8.8.8.8.
-
Exactly.. Client doesn't know answer didn't come back from 8.8.8.8
It just really knows it gets an answer back to its source port it asked 8.8.8.8 from
-
Very cool. I learned something today.
Thanks