Everything but pfsense web gui works when connected via OVPN
-
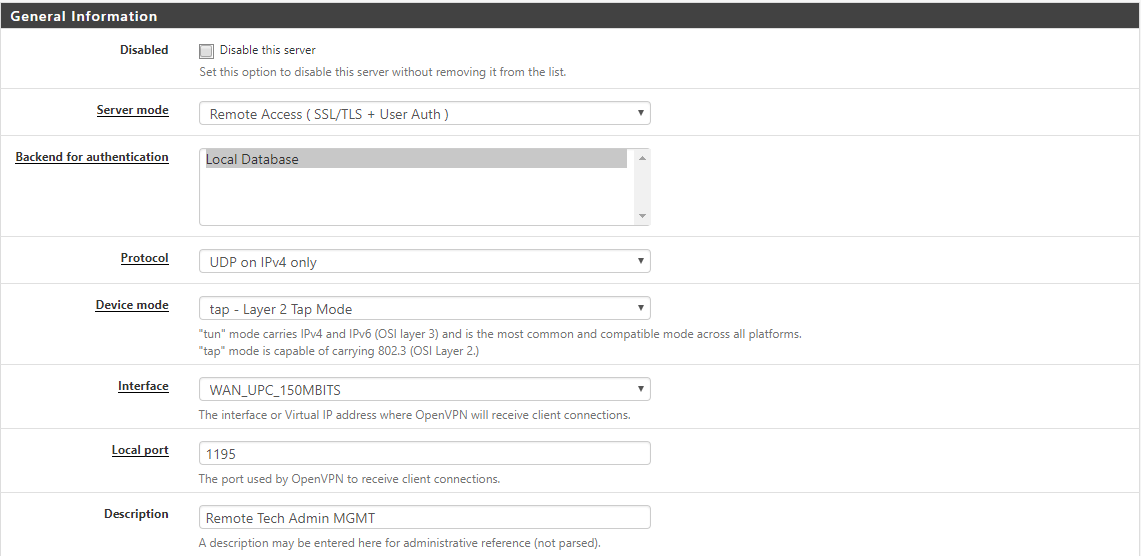
hi everyone, I have successfully created a ovpn tunnel (tap) to my managament lan. I can ping, ssh and web admin all devices except for pfsense itself.
when connected pfsense can be pinged but the web gui doesn't want to cooperate. neighter via port 80 nor port 443.The openvpn client gets the correct ip from the dhcp server on the mgmt interface and as far as i can tell routing works correctly. The only difference between beeing on the mgmt lan and connecting via openvpn is access to pfsense's web gui.... I'm sooo out of ideas.
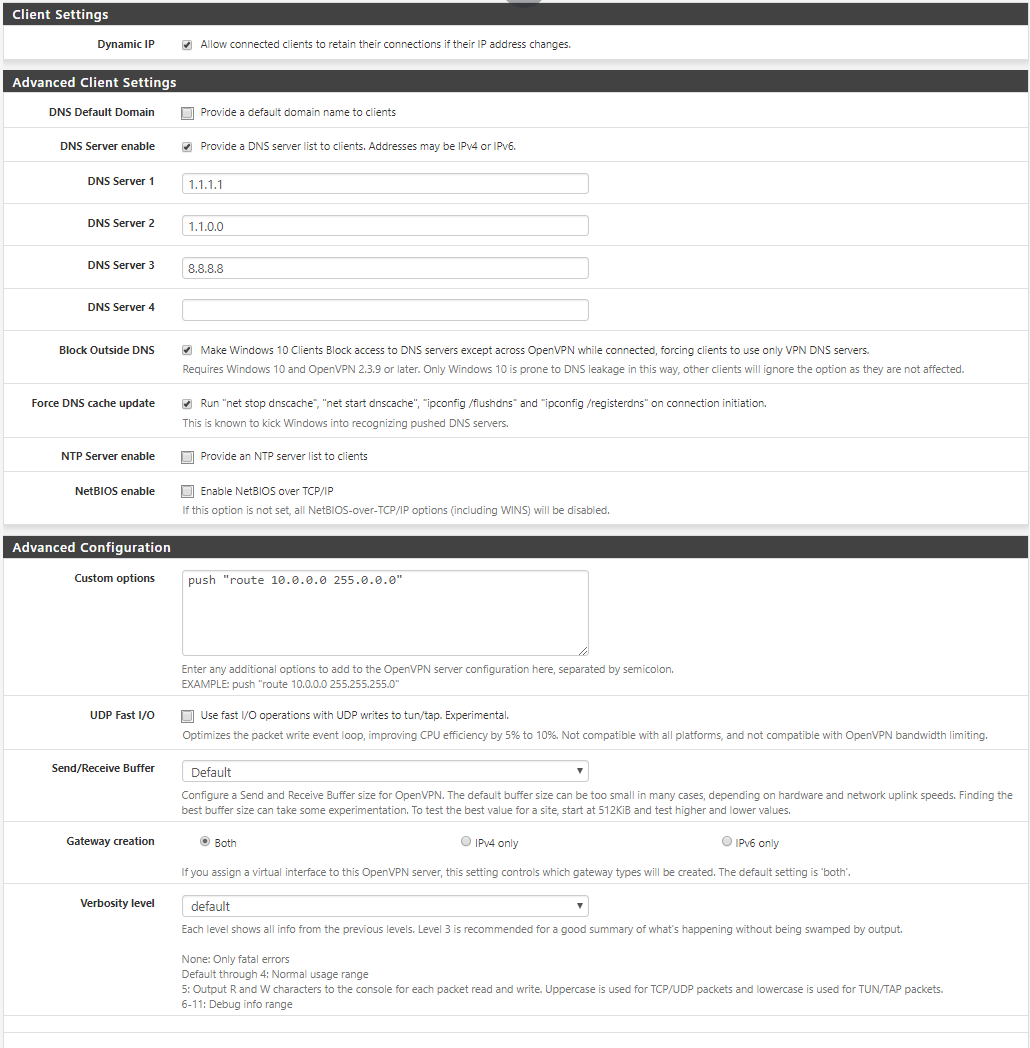
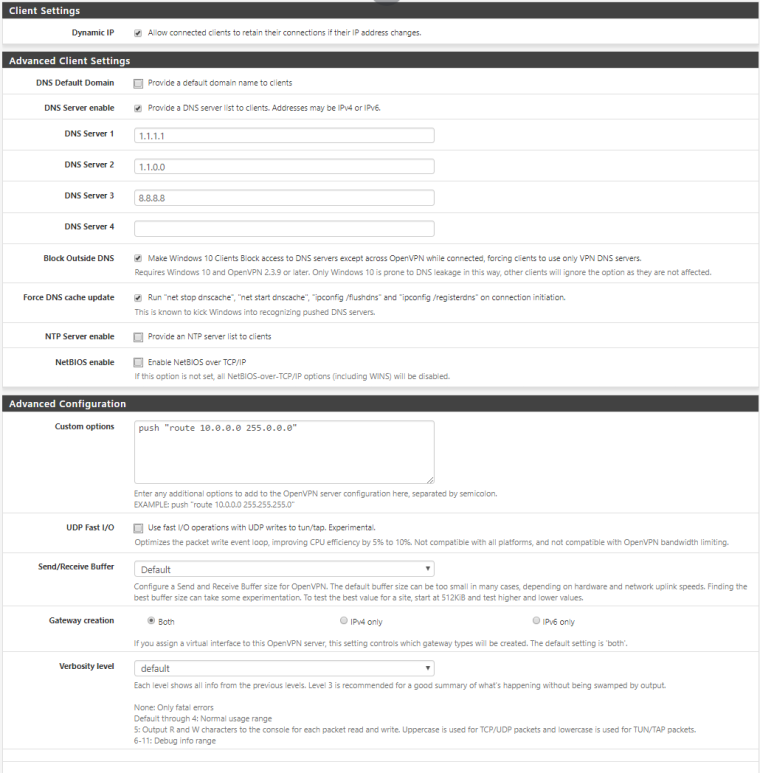
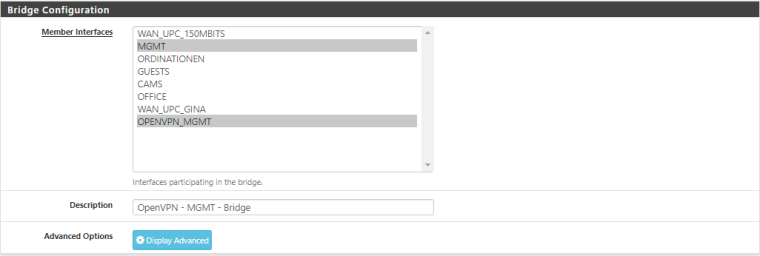
My config is as followed:
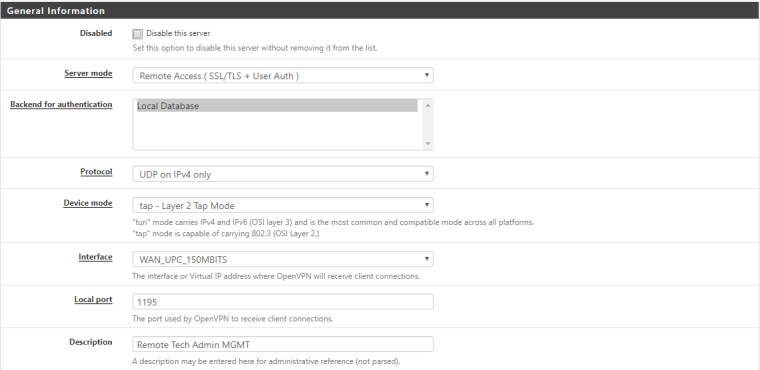
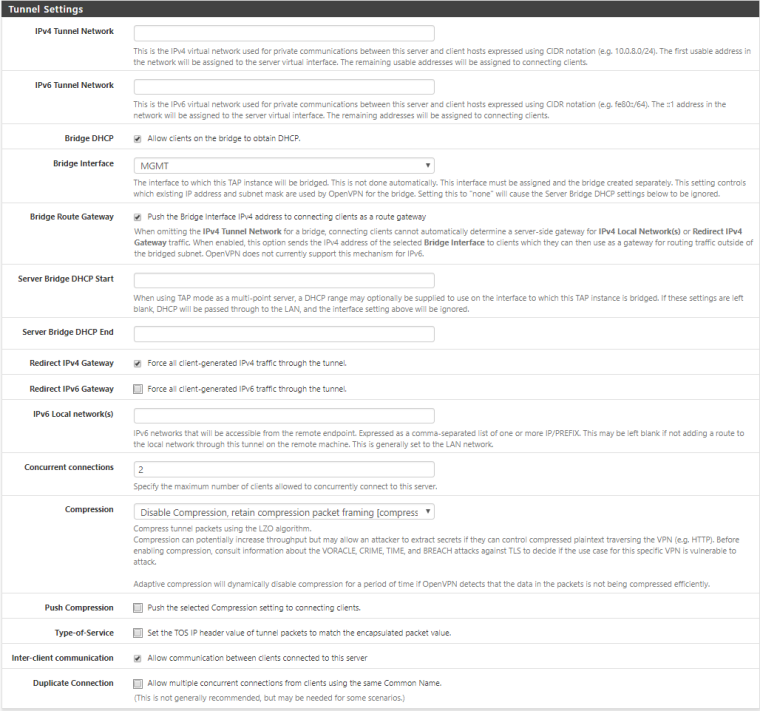
According to a tutorial I assigned an interface to the openvpn "network port" and bridged it with the mgmt interface.
I do have a tun ovpn server configured on the standard port for testing reasons, which is able to connect to pfsense.
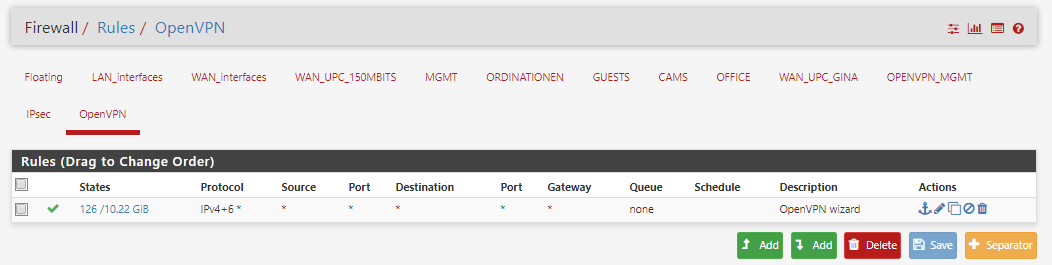
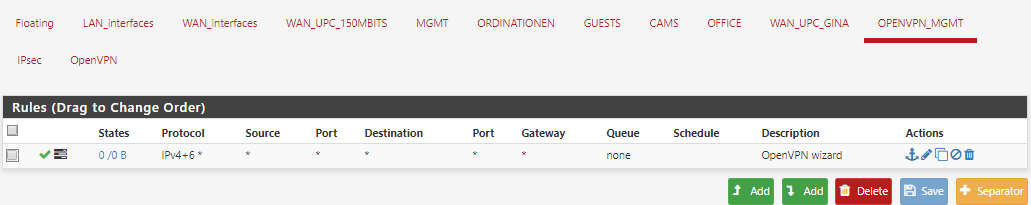
FW rules are as followed:
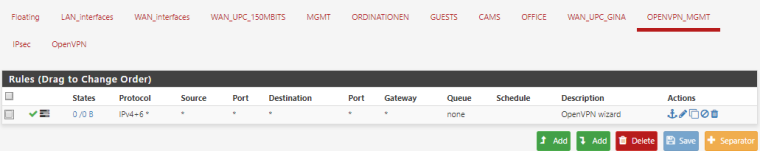
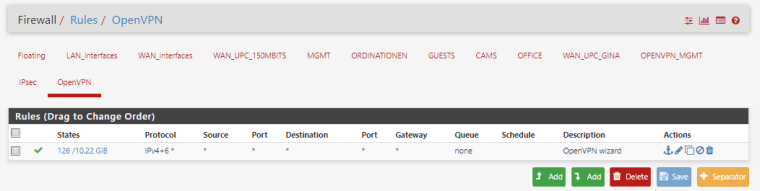
In regards to the fw rules: I do not understand why the openvpn_mgmt interface (which i assigned) doesn't see any traffic. Might this be the issue?
I hope someone can help.
-
Your assigned Interface doesn't see any traffic in Rules because the OpenVPN Group Tab is processed first and hits your any-any Rule.
Any serious reason for tap and not tun Mode?-Rico
-
There are some devices on the mgmt lan that will only accept requests from devices which are also in the mgmt subnet.
Since I'm usually not doing much networking stuff I did some reading on the possible ways to configute openvpn and tap as a layer 2 bridge seemed like the less complicated variant since, from what I understand, it creates an 'as if I'm on the same lan & subnet' kind of scenario for connecting clients. literally like a virtual ethernet bridge. (?)
SInce your comment is not the first time I see people getting asked if the really need/want a tap configuration I'm starting to think that I'm propably missing some disadvantages of using it?
The thing that confuses me is that my tap bridge seems to work as expected. the client gets the correct ip from the dhcp server configured on the mgmt lan that my ovpn bridges to. EVERYTHING works, except for connecting to the web gui of pfsence. pinging pfsense works just fine...
Shouldn't the (one of the) any-any Rule(s) you mentioned make sure that traffic comming from ovpn can do pretty much anything it wants?Thank you so much!
-
Note from the pfSense Book:
Not all clients support tap mode, using tun is more stable and more widely supported. Specifically, clients such as those found on Android and iOS only support tun mode in the Apps most people can use. Some Android and iOS OpenVPN apps that require rooting or jailbreaking a device do support tap, but the consequences of doing so can be a bit too high for most users.Can you see any activity in your Firewall Logs when trying to access the pfSense via WebIF or SSH?
I would follow the guide again and try exactly as described with a very basic setup: https://www.netgate.com/docs/pfsense/book/openvpn/bridged-openvpn-connections.html
e.g. don't push any routes, don't use redirect gateway and so on, just basic.Disable the Rule in your OpenVPN tab to make your Interface Rule active (which should not make any difference for this problem tho).
-Rico