Newbie to pfsense, got typo in WAN host name How to fix?
-
John;
Calling TWC right now. -
If you have a biz connection then yeah they prob update it for you - the TTL is 24 hours... So anyone that has that cached you will have to wait on, etc..
But that really shouldn't have any effect on someone resolving a fqdn vpn.domain.tld to get to your IP... That would be what you control if you are the owner of said domain.tld Nor would it have anything to do with what fqdn or SAN is listed in a cert... Where they mostly come into play is say an email server sending email saying hey my name is smtp.domain.tld... And when the recv smtp server tries to look up the PTR for that IP it gets back something.else.tld - which screams the owner of smtp server doesn't have a clue - this is prob spam ;) heheeh For what your most likely doing getting users to access vpn.domain.tld the PTR doesn't really matter.. But if they will change it then yeah its good idea to have forwards and reverse for an IP match up when possible.
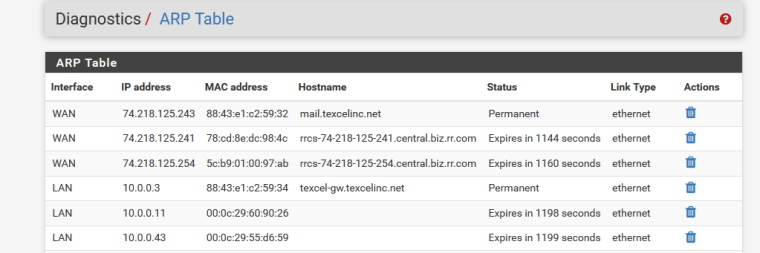
Example - here is arp table for my pfsense wan at home.

This is the PTR of that IP owned by my ISP.. But I can point any forward (a record) I want to it.. vpn.mydomain.tld if I own the domain.. Or can have records edited, etc..
-
John;
our registar is bluehost I just -
@markp4289 said in Newbie to pfsense, got typo in WAN host name How to fix?:
vpn.texcelinc.net
Yeah I see that..
;; AUTHORITY SECTION:
texcelinc.net. 300 IN SOA ns1.bluehost.com.That resolves just fine - but WOW what a short ttl on a SOA record... Uggghhh!! That resolves just fine - but that has zero to do with PTR
-
BTW - let me know if you want me to clean up the public IPs and fqdn that resolve to this IP - some people have issues with posting such info on public forum.. I only posted it because you had already done so, etc. but be happy to clean up the whole thread replacing with placeholder names..
-
pfsense is suppose to protect me so you can leave it alone
-
hehee - ok.. pfsense doesn't stop someone doesn't like something you say here on the board and pointing some bot net at your ip to flood your connection with a ddos... Just saying...
Bot nets can be hired for pennies these days..
-
Never really dug too deep into that but is it not possible dhclient sent that to the provider?
Unless that was similarly typo'd at some other point.In which case I would expect it to expire at some point.
But either way the issue here appears to be that the VPN server certificate was created with the old host name and clients are refusing it right?
In which case just regenerate the server cert.
Steve
-
@stephenw10 said in Newbie to pfsense, got typo in WAN host name How to fix?:
Never really dug too deep into that but is it not possible dhclient sent that to the provider?
No... I don't think so - never seen a provider update their PTR records with hostname via dhcp client.. Not saying it not possible.. And not really a good idea to be honest.. Since its quite possible you wouldn't want the PTR to reflect host name of the router, but the forward name of say a smtp server you have behind that public IP, etc.
If his ISP is allowing him have a PTR of his choice - then a simple call to them should get it fixed up. You could also just have your dns look like it owns the netspace.. So for example just created record in unbound for my pfsense for my public IP.. And now it shows this in the arp table.

But that has zero to do with how anyone else on the planet would resolve it... Just makes anyone using my unbound as their dns resolve that PTR. Simple local-data-ptr in the custom box easiest way to do it ;)
And as discussed this would have nothing to do with any sort of cert not complaining about a common or san name in a cert.
-
If it's what you see in the ARP page, that should be what is resolved locally, so either the hostname under System > General or maybe a host override.
If it's the GUI cert that has an unexpected hostname, then you can make a new cert manually, or use
pfSsh.php playback generateguicertafter correcting the hostname, or (Even better) use ACME to get a real trusted cert.If it's a VPN cert, make a new server cert.
If you can't find where else the wrong hostname is present, download a config.xml backup and then open it in a text editor. Do a search inside for the incorrect name.
-
Hmmmm; My WAN link is static IP and config that's why I thought it was my typo. I just got off the phone with TWC took an about to get to the Level III that knew what I was talking about. This is the 4 th TWC problem that I've had in 7 days.
-
Looks like they BROKE it to me.. now all you get back is SOA when you query the SOA for that PTR ;)
So vs them fixing it to the actual fqdn you wanted to be returned, they just removed the record completely ;)
-
Nice.

Though still not clear to me why that should be an issue. If this is just VPN clients refusing the cert just regenerate it.
Steve
-
Its not an issue what his PTR reports or doesn't report has ZERO to do with his overall problem.. I believe what he saw in his arp table just confused him..
-
After TWC deleted PTR records.
-
yup that is what I show for those IPs PTR ;)
I don't see any vpn one though? the forward points to .242 but the PTR is just gone.
-
So it looks like the General setup generates the LAN hostname but nowhere is the WAN hostname entered. How do I get the WAN hostname in there?
-
That is the WAN hostname. Or at least that is the name send by dhclient to an upstream server.
Steve
-
Get it in where?? Not sure why you think you need a WAN IP to resolve to something in your arp table for vpn clients to connect to you?
I am thinking you still don't quite grasp what a PTR or reverse is...
Your vpn.domain.tld resolves to IP.242 address.