Guest Wi-Fi on various VLANs not getting DHCP addreses
-
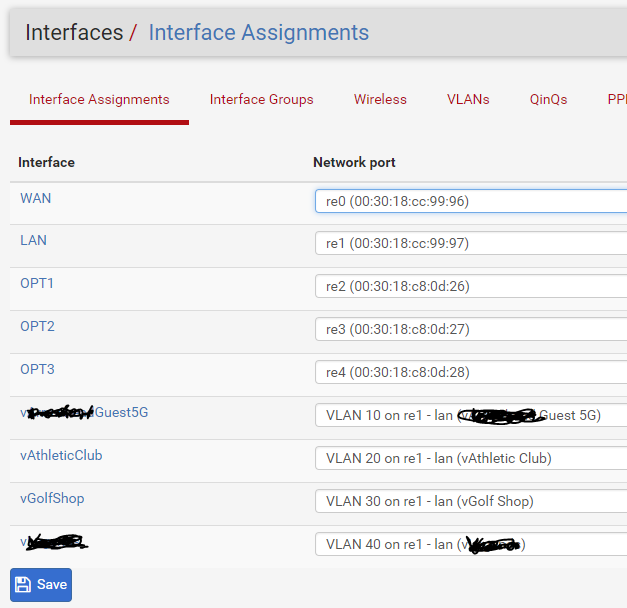
I have pfSense running on hardware that has a total of 5 Ethernet ports:
WAN - re0
LAN - re1
Opt1 - re2
Opt2 - re3
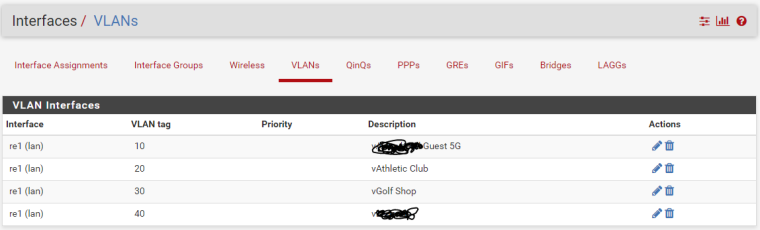
Opt3 - re4I have a Wi-Fi system setup that each SSID is on a different VLAN but bound to the LAN interface:
vSSID1 - 10 on re1 LAN
vSSID2 - 20 on re1 LAN
vSSID3 - 30 on re1 LAN
vSSID4 - 40 on re1 LANI have the Wi-Fi system assigning the different VLAN tags to the different SSIDs.
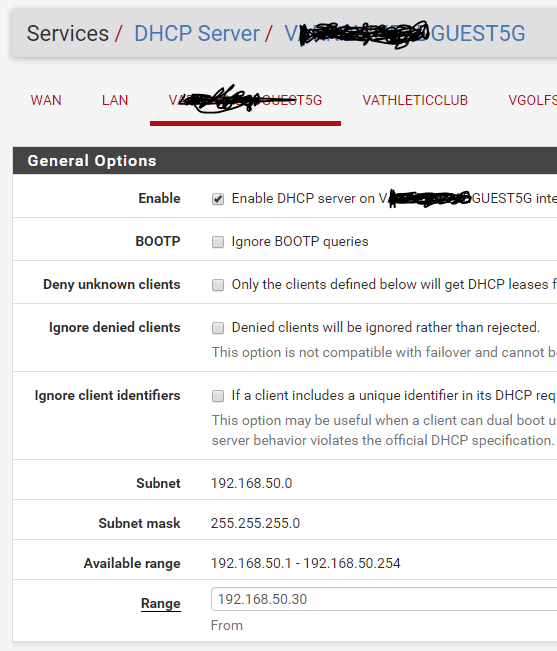
Within pfSense I have setup DHCP for each "interface" that was defined as a VLAN on re1. For testing purposes I have setup "pass all" rules on each interface in the firewall section.
My overall problem is that I'm not getting a DHCP address assigned to the client on the different SSIDs. Can I get some ideas on what I'm doing wrong?
-
your switch config would be my first guess
-
My first guess too.
-
What type of switch are you using? You'll need to create each of these VLANs on the switch in order for this to work. It can't forward traffic on a VLAN it does not know about.
-
Exactly... You would need to tag those vlans on the port connected to pfsense lan... And also they would need to be tagged on the port your AP is connected too.
What AP are you using? What switch are you using?
-
@awsiemieniec
Check the dhcp log for the usual discover, offer, request and ack messages to see where it drops off. I had a similar problem and it was a problem with the AP. -
@bhjitsense said in Guest Wi-Fi on various VLANs not getting DHCP addreses:
What type of switch are you using? You'll need to create each of these VLANs on the switch in order for this to work. It can't forward traffic on a VLAN it does not know about.
He's set up VLANs on pfSense and also on the AP. A managed switch should pass all VLANs, through trunk ports, without further configuration. However, specific VLANs may be blocked. Of course, if an unmanaged switch is used, it would be transparent to VLANs.
However, as mentioned above, more info about the switch is needed. Running Wireshark may also help.
-
@heper Thank you for all the ideas.
Switches are multiple UniFi managed, PoE 24-port switches as seen here: https://www.ubnt.com/unifi-switching/unifi-switch-poe/
One plus which is also sometimes a hardship, is that all the UniFi devices play well together - like a Mac. A lot of the "under the hood" configuration settings are hidden from the tech; you make a change within the management systems and the management system puts that change on the device(s) that needs it. Everything on the LAN is UniFi with the exception of the pfSense firewall.
-
@johnpoz The APs are UniFi AP-AC-Pro (https://www.ubnt.com/unifi/unifi-ap-ac-pro/) and a few of the AC-Mesh units (https://unifi-mesh.ubnt.com/#products)
-
@awsiemieniec thank you for providing great insight into the network
-
I run unifi AP.. So I know those work and no issues with tagged vlans and ssid. I run them myself..
But if your not seeing dhcp discover on pfsense vlan interface then is your switch config. You prob get good support over on their forums..
-
@johnpoz Ok. So with what I've shown on the pfSense side, do you think I've set it up right? I didn't miss something obvious, right?
I'll check out the UniFi support next. They are pretty good but I like the pfSense people better. :)
@jknott All of the unmanaged switches have been removed from the LAN.
-
Whatever switch port you connect to re1 neets to be untagged on whatever VLAN LAN is and tagged on VLANs 10, 20, 30, and 40. That's pretty much all there is to it. Everything else is done with the right VLAN tags throughout your switching and wireless gear.
-
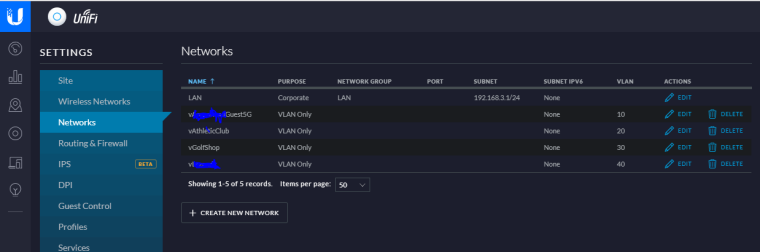
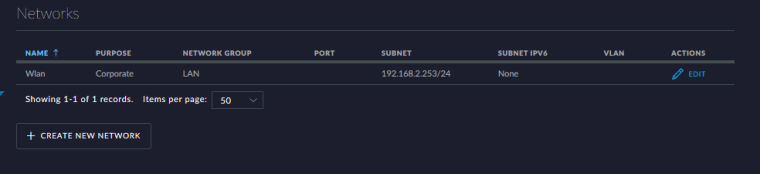
Found the solution. I had missed creating the VLAN networks within the UniFi system. Whoops.
UniFi support always told me to not ever change the "Networks" tab if you don't have their firewall device. So I didn't think about adding the VLANs here. Good to know.
-
You do not need to do that when all you have is the APs... But that prob lets the switches know about the vlans ;)
How exactly did you set the switch ports to tagged if you handn't created the vlans? With wifi you just set it in the wifi setup
When I was running USG you had to have your vlans setup there.. But with pfsense you do not need those when no unifi switches.
-
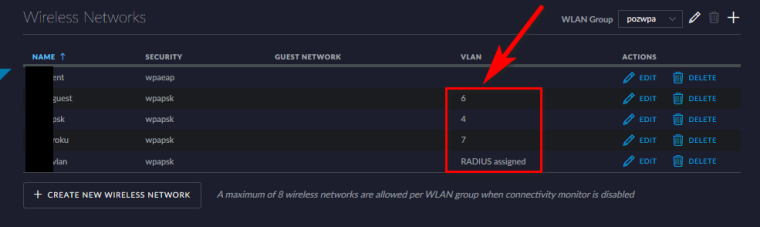
@johnpoz Like what you show in your image of the wireless networks, I had already setup VLANs for the various SSIDs but I wasn't getting any DHCP traffic to my pfSense (except for on the management VLAN).
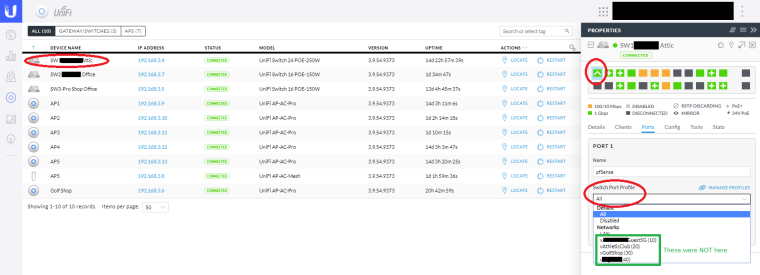
First thing the UniFi tech had me check on was what was the port type set to in <switch>, properties, port #, Switch Port Profile and make sure it was set to "ALL" (their version of trunk). It already was set to that value.
Then he had me navigate to settings, networks and said "whoa! there's the problem". He explained that I need to setup VLAN-Only networks so the switches would be aware of them. So did that and voila!~
Hope that helps explain some.
-
Which is exactly what I was saying ;)
