Slow http/https traffic
-
Hellow every one
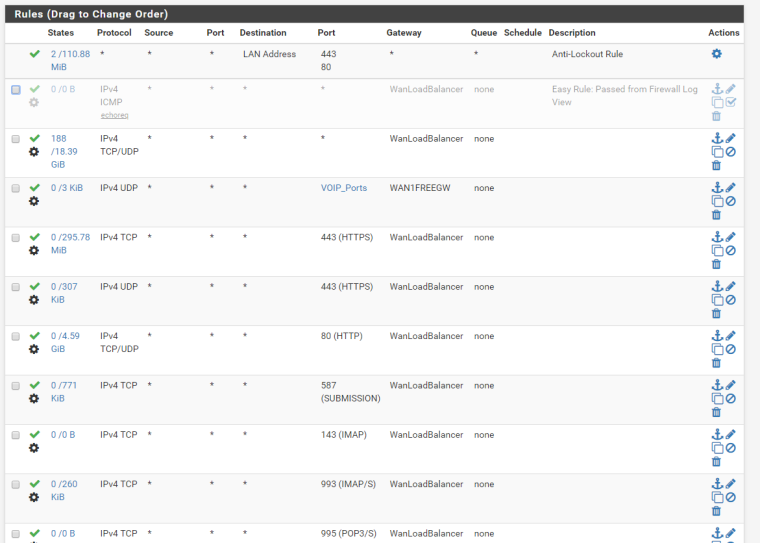
I have a question for you, i set up a firewall with pfsense few month ago and my http / https traffic is low with my current configuration.When i put in the top of the rule a new on wich allow all port ... the traffic is pretty fast but when i remove this rule the traffic is slow.
Could you help me to understand please ? How can i see what is blocked ?
Tell me if you want more information.Have a good day
-
The default rule on pfsense is allow all... So your going to have to post screenshots of your rules.. How are you tresting this speed difference?
Are you using proxy, IPS, pfblocker, etc. etc.?
-
i guess you can check firewall logs and traffic shaping wizard .
prioritizing ack packets will speed up web traffic in my experience -
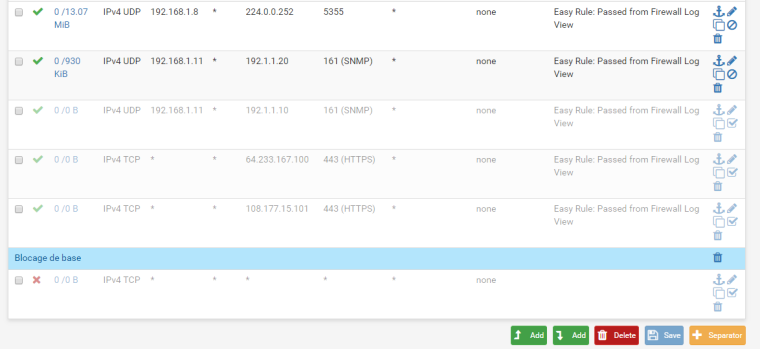
Hello, You can find in attachment my rules. Now all my connection is pretty ok because i accept all (2nd rule) but when i deseable it i have no internet anymore.
I saw the defference when i want to load a page.
No i use no proxy or anything else yet.
-
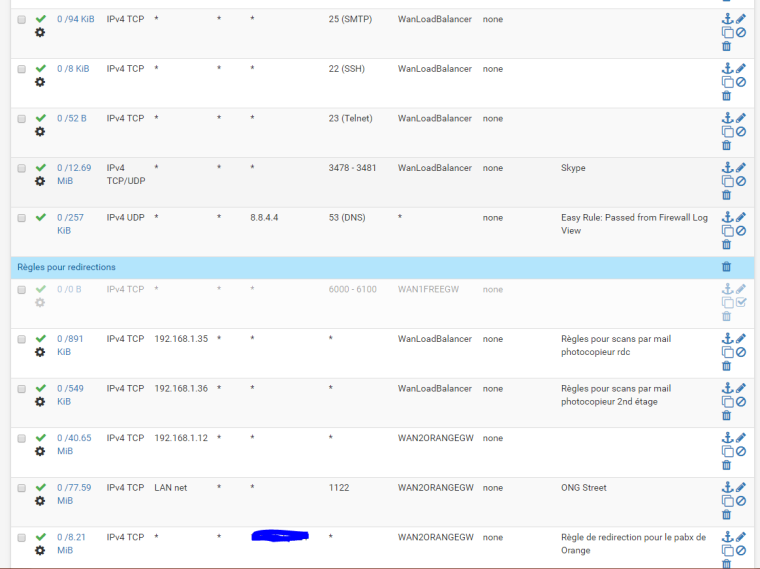
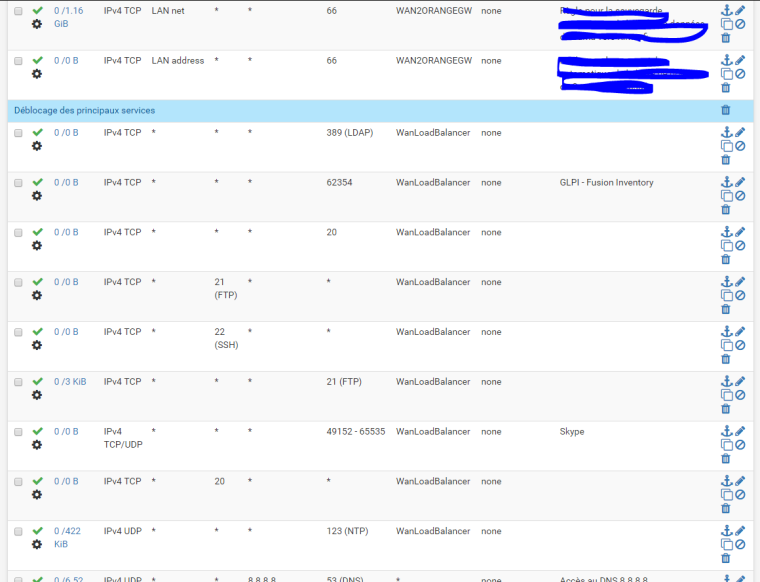
Every rule below your any any is pointless!!!!
Rules are evaluated top down, first rule to trigger wins no other rules are evaluated. What are you doing with wanloadbalancer?
Where do your clients get dns - because with those rules their dns is going to be forced out your gateway.. And they can not even ask pfsense for dns.
The only way your getting hits on your below rules is must be turning off that top rule?
What do you think the point of a allow to ntp rule is that below a any any rule??
Here is what I would do - delete all of those leave the default any any rule and not shove it out a load balancer - how is your speed now? Then after you have read the manual on how rules are evaluated... Then an only then start dicking with them ;)
-
Thank to the reply.
I do some modification :
I diseable the rule any any
I add two new rules in the begenning of the list :
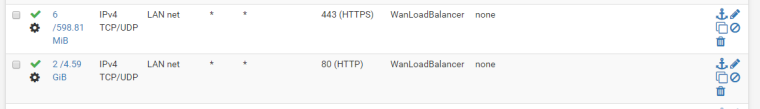
I add a rule in the bottom of the list with block allThe connection appears ti be faster.
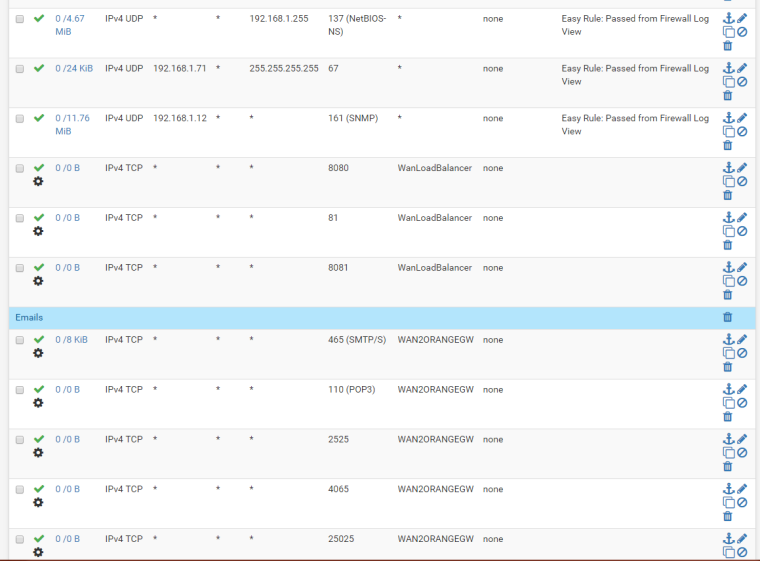
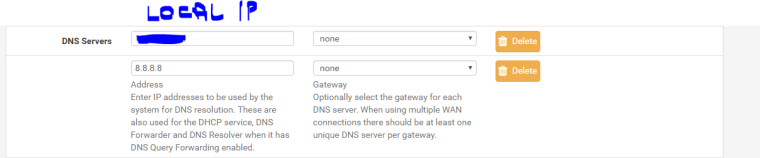
Do i have to create a rule for my dns (dns is on one of my server) ?
-
There is a block all rule by default.. Where are you clients getting dns? Looks like you only 8.8.4.4
And again - all of those rules that allow say port 20 as dest?? For what possible purpose is that - 20 is a source port used in active ftp connection... What are you hoping to accomplish with that rule? You also have rules with sorce ports of 21 and ssh... What are those suppose to be doing?
I really really suggest you read the pfsense book on how rules are evaluated.. Return traffic is allowed via states, and rules below an any any don't make any sense..
https://www.netgate.com/docs/pfsense/book/firewall/index.html
-
@johnpoz said in Slow http/https traffic:
There is a block all rule by default.. Where are you clients getting dns?
My client get dns from a local serverAnd again - all of those rules that allow say port 20 as dest?? For what possible purpose is that - 20 is a source port used in active ftp connection... What are you hoping to accomplish with that rule? You also have rules with sorce ports of 21 and ssh... What are those suppose to be doing?
Sometime i have to send data from ftp or sftp that why i allow ports, the rules with source 20 are mistake and i diseabled them.
rules below an any any don't make any sense..
Iknow it was a test to see if ot was one of my rules that slowed down my connection.And thanks for the link i will check it.
-
Talking to outbound 21 or 22 would not = a source PORT on your rule..
When you see dns from local server - you mean pfsense, so local server on same vlan? Because I didn't see any rules that allowed access to pfsense IP for dns.. And your forcing everything out your gateway which doesn't allow for talking to pfsense IP for any dns.
Please read through the info on how the firewall rules work... If you have questions ask... But looking at those tell me you don't quite understand how they are evaluated..
-
Hello,
First, thank you for your help, i think i understand the rule and how they work.
You can find bellow my dns configuration on pfsense and if i understand i need to create a rule from my lan network to 8.8.8.8 and an other to my local ip 172.X.X.X?
-
Why would you be hiding a local rfc1918 address?
Why would you tell your clients to use 2 different DNS that can not resolve the same thing... 8.8.8.8 for sure is not going to resolve your local stuff... Nor would you ever want to be sending to the public internet your local names in the first place..
You can never be sure which NS a client will use when you give them more than 1.. If they happen to ask 8.8.8.8 for host.localdomain.tld they would get back NX and never go and ask the other NS listed..