Network security in garage
-
hey guys, quick question about security.
i just installed conduit to our garage. I am going to run either a fibre cable or some cat 6 to a switch in the garage. Off the switch, i am going to put a Unifi AP so we have wifi in the garage, as well as 2 wired security cameras.
On my camera segment, all internet and firewall access is blocked via firewall rules. I am wondering if someone got into my garage and had access to the switch or even unplugged the Unifi AP, and plugged in a laptop, how would i make sure that they couldn't compromise my network?
I know it is unlikely, just wondering what I am getting myself into.
-
Your firewall is in the house somewhere right.. So depending on your firewall rules - they would only be able to do what those firewall rules allow..
You could if you want even do static arp on that segment so even if they plugged in their laptop they wouldn't even be able to talk to pfsense since mac would not be listed.
Also what switch do you have in the garage.. You could run port security on it - so only listed mac can talk.. But if they are into your garage.. I would think you network security is kind of moot at that point ;)
-
hey John, thanks for responding.
yes, firewall is in network closet inside the house, garage is detached so someone could be in the garage without access to the house.
I would put maybe a 5 port smart switch out there. I guess one port would be a trunk to carry all my selected networks. One port would be just the camera network, another port would be just the wireless lan segments. That would still leave a few ports open and accessable.
Do you have a suggestion for a fairly cheap 5 port switch that will work with VLANs from pfsense and my Cisco switches? right now I only have a couple dumb switches lying around in my parts boxes that I am not using.
-
Stay away from the tplink cheap switches - I know v1 and v2 of those did not do vlans correctly. They suppose to have a firmware out to fix v3 of the units... Still would stay away. I have both a netgear and a dlink that do vlans correctly.. Both cheap..
d-link
DGS-1100-08netgear
GS108Ev3What you running for cisco? I run a sg300-10 in my av cab.. Then a sg300-28 for main switch.
I got fed up with the limited feature set of the cheap switches I had running in av cab.. So move my -10 to that and got the -28 as upgrade...If your running camera and unifi AP - you prob in the market for POE.. I would think maybe their 60w 8 port POE might work - depending on what poe your AP and Camera's can do. US‑8‑60W
-
Yeah if you're using a Unifi AP and Unifi cameras then using their switch to power those seems like a logical choice. Especially if they're the older 24V type.
Steve
-
John,
i have a Cisco SG300-28, and 2 SG300-10MPP, and a couple 10 port Cisco dumb switches. Sucks that Ubiquiti uses a weird POE spec, i have 2 of their AC-Pro's that i can power off my Cisco switch but the old Unifi I have lying around can't. I guess if i feed that smaller switch with poe, it won't be passed on to the camera?
The static ARP you are talking about, would that be within pfsense or on the new smart switch itself? How would i deal with the arp on the trunk port that would be carrying a few of my networks.
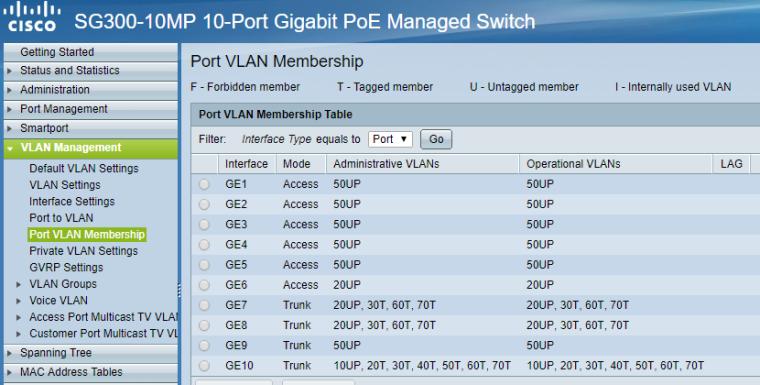
Sorry for all the questions.. Here is a picture of my Cisco with the VLAN assignment page.
-
hey Steve, just using a Unifi AP that I had lying around, I have a POE injector for. The cameras are Hikvision that use standard POE.
-
The Pro's are standard poe.. The lite and LR models are not...
The static arp stuff would be in pfsense.
https://www.netgate.com/docs/pfsense/dhcp/dhcp-server.htmlThe deny unknown/static arp setting
-
thanks man, will have a read!!
-
One thing i was thinking about, how would i use deny unknown for my wifi segment where i would want that in the garage on that particular port but within my house, i want friends and family to be able to connect without being denied?
-
You can turn that on for specific vlans.. You wouldn't turn it on for guest networks..
Keep in mind again - none of this really needed since unless your would be hacker unplugs device knows what vlan tag to set.. How would they get anywhere? And then that gets them what on your iot network? Which per your firewalls can do what exactly?
I think your way over thinking this here ;)
Per basic security any of those ports on your switch that do not have devices connected to them should be OFF anyway ;)
Your camera's ports could have port security set on them so only the camera mac would work.. And or static arp on that vlan. And again what could they do even if they got on that network? Only one that might be of concern is if they knew or figured out the vlan ID for your "secure" wireless network and connected as that.. Which you could run static arp on as well.. But they would be on that L2 then.. What else is on that L2 that they could get to?
Since when is your garage a dod facility ;)
-
thanks again John, have too much time to think before the wife and kids get up and dictate my day :)
that makes sense. I just didn't want to have open doors to my network in the garage. I guess i would just trunk in the camera network and the main wifi network into a port in the garage switch, lock one port to the MAC of the UNIFI AP, and the other 2 ports to the specific camera MACs.
I saw the settings on my Cisco switch for port security, i will have a look to see if the Dlink or the Netgear have that, i didn't even know that existed :)
Haha, thanks, as always for your help! i think part of the problem is i know just enough about networking to make me dangerous and a security threat to myself :)
-
Port security is common in enterprise setups... Say a conference room or common area ports that say a printer connects to or something.
If you really want to get fancy start doing 802.1x where devices have to auth ;) You could do mac based vlans, lots of stuff you can do to keep unwanted devices off your network that have physical access to a port.
Take a look at packetfense for an opensource NAC you can run.. You can get it work with your sg300 I would think - but been a while since played with it.
All of said stuff is fun - but don't lock it down so hard you make it a pain the ass for you to connect new devices.. And these shitty iot devices sure and the hell do not support enterprise grade stuff.. It would be fantastic for starters if they would support wpa-enterprise for their wifi.. I would love to use eap-tls for their wifi network for example ;)
While you can do say static arp on pfsense.. That doesn't lock down that L2 they would be connecting too.. What you could do is private vlans if devices on that L2 do not need to talk to each other. Camera's for example should have no need to talk to each other - so even if they go on and connected to your network they wouldn't be able to see any other traffic on that vlan. And even if they used same mac they could only talk to pfsense and do whatever firewall rules for said camera allowed, etc.
-
ya i don't want to make it more complicated that it needs to be.
Since you are around, can i ask you a somewhat related question? do you have an opinion on running fibre? is it dangerous to run copper underground outside to the garage and is it worth the extra expense to run 1 fibre line? I can do 3 cat6's for about $75, while fibre, i need media converters, SFP's, and expensive cable, probably closer to $250.
Have been reading about lightning strikes and frying equipment. That being said, i live in Vancouver, and haven't seen lightning in years :)
-
Mmm, I think you have a higher class of burglar in Vancouver than we do in London if that's a real threat.

But a useful experiment in locking stuff down.
Steve
-
haha, i didn't know if it was a threat, we live in a pretty good neighborhood as well. Just didn't want to do anything stupid by leaving unsecured network ports out and about :)
-
@xman111 said in Network security in garage:
ya i don't want to make it more complicated that it needs to be.
Since you are around, can i ask you a somewhat related question? do you have an opinion on running fibre? is it dangerous to run copper underground outside to the garage and is it worth the extra expense to run 1 fibre line? I can do 3 cat6's for about $75, while fibre, i need media converters, SFP's, and expensive cable, probably closer to $250.
Have been reading about lightning strikes and frying equipment. That being said, i live in Vancouver, and haven't seen lightning in years :)
Copper is always going to be cheaper and easier to work with. The only advantage glass has over copper is link length. You can go much further with fibre than copper.
If you are going to run fibre, do two runs. Use one for the connection and keep the other one dark in the (unlikely) event you need it. It's cheaper to do it at the same time than in the future. And in the event you have issues with the first fibre run, you can swap over to the second easily to verify/validate issues.
If it only costs you $250 to get the gear for an exterior fibre run, definitely do two. $250 is a steal, it usually starts at $1K for outdoor fibre.
-
what about risk of lightning strike? thanks for the reply Tim.
-
@xman111 said in Network security in garage:
what about risk of lightning strike? thanks for the reply Tim.
IMHO the probability is low that you'll attract a strike.
Also, there are varying degrees to lightning strikes. If it's not a direct hit, somethings may survive. But if your telco gets hit by a direct lightning strike, that has a higher probability of frying everything. Not even your retail surge protectors can protect against a direct lightning strike.
The worst thing about a lightning strike is static electricity. It electrifies the air and everything around it to certain degrees. So you could theoretically have a tree outside your window get hit, and the static electricity can be strong enough to damage (not destroy) electronics.
So I rarely if ever take lightning into consideration when designing a home network. I have a client with a detached garage, similar probably to your situation. He's on top of a mountain in PA that is prone to lightning storms. Never had an issue, and we ran 250' of copper to his garage from the main house.
I don't worry about lightning.
-
@xman111 said in Network security in garage:
Have been reading about lightning strikes and frying equipment. That being said, i live in Vancouver, and haven't seen lightning in years :)
Well, there has been a lot of installed copper for decades before fibre was available. If you're worried you can get surge arresters for Ethernet. How far is the run? Is the garage electrical system fed from the house? Also, there is no electrical connection between Ethernet cables and interfaces, PoE excepted. However, there is supposed to be isolation between the PoE part of the equipment and the rest. The signal passes through a transformer, which can withstand a significant voltage. The original 10baseT Ethernet (StarLAN) was designed to work over cables shared with telephones. An analog phone line can have typically 90V 20 Hz AC on it when ringing. The NICs were designed to tolerate being mis-connected to a phone line. So, what's the risk in an area where lightning is rare?
.
Mmm, I think you have a higher class of burglar in Vancouver than we do in London if that's a real threat.
Only high class burglars can afford to live in Vancouver.
