Squid & Firewall Rules
-
I've put in rules on my pfSense firewall to block traffic between VLANs. I'm also using pfBlockerNG to implement Talos, Emerging Threats, and DShield IPv4 blacklists.
I would also like to implement Squid and ClamAV, but when I do this, my firewall rules are ignored; it allows HTTP/HTTPS traffic across VLANs and to IPs on the blacklists.
It's my understanding that this is how Squid is supposed to work, however, I'm wondering if anybody has a workaround which would allow me to implement Squid and still have my firewall rules apply?
Thank you,
tscheese -
You need to be a lot more specific on how you are trying to set this up.
Describe your network layout and how you are setting up squid.
I run Squid, pfBlockerNG-devel, and Suricata on my network with 3 subnet's which one
is wireless and there is no traffic to my other 2 subnet's.If you enable transparent proxy Squid does enable it's own firewall rule also if you select
Allow Users on Interface on the general setup page's all user's on that interface or interface's will be able to communicate.I run mine in non-transparent with browser's manualy configured and since I have 3 subnet's
say 192.168.1.1/24 my proxy setting's in my browser setting's are 192.168.1.1 port 3128 for the system's in that subnet.
If the second subnet is 192.168.2.1/24 the browser setting's for those system's would be 192.168.2.1 port 3128.My subnet's I allow are entered into the allowed subnet's box under the ACL's tab in squid.
I am sure similar to this could be accomplished with VLans and transparent but you will
have to find the firewall rule's squid insert's and make them work with your's, I believe
Doktornator posted them once on the old forum's but that's been a long time ago. -
Thank you very much for your reply; it’s greatly appreciated. I’ve provided a little more detail about my setup, below:
I have a number of VLANs setup on different subnets: LAN, Guest, Management, Voice, and a few more.
I have rules in-place on each interface, blocking traffic to an alias, which contains all of my local subnets. This rule works as I would expect.
I’ve installed Squid and turned it on in transparent mode, but other than that, I’ve done no further configuration. Now, for example, users on the LAN VLAN can access the HTTP page of my switches on the management VLAN and my IP PBX in the Voice VLAN.
I’m hoping someone could point me in the right direction, so that I can configure Squid to be transparent, but still not allow traffic between VLANs and also leverage the block lists generated by pfBlockerNG. Based on your reply, it sounds like there may be some firewall rules put in-place by Squid that I cannot see?
-
*Bumping this post.
I'm surprised nobody else is having a similar issue with Squid.
-
Nobody else has a similar issue because there are clearly labeled and documented options in squid to prevent exactly what you are seeing.
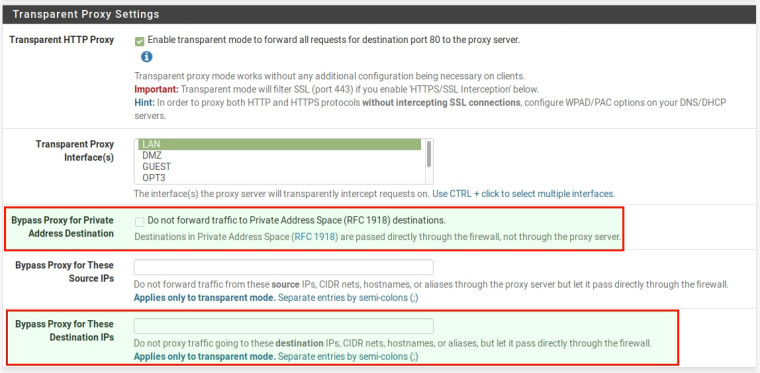
Check the box in squid labeled Bypass Proxy for Private Address Destination. Alternately, use your alias in the Bypass Proxy for These Destination IPs list.
-
@jimp
Thank you very much for your reply! This solved my problem.I suppose I could have worded my previous comment a little differently. I've found lots of others online who are having a similar troubles. As such, I wasn't so much surprised that nobody else was having the same issue, rather, I was surprised that I hadn't yet found an answer similar to what you've provided, above.
Thanks again for your help with this!