blocking traffic between interfaces
-
Hello,
I am using pfsens with the last version and I have multi interfaces:
wan: 192.168.0.2/24 with gw 192.168.0.1
lan 192.168.1.1/24
wifi 192.168.2.1/24
management 192.168.3.1/24
I want to allow lan and wifi using internet but not routing between them.
I want to allow port 80 from wifi to lan.
I want to allow management can route to lan and wifi but no internet working on it.
I want to allow management ip 192.168.3.2 can route to lan and wifi and have internet access.
I am using manul nating and enable it only from lan to wan and wifi to lan and management to wan
I try to make that with multi ways but I didn't success.
so what the rule should I have to do ?
thanks. -
Nobody is going to write all your rules for you. Show us what you have done and we can make corrections if there are mistakes.
One mistake a lot of people make is that they forget to clear the existing states after changing the rules. Existing states will NOT be affected by a new rule or modifying an existing rule.
-
I would read a little here first to understand how the pfSense firewall works and how to setup and configure rules:
https://www.netgate.com/docs/pfsense/book/firewall/index.html
If you have any questions after that, please let us know and we can help you with specifics.
Hope this helps.
-
This post is deleted! -
pls check the attached file:
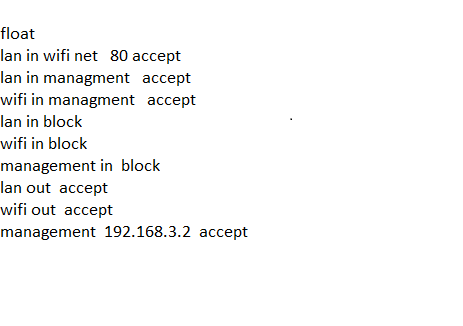
thanks. -
Dude post a screenshot of your rules tabs
example
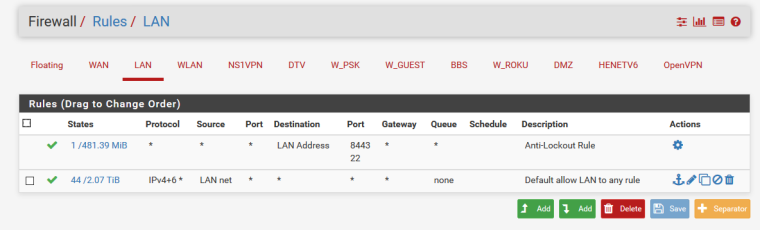
-
@aminbaik said in blocking traffic between interfaces:
Hello,
I am using pfsens with the last version and I have multi interfaces:
wan: 192.168.0.2/24 with gw 192.168.0.1
lan 192.168.1.1/24
wifi 192.168.2.1/24
management 192.168.3.1/24
I want to allow lan and wifi using internet but not routing between them.
I want to allow port 80 from wifi to lan.
I want to allow management can route to lan and wifi but no internet working on it.
I want to allow management ip 192.168.3.2 can route to lan and wifi and have internet access.
I am using manul nating and enable it only from lan to wan and wifi to lan and management to wan
I try to make that with multi ways but I didn't success.
so what the rule should I have to do ?
thanks.If you want to "isolate" subnet , you can do it in few clicks, just assign your gateway under your lan firewall rule "any to any", go trought "advanced tab" and swap Gateway "Default *" to your gateway specific name.

And rule looks like this:

Additionally you can block incoming tcp/udp packets, from other interfaces by adding specific blocking rule at top of your interface rules grid for extra secure, but usually is enough specific only gateway than default. Check this by yourself!
Cheers. -
No.
Do not rely on routing to block traffic.
If you do not want DMZ hosts to access LAN hosts, then block traffic on DMZ to destination LAN network.
-
@babiz
thank you so much … its working now :) -
Yes @aminbaik , but same as @Derelict said, is not best pratiche, (forcing gateway on standard firewall rule to rely "blocking stuffs" at routing stage instead a proper firewall rule), anyway for smallest enviroments just work enough, I have this kind of configuration because here is no bigger hackers
 and I not noticed any issue related this kind of basic rule setting..
and I not noticed any issue related this kind of basic rule setting..
Goodbye!