Server listening on different interfaces
-
Hello,
I am new here, maybe you boiz already had this answered but i didn't managed to find it.
Long story short :
2.4.3-RELEASE-p1 (amd64)- Server is configured under wan interface
- wan interface has private ip to which public ip is routed, so firewall has virual ip configured (public).
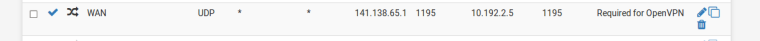
- in order this to work i have port forward and corresponding rule (wan) : source any => destination public port udp 1195 to wan interface private
Vpn connection works like this.
However now i have request to enable vpn connection which comes to internal (trusted) interface. Don't ask why. it's long story.
I tried with same port forward but now configured under internal interface, that didn't work. I can see traffic coming but vpn server doesn't respond. Or at least it's not responding trough internal interface.
Internal interface has rule allow everything.I dont want to configure another vpn server tied to internal interface because than client would need two config files if they work from home or at the office in dmz lan (this dmz is behind cisco router and acl's)
Thank you in advance.
Regards
-
So you port forward to pfsense wan IP 1195..
Why would you think you need another vpn instance to get anywhere from this vpn connection?
I would suggest you draw up your network and where your vpn clients need to connect too.
-
This post is deleted! -
They need vpn connection to jump between vlan's
Diagram would be looking something like this
Pfsense firewall (at DataCenter)
Cisco router (on-site using DMVPN to connect to DC)
Cisco switch (on-site)Customer on-site has couple of corp vlans and DMZ for some testing purpose. DMZ is configured on router where access to rfc1819 is blocked, only internet access.
Now they want to use vpn from DMZ if is sometimes they need resources in corp vlans.I can't get this vpn connection to work if it comes from DMZ, as i said from Internet it works, from internal i can see openvpn traffic coming but no connection established, or any packet replay.
-
How is that a diagram?
Break out crayons and a napkin if you need to - and label the different networks.. With actual network address space as well ie 192.168.0/24, 172.16, 10/? etc. etc..
Pfsense firewall (at DataCenter) Cisco router (on-site using DMVPN to connect to DC) Cisco switch (on-site)How as that a Diagram???
-
@johnpoz
Ahhh, i am not able to draw now.I can type and send few screenshots
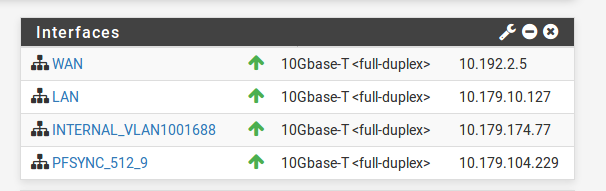
interfaces
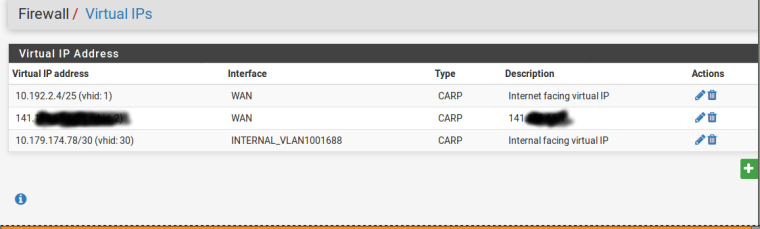
virtual ip's
port forward for openvpn
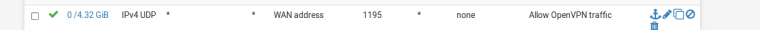
rule to allow vpn traffic
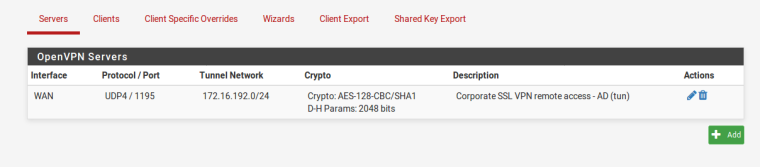
and finaly openvpn server
All this is fine if traffic is coming from Internet to public 141.....
But when traffic is coming from internal_vlan1001688 it doesnt workSubnets coming to this internal interface
192.168.11.0/24
192.168.14.0/24
192.168.111.0/24(192.168.11/14.0 are pushed trough vpn)
192.168.111.0/24 is considered as DMZ and it's blocked to jump to other 2.
That block is done on a router which comes before pfsense. Now i want to be able to turn on existing vpn and than users should be able to jump to other two vlans.Thanks
-
So your running HA pair setup... Kind of should of mentioned this out of the gate ;)
Why would you be running public IP vip on a rfc1918 network and then forwarding to it?
If you have traffic hitting interface X, and you wan it to be able to get to the IP and port your vpn instance is listing on - then just put a rule on that specific interface X to allow allow it.