Dual routing from OpenVPN server to Client Internet
-
I have successfully setup an OpenVPN between two Pfsense 2.4 systems. One is the OpenVPN Server, and the other is the OpenVPN client.
OpenVPN Server can access the OpenVPN Client LAN no problem.
OpenVPN Client can access the OpenVPN Server LAN no problem.
OpenVPN Server cannot access the OpenVPN Client's internet connection.
OpenVPN Client can access the OpenVPN Server's internet connection no problem (with the right NAT and firewall rules).
Is it even possible for the OpenVPN Server to be able to access the OpenVPN Client's internet connection. No matter what rules I try to put in place, I can't get it to work. Before getting into details of potential rules to make it work, I just want to ask whether what I am trying to do is even possible?
-
Why would you even use the Internet Connection from the far side? I don't get your point...
-Rico
-
avoid geobkocking
-
Can't say I've ever tried it that way... it's usually the other way around due to the server typically having the faster connection, but the short answer is yes. You should be able to policy route specific server-side traffic over the tunnel and then NAT it out the client-side WAN.
-
You will need to policy route the traffic out the OpenVPN to the client side most likely.
I can't imagine a very satisfactory experience if both sides have redirect-gateway enabled to the other.
-
@derelict said in Dual routing from OpenVPN server to Client Internet:
You will need to policy route the traffic out the OpenVPN to the client side most likely.
I can't imagine a very satisfactory experience if both sides have redirect-gateway enabled to the other.
I've finally got time to get back to this. To create a policy based route, I need:
- On the OpenVPN server I don't have a VPN interface like I do on the OpenVPN client.
- Without a VPN interface in existence, I cannot create a route
If I try and manually create a VPN interface on the OpenVPN server, the VPN dies immediately as that's not the way to setup an OpenVPN server. The client is the one with the interface, and it establishes a connection to the OpenVPN Server.
-
Server, Client. Doesn't matter.
You ALWAYS have to bounce the OpenVPN instance after you assign an interface. Did you do that?
-
@derelict said in Dual routing from OpenVPN server to Client Internet:
Server, Client. Doesn't matter.
You ALWAYS have to bounce the OpenVPN instance after you assign an interface. Did you do that?
It might be helpful to re-read my original post as to how the OpenVPN works today. Also, note that the OpenVPN was setup by netgate support.
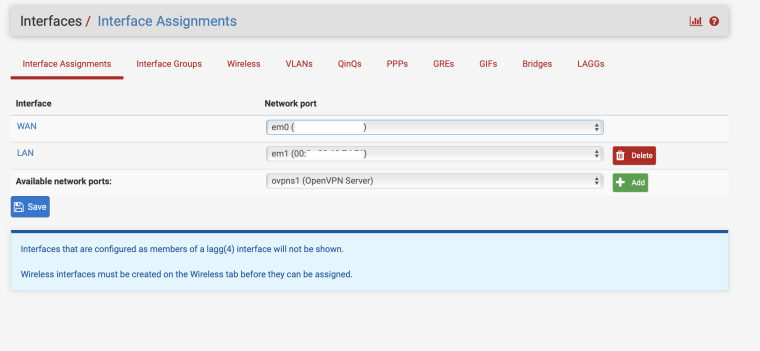
Here is the server side interfaces:
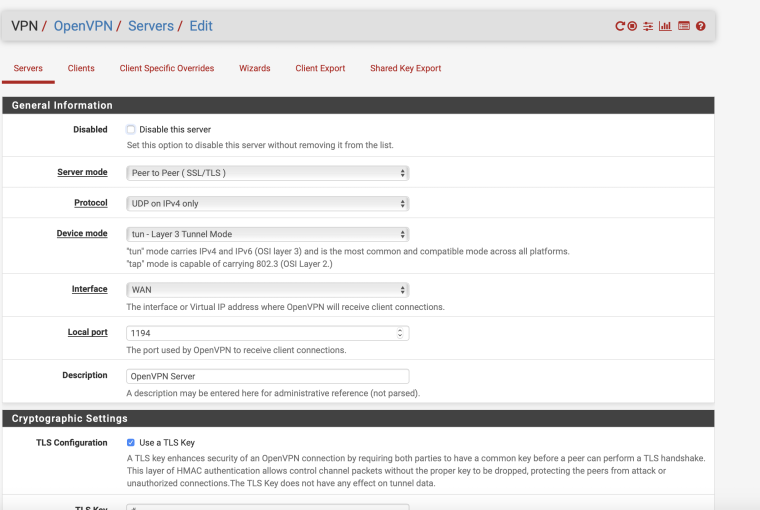
Here is the server side VPN server config:
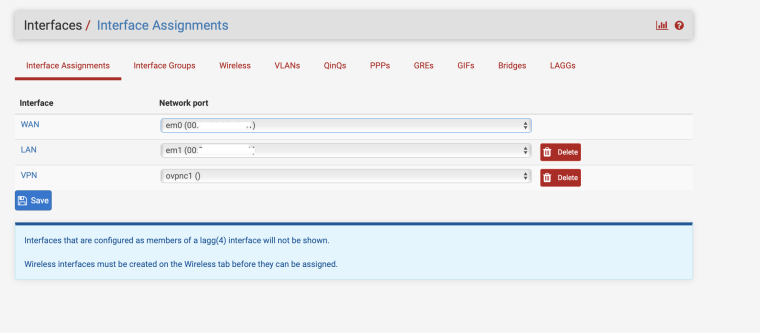
Here is the client side interfaces:
-
You have to policy route everything across it. To do that you need an assigned interface. You don't have one assigned. So assign one.
Then bounce the OpenVPN server or it will not pass any traffic after the interface is assigned.
-
@derelict said in Dual routing from OpenVPN server to Client Internet:
You have to policy route everything across it. To do that you need an assigned interface. You don't have one assigned. So assign one.
Then bounce the OpenVPN server or it will not pass any traffic after the interface is assigned.
The moment I create an interface on the server side, the OpenVPN breaks. Also, according to the manual, it says exactly not to do that.
-
Negative.
The moment you assign the interface the VPN breaks. THEN you have to stop and start the server process. Client or server. Does the same thing.
Show me in the manual where it says not to assign an interface to an OpenVPN server.
-
@derelict said in Dual routing from OpenVPN server to Client Internet:
Negative.
The moment you assign the interface the VPN breaks. THEN you have to stop and start the server process. Client or server. Does the same thing.
OK - let me give that another go and I'll revert. Cheers.
-
@larrikin said in Dual routing from OpenVPN server to Client Internet:
The moment I create an interface on the server side, the OpenVPN breaks. Also, according to the manual, it says exactly not to do that.
Well, I can neither confirm nor deny what's in the manual since I personally haven't read it, but we can tell you what works. It's fairly straight forward and much like Derelict mentioned. In order for a gateway to show up for policy-based routing, you have to assign the tunnel to an interface. Once the tunnel is assigned to an interface, having issues passing traffic over that tunnel is often expected. Bouncing the service (Status -> Services) that the tunnel is running on resolves the connectivity issues from the act of assigning a tunnel to an interface.
I've seen multiple how-to's, wiki's and forum posts that specifically tell you to bounce the tunnel after assigning it to an interface or traffic will not flow properly.
-
@derelict said in Dual routing from OpenVPN server to Client Internet:
Negative.
The moment you assign the interface the VPN breaks. THEN you have to stop and start the server process. Client or server. Does the same thing.
Show me in the manual where it says not to assign an interface to an OpenVPN server.
You are right. It worked. Many thanks.