Forward Public IPs to VPN Clients *LAN*
-
Heyo Folks,
I am having so much trouble on getting this network setup.
What I'm trying to do is forward a Block of IPv6 of a remote server (SERVER A) [2a06:AAAA:A:AAAA::/64]
Similar to how HE's TunnelBroker provides IPs, Unfortunately TunnelBroker does not work in this case because they Block CloudFlare (YES THEY FREAKING BLOCK CLOUDFLARE!!!).Followed this article to a TEE >> https://techblog.synagila.com/2016/02/24/build-a-openvpn-server-on-ubuntu-to-provide-a-ipv6-tunnel-over-ipv4/
Used this article as a resource >> https://feeding.cloud.geek.nz/posts/ipv6-and-openvpn-on-linode/
Looked at this article and I don't have PFsense on both servers only on Server B>> https://forum.netgate.com/topic/42698/how-to-openvpn-tap-bridging-with-lan
What about IPv6? >> https://forum.netgate.com/topic/35151/openvpn-bridging-config-how-to/2
(Server A) is limited on what I can do with it, Its a Debian OpenVZ Container.
I'm able to Connect to the OpenVPN server and ping tunnels and Outside Network.
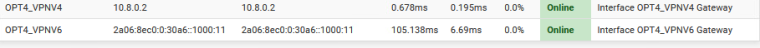
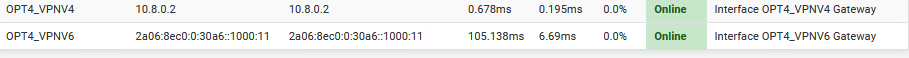
(Server B) is a pFSense Router connecting to (Server A). I'm able to Ping (Server A) just fine and able to do Test Ports just fine under that Interface(OPT4 (ovpnc1)).Here's were i'm having trouble!!
I have a LAN setup on (Server B) and I'm trying to Setup the Lan's IPv6 to use an IP of the VPN's Network [2a06:AAAA:A:AAAA::/64] it fails and says that its overlapping the VPN Tunnel. :(I've tried splitting the Tunnel's network to be different subnets ex [Tunnel 2a06:AAAA:A:BBBB::/64] I am able to set LAN's Interface to be [LAN 2a06:AAAA:A:AAAA::1] and LAN devices get assigned inside the [LAN 2a06:AAAA:A:AAAA::/64] network.
Devices in this network are not able to communicate to the OpenVPN Server. (No ping,no Internet)
Tried Setting a Static Route to route [2a06:AAAA:A:AAAA::/64] via [Tunnel 2a06:AAAA:A:BBBB::/64] as gateway.. Failed.
Tried Setting a Firewall Rule on LAN to set Gateway as [Tunnel 2a06:AAAA:A:BBBB::/64] and that still failed.
Tried Setting the VPN Settings to have Remote Network as [2a06:AAAA:A:AAAA::/64] that also failed.Tried Changing the Tunnels Network back to [Tunnel 2a06:AAAA:A:AAAA::/64] and left LAN still having [2a06:AAAA:A:AAAA::/64] for the fun of it. that still failed. Nothing could communicate (the routes were bad)
Decided to go smaller, Broke it down to smaller subnets
[Tunnel 2a06:AAAA:A:AAAA::1000/100]
[LAN 2a06:AAAA:A:AAAA::2000/100]Tunnel Adapter (Server B Client 2a06:AAAA:A:AAAA::1000:1010) is able to Ping SERVER within (Tunnel 2a06:AAAA:A:BBBB::1000:11) Vice Versa.
LAN is not able to PING OPENVPN SERVER but is able to PING Tunnel Adapter (Server B Client 2a06:AAAA:A:AAAA::1000:1010)Tried doing, the same Static Route as the Entire [2a06:AAAA:A:AAAA::/64] to be routed via (Server B Client 2a06:AAAA:A:AAAA::1000:1010) .. That failed as well.
Tried Setting a Firewall Rule to route everything through that gateway and had no effect.
Tried Setting the VPN Settings to have Remote Network as [2a06:AAAA:A:AAAA::/64] that also failed.
...I am out of Ideas, any ideas would be helpful
Thank you in Advance.
-
You need to push the IPv6 /64 as a route. It needs to be distinct from the tunnel network. I assume you have more than a /64 to use? /48 or /56?
Similar to how HE's TunnelBroker provides IPs, Unfortunately TunnelBroker does not work in this case because they Block CloudFlare (YES THEY FREAKING BLOCK CLOUDFLARE!!!).
Based on my experiences with HE over the years, if they did in fact block these sources, they have a good reason for doing so.