pfSence network order and VM ware 15
-
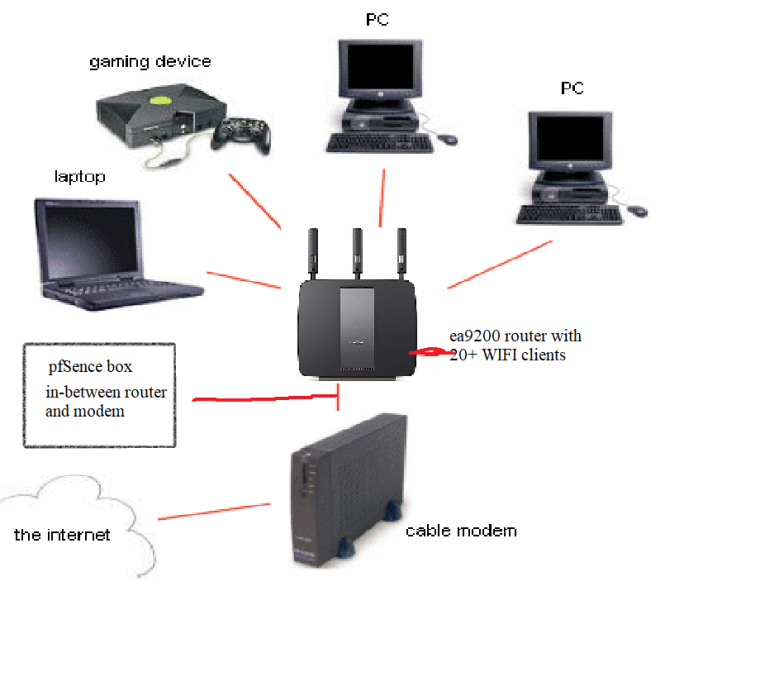
im trying to use pfSence as a simple cache proxy in VMware 15 pro via squid plugin. my network is a simple cable modem attached to a linksys ea9200 router with the new box before the router. it is my understanding that all traffic must pass thru the box then to router.
i have 2 onboard NIC's one directly from cable modem (wan) and the (wan) port on the ea9200 labeled blue plugged into the other as LAN. Pfsence detect both fine and works as far as itself.
issue is the box has network but none of my clients do via WiFi and LAN. admittedly I don't know if im doing this right or if i have to use certain port on the router. I've tried several guides and certain i have VMware working right.

-
Try to post a network diagram.
Pf is essentialy a router and a firewall
Do you still need the linksys? And if yes, it should only server traffic to the pf. -
I must have the router as it my backbone for Wifi clients and some lan.
this diagram is what i think it should look like via hardware. however i suspect i dont have something connected in the right port or maybe Nic settings in VMware.
-
@unsunghero Please show more detail for the in between part.
Also at least describe the private lans.
The ea200 shoud be configured to act as a lan switch and wifi access point but not as a router.
It makes the situation complicated and probably introduces double nat.Any soecific goals for your lan/wifi?
As for vmware, why host only second interface?
You need two bridged interfaces pingable from the cable modem and from your lan respectively, to begin with. -
this is a straightforward no thrills home network no Vlans only 3 pieces of hardware: router, modem, pfsence box. The private lans only TV's the main bulk is WiFi clients. the only goal is take my basic home network and toss in Pfsence as a cache proxy that's it, however after everything is setup nothing after the router has internet.
as for the host only several guides stated to block intruders as its in a open environment. please keep in mind im running this VMware with other services running such as file shares and Plex and don't feel like sharing with the world.
auto bridge em0>WAN modem
host only em1> Ea9200 ROUTER connected from the internet port to em1 lani know the Ea9200 HAS bridge mode have no idea if it makes the WIFI open (no password) do i need to have it enabled so it stops DHCP and just switches? i want to maintain my WIFI secured as it currently is.
-
@unsunghero These several guides are obviously irrelevant to your situation. And certainly isn't a three piece hardware since vmware is involved.
Host only means, the vm will only talk to the vmware host.
Now, unless the ea9200 is also your vmware host, traffic will never reach it. It is very expected for only the pf to have internet and nothing else. (and also very secure too :P )
Moving forward, since the ea9200 is a router, there is no non ethernet wan to bridge.You need to rething your situation.
intruders are stopped at the pf level.
vmware offers complete isolation however pf needs to physically take traffic from the cable modem and nat it to your lan, so it needs physical network access to both.
The ea9200 is not needed anymore and will be used only as a wifi access point and/or lan switch.Your other vm's are bridged to the internal network, receive internal ip's (either static or via dhcp (provided preferably by the pf) and are protected since they are behind nat.
(keep ipv6 disabled until you feel confident with it, since it is not natted by design)
After this works, then you need to experiment with the caching solution of your choice and add as much security as you wish. -
this is just an old clunker with i-7 3770k with windows 10 as the host system. also running on the host OS is plex,shares,NAS attached to it. PF is my only VM running all on one bargain barn computer. so my network on the front is only 3 pieces of hardware. and do not want anything to happen to it.
- Is it PF's firewall that's blocking all traffic? and i have everything physically connected right?
- having auto bridge on both will let people see my local network on the host system?
- do i enable bridge mode or not on the router as this is a feature? so it just switches then plug the cable into the wan port on it? (this will be em1 LAN to PF so the rest of my stuff has internet)
- why is this so hard when i really feel this a simple fix or someone just tell me "hey retard you got it plugged in all wrong now do these next 3 steps and your done."
I appreciate your help
-
@unsunghero 1. Its pf lack of communication with your lan.
2. No. The lan side of the pf isn't allowing any inward traffic (and you are behind nat besides)
3. No bridge mode is required. Also no other router except pf is required.
4. Its not hard. Just complicated -
I just take it off of auto DHCP and set the routers static IP to fix all this mess? i really dont understand all the plethora of settings in PF let alone navigating it.
-
@unsunghero The sort answer is unfortunately, NO.
pf is an enterprise grade firewall solution. It is never meant to be a plug and play box. It can do many complicated things, but then its like driving a racing car.
You have more things to do apart from the steering wheel and the gas pedal.
Here is a great reference for all things pfsense
https://www.netgate.com/docs/pfsense/book/
It will answer all your questions, but then you need to invest some time and effort.