OpenVPN Remote Access connection problem
-
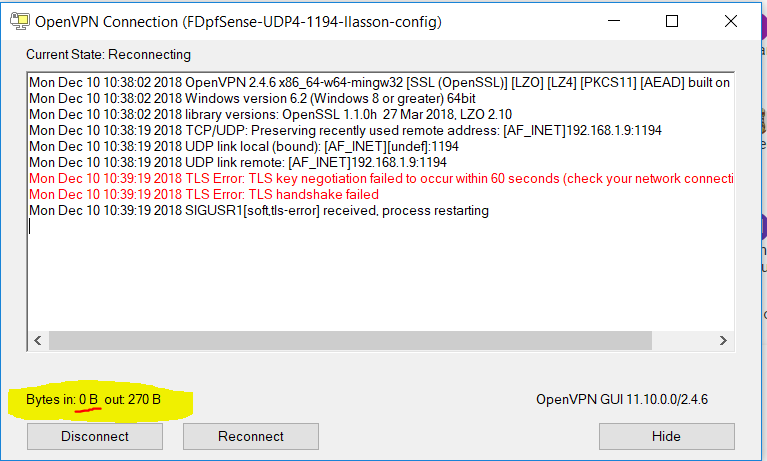
Hello. I'm new to pfSense and I'm trying to setup an openVPN in my lab. The Netgate SG-3100 running pfSense 2.4.4 - P1. When I try to connect, it acts like the server isn't listening and no bytes are returned in the handshake and I get the 60 time out.
WAN 192.168.1.1
LAN 192.168.55.0/24
Tunnel Network 192.168.60.0/24Server config:
dev ovpns1 verb 1 dev-type tun dev-node /dev/tun1 writepid /var/run/openvpn_server1.pid #user nobody #group nobody script-security 3 daemon keepalive 10 60 ping-timer-rem persist-tun persist-key proto udp4 cipher AES-128-CBC auth SHA256 up /usr/local/sbin/ovpn-linkup down /usr/local/sbin/ovpn-linkdown client-connect /usr/local/sbin/openvpn.attributes.sh client-disconnect /usr/local/sbin/openvpn.attributes.sh local 192.168.1.9 tls-server server 192.168.60.0 255.255.255.0 client-config-dir /var/etc/openvpn-csc/server1 username-as-common-name plugin /usr/local/lib/openvpn/plugins/openvpn-plugin-auth-script.so /usr/local/sbin/ovpn_auth_verify_async user TG9jYWwgRGF0YWJhc2U= false server1 1194 tls-verify "/usr/local/sbin/ovpn_auth_verify tls 'fdservercert' 1" lport 1194 management /var/etc/openvpn/server1.sock unix max-clients 10 push "route 192.168.55.0 255.255.255.0" ca /var/etc/openvpn/server1.ca cert /var/etc/openvpn/server1.cert key /var/etc/openvpn/server1.key dh /etc/dh-parameters.2048 tls-auth /var/etc/openvpn/server1.tls-auth 0 ncp-ciphers AES-128-GCM persist-remote-ip float topology subnetClient config:
dev tun persist-tun persist-key cipher AES-128-CBC ncp-ciphers AES-128-GCM auth SHA256 tls-client client resolv-retry infinite remote 192.168.1.9 1194 udp verify-x509-name "fdservercert" name auth-user-pass pkcs12 FDpfSense-UDP4-1194-llasson.p12 tls-auth FDpfSense-UDP4-1194-llasson-tls.key 1 remote-cert-tls serverThe client shows:
I have reset and started over a number of times over the last two weeks. I've tried different server modes for Remote Access all with the same result.
What else should I try or document to help resolve the problem?
Thanks in advance for your help.
Lee -
Did you run through the wizard or manual setup?
Firewall Rules in place (WAN Interface)?
Anything happens in the pfSense OpenVPN Log when the Client tries to connect?
Since your WAN is RFC1918 you have the Options Block private networks and loopback addresses and Block bogon networks for the WAN Interface unchecked, right?-Rico
-
Are your packets even hitting your WAN? Double NAT is really never a good idea for servers if you can help it.
Packet Capture is your friend.
-
@leelasson said in OpenVPN Remote Access connection problem:
WAN 192.168.1.1
Where exactly is your client? Unless its on the wan network your going to have issue getting to a rfc1918 address from the internet ;)
Also you list wan as .1 but openvpn is listening on .9? So you setup a vip?
Also mentioned if your on the wan network 192.168.1 and trying to test this you would have to make sure you disable the block rfc1918 on your wan interface.
-
-
@Rico mentioned that in the first post..
-
@rico you nailed it also. However, I didn't uncheck the second option 'Block bogon networks'. What may fail with the Block bogon networks still checked?
I will be moving this to the Internet and will re-check the rfc1918 on deployment. For now I'm just getting used to pfSense in my lab and appreciate the lesson!
Thanks to you and all who replied.
Thanks,
Lee -
What would fail with bogon still blocked is bogon's - but pretty sure pfsense pulls the rfc1918 space that is normally in bogon out... And lists in the different rfc1918 listing.
rfc1918 is a bogon ;) Well if you want to get technical about its - better term is prob martian...