Numerous ET SCAN Potential SSH Scan OUTBOUND alerts. Is Pfsense infected?
-
@boobletins Thanks for your help!!!! I disabled the ntop wan interface and No more alerts!
-
@chromefinch said in Numerous ET SCAN Potential SSH Scan OUTBOUND alerts. Is Pfsense infected?:
@boobletins Thanks for your help!!!! I disabled the ntop wan interface and No more alerts!
So your firewall was infected -- but with ntop instead of a trojan ...
 . (Just kidding).
. (Just kidding). -
@boobletins Yup lol I sure did have ntop installed. Must have been a bug with the package because I haven't gotten anything since the reinstall. Now I will know what to look out for!
Great work guys. That makes me feel a little bit better about my security :p
-
I'm having same issue with ntop .. .. seems to try ip's like 0.106.219.157...
installed, reinstalled several times. ... anyone might know what is the issue? -
This post is deleted! -
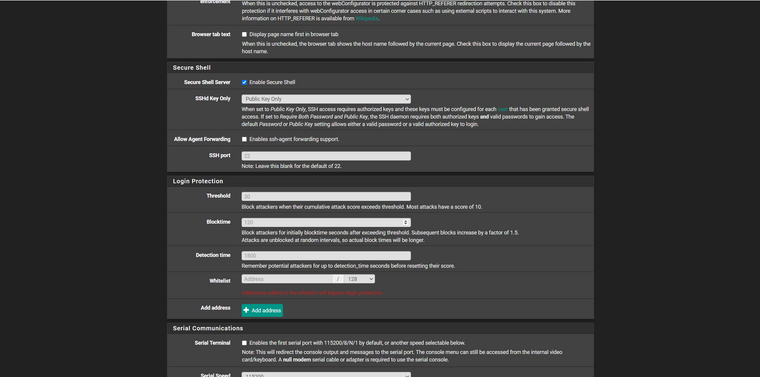
@lambro690 Same like me, but I prepared to protect my firewall with pivate and public key, and limit access to my firewall with SSHd Key Only > Public Key Only.
-
I have the same problem and even more dangerous behavior from pF after latest ntop update. Even my avahi demon send mdns externally!
I'm on the latest pF 2.5 btw.I found this is due ntop bag and resolved by turning off hosts discovery in ntop itself.
If you are affected is easy to check after ntop update by visiting ntop host details page where you will see a lot of errors.I also added all my local networks under the ntop settings in pF.
This stop pF from crazy behavior with this snort allert, mdns and also fixed host details page in ntop itself.
I think this ntop bug affecting only folks with WAN enabled under ntop setting in pF but didn't check that.
Annoying thing is that after rebooting your pF you need go to ntop setting page in pf and just clink save all settings again.
-
I have the same problem and more dangerous behaviour from pF after latest ntop update. Even my avahi demon send mdns externally!
I'm on the latest pF 2.5 btw.I found this is due ntop bag and resolved by turning off hosts discovery in ntop itself.
If you are affected it is easy to check after ntop update by visiting ntop host details page where you will see a lot of errors. This behaviour is discovered even you not using ssh on your pF so changing logging behaviour don't make sense.I also added all my local networks under the ntop settings in pF.
This stop pF from crazy behaviour with this snort allert, mdns and also fixed host details page in ntop itself.
Don't have time enough to check if all this mess really go outside or just happened on localhost interface with ntop.If still not updated bug you can contribute on freeBSD forum for it.
I think this ntop bug affecting only folks with WAN enabled under ntop setting in pF but didn't check that.
Annoying thing is that after rebooting your pF you need go to ntop setting page in pf and just clink save all settings again.
Final conclusion is if you have any package wrong configured on your pF then you can become in internet even like an attacker regardless you are reseeding not your own traffic.
Maybe good way to truly test all updates on pF platform :) not simply fork them.How you run the process is important too because I feel ashamed a bit that my pF firewall became unaware that behave like a worm for resident and friendly network by simply copy redundant traffic across interfaces because one of the distributed packages wasn't test enough.
Form me personal interesting in this is how you are utilise your pF when this can become dodgy for your network. All about is use the tools, analyze the logs and do the tests :)
I love pF btw always my recommendation like you can see in open source we can resolve a lot annoying problems. :)