Windows Defender and pfSense
-
@johnpoz
Thank you. I will try to see if i can do as you described. -
@johnpoz
Nothing in front of pfSense, it is running and i use some of my devices with it, including Xbox over a dedicated NIC and LANDMZ with UPnP enabled and firewall disabled completely. That is the only way i was able to have an open NAT with it.
The rest is a bit hard for me as first i have to become familiar on a few things, before being able to understand how to do it. The ISP said they are not filtering any ports. -
I did it, I now have an open NAT.
What i did is the following.
Assign a static Mapping to the PC. (I had already done this). Added static ports.
Firewall > Aliases > Create an Alias for my gaming pc.
Firewall > NAT > Outbound > add PC there > add pc to ACL.
Port Forwarding was already created for the specific game.Tested the game and it has now open NAT.
I thank everyone for pointing me in the right direction. I have another question. Is what i have done correct or would it expose me to some atrocious threats?
-
You did what? You set everything from that PC to be static outbound? Yeah that is NOT the right way to do it.. Unless that PC is the only device on your network behind the napt..
What I said to do was look to see which ports the game used that were static, and then set those up as static outbound.. Not EVERY connection from the PC..
Your going to run into issues with such a setup.. What happens when device A used port X as source.. And then your PC wants to use X as source as well.. Now what happens? The more devices you have the more sessions they create the more likely you going to conflict with the source ports the PC wants to use.
You need to find the ports the game uses that require static source ports. Not set every port your pc ever uses on every connection as static.
-
Oh... hmmm.
i may have to do some more digging then.
Sadly, I believe my whole setup is well, how to put it, just ... meh. -
Does anyone know of a good and easy book that would help me with the basic of networking so that i may be better equipped (and use it as a reference) to better follow advice on this forum and/or the available manual?
-
Have you read the pfsense book?
Linked too in my sig..Or you looking for something more basic to tcp?
-
I am reading the pfSense book here and there, meaning as needed. Yeah, i definitely need something more basic, to fill in some knowledge the pfSense book assumes.
-
Have you checked out
http://www.tcpipguide.com/ -
@johnpoz Thank you very much. I will work a bit with it. Whenever i need to lknow what the pfSense book is talking about i can fall back on the TCP/IP guide.
-
What does it mean to validate my game? How can i do so? Where do i look for what ports are open and if static or not?
-
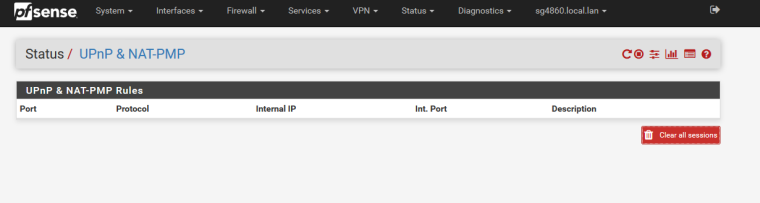
When you enable UPnP - you can look in the interface of UPnP and see what ports got opened and if static or not, etc.
-
I reversed the modifications i previously had done.
I restored pfSense to a previous configuration.
I enabled UPnP on my LAN as well. Nothing shows up under StatusUPnP & NAT-PMP. It is completely empty.
As far as firewall logs go, nothing from my PC tries to connect to any of the ports listed by the game provider. Yet i keep having that strict NAT.in the states all i can see is this:
LAN udp .192.168.xxx.xxx:3074 -> 185.34.107.128:3074 MULTIPLE:MULTIPLE 117 / 2 6 KiB / 86 B
LAN tcp .192.168.xxx.xxx:65145 -> 185.34.107.238:3074 ESTABLISHED:ESTABLISHED 296 / 287 63 KiB / 151 KiB
LAN tcp .192.168.xxx.xxx:49240 -> 52.200.29.218:3074 CLOSED:SYN_SENT 2 / 0 104 B / 0 B
LAN tcp .192.168.xxx.xxx:49241 -> 52.200.29.218:3074 CLOSED:SYN_SENT 3 / 0 156 B / 0 B
LAN tcp .192.168.xxx.xxx:49242 -> 52.200.29.218:3074 CLOSED:SYN_SENT 1 / 0 52 B / 0 B
LAN tcp .192.168.xxx.xxx:49244 -> 52.204.177.40:3074 CLOSED:SYN_SENT 3 / 0 156 B / 0 B
LAN udp .192.168.xxx.xxx:3074 -> 199.116.119.101:30380 MULTIPLE:MULTIPLE 46 / 43 6 KiB / 32 KiB -
Is this the right way to do what I am trying to do?
https://www.youtube.com/watch?v=whGPRC9rQYw
Is the person in the video showing "the right way"?
-
States can show you sure.. But just look in the UPnP interface.. It shows you what was requested and what was opened.
-
@johnpoz When I start the game on my pc nothing happens there with UPnP enabled. On the other hand it does show activity from my xbox.
What do you think of this method instead? is from the video i linked.
-
Status > DHCP Leases > add a Static Mapping for the gaming platform(s)
-
In static mapping fill in Client Identifier, give an IP address, Hostname, and Description > Save > Apply Changes.
-
Repeat steps 1 and 2 above for each gaming platform, if needed.
-
Firewall > Aliases > Add . Fill in the fields Name, Description, IP or FQDN and the description field next to it. If needed add mutiple Hosts, based on how many Gaming Platforms are needed. > Save > Apply Changes.
-
Firewall > NAT > Outbound > Select Hybrid Outbound Mode > Save > Apply.
-
in Firewall > NAT > Outbound, add a New Mapping. Interface: WAN, Protocol: Any, Source: Network for the Outbound Mapping: type in your Alias. and select 32 after the forward slash, "/". Scroll down to the section titled Translation and check Static Ports. In the bottom section named Misc, add a description. > Save > Apply.
-
Services > UpnP > check Enable UPnP & NAT-PNP > check Allow UPnP Port Mapping > check Allow NAT-PNP Poirt Mapping. Keep External Interfaces selection to WAN. Interfaces: slect the interface(s) used by your gaming platform(s). Check Default Deny at the bottom of the settings section.
-
make an ACL entry with the following format. allow 53-65535 "your gaming console Ip"/32 53-65535. Add other entries if needed. Save.
For Multiple gaming platforms NAT Reflection is needed. To Enable NAT Reflection do the following.
-
System > Advanced > Firewall & NAT > Scroll down to Network Address Translation section > set Network Default Mode for Port Forwards to Pure NAT. > check Enable Automatic Outbound NAT for Reflection. > Save.
-
Reboot your gaming Platforms.
-
Diagnostics > States > Reset States > check Reset the Firewall States Table > click Reset.
What if at step 8, "make an ACL entry with the following format. allow 53-65535 "your gaming console Ip"/32 53-65535. Add other entries if needed. Save." instead of opening all those ports i would only open 3074 for instance, but just tailored to the ports specified by the game provider. Would that help. I guess i would still need Reflection with multiple gaming platforms. Am I correct?
-
-
Would using IPV6 help solve the issue?