Subnet problem?
-
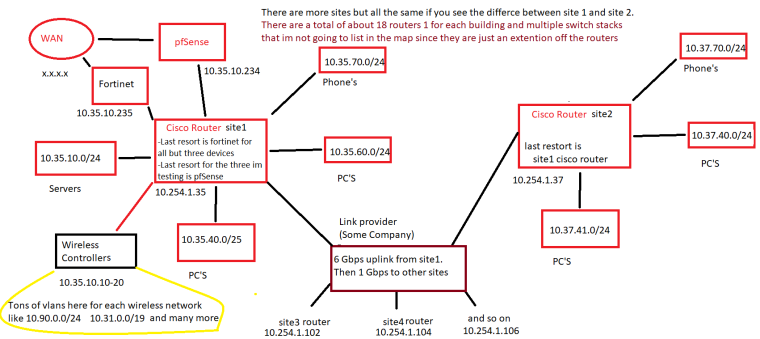
Ok I did it. If you need more on this god help me then lmao. There are many more vlans set up but we would need and entire wall to map it out completely. But this is the idea of it.
pfSense addon running are:
Squid Proxy Server
SquidGuard Proxy filter
DNS Resolver
softflowd
Suricata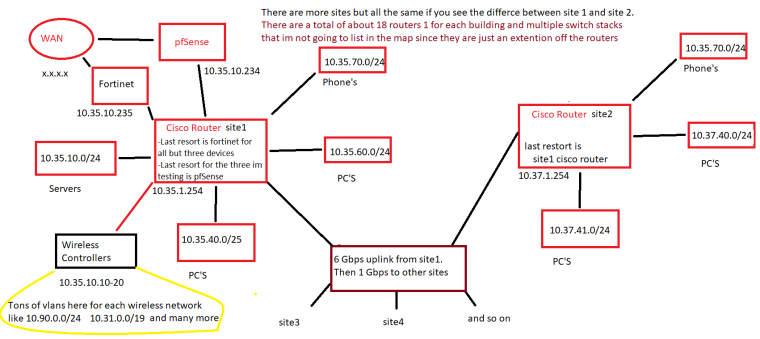
-
So your 10.35.10 should be a TRANSIT network servers should not be on this network. Or just create a new transit network to connect pfsense to your cisco. Say 172.16.0.0/30 or /29
So 10.37.1 is also a transit that connects your different sites cisco routers?
So is the plan to get rid of the cisco as well, or just use pfsense as new edge router?
So you have 18 routers in each site? That seems a bit excessive.. But without seeing the whole thing its hard to say how best to fix it.. Guess nobody ever heard of cisco 3 layer model? ;) Core, Distribution, Access?
-
@johnpoz
LOL no 1 Router per site with many switches. I just didnt map the switches.Sorry forgot about this - Technically the transit that connects the routers at the sites is 10.254.1 and the transit within the sites switches is what I listed
example these are all mostly Cisco C3850-24XS routers and C2960X-48FPD switches
10.254.1.35 and at this site switches start at 10.35.1.10 with router being 10.35.1.254
10.254.1.37 and at this site switches start at 10.37.1.10 with router being 10.37.1.254
10.254.1.102 and at this site switches start at 10.102.1.10 with router being 10.102.1.254
10.254.1.104 and at this site switches start at 10.104.1.10 with router being 10.104.1.254
etc.i just access them by the switch transit on the router itself. Also if at any point you peeps think I'm without hope lol let me know. I can't learn any better than making mistakes myself lmao. My boss/friend calls me his biggest asset as well as his biggest liability for a reason.
Also I am learning terminology as I go if you can't tell. Didnt even know what transit meant here until you used it a couple times and I figured out what you meant and wanted.
**As I said, I am not a net admin (but having fun learning it).
My sysadmin skills are no longer growing(I have come up with every idea under the sun and implemented it so I am moving on as they say)I have no formal edu here as I graduated with a BS in Business Admin but had a passion since I took my first computer apart the day I got it on xmas in '97. Needless to say mom wasn't happy her $2k present was ripped apart.**
-
Replace both Ciscos and the Fortinet with two pfSense boxes. Done!
This network can be simplified, and by doing so, troubleshooting will be a LOT easier.
Run pfSense in a basic, default mode FIRST to get your routing working properly. Once you've done that, add stuff. If you cannot get the routing to work and you install add-ons, it makes troubleshooting that much more difficult.
-
@tim-mcmanus said in Subnet problem?:
Replace both Ciscos and the Fortinet with two pfSense boxes. Done!
This network can be simplified, and by doing so, troubleshooting will be a LOT easier.
Run pfSense in a basic, default mode FIRST to get your routing working properly. Once you've done that, add stuff. If you cannot get the routing to work and you install add-ons, it makes troubleshooting that much more difficult.
Sorry, there are not just two Cisco routers, but many many more than that, and this is a production environment so replacing them would mean bukku overtime during off hours which I can guarantee will not be approved. That sort of undertaking would have to be during summertime being I work for a school district.
-
Based on your drawing, my guess is at least one, if not multiple, things were happening in the beginning:
-
There was no return route on PFsense for the 10.35.60.0/24 network
-
The router at site 1 was not routing traffic properly to PFsense. You would need to configure PBR on the router at site 1, but considering traffic is flowing now, this appears to be done and working.
-
If there was a return route on PFsense, it may be pointed to the wrong IP.
-
There was no outbound NAT configured for traffic sourced from 10.35.60.0/24
PFsense will only NAT traffic from interfaces that it knows about, so when you had your LAN interface configured as 10.35.10.234/24, it was only NATing traffic sourced from 10.35.10.0/24 and nothing else. In order to get to the internet from your test host, you would've had to switch to Hybrid Outbound NAT mode and manually configure an Outbound NAT mapping for 10.35.60.0/24.
So, as soon as you gave your LAN interface a /8 mask, two things happened:
-
PFsense auto-generated an outbound NAT for traffic sourced from 10.0.0.0/8, which obviously includes IP's from the 10.35.60.0/24 network.
-
A route for 10.0.0.0/8 was added to the routing table, so now PFsense knows where to send return traffic
Your current setup will continue to work as is, but IMO there may be a cleaner approach. I would configure an unused, much smaller subnet as your transit network between PFsense and your Cisco router @ site 1 and then run OSPF as a routing protocol throughout the entire network. You could then get as granular as necessary with your NATing and firewall rules by creating aliases for allowing and/or denying internet access for certain subnets. Personally, I'd do all the same stuff even if you keep your Fortinet. Doing so will avoid possible routing issues down the road from things like site-to-site tunnels where the remote end has subnets in the 10.0.0.0/8 IP space.
@johnpoz said in Subnet problem?:
If devices do not point to pfsense as gateway then yeah more than likely your going to run into asymmetrical problems.
Not necessarily, It depends on the design. In this instance, his endpoints will be using the IP of each subinterface on the router or the SVI of an L3 switch stack as the default gateway.
@tim-mcmanus said in Subnet problem?:
Replace both Ciscos and the Fortinet with two pfSense boxes. Done!
This network can be simplified, and by doing so, troubleshooting will be a LOT easier.I agree with the K.I.S.S. principle, however, replacing the edge router (and others) at each site with PFsense would not simplify his network. All sites are connected via private circuits with internal addressing, so outside of special use cases, there is no need for a firewall at each site. Yes, PFsense can be configured as a router only, but IMO why add the complexity? His high-level drawing is fairly common among org's with multiple sites that are routed thru a main branch for internet. Not to mention, PFsense itself was not actually the issue, so IMO adding more PFsense boxes would not have helped him troubleshoot any more than he already had for this particular problem.
@Fratopolis Thank you for posting the map. Things became much clearer after seeing it.
-
-
@marvosa said in Subnet problem?:
Not necessarily, It depends on the design. In this instance, his endpoints will be using the IP of each subinterface on the router or the SVI of an L3 switch stack as the default gateway.
Yeah if there is a transit network connecting the L3 then no you wouldn't be asymmetrical.. But if he is going to try and leverage that 35.10 as a transit then yeah its asymmetrical.
Ya don't put hosts on a transit... Not sure how that network came to be.. But sorry while /8 might be a work around.. Its not the correct way to fix those problems.. He needs actual transit to connect pfsense to the downstream.
-
@johnpoz said in Subnet problem?:
Yeah if there is a transit network connecting the L3 then no you wouldn't be asymmetrical.. But if he is going to try and leverage that 35.10 as a transit then yeah its asymmetrical.
Ya don't put hosts on a transit... Not sure how that network came to be.. But sorry while /8 might be a work around.. Its not the correct way to fix those problems.. He needs actual transit to connect pfsense to the downstream.Agreed.
-
This post is deleted! -
First off, let me just say thank you all, for just diving head first without me having any clue what you all needed from me.
This network was setup before anyone that works in our dept was even there over 12-13 years ago. We have upgraded equip since then and went to 10Gb routers and switch stacks for furture enhancement but not sure if anything design wise has changed, I'd have to ask our net admin. We all wear many hats, I more than anyone only because I engage in everything I can get my dirty little hands on.
Ok so after I learned how to draw, learned what transit meant, then learned how to semi properly map things out, the consensus seems to be that the network is not as bad as originally thought by everyone "so I hope". "creating aliases for allowing and/or denying internet access for certain subnets." this works with our current setup and as far as diagnosing problems, we or I should say our net admin has never had problems doing so so far.
Updated map. (Yes I know that 10.31.0.0/19 wireless network is huge. Did it for a reason as it is our guest network. There are only ever about 150-300 people on it at once but my thought was give them an IP and they keep it for I think 2 years. Lets us easily track mischievousness)
I will not be making major changes until after the holiday break seeing as I am not at work to see how those changes affect anything. I do have a remote AP at my house with a VM added to our domain so I will continue working/testing other things in pfSense until i get back.