dnsleak issues when using local resolver
-
Configuration:
pf 2.4.4, Network-wide OpenVPN client configuration connecting to VPN, Provider.Issue: Anytime the client PC uses the local/pfsense/DNS Resolver, the dnsleak.com reports a leak. However, if the client only uses the VPN Provider DNS no dnsleak is seen.
The following is seen by dnsleak.com when the PC Client uses the pfSense Resolver:
LEAK:Your IP: 172.x.x.198 (VPN Provider IP to the OpenVPN Client) DNS IP: 136.x.x.144 (ISP DHCP/IP) to the WAN IF Hostname: 136.x.x.144 (ISP DHCP/IP) to the WAN IF Country: US City: SomeCityThe following is seen by dnsleak.com when the PC Client uses the VPN Provider DNS:
NO LEAK:Your IP: 172.x.x.198 DNS IP: 172.x.x.198 Hostname: 172.x.x.198 Country: US City: FarAwayCityFor the local subnet, I need to use the local pfsense resolver for name resolution; however with local resolver there's dnsleak. (I'm guessing because the local resolver uses dns forwarding).
Question: How to I setup local name resolution and still prevent dnsleaks? -
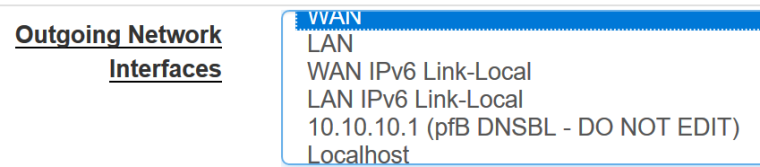
@rsaanon I exclude WAN from the Outgoing Network Interfaces in dns resolver and configure my vpn by host ip.
-
@gjaltemba thanks for your response. Could you expand on your response? What do you mean by "..configure my vpn by host ip"? In other words, which host ip are you referring to? Thanks.
-
@rsaanon Your vpn server host ip. For my openvpn client config, it is
VPN->OpenVPN->Clients->Server Host or Address
-
@gjaltemba Still unsure of what you mean. In your initial response, you stated that you "..exclude WAN interface from the outgoing dns queries and configure my vpn by host ip". If you exclude WAN interface from the outgoing DNS queries, then how will the local resolver handle queries that it does not know about? Also, what does "configure your vpn by host ip" do?
The issue at hand is about internal DNS resolution. I am running pfsense DNS Resolver/unbound to handle internal as well as external dns queries. I also have a VPN client configured that connects to my VPN provider. All dns queries initiated by the end-point/user go to the local resolver which if it can't resolve forwards the query to the VPN Provider's DNS servers. The problem, in my opinion, is stemming from the fact that with the local resolver enabled, the dnsleak test is able to see DNS queries coming from my ISP provided IP instead of the VPN Provider's VPN IP.
When I configure
-
@rsaanon said in dnsleak issues when using local resolver:
@gjaltemba If you exclude WAN interface from the outgoing DNS queries, then how will the local resolver handle queries that it does not know about? Also, what does "configure your vpn by host ip" do?
dns queries will use the vpn interface.
vpn server address cannot be configured by name when vpn is down. Makes sense?
-
@rsaanon said in dnsleak issues when using local resolver:
@gjaltemba thanks for your response. Could you expand on your response? What do you mean by "..configure my vpn by host ip"? In other words, which host ip are you referring to? Thanks.
Go to: Servicer / DNS Resolver.
Then look at the "Outgoing Network Interfaces" box, and make sure WAN in not selected.You also may need to go to: System / General
And add at least on DNS on the WAN Gateway, for instance Google DNS 8.8.8.8 and 8.8.4.4, otherwise you might not be able to connect to your OpenVPN service providers DNS, and therefore not be able to reach anythin on Internet using DNS-queries. -
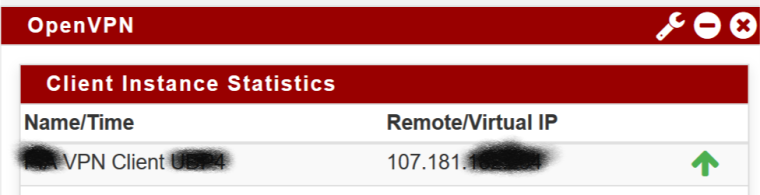
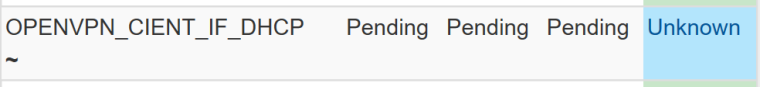
@gjaltemba Even though, I have a OpenVPN client that's connected to my VPN Provider,I do not have a OpenVPN Interface in my Outgoing Interfaces list:
OpenVPN Client Interface:
Interfaces defined:
-
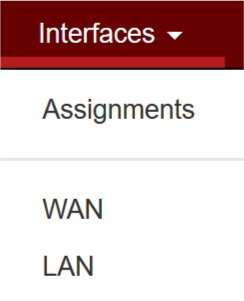
Well, you first need to assign a interface to your ovpnc1 network port.
You find it at: Interfaces / Interface Assignments
Then you also need to add a gateway for your OpenVPN interfafce, which you at: System / Routing / Gateways -
@no_jah I created the OpenVPN Interface with IPv4/6 Configuration Type to None.
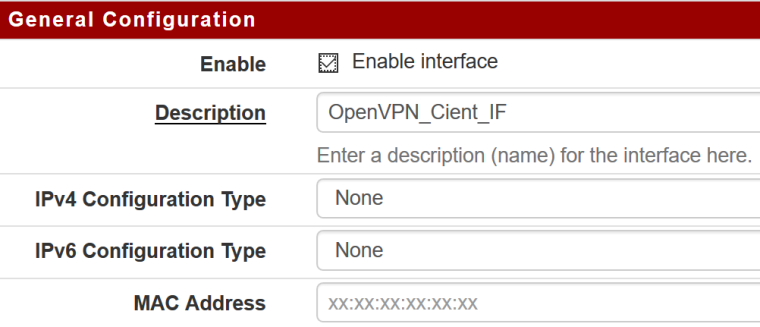
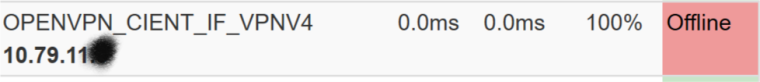
Looking at the Gateway Status:

In the above image, I see a private IANA address (10.11.10.5) that's assigned to this interface with Gateway Status: Offline. Why is this private IP showing up as Gateway when IP configuration type is set to None?
-
What version of pfSense do you have?
I can't even select connection type on my OpenVPN interfaces running 2.4.4_p1 -
@no_jah 2.4.3-RELEASE
Note, the last "General Configuration" image I posted is from the Web GUI->Interfaces->OpenVPN_Client_IF. The configuration type (ie: dhcp, ppp, static, etc.) have always been there. -
Ok, I think you should use DHCP as IPv4 Configuration type for your OpenVPN interface.
-
@no_jah OpenVPN Interface set to DHCP v4, but then the Gateway status shows:
However, if I disable ConfigurationType, the Gateway Status changes to:
-
Did you get it to work?