SG-1100 Crypto Hardware
-
I recently purchased one of these goodies and I coming from "big iron" Intel box down to this baby so its taking a little getting used to on the relatively less horsepower and memory. So far so good just trying to get the optimal rule sets loaded for Suricata sorted out with so much less memory.
Questions:
-
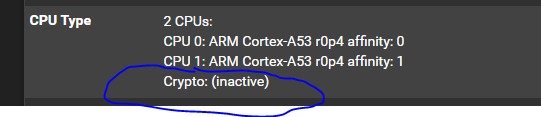
The Dashboard indicates no cryptographic hardware even after toggling the Intel or the BSD options under (Advanced) I think. Does this device in fact have the ability to do hardware crypto?
-
Is there the ability to do any hardware offloading by the NIC's? I haven't change anything in the configuration yet...
Thanks
-
-
The Dashboard indicates no cryptographic hardware even after toggling the Intel or the BSD options under (Advanced) I think. Does this device in fact have the ability to do hardware crypto?
We are still working on the hardware crypto driver. If the concern is "will this be supported in the future?" Yes we will support this for it's entire product life cycle.
-
I tried to find documentation how to activate this in the correct way. But i was not able too. Is there support for this now? In that case is there some documentation what setting should be active?
-
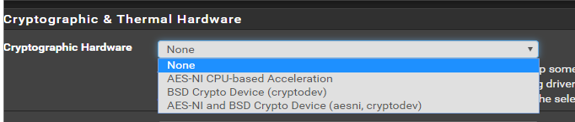
Is it this setting i have to change? What should i choose?
-
We are still aggressively working on the driver for the SG-1100; there is no setting you need to change to enable it.
-
Yes, there is no way to enable it right now but you will want 'BSD crypto device' selected there to use the driver when it is included.
Steve
-
@chrismacmahon said in SG-1100 Crypto Hardware:
We are still aggressively working on the driver for the SG-1100; there is no setting you need to change to enable it.
AH! Ok. Good. That was on my "to-do list".. One less point to worry about for me then ;) .. No rush for my sake! :)
-
@chrismacmahon So, what is the openvpn performance of this machine with no hardware crypto acceleration? (Which by the way is something that should have been in big bold red letters in the advertisements and specifications. I have an expectation that all new pfsense hardware will have WORKING hardware crypto acceleration. I do not like my first hint that it might not work yet being me getting the unit, turning it on and seeing "Crypto: (Inactive)". I do not trust "The check is in the mail" with no timeframes mentioned. If I built a pfsense of course unsupported features are not your problem, but when I buy direct from Netgate I have an expectation of a product with primary features that work. Crypto acceleration is a primary feature. If I didn't need/want it I could use a computer that is 2 decades old.
-
@kejianshi i have done tests with my 100Mbit line and VPN works great with top speed. I have 2 tunnels running and i think i have not seen any cpu usage above 50%.. I think i read somewhere that it can do 900Mbit but dont quote me on that.
-
@Taz79 I hope you are right. I don't need to max out gigabit ethernet or anything. Just run a few tunnels with relatively low bandwidth requirement. 10 - 30 MB/s. I just don't like being surprised (-;
Thanks for your reply. Its encouraging. I just got this thing hooked up from about 8700 miles away and I'm really hoping its as stable as the box its replacing. I do like the low power, small form factor etc etc. I will configure the VPN and let you know how it performs long-haul. -
I have seen ~150Mbps OpenVPN in local iperf3 testing here. Latency and packet size variation etc will impact that though.
Steve
-
@kejianshi the 900Mbit i saw must have been the performance of the routing. Not the VPN speed when i think about it. But i have tested with 117Mbit/s that is my max speed of my connection and it works great. My box were up for 65 days before i needed to shut it down to move it :)
-
@stephenw10 Thanks old timer. Still at it huh? This tiny box is replacing a AMD X2 3800... I got a LOT of miles out of that box!
-
Yup, still here.

-
Any ballpark estimates on the gains that will be seen by even supporting the hardware cryptography?
I'm assuming in daily operation it won't matter so much but only on ipsec and openvpn.I bought a few of these, I might put one in place of my current home FW which is a 3rd gen Intel Core i5 on an Intel DQ77MK mobo. I have 500mbps internet and three ipsec vpn tunnels, and 2 vlans.
-
We are doing the work on our own on this, we do expect gains but to put out firm numbers would be a disservice to all involved.
-
@chrismacmahon
Will there be any support for the crypto hardware on the SG-1000 (now EoS)? -
That's a good question. Let me get back to you on that.
-
@bigsy We don't think the work will be impacting the SG-1000.
-
@chrismacmahon Thanks for all your hard work! What would be the best way to keep tabs on the development of this driver?