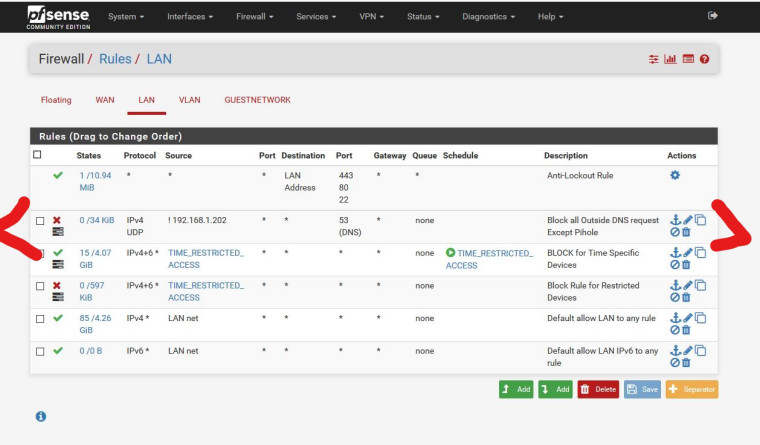
Easy Question: Block all outside DNS except Pihole
-
I believe this rule should do everything I want, but I wanted to have someone else look at it. I'm trying to block all outside DNS requests on the LAN and only allow my Pihole (192.168.1.202 invert match set) to reach out to an upstream server.
-
PASS TCP/UDP source 192.168.1.202 dest port 53
REJECT TCP/UDP source any dest port 53But anyone can try to spoof IP address 192.168.1.202 in that configuration.
It would be better to have the pihole on another subnet/interface.
-
Thanks Derelict, i understand the your rule suggestion. Does the "inverted match" cover that or is there an issue using it like that?
"Another subnet/interface" is beyond my understanding. I'm no expert, just an end user. I do appreciate the help.
-
Personally I never use
!rules. I despise them. Other people - some of them pretty smart - disagree.You are doing
block ! 192.168.1.202which is better than using apass ! hostsrule to block traffic to hosts.But there is no reason for it. If you want to pass it, pass it. If you want to block it, block it.
It makes the rule set much easier to understand, at least for me.
Doing this will likely be "good enough" even if a client could spoof 192.168.1.202.
It'd probably break everything if someone tried that though since there would be two 192.168.1.202 hosts on your network so a lot of things would probably break unless they were pretty good.
-
While your inverted rule should work, Derelict is not a fan of such rules ;) Which is why he shows explicit way of doing it..
If your going to use an inverted rule you need to MAKE sure its working.. There things that can mess with doing such rules. pfsblocker adding its vip can mess with it for starters. The better way to do it is to actually block/reject vs doing an inverted allow rule.
Also you need to block both udp and tcp on 53. DNS can use either.
edit; Hist point of moving the pihole to another network/interface would prevent users of changing their IP to the piholes IP and being let out for dns. If you moved the pihole to a network that no users are on, then they can not change their IP to to machine the piholes IP and use that rule.
-
Thanks for the input guys. I like to keep things simple. I think I'm going to change the rules to reflect what Derelict was suggesting, separate rules for pass and block.
-
His method is cleaner easier to read, and better in the long run. Inverted rules can be useful, and I do use them, they are not for everyone ;)
