False Positive?
-
Hello,
I'm new to suricata. I've been watching the logs for a while now but I'm having difficulties trying to figure out what entries are false positives.
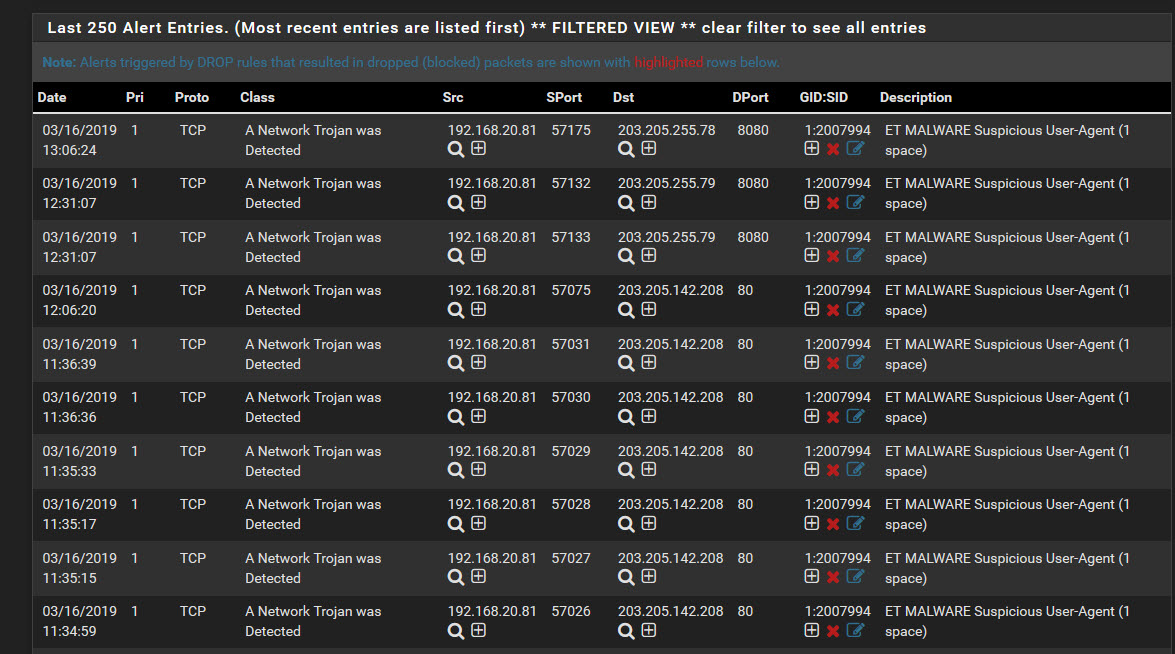
Below is a screen shot of my wifi interface in inline mode from an apple iphone connecting to IP's in China. How does on determine if the sample log "ET MALWARE Suspicious User-Agent (1 space)" below is a false positive. Do i set the log to drop or reject. Any help would be much appreciated.
Thanks,
-
Google searches are your best friend when learning how to administer an IDS/IPS product such as Suricata or Snort. To validate if this is truly a false positive in your environment, you will need to capture the packets in Wireshark or an equivalent product and analyze them.
I did a quick query on Google using the text from this rule and found these entries at the top my search results:
https://lists.emergingthreats.net/pipermail/emerging-sigs/2014-March/023900.html
https://community.ubnt.com/t5/UniFi-Routing-Switching/IPS-Alert-Network-Trojan/td-p/2278732
https://lists.emergingthreats.net/pipermail/emerging-sigs/2012-January/016930.htmlSo, looking through the material in the links posted above, I would hazard a guess you are seeing false positives generated by an app installed on the phone. Examining the packet captures will be required in order to validate whether the traffic is benign or not.
-
^ exactly... Running a IPS/IDS is not something you just turn on.. Welcome to a HUGE learning curve!!!
While others can take guesses to false or not.. To be honest your the only one that is going to know your system(s) and what apps your using, and require to do what your doing.. So your going to have to make the call if false or bad, normal, etc.
-
Thank you both for your input. Yes this will be a huge learning curve for me. I will keep on analyzing.