OpenVPN passes ssh traffic but not HTML or other traffic.
-
I have an openvpn server running and I have used the OPENVPN client to connect to the network successfully for the last couple of years. The public IP address of the network changed recently. I changed the server configuration to reflect the new IP address, exported the config and found that while the connection was established, I had no access to anything on the LAN side. I then removed the server, and recreated everything from scratch. I have no problems connecting to the new tunnel, but I have no access to anything on the LAN side via the browser. I can ssh into the pfsense box or any of the other servers, but I can not access the gui interface for the PFsense box or any other server (including ones that use an alternative port). I have the default openvpn rule that passes everything. I have a dozen other pfsense boxes that I access successfully via OpenVPN and they have the same configuration. I have been working on this for a couple of days with no success - I am sure it is something simple that I am overlooking. Any ideas on where I might look?
-
I have worked on this for a couple of days with no solution. The OVPN server is setup exactly the same as on the other pfsense boxes. This box has an ipsec tunnel set up between it and some of the other pfsense firewallls. If we call this PF1 and one of the others, PF2, I can connect to PF2 via OVPN, remote into a client and then access the webgui of PF1 via the ipsec tunnel with no problem. If I connect via OVPN directly to PF1 I can not access the web gui of PF1 - I can, however, ssh directly to the console of PF1. The connection to the webgui seems to be working in one direction only. When I try to connect, the browser responds with "waiting for...." and takes several minutes to time out. I turned on logging for the openvpn interface and the logs show the packets passing correctly. I have no idea what is causing the problem - and of course it only happens when I am 2000 miles from the office.
-
Since you can ssh but not web access its definitely not a routing problem.
So it has to be filtering.
Still, your description is not very clear.
Post a diagram, explaining what works and what doesn't and firewall rules of relevant interfaces. -
So here is a drawing of the network.
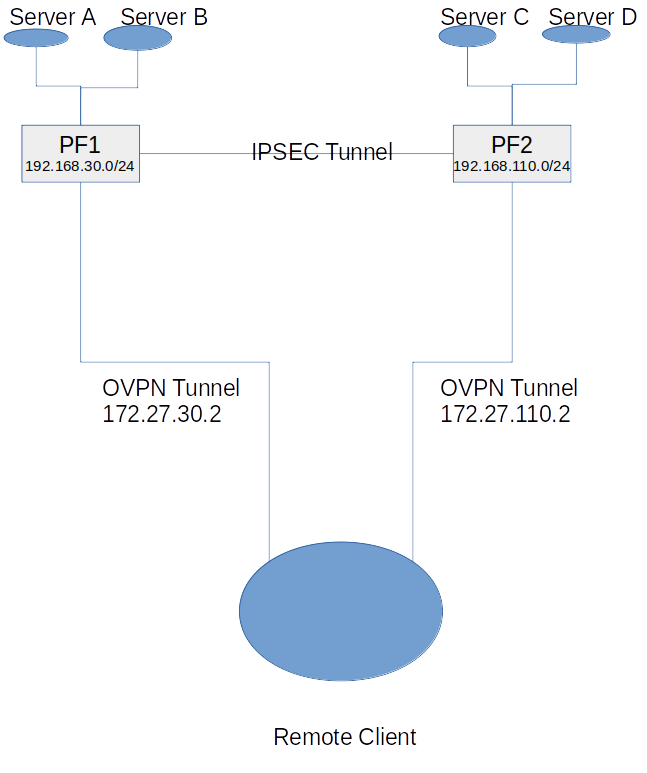
using ssh the client can connect to PF1, Server A, Server B, as well as PF2, Server C and Server D
using html the client can not connect to PF1 or Server A and B, but can connect to Server C and D as well as PF2.
the client can connect via OVPN to a client on the network behind PF2, with RDP and then use that client to connect to PF1, Server A and Server B with HTML through the IPSEC tunnel.Both pfsense boxes have the default (everything to everything) OpenVPN rules.