DLNA, IGMP Proxy, VLANs, Subnets... Oh, dear...
-
Hi Folks,
This is the case of:
- IGMP Proxy is really broken in 2.4.4_p2 (have not tried it on p3, yet)
- What I want to do cannot be done
- Or, I am really missing the boat here

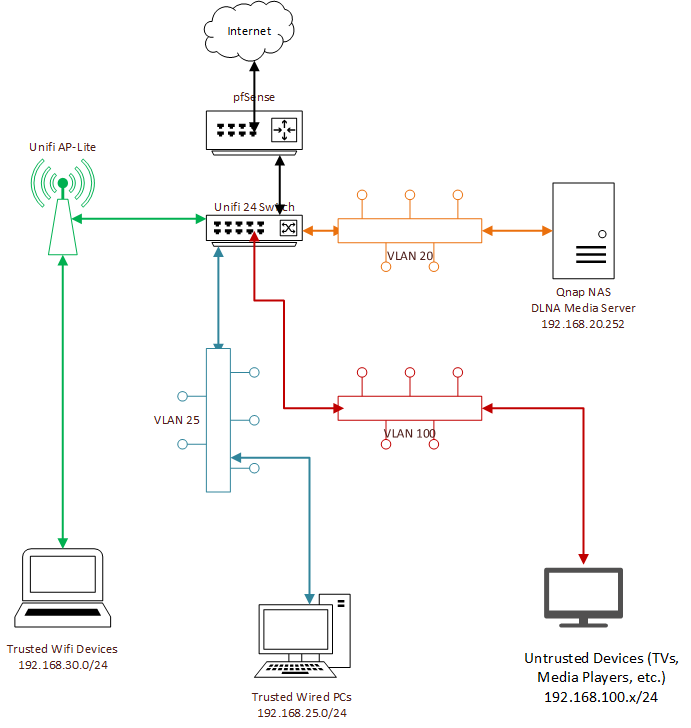
Here is the setup:
- pfSense 2.4.4_p2
- Unifi 24 managed switch with VLANs and IGMP snooping enabled on the appropriate ports
- All internal VLANs go through the pfSense firewall (for what it is worth, DMZ and Internet are separate physical ports)
- VLAN 30 (green) for the 192.168.30.0/24 subnet for trusted WiFi clients
- VLAN 25 (blue) for the 192.168.25.0/24 subnet for trusted wired clients
- VLAN 20 (orange) for the 192.168.20.0/24 subnet for servers
- VLAN 100 (red) for untrusted wired clients (e.g., TVs, Playstation, etc.)
I have one of my NASes (Qnap) running as a media server using DLNA (192.168.20.252).
I have set up the IGMP proxy with the Qnap being the upstream source (specifically, 192.168.20.252/32).
The IGMP proxy has the downstream as 192.168.25.0/24 and 192.168.20.0/24 and 192.168.100.0/24.I have tried using the firewall rules to allow IGMP explicitly allow 192.168.25.0/24, 192.168.30.0/24 and 192.168.100.0/24 to access the NAS (192.168.20.252) including the "Allow packets with IP Options" option. Note that 192.168.25.0/24 and 192.168.30.0/24 have full TCP, UPD and ICMP access to 192.168.20.0/24 (Yes, I know - I will be tightening that up...).
I still cannot get any DLNA clients (e.g., the LG TV on the untrusted network, VLC media player on a Linux Mint wired and wireless laptop, or MediaHouse on an Android tablet) to see the Qnap DLNA media server.
What am I missing here? Diagram is below. Thanks!
-
@nfld_republic Did you try disabling IGMP snooping on the switch and see if anything changes?
How many ethernet interfaces does the Qnap have?
-
@sotirone
The Qnap only has 1 interface. I will try disabling IGMP snooping on the switch and see if that works. (Having IGMP snooping enabled on the switch was noted as being needed in other posts - but what do I have to lose? )
) -
@nfld_republic Any luck?
What Media Server software is the Qnap running?
If the Qnap had more interfaces I would advise you to configure each interface for another VLAN so you didn't have to L3 route through the firewall.
Have a look at this article: http://troglobit.com/howto/multicast/
Is there any chance TTL has something to do with your problem?Edit:
Take a look at this as well: https://community.ubnt.com/t5/EdgeSwitch/Multicast-Routing-across-VLANS-subnets-not-working/m-p/2195488#M15424Scrap that, that is for the EdgeSwitches
-
I'd also have multiple SSIDs on the AP rather than just the one and why distinguish between trusted WiFi & trusted wired, rather than just a trusted.
I'd create 3, Trusted, IOT & Guest.
-
@sotirone Thanks - I'll take a deeper look at that article. I think that I have read something similar.
-
@NogBadTheBad No real reason other than "making it work" (and a son on wired who sometimes needs to have his access restricted
 ). That said, the same issue exists on both trusted wired and trusted wireless - it doesn't work on either.
). That said, the same issue exists on both trusted wired and trusted wireless - it doesn't work on either. -
@sotirone I forgot to add that the DNLA media server is the default Qnap DNLA app (https://www.qnap.com/hu-hu/how-to/tutorial/article/how-to-enjoy-multimedia-content-stored-on-the-qnap-nas-via-dlnaupnp). I tried Plex as well but that did not work either.
-
For what its worth, I had all sorts of issues with my Synology trying to the same thing. over multiple VLANS, not ideal I know.
In the end dual homing the thing and tightening down the access via firewall rules on the additional Synology interface.
-
@NogBadTheBad I had that thought as well but without multiple NICs that isn't possible... I might end up moving the Qnap to a trusted subnet and merging the trusted wired and wireless subnets tp the same one as the Qnap.
-
Can you do vlans on the Qnap interface ?
-
The other thoughts is the IGMP Proxy is still borked...
-
@NogBadTheBad Unfortunately no. I have the TS-219P II which has a Marvell processor; it seems only the x64 NASes can do VLANs. (I thought about that too
 )
) -
Well, I tried turning IGMP snooping off the source and destination VLANs but there was no change. I did verify with a host on the 192.168.20.0/24 network that the DNLA servers (I installed one on my Synology NAS as well for testing) are visible and I could play content.
I also updated IGMP Proxy manually to igmpproxy-0.2.1_1,1.txz.
I also tried Twonky but that did not work either.
On thing I have noticed with pfTop is:
pfTop: Up State 1-2/2 (501), View: long, Order: bytes PR DIR SRC DEST GW STATE AGE EXP PKTS BYTES AVG RU igmp Out 192.168.30.254:0 224.0.0.1:0 SINGLE:NO_TRAFFIC 90653 26 14685 469920 5 * igmp Out 192.168.25.254:0 224.0.0.1:0 SINGLE:NO_TRAFFIC 90653 26 14685 469920 5 *I do not have any rules for 224.0.0.x (multicast). Is this necessary?
-
Post a copy of your rules.
Sure you don't have something like:-
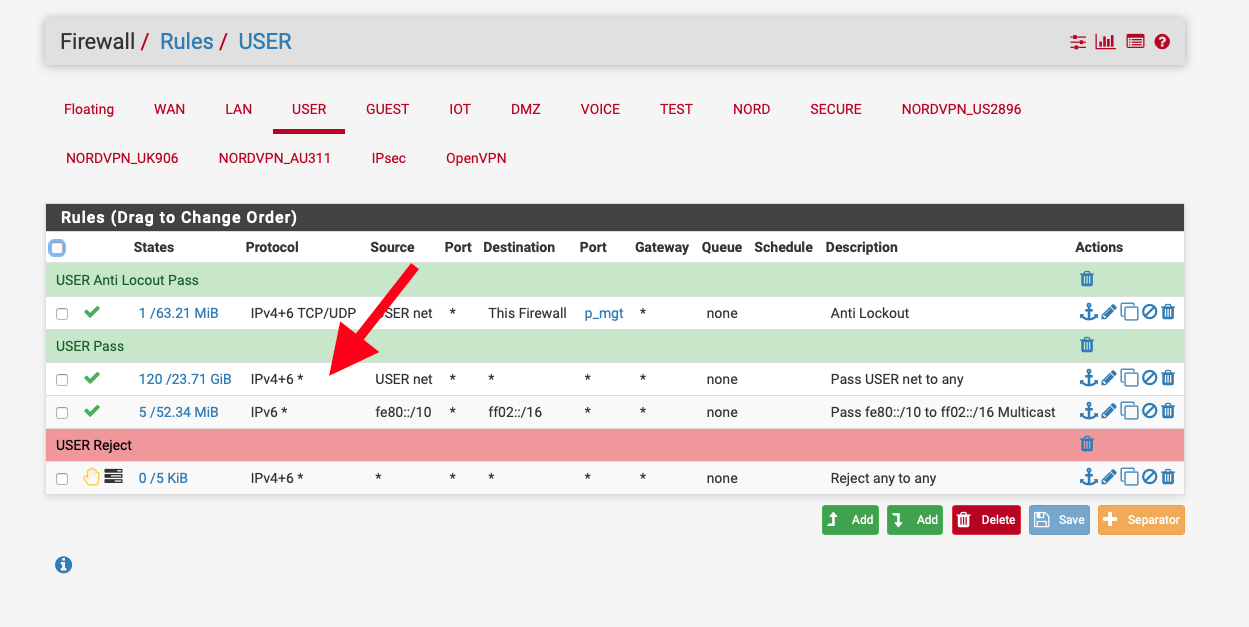
My 3rd rule is for IPv6 multicast as the source is fe80:/10.
-
@NogBadTheBad Except for the IPv6 rule I have full access from the to user networks to any my rule is the same.
Rules (Drag to Change Order) States Protocol Source Port Destination Port Gateway Queue Schedule Description Actions 2 /49.19 MiB IPv4 * WIREDTRUSTED25 net * * * * none 0 /0 BI note that you don't have IGMP as a rule - it is not needed?
-
Debugging igmp proxy issues is usually easiest if you try starting it from the command line in verbose mode.
That way you can see what connections are happening and if there are erros when it start.
igmpproxy -d -vv /var/etc/igmpproxy.confObviously stop the service in the GUI first.
Steve
-
@stephenw10 said in DLNA, IGMP Proxy, VLANs, Subnets... Oh, dear...:
igmpproxy -d -vv /var/etc/igmpproxy.conf
Here's some output... Anyone have any ideas?
igmpproxy -d -vv /var/etc/igmpproxy.conf Searching for config file at '/var/etc/igmpproxy.conf' Config: Quick leave mode enabled. Config: Got a phyint token. Config: IF: Config for interface igb3.20. Config: IF: Got upstream token. Config: IF: Got ratelimit token '0'. Config: IF: Got threshold token '1'. Config: IF: Got altnet token 192.168.20.0/24. Config: IF: Altnet: Parsed altnet to 192.168.20/24. Config: IF: Got altnet token 224.0.0.0/4. Config: IF: Altnet: Parsed altnet to 224/4. IF name : igb3.20 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 1 Allowednet ptr : e25000 Config: Got a phyint token. Config: IF: Config for interface igb3.30. Config: IF: Got downstream token. Config: IF: Got ratelimit token '0'. Config: IF: Got threshold token '1'. Config: IF: Got altnet token 192.168.30.0/24. Config: IF: Altnet: Parsed altnet to 192.168.30/24. IF name : igb3.30 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 2 Allowednet ptr : e25020 Config: Got a phyint token. Config: IF: Config for interface igb3.25. Config: IF: Got downstream token. Config: IF: Got ratelimit token '0'. Config: IF: Got threshold token '1'. Config: IF: Got altnet token 192.168.25.0/24. Config: IF: Altnet: Parsed altnet to 192.168.25/24. IF name : igb3.25 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 2 Allowednet ptr : e25030 Config: Got a phyint token. Config: IF: Config for interface igb1. Config: IF: Got disabled token. IF name : igb1 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface igb3.201. Config: IF: Got disabled token. IF name : igb3.201 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface igb5. Config: IF: Got disabled token. IF name : igb5 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface igb3.100. Config: IF: Got disabled token. IF name : igb3.100 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface igb3. Config: IF: Got disabled token. IF name : igb3 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 Config: Got a phyint token. Config: IF: Config for interface igb2. Config: IF: Got disabled token. IF name : igb2 Next ptr : 0 Ratelimit : 0 Threshold : 1 State : 0 Allowednet ptr : 0 buildIfVc: Interface igb1 Addr: 156.57.107.225, Flags: 0xffff8943, Network: 156.57.104/22 buildIfVc: Interface igb2 Addr: 10.100.101.254, Flags: 0xffff8843, Network: 10.100.101/24 buildIfVc: Interface igb3 Addr: 10.100.200.254, Flags: 0xffff8943, Network: 10.100.200/24 buildIfVc: Interface igb5 Addr: 192.168.10.254, Flags: 0xffff8943, Network: 192.168.10/24 buildIfVc: Interface lo0 Addr: 127.0.0.1, Flags: 0xffff8049, Network: 127/8 buildIfVc: Interface igb3.30 Addr: 192.168.30.254, Flags: 0xffff8943, Network: 192.168.30/24 buildIfVc: Interface igb3.100 Addr: 192.168.100.254, Flags: 0xffff8943, Network: 192.168.100/24 buildIfVc: Interface igb3.25 Addr: 192.168.25.254, Flags: 0xffff8943, Network: 192.168.25/24 buildIfVc: Interface igb3.20 Addr: 192.168.20.254, Flags: 0xffff8943, Network: 192.168.20/24 buildIfVc: Interface igb3.201 Addr: 10.100.201.254, Flags: 0xffff8943, Network: 10.100.201/24 buildIfVc: Interface ovpns1 Addr: 192.168.99.1, Flags: 0xffff8051, Network: 192.168.99/24 buildIfVc: Interface ovpns2 Addr: 172.16.1.1, Flags: 0xffff8051, Network: 172.16.1/24 Found config for igb1 Found config for igb2 Found config for igb3 Found config for igb5 Found config for igb3.30 Found config for igb3.100 Found config for igb3.25 Found config for igb3.20 Found config for igb3.201 adding VIF, Ix 0 Fl 0x0 IP 0xfe1ea8c0 igb3.30, Threshold: 1, Ratelimit: 0 Network for [igb3.30] : 192.168.30/24 Network for [igb3.30] : 192.168.30/24 adding VIF, Ix 1 Fl 0x0 IP 0xfe19a8c0 igb3.25, Threshold: 1, Ratelimit: 0 Network for [igb3.25] : 192.168.25/24 Network for [igb3.25] : 192.168.25/24 Found upstrem IF #0, will assing as upstream Vif 32 adding VIF, Ix 2 Fl 0x0 IP 0xfe14a8c0 igb3.20, Threshold: 1, Ratelimit: 0 Network for [igb3.20] : 192.168.20/24 Network for [igb3.20] : 192.168.20/24 Network for [igb3.20] : 224/4 Got 262144 byte buffer size in 0 iterations Joining all-routers group 224.0.0.2 on vif 192.168.30.254 joinMcGroup: 224.0.0.2 on igb3.30 Joining all igmpv3 multicast routers group 224.0.0.22 on vif 192.168.30.254 joinMcGroup: 224.0.0.22 on igb3.30 Joining all-routers group 224.0.0.2 on vif 192.168.25.254 joinMcGroup: 224.0.0.2 on igb3.25 Joining all igmpv3 multicast routers group 224.0.0.22 on vif 192.168.25.254 joinMcGroup: 224.0.0.22 on igb3.25 SENT Membership query from 192.168.30.254 to 224.0.0.1 Sent membership query from 192.168.30.254 to 224.0.0.1. Delay: 10 SENT Membership query from 192.168.25.254 to 224.0.0.1 Sent membership query from 192.168.25.254 to 224.0.0.1. Delay: 10 Created timeout 1 (#0) - delay 10 secs (Id:1, Time:10) Created timeout 2 (#1) - delay 21 secs (Id:1, Time:10) (Id:2, Time:21) RECV Membership query from 192.168.30.254 to 224.0.0.1 RECV Membership query from 192.168.25.254 to 224.0.0.1 RECV V2 member report from 192.168.25.240 to 224.0.1.60 Should insert group 224.0.1.60 (from: 192.168.25.240) to route table. Vif Ix : 1 No existing route for 224.0.1.60. Create new. No routes in table. Insert at beginning. Inserted route table entry for 224.0.1.60 on VIF #1 Joining group 224.0.1.60 upstream on IF address 192.168.20.254 joinMcGroup: 224.0.1.60 on igb3.20 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 ----------------------------------------------------- RECV V2 member report from 192.168.25.254 to 224.0.0.2 The IGMP message was from myself. Ignoring. The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.25.240 to 224.0.1.1 Should insert group 224.0.1.1 (from: 192.168.25.240) to route table. Vif Ix : 1 No existing route for 224.0.1.1. Create new. Found existing routes. Find insert location. Inserting at beginning, before route 224.0.1.60 Inserted route table entry for 224.0.1.1 on VIF #1 Joining group 224.0.1.1 upstream on IF address 192.168.20.254 joinMcGroup: 224.0.1.1 on igb3.20 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 ----------------------------------------------------- The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.25.254 to 224.0.0.22 The IGMP message was from myself. Ignoring. The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.30.4 to 239.2.0.252 Should insert group 239.2.0.252 (from: 192.168.30.4) to route table. Vif Ix : 0 No existing route for 239.2.0.252. Create new. Found existing routes. Find insert location. Inserting after route 224.0.1.60 Inserted route table entry for 239.2.0.252 on VIF #0 Joining group 239.2.0.252 upstream on IF address 192.168.20.254 joinMcGroup: 239.2.0.252 on igb3.20 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 #2: Dst: 239.2.0.252, Age:2, St: I, OutVifs: 0x00000001 ----------------------------------------------------- RECV V2 member report from 192.168.30.254 to 224.0.0.22 The IGMP message was from myself. Ignoring. RECV V2 member report from 192.168.30.254 to 224.0.0.2 The IGMP message was from myself. Ignoring. RECV V2 member report from 192.168.25.205 to 239.0.0.250 Should insert group 239.0.0.250 (from: 192.168.25.205) to route table. Vif Ix : 1 No existing route for 239.0.0.250. Create new. Found existing routes. Find insert location. Inserting after route 224.0.1.60 Inserted route table entry for 239.0.0.250 on VIF #1 Joining group 239.0.0.250 upstream on IF address 192.168.20.254 joinMcGroup: 239.0.0.250 on igb3.20 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:2, St: I, OutVifs: 0x00000002 #3: Dst: 239.2.0.252, Age:2, St: I, OutVifs: 0x00000001 ----------------------------------------------------- About to call timeout 1 (#0) Aging routes in table. Current routing table (Age active routes): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:1, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:1, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:1, St: I, OutVifs: 0x00000002 #3: Dst: 239.2.0.252, Age:1, St: I, OutVifs: 0x00000001 ----------------------------------------------------- About to call timeout 2 (#0) SENT Membership query from 192.168.30.254 to 224.0.0.1 Sent membership query from 192.168.30.254 to 224.0.0.1. Delay: 10 SENT Membership query from 192.168.25.254 to 224.0.0.1 Sent membership query from 192.168.25.254 to 224.0.0.1. Delay: 10 Created timeout 3 (#0) - delay 10 secs (Id:3, Time:10) Created timeout 4 (#1) - delay 21 secs (Id:3, Time:10) (Id:4, Time:21) RECV Membership query from 192.168.30.254 to 224.0.0.1 RECV Membership query from 192.168.25.254 to 224.0.0.1 The IGMP message was local multicast. Ignoring. The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.25.240 to 224.0.1.1 Should insert group 224.0.1.1 (from: 192.168.25.240) to route table. Vif Ix : 1 Updated route entry for 224.0.1.1 on VIF #1 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:1, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:1, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:1, St: I, OutVifs: 0x00000002 #3: Dst: 239.2.0.252, Age:1, St: I, OutVifs: 0x00000001 ----------------------------------------------------- RECV V2 member report from 192.168.30.254 to 224.0.0.2 The IGMP message was from myself. Ignoring. The IGMP message was local multicast. Ignoring. The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.25.205 to 239.0.0.250 Should insert group 239.0.0.250 (from: 192.168.25.205) to route table. Vif Ix : 1 Updated route entry for 239.0.0.250 on VIF #1 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:1, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:1, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:1, St: I, OutVifs: 0x00000002 #3: Dst: 239.2.0.252, Age:1, St: I, OutVifs: 0x00000001 ----------------------------------------------------- The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.25.240 to 224.0.1.60 Should insert group 224.0.1.60 (from: 192.168.25.240) to route table. Vif Ix : 1 Updated route entry for 224.0.1.60 on VIF #1 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:1, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:1, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:1, St: I, OutVifs: 0x00000002 #3: Dst: 239.2.0.252, Age:1, St: I, OutVifs: 0x00000001 ----------------------------------------------------- The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.25.254 to 224.0.0.22 The IGMP message was from myself. Ignoring. RECV V2 member report from 192.168.25.254 to 224.0.0.2 The IGMP message was from myself. Ignoring. The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.30.254 to 224.0.0.22 The IGMP message was from myself. Ignoring. About to call timeout 3 (#0) Aging routes in table. Removing group 239.2.0.252. Died of old age. Removed route entry for 239.2.0.252 from table. Leaving group 239.2.0.252 upstream on IF address 192.168.20.254 leaveMcGroup: 239.2.0.252 on igb3.20 Current routing table (Remove route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:2, St: I, OutVifs: 0x00000002 ----------------------------------------------------- Current routing table (Age active routes): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:2, St: I, OutVifs: 0x00000002 ----------------------------------------------------- About to call timeout 4 (#0) SENT Membership query from 192.168.30.254 to 224.0.0.1 Sent membership query from 192.168.30.254 to 224.0.0.1. Delay: 10 SENT Membership query from 192.168.25.254 to 224.0.0.1 Sent membership query from 192.168.25.254 to 224.0.0.1. Delay: 10 Created timeout 5 (#0) - delay 10 secs (Id:5, Time:10) Created timeout 6 (#1) - delay 115 secs (Id:5, Time:10) (Id:6, Time:115) RECV Membership query from 192.168.30.254 to 224.0.0.1 RECV Membership query from 192.168.25.254 to 224.0.0.1 RECV V2 member report from 192.168.25.240 to 224.0.1.60 Should insert group 224.0.1.60 (from: 192.168.25.240) to route table. Vif Ix : 1 Updated route entry for 224.0.1.60 on VIF #1 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:2, St: I, OutVifs: 0x00000002 ----------------------------------------------------- RECV V2 member report from 192.168.30.254 to 224.0.0.22 The IGMP message was from myself. Ignoring. The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.25.254 to 224.0.0.2 The IGMP message was from myself. Ignoring. The IGMP message was local multicast. Ignoring. The IGMP message was local multicast. Ignoring. The IGMP message was local multicast. Ignoring. RECV V2 member report from 192.168.30.254 to 224.0.0.2 The IGMP message was from myself. Ignoring. RECV V2 member report from 192.168.25.254 to 224.0.0.22 The IGMP message was from myself. Ignoring. RECV V2 member report from 192.168.25.205 to 239.0.0.250 Should insert group 239.0.0.250 (from: 192.168.25.205) to route table. Vif Ix : 1 Updated route entry for 239.0.0.250 on VIF #1 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:2, St: I, OutVifs: 0x00000002 ----------------------------------------------------- RECV V2 member report from 192.168.25.240 to 224.0.1.1 Should insert group 224.0.1.1 (from: 192.168.25.240) to route table. Vif Ix : 1 Updated route entry for 224.0.1.1 on VIF #1 Current routing table (Insert Route): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:2, St: I, OutVifs: 0x00000002 ----------------------------------------------------- About to call timeout 5 (#0) Aging routes in table. Current routing table (Age active routes): ----------------------------------------------------- #0: Dst: 224.0.1.1, Age:2, St: I, OutVifs: 0x00000002 #1: Dst: 224.0.1.60, Age:2, St: I, OutVifs: 0x00000002 #2: Dst: 239.0.0.250, Age:2, St: I, OutVifs: 0x00000002 ----------------------------------------------------- ^Cselect() failure; Errno(4): Interrupted system call Got a interrupt signal. Exiting. clean handler called Removing route entry for 224.0.1.1 Leaving group 224.0.1.1 upstream on IF address 192.168.20.254 leaveMcGroup: 224.0.1.1 on igb3.20 Removing route entry for 224.0.1.60 Leaving group 224.0.1.60 upstream on IF address 192.168.20.254 leaveMcGroup: 224.0.1.60 on igb3.20 Removing route entry for 239.0.0.250 Leaving group 239.0.0.250 upstream on IF address 192.168.20.254 leaveMcGroup: 239.0.0.250 on igb3.20 All routes removed. Routing table is empty. Shutdown complete.... -
Well it looks to be working at least some-what as expected.
Do those IPs on the downstream interfaces look correct? 25.240, 30.4, 25.205?
I assume pfSense is using .254 on each interface?
What I don't see there is any traffic from 20.252 but this is not something I look into very often.
Do you see any blocked traffic on vlan 20?
Steve
-
@stephenw10 Thanks for the response.
- Downstream interfaces are correct.
- Nodes are corrects (trusted wired (LG TV) and trusted wireless (Roku) clients - although another one is an HP OfficeJet Pro
 )
) - Not actually seeing MediaHouse (Android, TrustedWiFi) or VLC (Ubuntu, VLC Player) clients, though
- Interface gateways are correct
- Not seeing any blocked traffic on VLAN 20 for the media server (20.252) (all accepted)
May 25 21:20:44 SERVERS20 192.168.20.252:41914 239.255.255.250:1900 UDP May 25 21:20:44 SERVERS20 192.168.20.252:1900 239.255.255.250:1900 UDP May 25 21:20:22 SERVERS20 192.168.20.252:137 192.168.20.255:137 UDP May 25 21:19:44 SERVERS20 192.168.20.252:41914 239.255.255.250:1900 UDP