Duplicate IPv6 addresses
-
Following the update to Windows 10 1903, I have the following issue:
- When the PC NIC acquires it's IP, for a couple of seconds there is 1 IPv6 permanent address and 1 IPv6 temporary address, then those addresses get doubled.
Here's an example:
- First seconds after acquiring IPs:

- 5 Seconds later:

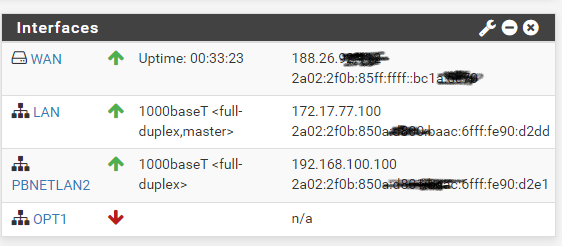
My PFSense interfaces:

And Switch (Mikrotik SWOS WLAN Assignments to ports)

Any help/hint would be greatly appreciated, since I'm really lost here and I would really love to have IPv6 back on my main PC.
Thanks.
Andy. -
@pbnet said in Duplicate IPv6 addresses:
Any help/hint would be greatly appreciated, since I'm really lost here and I would really love to have IPv6 back on my main PC.
Does it affect any other device?
-
@JKnott : Yes, any PC wired to the switch. Wireless clients are not affected, that's why I'm lost here.
-
Could this be related?
https://social.technet.microsoft.com/Forums/en-US/b16e7d78-e390-4ada-a24b-3ccba60fa571/no-ipv6-dns-statelessdhcp-since-windows-10-anniversary-update?forum=win10itpronetworkingIf yes, is there any way to assign IPv6 to my VLANs other way than using Prefix Delegation?
Thanks.
-
you do understand its normal to have more than 1 temp address right...
Those address are not "duplicated" they are different you see d800 and d801 on the other.
Your double global is not good, but its a different prefix..
To be honest any doesn't seem like correct term for setting a vlan on a access port.. If all there is a pc, then it should only see traffic from whatever vlan its in.. not "any" So your prob running multiple layer 3 on the same layer 2 - which is why your seeing ipv6 from multiple prefix.
-
@johnpoz Thanks a lot for your reply. I noticed the difference now.
Could you give me some pointers where to look? PFSense VLAN settings or Switch (Mikrotik) VLAN Settings?
As I said, the issue only arise after the update to build 1903.Thanks again for any help you can provide.
Andrei.
-
just because you only noticed it after 1903 doesn't mean anything... Your switch settings make no sense to me..
When you have a device connected to a port and its in say vlan X... The only traffic that should go in an out of that port is vlan X... This "any" setting makes ZERO sense to me..
You would not be able to get an IP in a different prefix, unless you were on the same L2 as where that prefix is being advertised.. If your seeing prefix from 2 different network - then means you have a common L2 issue.
d800, and d801 are 2 different /64 prefixes.
Which network do you have d800 setup and which do you have d801 setup? Clearly there is a connection there at L2
-
@pbnet said in Duplicate IPv6 addresses:
Could this be related?
That was from almost 3 years ago and I haven't seen that problem.
-
@johnpoz said in Duplicate IPv6 addresses:
Those address are not "duplicated" they are different you see d800 and d801 on the other.
Those numbers appear to be on the prefix portion of the address, not suffix. There should only be one prefix, but you just pointed out 2.
-
@pbnet said in Duplicate IPv6 addresses:
Thanks a lot for your reply. I noticed the difference now.
Since you have a VLAN, I assume you have a managed switch. Any chance that switch is TP-Link? Some models of TP-link switch don't manage VLANs properly.
-
@JKnott Thanks for your reply
The switch is a Mikrotik (see below) and this one is cascaded to a cisco SG200-26.
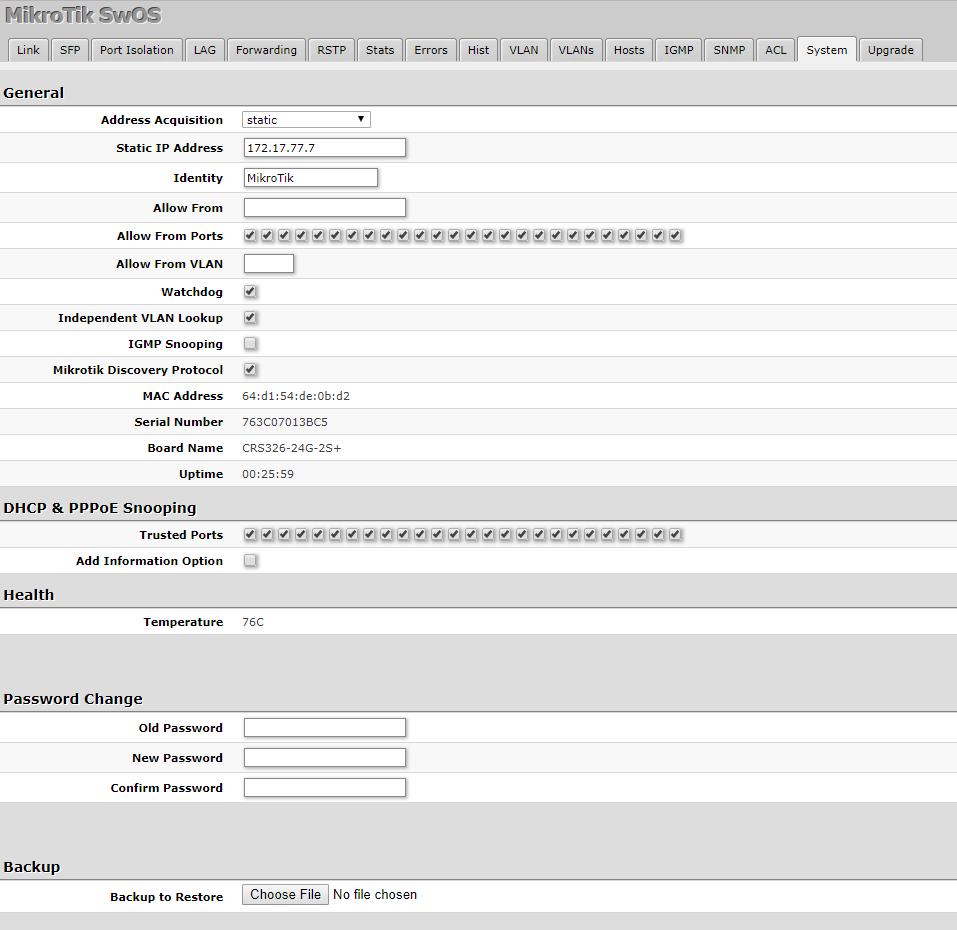
I've tagged VLAN 5 both in PFSense and on the Mikrotik switch, and nothing changed, IPv6 still don't work on my PC.
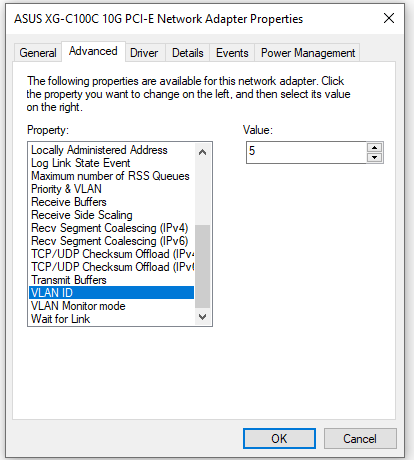
Then I've taggged packets for VLAN5 on the switch port where the PC is connected and it only works on IPv4 if I specifically tell the NIC on the PC I'm on VLAN5.

I'm really lost here :(
Thanks for all your help.
Andy.
-
@pbnet said in Duplicate IPv6 addresses:
I'm really lost here :(
Are the 2 prefixes assigned on your network? Have you run Wireshark to examine the RAs? If you're seeing RAs for both prefixes, you've got something crossed somewhere. The TP-Link problem I mentioned above was due to multicasts not being restricted to the VLAN so a device on the LAN would get the wrong prefix. Also, look at what's actually leaving pfSense. You can do that with Packet Capture right in pfSense or Wireshark, with port mirroring on the managed switch.
-
Not sure here
This is what gets assigned automatically on PFSense:
There is no DHCPv6, only RA:
-
OK, so I figured out that both prefixes (from VLAN5 and VLAN10) are assigned to the NIC on VLAN5 on the PC.
The problem is I have no idea how to limit the prefix to a specific VLAN. -
Then as I stated you do not have actual vlan isolation... Your just running multiple L3 on the same L2..
That is going to be issue with your switch config.. Are these both tagged, is 1 not tagged on pfsense?
pfsense - em0 vlan5T, vlan 10T -- switch -- vlan 5U -- pc..
There would be no possible way for pc connect to vlan 5 switch port to see vlan 10, traffic - unless you have it mis configured on the switch, etc.
-
@johnpoz
Well, each VLAN leaves PFSense on its own NIC:VLAN5 is on NIC bce1 and appears in PFSense as LAN: VLAN 5 on bce1 (VLAN5)
VLAN10 is on NIC bce3 and appears in PFSense as PBNETLAN2: VLAN10 on bce3 (VLAN10)The network cables that leave PFSense (running on a dell R710), reach the Mikrotik Switch like this:
- VLAN5 --> Port 1 --> VLAN Mode: Enable // VLAN Receive: Only Tagged // Default VLAN ID: 5
- VLAN 10 --> Port 2 --> VLAN Mode: Enable // VLAN Receive: Only Tagged // Default VLAN ID: 10
Desktop PC: Port 24: VLAN Mode: Enable // VLAN Receive: ANY // Default VLAN ID: 5
Call me stupid, but I still don't figure out what is wrong on this config.
Thanks.
-
Is port 24 an access or trunk port? Normally, it should be an access port, unless you need more than one LAN/VLAN on it.
-
@pbnet said in Duplicate IPv6 addresses:
VLAN5 --> Port 1 --> VLAN Mode: Enable // VLAN Receive: Only Tagged // Default VLAN ID: 5
Why are you setting up vlans on pfsense? If its the only network on the interface... It would just be native an untagged then..
-
Well, as far as I can understand from my logic, it looks more like trunk to me :(
Here's what Mikrotik says: https://wiki.mikrotik.com/wiki/SWOS/CSS326-VLAN-ExampleAnd this is my setup:
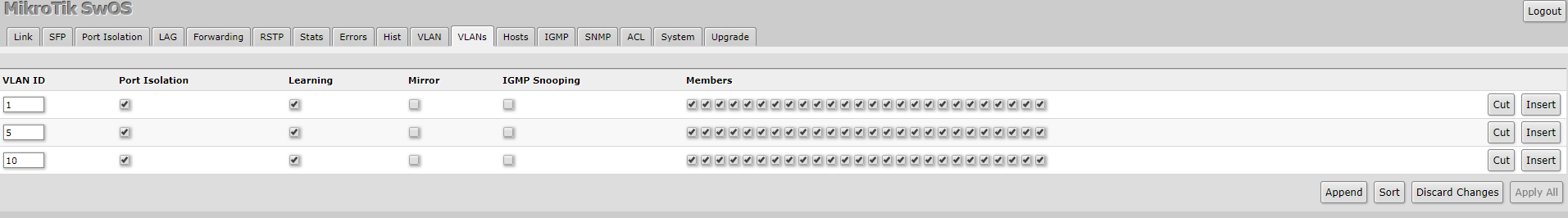
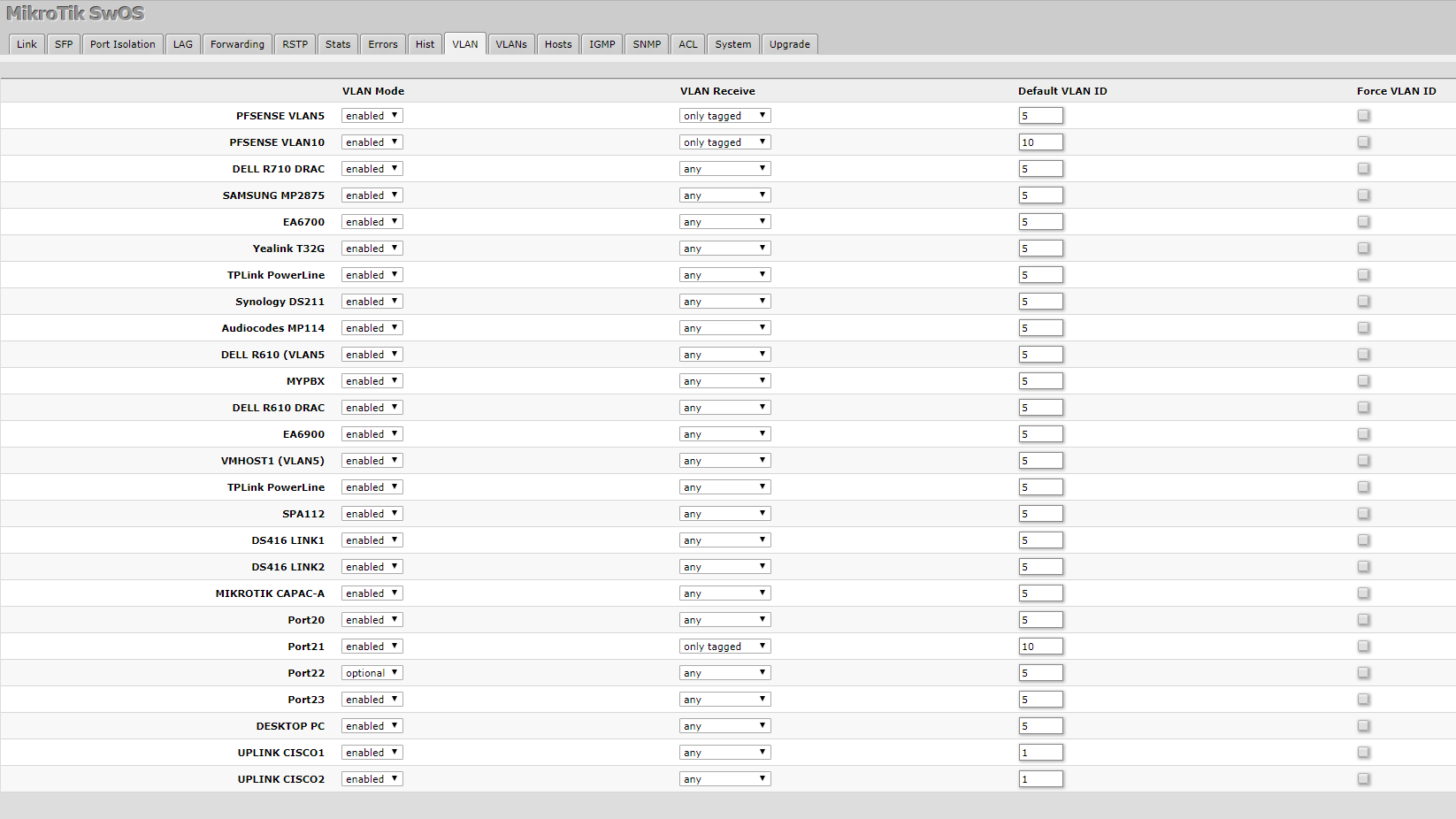
Correct me if I'm wrong. I didn't quite get the VLANS tab part :(
-
@johnpoz That seemed logical at that time when I first set up the VLANs... Can this be a problem?