Weird route for OpenVPN server
-
I just configured my OpenVPN server for remote access. I set the VPN network to 172.16.100.0/24 and everything seems to be working without an issue but when looking at Diagnostic - > Routes, it looks like the route for my VPN network is odd.
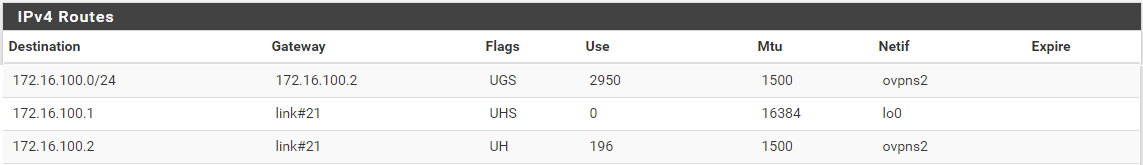
It seems odd to me that the gateway for the 172.16.100.0/24 network would be a client IP address. I tested by having two sessions connected so one laptop got .2 and .3 and everything was working okay. I tested by doing a continuous ping to google from .3 and when I disconnected .2 there was about a 20ms lag on the following ping but everything kept responding and working fine.
Is that route odd or is it just me? Is there a way to fix it or should I just not be concerned since everything appears to be working?
Thanks.
-
Is it working?
Looks normal to me.
That is how the kernel routing table routes that subnet into the OpenVPN server.
-
@Derelict Yes it is working so I'm not too concerned about it, but just to learn I was hoping to understand why the one route is that way.
The routes for 172.16.100.1 and 172.16.100.2 make sense to me but the 172.16.100.0/24 route confuses me a little.
If I'm somewhere else on the network and attempting to access a PC I have VPN'd in on 172.16.100.4, the traffic looks like it would get sent to 172.16.100.2 which is a client IP on the VPN subnet. Not a pfSense expert though so I could be misunderstanding the routes table.
-
A remote access server hands an address out of its tunnel network to each connected client.
You set 192.168.100.0/24 there. That uses the first two addresses for the server itself and then hands out the rest as clients connect.
The traffic to that server will get sent to 192.168.100.2 where OpenVPN itself will route the traffic to the connected client using its knowledge of what client has what address.
-
@Derelict Interesting, thanks.
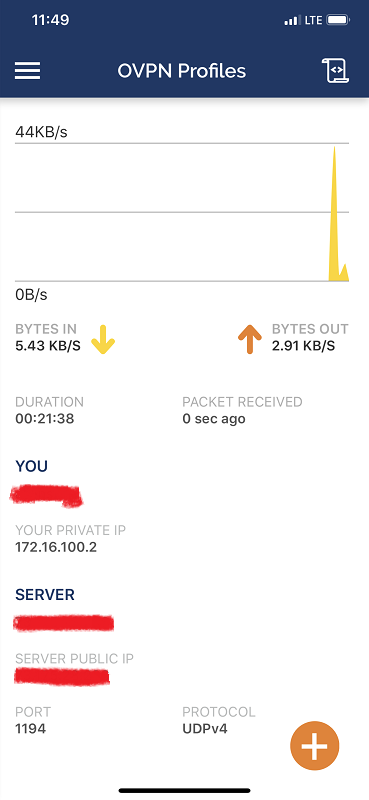
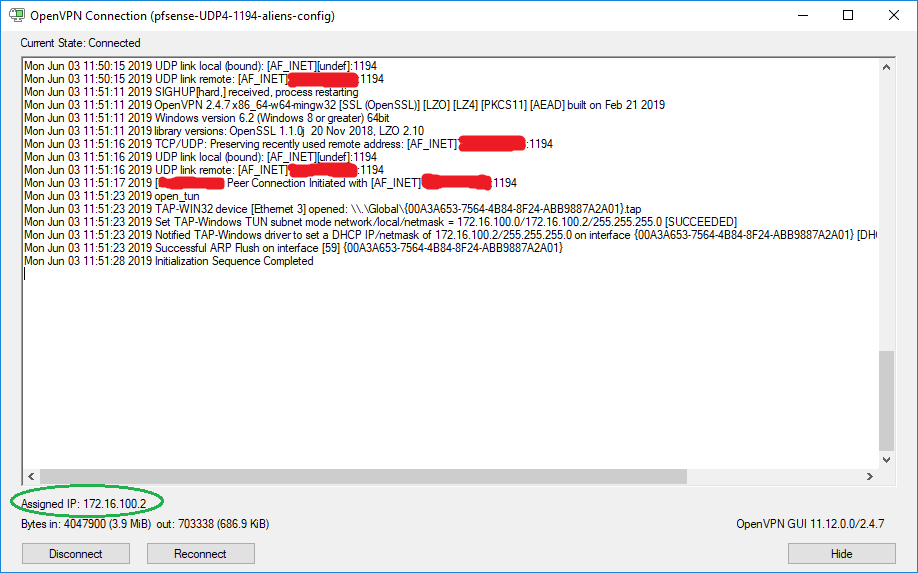
The first client I connect will always grab 172.16.100.2 so it's interesting that the IP is also used by pfSense itself.
I had my phone connected and it's IP was 172.16.100.2 and my PC was connected as 172.16.100.3
I disconnected my phone and reconnected my PC and it grabbed 172.16.100.2
-
OK. Did it work?
That is just the first client address.
What isn't working?
-
@Derelict Everything is working as far as I can tell. I love pfSense and would like to pitch it as an option for a few of our remote locations but before pitching the idea I'd like to understand what I'm looking at.
In my OP, the first line of the screenshot of the routes looks likes it's saying that it will send any traffic destined for the VPN network (172.16.100.0/24) to the gateway of 172.16.100.2 which is the first client IP address which is confusing to me.
You're saying that OpenVPN will use the first two IP's, I was assuming you didn't mean the .0 network IP and that OpenVPN server would use 172.16.100.1 and 172.16.100.2? But if that were the case then why is that IP also handed out as a client IP?
I'm hoping to understand why that route is worded that way or if it's just a mistake? Why would the traffic destined for the VPN network's next hop be to a client IP address?
-
OpenVPN has its own routing table. What you are seeing is a route for the whole subnet into OpenVPN. From there, OpenVPN sends the traffic to the appropriate clients.
Status > OpenVPN See the routing table there.
-
@Derelict Ah, that makes sense. Thank you very much for the help.