Running EdgeRouter X behind Pfsense
-
Hello guys is this possible?
I would like to use the edgeRouter X to stop bittorrent protocol on the network as there have been issues with pfsense doing that. So i decided to use edgeRouter X instead. -
Yes. You are double NATing which makes opening inbound connections harder but apart from that it will work fine.
I would consider that as pfSense behind the Edge Router though.
Steve
-
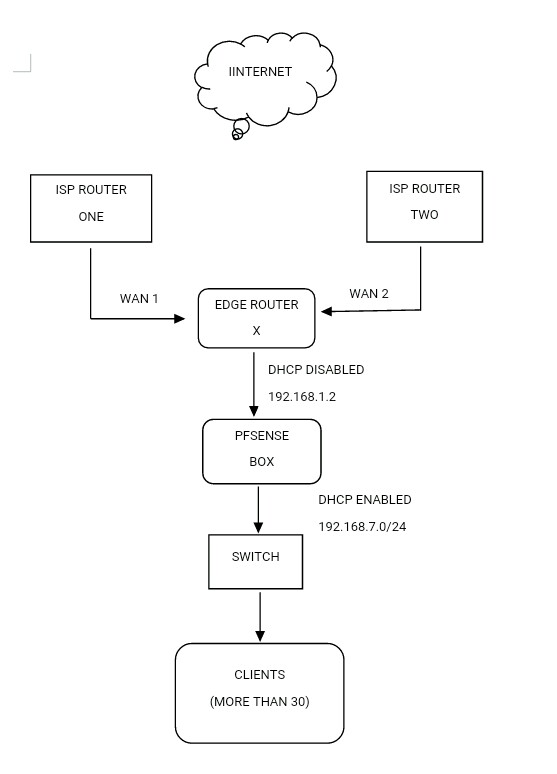
@stephenw10 I place the EdgeRouter before Pfsense to block torrents only, and pfsense hands over dhcp to all clients. I prefer pfsense to hand out dhcp as i can use Ntopng to check network usage for each Ip address and also use of pfblockerng
-
@OpenWifi said in Running EdgeRouter X behind Pfsense:
stop bittorrent protocol on the ne
Have you tried Snort and OpenAPPID to block bittorrent.
There is a rule:-
alert tcp $HOME_NET any -> $EXTERNAL_NET any (msg:"BitTorrent";flow:from_client;appid:bt; sid:70038 ; classtype:misc-activity; rev:1;)
-
@NogBadTheBad Imagine i tried that for about 3 weeks but snort can only block the host(and that would be bad for clients) in the case that someone downloads a torrent using that ip address.This would mean that the client might be blocked for the specified period of time. I just needed all torrents blocked on my network and not the host.
-
Maybe worth waiting for this:-
https://forum.netgate.com/topic/143810/snort-package-v4-0-for-pfsense-2-5-devel-release-notes
-
@OpenWifi said in Running EdgeRouter X behind Pfsense:
@NogBadTheBad Imagine i tried that for about 3 weeks but snort can only block the host(and that would be bad for clients) in the case that someone downloads a torrent using that ip address.This would mean that the client might be blocked for the specified period of time. I just needed all torrents blocked on my network and not the host.
If you want to try pfSense-2.5-DEVEL, I just posted a new Snort package for that version that supports inline IPS mode operation. That would be perfect for your application. You would enable the Inline IPS Mode and then use SID MGMT tab settings to change the action for rule SID 70038 from ALERT to DROP. The new rule would then look like this:
drop tcp $HOME_NET any -> $EXTERNAL_NET any (msg:"BitTorrent";flow:from_client;appid:bt; sid:70038 ; classtype:misc-activity; rev:1;)Of course if you have a production environment, pfSense-2.5-DEVEL might not be appropriate. But unless pfSense-2.5 takes a very long time to make it to RELEASE, there are no plans to backport this new Snort functionality to pfSense-2.4.
-
@bmeeks i am a wireless internet service provider. Would 2.5 Development work for me
-
@bmeeks Actualy no need, i already installed the new update to 2.5 dev. Kindly take me through step by step on how to configure snort to drop bittorent packets. I know it may take time but i am desperate and do kindly understand. Thank you
-
@OpenWifi said in Running EdgeRouter X behind Pfsense:
@bmeeks Actualy no need, i already installed the new update to 2.5 dev. Kindly take me through step by step on how to configure snort to drop bittorent packets. I know it may take time but i am desperate and do kindly understand. Thank you
I don't know if I can give you step-by-step as I don't normally provide that level of support, however the configuration is pretty easy. I can give you a summary and a few links to help.
-
First you need to install the latest Snort 4.0_1 package on the pfSense-2.5 firewall. If you have an older version of Snort there already, then first remove that package completely and install it again. Do not just click the reinstall icon! To remove it, go to the SYSTEM > PACKAGE MANAGER page and on the Installed Packages tab click the trash can icon beside the Snort package to remove it. Let the removal process finish before you click away from the tab. It will take a few seconds. If you don't have Snort installed at the moment, then skip this removal step.
-
Now click the Available Packages tab and find the Snort 4.0_1 package. Click to install it. Any previously saved configuration settings for Snort will be restored during the installation. Let the process complete! You will get a green bar and a success message when it finishes.
-
With the new package installed, go review the setup instructions in this link: https://forum.netgate.com/topic/143812/snort-package-4-0-inline-ips-mode-introduction-and-configuration-instructions. There are screenshots in that link.
-
For your situation, choose the selection of OpenAppID rules or OpenAppID categories that you wish to block content. You can do that by looking at them on the CATEGORIES and RULES tabs. You need to click the checkbox beside each category you want to use on the CATEGORIES tab. Save the changes on that tab. You can then see the individual rules on the RULES tab when selecting a category in the drop-down selector on that page.
-
Now go to the SID MGMT tab and click the checkbox to enable Automatic SID Management.
-
In the middle section, click Add to create a new SID Management list. Name the list
dropsid.conffor clarity. In the text box you can use commands similar to what were shown in the linked example. In your case change the rule category name from "emerging-scan" to whatever OpenAppID rule categories you want to drop. For example, openappid-social_networking. Add any other rules on the same line by separating with a space, or you can put each category on the same line. The syntax of the SID management conf files is shown in the *-sample.conf files. You can click the pencil "edit" icon to open one of them and read the contents. -
Once you have a
dropsid.conffile filled in, save it and then at the bottom of the page assign the newdropsid.conffile to the interface by choosing the filename in the Drop SID List drop-down selector. -
Finally, click the checkbox under the Rebuild column to signal Snort to rebuild the rules for that interface when you save this new configuration. Be sure the click Save to save your changes.
-
If not already started, go start Snort on the interface and things should work.
-
-
@bmeeks Thank you, i tried that but as soon as i enable snort on lan interface i loose internet connection, so i have to login through OpenVPN and disable snort to get my connection back. I think i hurried to upgrade to 2.5 and really ashamed of that. I think the upgrade is the one affecting the connection
-
@OpenWifi said in Running EdgeRouter X behind Pfsense:
@bmeeks Thank you, i tried that but as soon as i enable snort on lan interface i loose internet connection, so i have to login through OpenVPN and disable snort to get my connection back. I think i hurried to upgrade to 2.5 and really ashamed of that. I think the upgrade is the one affecting the connection
I did not mention it specifically in my post above, but you must have a NIC whose driver supports netmap. That is currently a somewhat small list. Your NIC driver name in pfSense must be one of the following families or netmap is not likely to work: em, igb, ixgb, ixl, lem, re or cxgbe. You can see the name of your NIC drivers by going to STATUS > INTERFACES in pfSense. The driver name will be shown in the dark header band for each interface. It will show the interface name in pfSense such as LAN and then in parentheses the NIC driver family name.
-
@bmeeks i have 2 Wan interfaces(em0 and rl0) and 1 Lan(re0), will it work?
-
@OpenWifi said in Running EdgeRouter X behind Pfsense:
@bmeeks i have 2 Wan interfaces(em0 and rl0) and 1 Lan(re0), will it work?
The Intel em0 driver should definitely work. That's the one I tested with, in fact. The Realtek re0 driver is also supposed to work, but Realtek NICs and FreeBSD don't have a good working history together. Lots of issues with the Realtek drivers and those NICs have a poor reputation around here. The rl driver is not on the list of supported driver families.
Do you have a dual or quad port Intel NIC you could put in the box and abandon the Realtek ports? Since you have two WAN interfaces (I assume for redundancy), I would not suggest putting a Snort inline instance on either of them (and that rl driver interface would not work anyway).
Do you have another hardware box you could set up separately and test with. Even an old PC laying around that you could put an Intel network card in and just verify things work? That would then help you decide if it would be worth the trouble to reconfigure the hardware in your production setup.
-
@bmeeks As of this moment i do not have an extra Intel Nic(em0) but i could go and purchase one, although they are hard to get in my area. As long as that would enable blocking of the torrents then i would have no problem purchasing one. Just to clarify, that means the Realtek Nic wont work?
-
@OpenWifi said in Running EdgeRouter X behind Pfsense:
@bmeeks As of this moment i do not have an extra Intel Nic(em0) but i could go and purchase one, although they are hard to get in my area. As long as that would enable blocking of the torrents then i would have no problem purchasing one. Just to clarify, that means the Realtek Nic wont work?
According to the netmap documentation it is supposed to work, but I'm just saying that Realtek support in general on FreeBSD is not great. Do a search here on the forums for "Realtek" and you will see lots of threads about various Realtek driver problems. So I'm not saying the re0 interface won't work, but it would not be my first choice of NIC to use.
-
@bmeeks Could i reassign the Lan (re) interface for the Wan (em), in the case the Realtek doesnt respond?
-
@OpenWifi said in Running EdgeRouter X behind Pfsense:
@bmeeks Could i reassign the Lan (re) interface for the Wan (em), in the case the Realtek doesnt respond?
Sure, but that might confuse the existing Snort configuration. If you do that, and don't have a lot invested in the current Snort configuration, I would just delete all the interfaces from the Snort INTERFACES tab before re-assigning interfaces in pfSense.
After you get the interfaces sorted out in pfSense you could create the Snort configuration fresh. Snort uses the NIC driver name for its configuration and logging sub-directories for each interface, so if the driver name changes that will confuse Snort. Deleting the Snort interfaces and creating them again after you finish the NIC shuffle will be better.
-
@bmeeks Thank you. Would that mean that even for packages such as pfblockerng,ntopng and OpenVpn i would need to reinstall or change some config?
-
@OpenWifi said in Running EdgeRouter X behind Pfsense:
@bmeeks Thank you. Would that mean that even for packages such as pfblockerng,ntopng and OpenVpn i would need to reinstall or change some config?
I can't answer that one with 100% accuracy, but I don't think so. Those packages don't really care about the physical interfaces (at least pfBlockerng does not). Snort and Suricata are a bit different because they must know what's called the "real interface name" in FreeBSD in order to bind to that interface. So you call it WAN, LAN, OPT1, OPT2, etc. in pfSense; but to FreeBSD real interface names are em0, em1, re0, re1, etc. And a VLAN on an interface shows up as a decimal followed by the VLAN ID. Something like em0.10 for a VLAN on interface em0 with a VLAN ID of 10.