NAT/Firewall , restricting source IP ranges
-
Hi All
My rule/nat work fine when using no source IP range restriction. As soon as I place the source IP restriction on the NAT (which then automatically adds it to the rule), I cannot get in on port 6165.
My public IP is part of a Host alias thats permitted.
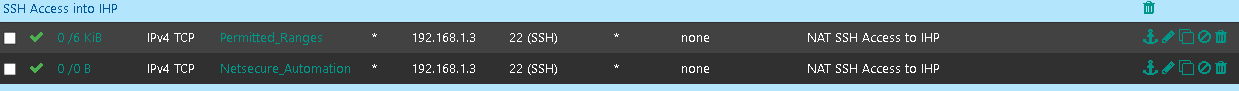
Rules
NAT
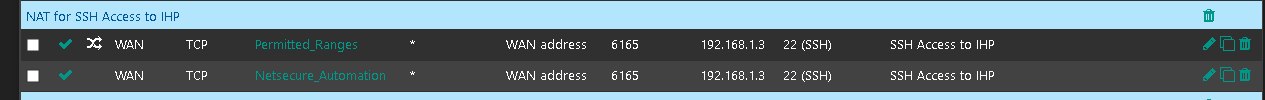
I dont understand why it works when I dont restrict the source, but fails when I do. The permitted range alias, has a static of subnets. The Netsecure Automation alias as some specific host ips, it contains the IP im trying to SSH From.
Packet capture shows the packets arriving but no traffic.
Odd!
Thanks
-
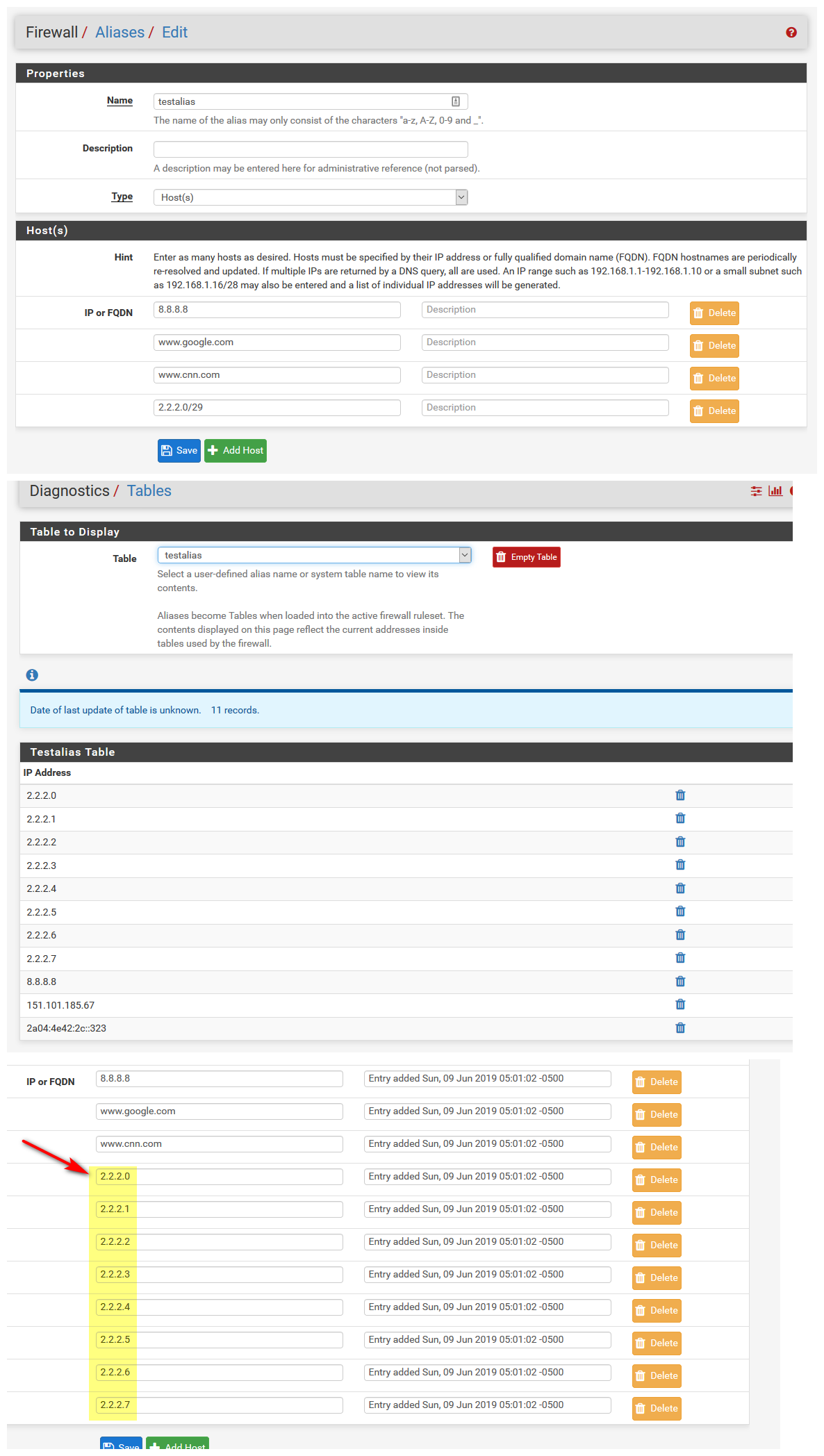
You validated your aliases are correct via the diag table feature, it will list what is in your alias.
Why do you have 2 rules? And the one is linked, and other is not..
-
I have two rules because I couldnt add two alias, one for hosts and one for networks.
When i tried to add hosts into a network alias, it wouldnt work.
Ill check diag. I fixed the linkage
Interesting, the Diag Table is not showing my Public IP inside, that would be why. But why wouldnt it!? I have 3 hosts in there, 2 are /32s and one is a DNS name of a host
Infact, the Table only shows 1 host address and fails to show the other (my PC's address) and also the resolved dns name
-
The table is failing. It's not doing the following:
A) Adding my public IP
B) Not resolving a public DNS name to a host entry and adding this -
Deleting and recreating the alias as fixed the issue
-
Not sure why you think you need multiple aliases to do that..
You can put in single ip, fqdn, and even a range into hosts.. Should not be too big of a range... But it will expand that range to single hosts, etc.
-
Thanks. Ill keep that in mind for next time. It would be nice to have multiple alias inside the rule, rather than nested alias
In any case, ill leave it how it is - as its easy to read for troubleshooting :)
Thank you