Allow specific access from DMZ to Internal Server
-
Folks - Maybe it has been a long day but I have a likely stupid question:
I want to allow access from the DMZ to a specific internal server - from a reverse proxy to an internal web server.Reverse proxy is 192.168.1.100
Internal web server is 192.168.2.100Specific to my problem the rules are...
- Deny all access to the internal network (e.g. block access to the 192.168.2.0/24 network)
- Allow access from DMZ to internal server (192.168.1.100 TCP/80 to 192.168.2.100 TCP/80)
I have logging for reverse proxy to internal web server enabled but nothing shows up in the log.
EDIT: I just enabled logging on the block DMZ to internal network rule and I can see the blocks here.
What am I missing here?
Thanks!
-
Rules are processed top-down, first-match. You need to put your allow rule above your deny rule.
https://docs.netgate.com/pfsense/en/latest/firewall/firewall-rule-processing-order.html
-
Hi Kom - I tried that... No success...
-
Post a screen of your DMZ rules.
-
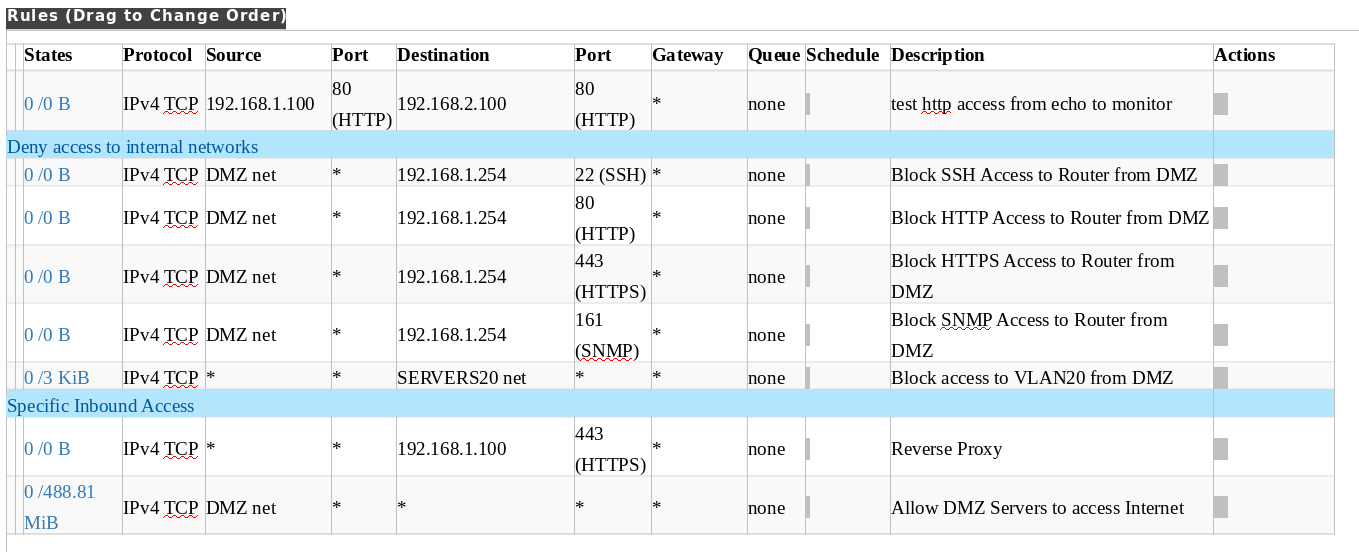
"Sanitized" version. VLAN20 is the internal network. "echo" is the proxy (192.168.1.100). "monitor" is the internal server (192.168.2.100)
-
This may be a stupid question since I don't have much experience with reverse proxies, but is the source port supposed to be 80 instead of *? Usually the initiating end uses a random source port >1024 to talk to the server at the server's listen port. When you see the blocks from DMZ to LAN in the firewall log, is 192.168.1.100 being blocked, or is it other traffic? If it's blocking 192.168.1.100, what source port is 192.168.1.100 using?
-
The reverse proxy listens externally to 443. Two reasons for this:
-
I only have one external IP address and want to run the web server on a standard port. There are a couple of other web servers in the DMZ that run internally on 80. The reverse proxy accepts all connections on 443 and then directs the requests (internally) to the appropriate server listening on 80. Thus
https://myurl.com/serverA:443 is directed to http://dmzservera.int:80
https://myurl.com/serverB:443 is directed to http://dmzserverb.int:80 -
This also makes it slightly easier to manage my SSL certificates - they all only have to go on the reverse proxy.
The external access works find from the proxy to the internal DMZ servers just fine.
The problem is the reverse proxy cannot access the internal server. The firewall is blocking the traffic despite the top rule allowing TCP 80 from the reverse proxy to internal server.
-
-
I have this working. Only two changes: 1. instead of IPs I created aliases and 2. I changed the source port to be any instead of 80.
...and I rebooted the firewall.
Now it works.
-
So it was the source port after all. Glad to here you got it working.