windows 10 openvpn connect to multiple remote clients
-
This post is deleted! -
OK so the routes are there. Are you passing the traffic into pfSense on the OpenVPN firewall rules?
Are the services on 192.168.1.0/24, 192.168.2.0/24, and 192.168.3.0/24 being blocked by some local firewall on the target hosts? (think windows firewall there.)
-
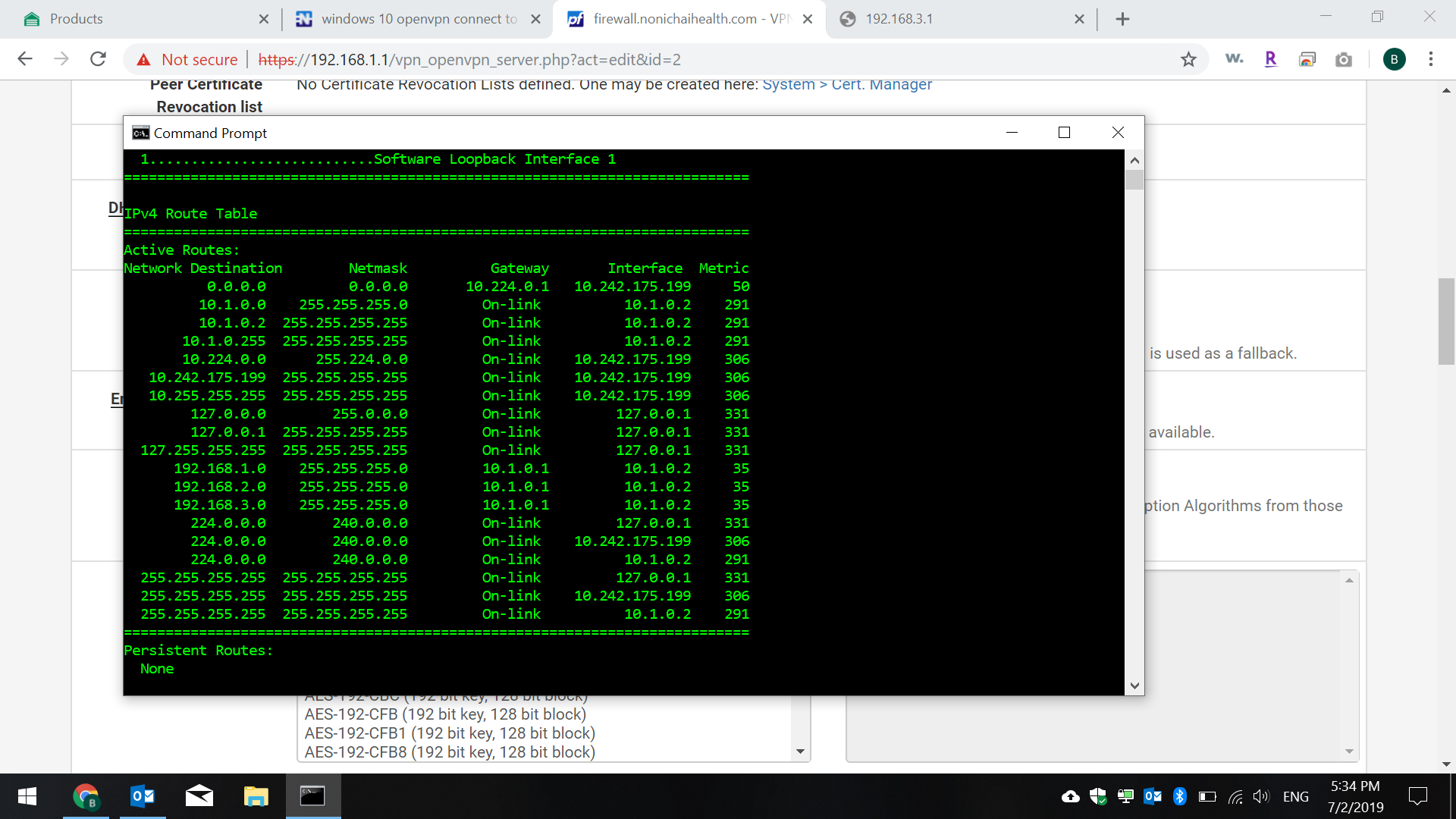
i imagine i type that command in CMD of windows? if yes, here is the screenshot of the results.
-
bump ^
-
@Derelict
my firewall in pfsense has a rule for openvpn interface to pass any protocal from ipv4
source and destination is set to any.
do i need another firewall rule in pfsense? -
Post said rule.
-
@Derelict see attached
sorry for the delay in responses, i have to wait 120 seconds between each post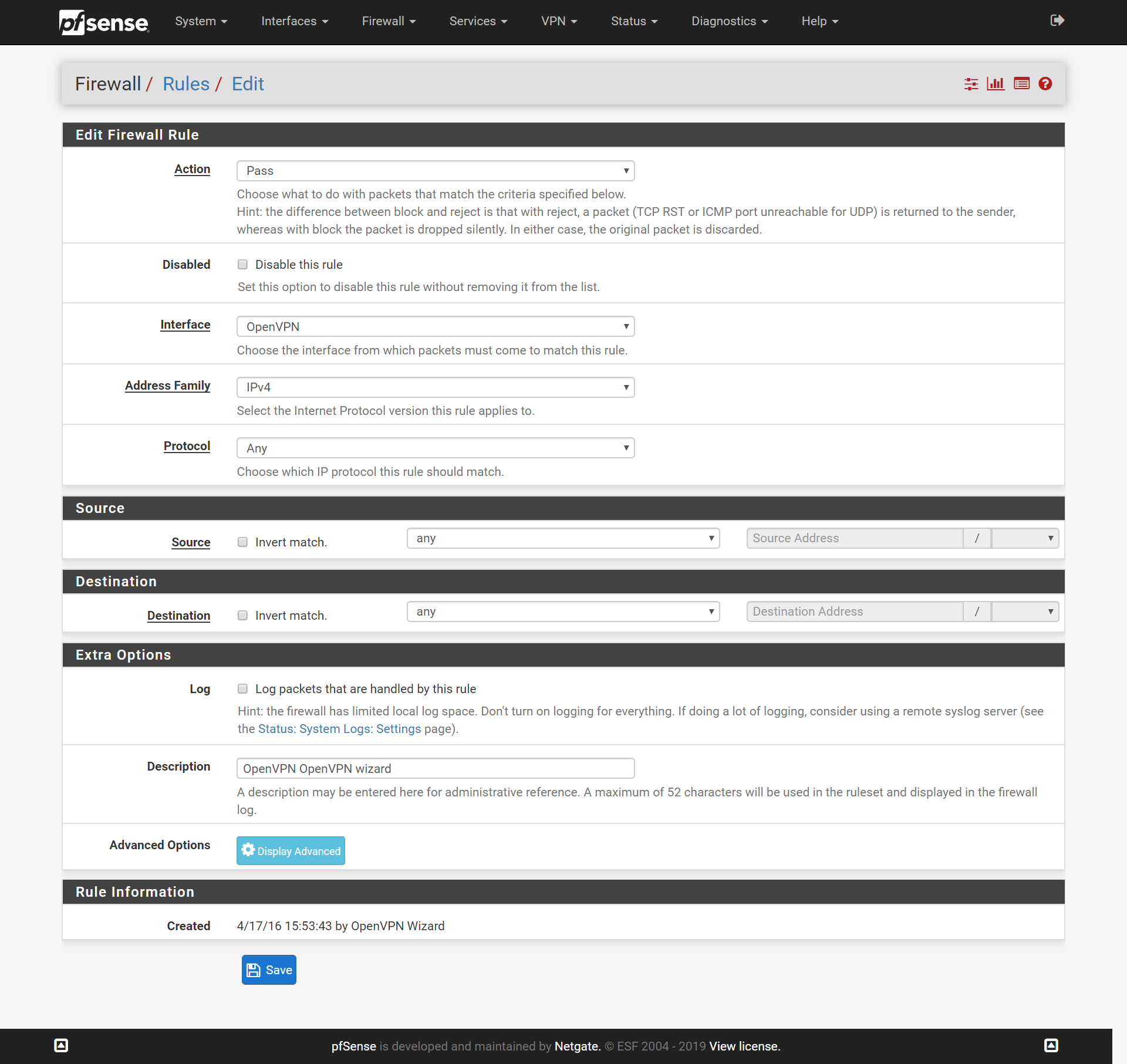
-
OK it's not that. check the firewalls on the target hosts.
Try to ping the pfSense interface addresses.
-
ping from pfsense router 192.168.1.1 to a remote one 192.168.3.1
PING 192.168.3.1 (192.168.3.1): 56 data bytes
64 bytes from 192.168.3.1: icmp_seq=0 ttl=64 time=31.684 ms
64 bytes from 192.168.3.1: icmp_seq=1 ttl=64 time=34.436 ms
64 bytes from 192.168.3.1: icmp_seq=2 ttl=64 time=33.773 ms--- 192.168.3.1 ping statistics ---
3 packets transmitted, 3 packets received, 0.0% packet loss
round-trip min/avg/max/stddev = 31.684/33.298/34.436/1.173 msping from CMD windows 10
Pinging 192.168.3.1 with 32 bytes of data:
Request timed out. -
No. From an OpenVPN client, man.
-
im sorry if im new and not understanding this properly and i appreciate your help.
isnt my windows 10 computer considered the client? this is a vpn connection on my laptop when i travel i have openvpn installed and i login and i can connect only to the main pfsense server that is hosting my openvpn to my laptop client as a remote access user auth.
however the same pfsense main server has other openvpn connections to remote pfsense routers in 2 other office locations using peer to peer shared key, and from my laptop i can not access those remote offices that are connected to my main pfsense server at the main office -
Your client is connecting and getting an address in the tunnel network, 10.1.0.0/24 (10.1.0.2)
It is being pushed routes to route 192.168.1.0/24, 192.168.2.0/24, 192.168.3.0/24 over the tunnel. That looks like it's working.
So from that connected client, ping 192.168.3.1. If that works, the VPN is working.
Then try to access a host on that network (or one of the others.) if that fails it is almost certainly a firewall on the TARGET host, not on the pfSense firewall. Windows in particular likes to filter connections to it to just it's local subnet. Yout 10.1.0.0/24 tunnel network will be outside of that subnet.
-
Don't take this the wrong way, but you might want to hire someone to set this up for you.
-
do you know someone?
-
-
thx