Having issues with pfSense box
-
Hi everyone,
I have a router running pfSense 2.4.4, its an Intel Celeron 3865U with 6 gigabit ethernet ports.
Recently I started noticing slow speeds while accessing some websites, not being able to access others.So fast forward I ended up spoofing the box WAN mac address and connecting directly to my laptop. I get the same IP the pfSense had, and I don't have the same connectivity problems.
But... MTR still shows me some packet loss.
Could this packet loss be amplified by pfSense in someway?Also, I use LDAP authentication on my pfSense box. If the authentication fails (link down, timeout, wtv) the pfSense locks up and I have to reboot it.
Many times I can't access the pfSense via FQDN, I must use the IP address.Now... I don't get errors on any interface. Not in nor out.
EDIT: Another thing I just remembered.
The issue of not being able to access the pfsense FQDN and some other websites happens in two different mac's. One has the latest OS updates (Mojave 10.14.5 (18F132)) and the other one is the latest High Sierra for the 2011 iMac.
It also happens when I try to access via Guest user (to clear possible profile-related issues).
BUT it works correctly when I access via iPhone, I can always access the firewall (unless it's bricked bc of ldap login failed) but other websites work.
The pfSense is the DNS server for the network:
127.0.0.1
1.1.1.1
1.0.0.1I have also restored a one month configuration backup, the issues persist.
I need help debugging this, if anyone may help.
I have Snort installed, but not-blocking.Thanks! RM
-
https://doc.pfsense.org/index.php/Connectivity_Troubleshooting
Disable any packages that might interfere with your traffic, like squid, snort, pfBlocker etc.
-
Hi Kom, thanks for your reply.
Even though having Snort with blocking disabled, you still recommend disabling/removing it completely?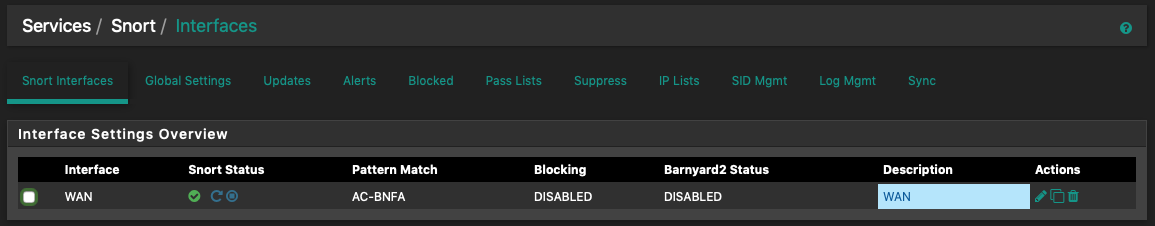
Not using pfBlocker, squid, etc
All the troubleshooting steps from the document you provided have been verified and its all OK.
I also don't get it why failing ldap auth bricks the router.
-
Just disable, no need to remove it. Packages that block things are one of the first suspects when you have connectivity issues.
No idea about ldap fails locking up pfSense. Lots of others use ldap auth without any problems. When you say locked, can you still access it via console? WebGUI has/had an issue where if its DNS was broken for whatever reason, the GUI response was really slow. Like 30s-2m to update.
Some of your other problems could be caused by DNS issues with Cloudflare as noted above. Are you using forwarder or resolver? Are you using DNSSEC? TLS/DNS?
-
Hi Kom,
Once again thanks for your feedback.
Well when I say locked, yes I can access it physically and perform a reboot via console. But for example if I have an active SSH connection this will break too.
I have DNS Resolver enabled, these are the options I have configured:
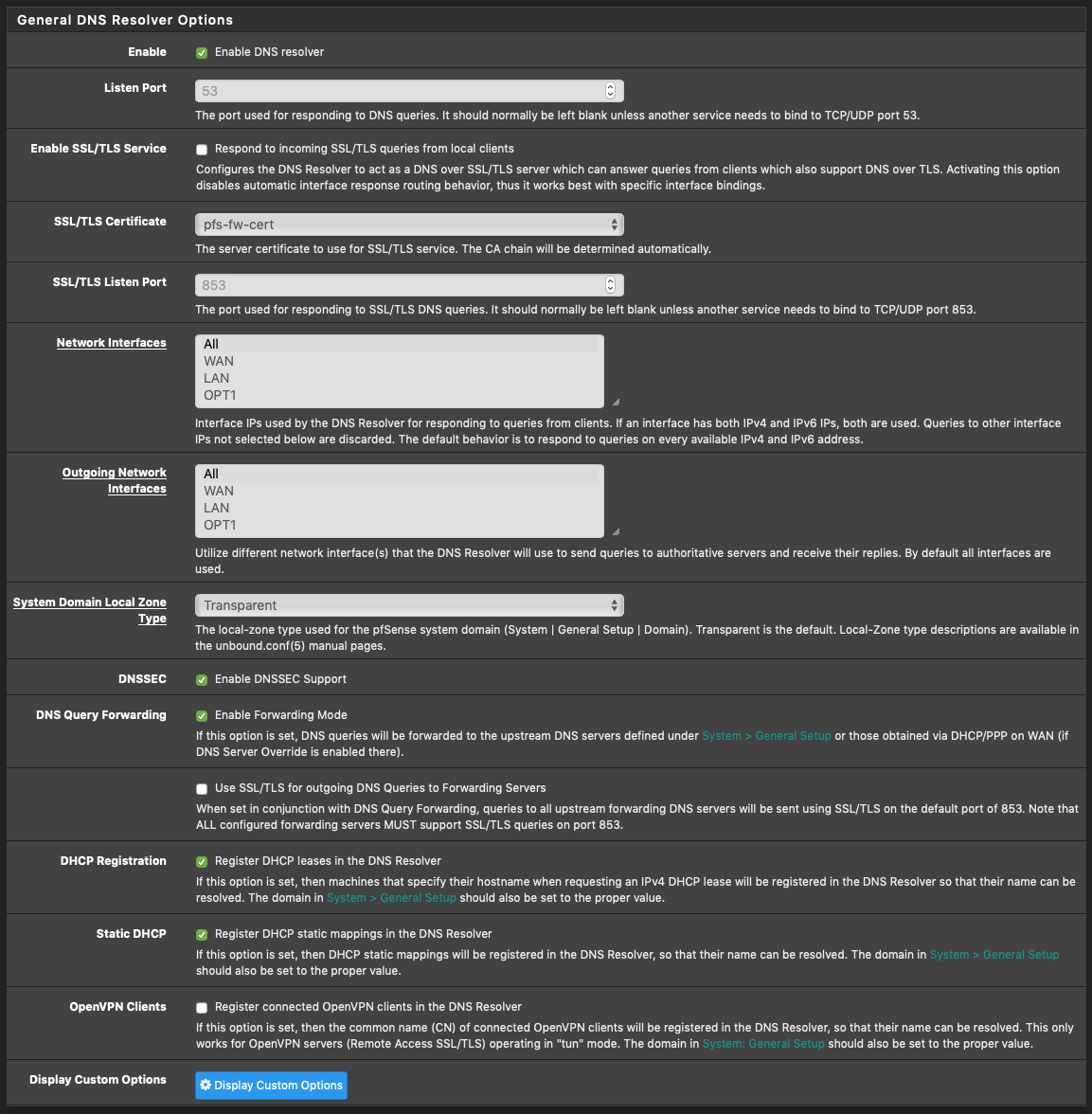
Certificate is valid, using acme package with let's encrypt.
-
i've seen several suggestions posted previously about unchecking DNSSEC being enabled in the resolver
- enabling use SSTL/TLS for outgoing DNS.
everything else looks good
-
Ok thanks. I will enable SSL/TLS for outgoing DNS Queries and if I have issues again I will disable DNSSEC support, bc before I wasn't having problems with it enabled, and right now, today, everything is working just fine!!! Thanks!
-
@maverickws said in Having issues with pfSense box:
I will enable SSL/TLS for outgoing DNS Queries
Which will add another layer of complicity to you DNS setup.
Your DNS requests between pfSense and the upstream DNS servers, the ones you are forwarding to, will be 'invisible'.@bcruze said in Having issues with pfSense box:
unchecking DNSSEC
Basically, you downgraded the Resolver to a simple forwarder - consider using the Forwarder then, and de-activate the Resolver.
DNSSEC has no sense when you use a forwarder. -
@bcruze said in Having issues with pfSense box:
unchecking DNSSEC
Basically, you downgraded the Resolver to a simple forwarder - consider using the Forwarder then, and de-activate the Resolver.
DNSSEC has no sense when you use a forwarder.I didn't disable DNSSEC!!
But can you please be a little more explicit about why you say "you downgraded the Resolver to a simple forwarder" didn't get this.
Thanks -
See here : https://docs.netgate.com/pfsense/en/latest/dns/unbound-dns-resolver.html
Also : pfSense has a build in Forwarder :
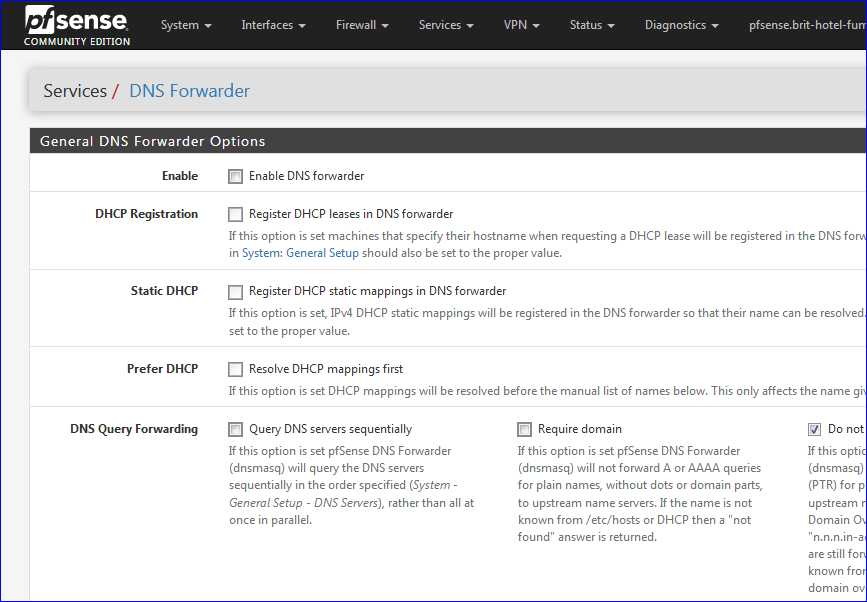
Note : the Forwarder- the good old dnsmasq - (probably) doesn't support "SSL/TLS for outgoing DNS Queries".
You can use the Forwarder (dnsmasq) - or the Resolver (unbound), but not both at the same time.
Btw : The default Resolver doesn't need you to put in any 'external' DNS servers.
Doesn't need you to do anything from working out of the box.IMHO : All the options and settings exists so it's more easy to break you DNS ^^
(and , of course, to handle these special case situations where the uplink Internet connection has some 'issues') -
Hi, thanks for your reply. I still don't understand why you are suggesting that I switch from resolver to forwarder. I must be missing something, I'm sorry.
Secondly,
Btw : The default Resolver doesn't need you to put in any 'external' DNS servers.
Doesn't need you to do anything from working out of the box.So, I can't /shouldn't tell my pfsense what upstream DNS servers to use?! It happens to be CF, could be OpenDNS, could be any others, why is it that I shouldn't put external DNS servers? (btw I have CF IPv4 and OpenDNS IPv6)
-
A forwarder merely forwards DNS requests to another upstream DNS server. For it to work, you need to give it the IP address of another server to forward to.
A resolver talks directly to the root DNS servers to find out from them who is the authoritative DNS for the FQDN you're requesting, and then talks to that authoritative DNS server and gets the IP address from that server. You don't supply any upstream DNS for this to work because it talks to the root servers which are a standard well-known list of special core DNS servers. However, resolver can work in forwarding mode, in which case you do need to supply it with upstream DNS via General Settings - DNS Servers. If you're going to forward, you may as well just use the forwarder and disable resolver.
There are other reasons why you would use one over the other that we can get into later if you're curious.
-
OOHH! Excellent explanation ok it all makes sense. Removing the upstream DNS servers from config!
I am always curious if you got the time and the will to let know about those other reasons, let it rip! :)You've been great, thanks for all the help!
EDIT: It seems that disabling the option "Enable DNS Forwarding" isn't enough, I MUST remove the upstream DNS servers from General Settings, or it will still query those. Am I wrong?
(bc I just disabled the option then went on Diagnostics > DNS Lookup and it kept querying the upstream servers.) -
@maverickws said in Having issues with pfSense box:
I MUST remove the upstream DNS servers from General Settings, or it will still query those. Am I wrong?
Yes ;)
The GUI page "Diagnostics => DNS Lookup" gets a listed of all name servers form the known systemwide resolver.conf file.
That's where are listed 127.0.0.1 (pfSense itself, thus the Resolver) and all other listed name servers, the ones you added yourself on the "General" page.
They are all tested by this PHP page.The Resolver itself, accsibkle at 127.0.0.1 @ port 53 - using default settings - doesn't use the these servers. It will question the 13 main root servers and dig downwards.
-
@Gertjan
Hi there, thanks for your reply!So what you say is, just to confirm I am understanding fully, I may keep them under General Settings, they may be used by the webConfigurator when I query via Diagnostics > DNS Lookup, but as long as I have forwarding disabled on the DNS Resolver they won't be used. That's it?
-
@maverickws IMHO : Yep.
-
Yes, Diag > DNS Lookup will test all the defined DNS servers on the system.
In the default config it will use the resolver directly though.
That means you are running the resolver (Unbound) not the forwarder (DNSMasq). Unbound is not running in forwarding mode. You have not checked
Disable DNS Forwarderin System > General Setup.Steve
-
@maverickws said in Having issues with pfSense box:
I am always curious if you got the time and the will to let know about those other reasons, let it rip! :)
Resolver is initially slower as it has to walk the DNS tree from the roots down until it gets its answer, but this is more private as you don't have a middleman seeing your DNS requests. Once resolver's cache fills up with the requests you make most frequently, it's just as fast as forwarder.
Forwarder is fast because it talks to upstream DNS that most likely already has cached the ip address you're requesting, but it's less secure because whomever you're forwarding to knows what you're requesting.
You can enable DNS over TLS to encrypt your DNS traffic from man-in-the-middle snooping by your ISP, for instance.
-
@KOM said in Having issues with pfSense box:
@maverickws said in Having issues with pfSense box:
I am always curious if you got the time and the will to let know about those other reasons, let it rip! :)
Resolver is initially slower as it has to walk the DNS tree from the roots down until it gets its answer, but this is more private as you don't have a middleman seeing your DNS requests. Once resolver's cache fills up with the requests you make most frequently, it's just as fast as forwarder.
Forwarder is fast because it talks to upstream DNS that most likely already has cached the ip address you're requesting, but it's less secure because whomever you're forwarding to knows what you're requesting.
You can enable DNS over TLS to encrypt your DNS traffic from man-in-the-middle snooping by your ISP, for instance.
so if you enable DNS over TLS with just the resolver enabled, no other DNS servers listed in general..
how do you know the DNS servers are capable of handling that type of service?
-
You don't and generally they are not. You need to use forwarding mode for DNS over TLS to something you know does support it.
Steve