Is it possible to use IDS/IPS with pfSense in bridged mode?
-
Question for the community:
I currently have Comcast and run pfSense with Suricata IPS and also pfBlocker. I have Unifi AP, with the Unifi controller also running on my pfSense box. A relatively clean setup.
My residential building recently got Starry ISP. It's a startup ISP that uses microwave technology for delivering connectivity. As I understand they use standard Ethernet protocols to deliver connectivity from the receiver on the roof of the building to the apartments. However, they require that you use their router/wifi equipment ("Starry Station") for connectivity, I suppose it does some sort of proprietary negotiation with their HQ to establish connectivity and get a public IP address. They claim that, at this time, you cannot place their router into a bridged mode.
My question: first, anyone has any experience with this type of setup for other ISPs? I would like to keep the protections that the pfSense offers (IPS, pfBlocker). I guess I have two options: (1) double-NAT (which may lead to other issues down the road when I want to do some port-forwarding); (2) place pfSense into bridge mode and connect Starry Station on the LAN side of the pfSense. In the case of #2, would I be able to still have my traffic inspected and blocked as I have today?
Any other options?
Thanks!
-
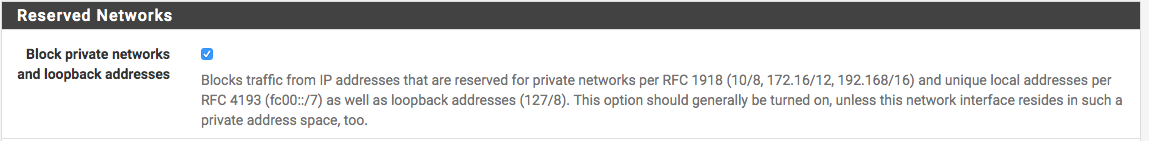
Bridge mode would mean bypassing pfsense I believe. So, when it comes into your apartment, does the ISP assigns a private IP address to you? If so, it would still work...you'll need to disable (uncheck) the private address on WAN.
-
You can run in double nat mode without any real issues if you must - that is going to be way less complicated then running pfsense in bridge mode..
I would just double nat, until such time you run into some issue.. Since your prob not going to..
-
@NollipfSense I think they would assign a public IP, but I don't know for sure. I got a 3-month trial. Will test next week.
-
@johnpoz Yes, I think that will be the easiest solution for now. My only question: would the VPN on my pfSense still work? I guess I'll need to do some port forwarding from the ISP's router. Or maybe even place the LAN side on their router into DMZ mode.
-
Normally what you would do in a double nat setup is yeah put pfsense wan IP in the dmz host of the router upstream.. This way you only need to mess with 1 place for port forwards.
But sure if you need port X to be forwarded on pfsense to something behind, then you would make sure the nat upstream forwards port X to pfsense wan IP first.