Conditional forwarder pointed to pfSense causes Error 5504
-
Hello,
I'm trying to use pfSense as our dedicated management router with its own DHCP and DNS services. We have conditional forwarders setup in our Windows-based DNS servers for our management domain, pointed at our pfSense instance, and vice versa. So:
pfSense DNS (10.0.10.1): management.local
-conditional forwarder for corporate.local via 10.0.0.1 (DC IP)Windows DNS (10.0.0.1): corporate.local
-conditional forwarder for management.local via 10.0.10.1 (pfSense IP)Resolving querys via the conditional forwarder works with pfSense, but not the Windows DNS server. Whenever I attempt to send a DNS query for management.local via the corporate.local DNS server, the query fails and the Windows DNS server event log gets entries for Event ID 5504: "The DNS server encountered an invalid domain name in a packet from 10.0.10.1. The packet will be rejected. The event data contains the DNS packet." Doing a query for corporate.local via the management.local DNS server works fine.
Are there some settings I'm missing? I've tried Googling for similar issues but haven't found anyone with something similar.
-
@kwaleeb said in Conditional forwarder pointed to pfSense causes Error 5504:
The DNS server encountered an invalid domain name in a packet from 192.168.121.1
How is 192.168.1.1 ?
It's asking who do resolver ?
What was the " invalid domain name" ?Note that an " invalid domain name" should return a fail, so is there actually a problem ?
-
Sorry, the IP was wrong in the error. It should've been 10.0.10.1.
I'm not sure, that's why I'm here asking. It says that the pfSense DNS server (unbound) is replying with invalid DNS packets, and I don't understand why. It happens on both Windows Server 2008R2 and 2016 DNS servers. The DNS entries, for example esxi.management.local, work on the 10.0.10.1 network itself, but any Windows DNS servers that have conditional forwarders pointed to the pfSense DNS server get errors.
I would just use IP addresses but some stuff (vSphere) requires DNS to be working.
-
Crank up the logging details on pfSense, and check the logs. You'll be able to see what it receives for resolving.
-
It was the "Access Lists" tab, I didn't know you had to allow networks outside of directly attached ones. Everything works now.
Thanks!
-
@kwaleeb Thanks, this helped me as well with Server 2012 R2 and PfSense DNS Resolver
-
@kwaleeb said in Conditional forwarder pointed to pfSense causes Error 5504:
It was the "Access Lists" tab,
That list, the "Access Lists" is only used when you check :
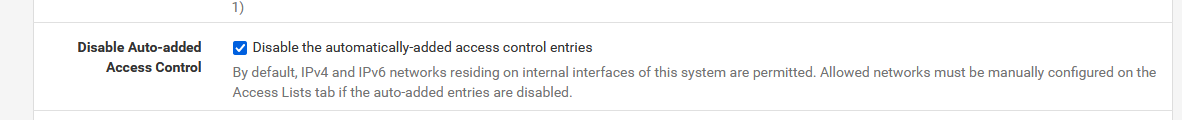
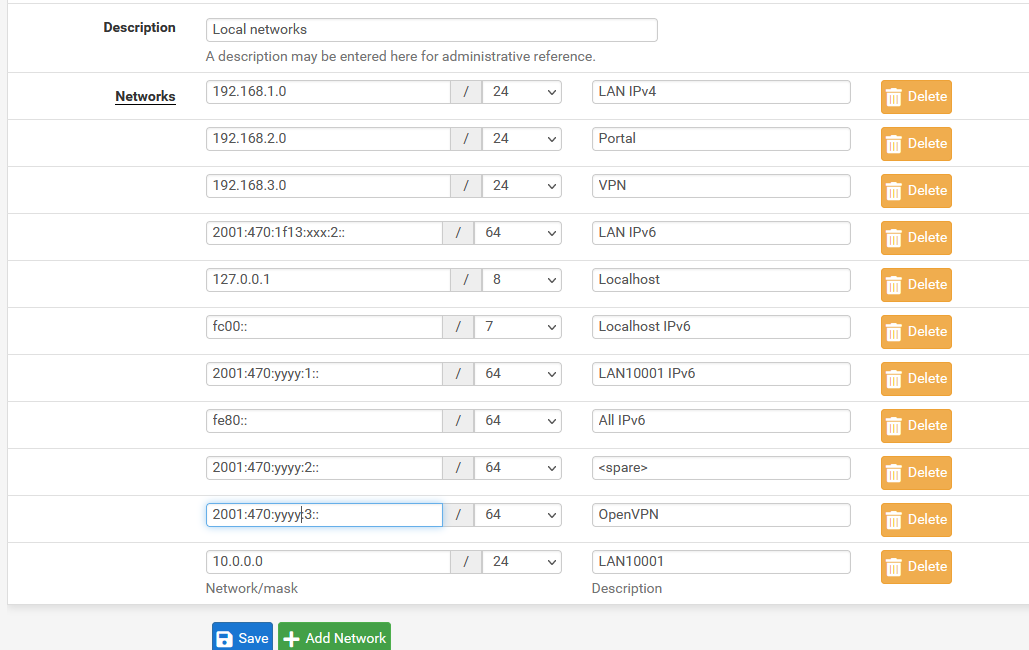
I've checked that "Disable Auto-added Access Control" so I have to populate the list myself :
Normally, the default is :
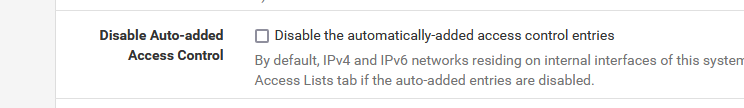
will do just fine, as all 'known' interfaces will get included :
By default, IPv4 and IPv6 networks residing on internal interfaces of this system are permitted.
If you have other networks, and these aren't known to pfSense (unbound), you have to use the Access Lists tab.
For IPv4 stuff, this isn't really hard.
Things gets a bit more complicated if you have a double stack (IPv4 and IPv6) - see my image.