NordVPN Setup
-
I have followed the instructions from this site https://nordvpn.com/tutorials/pfsense/pfsense-openvpn/ to setup NORDVPN on my new firewall.
I got to the editing firewall rules for the lan where you edit the ipv4 rule to change the gateway to NordVPN. That gateway did not show in the listing for that rule.
I must have missed something, but don't see where. Any ideas?
-
@amarcino said in NordVPN Setup:
I must have missed something
You missed something.
We missed all of it.Show (images ! ) what you did please.
-
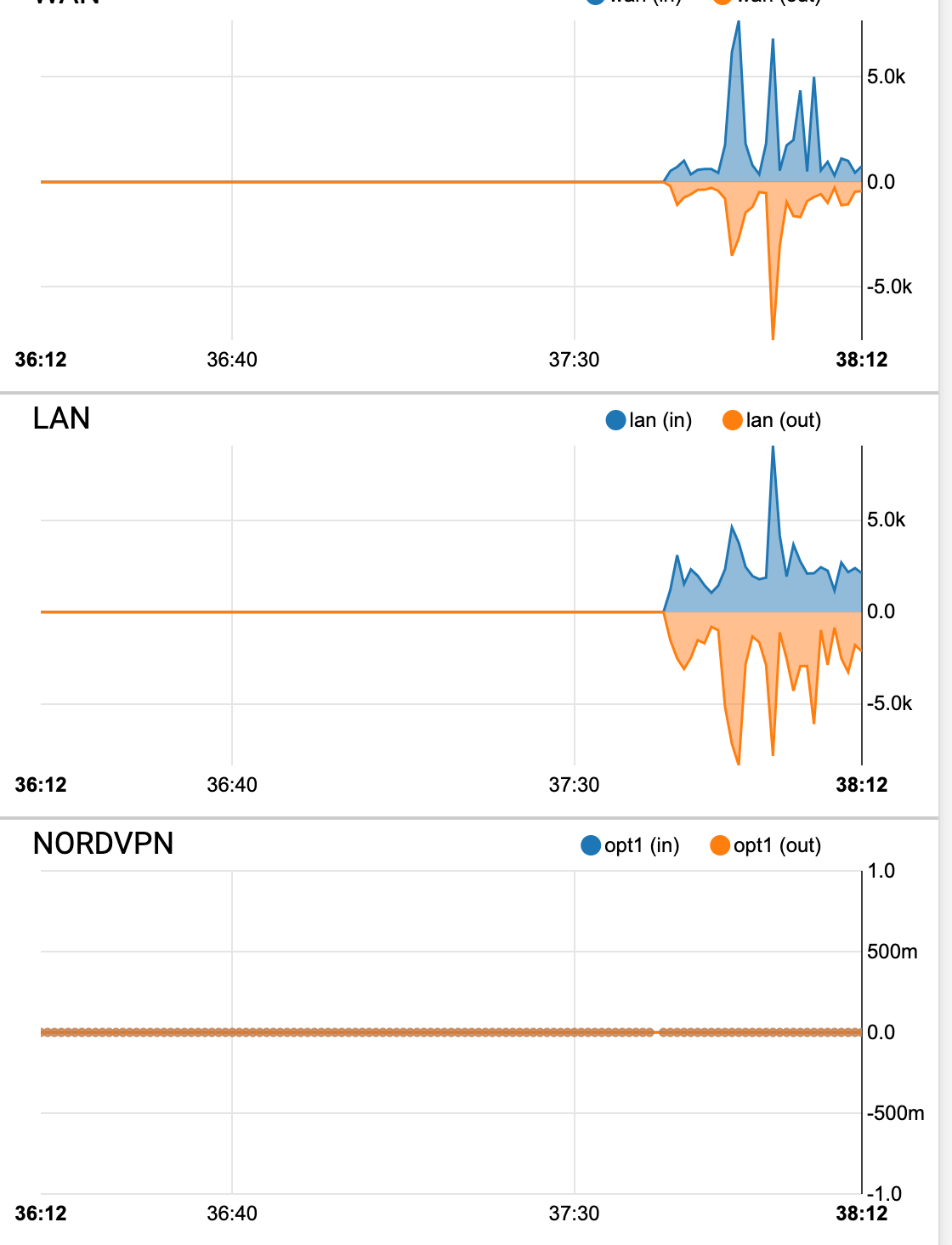
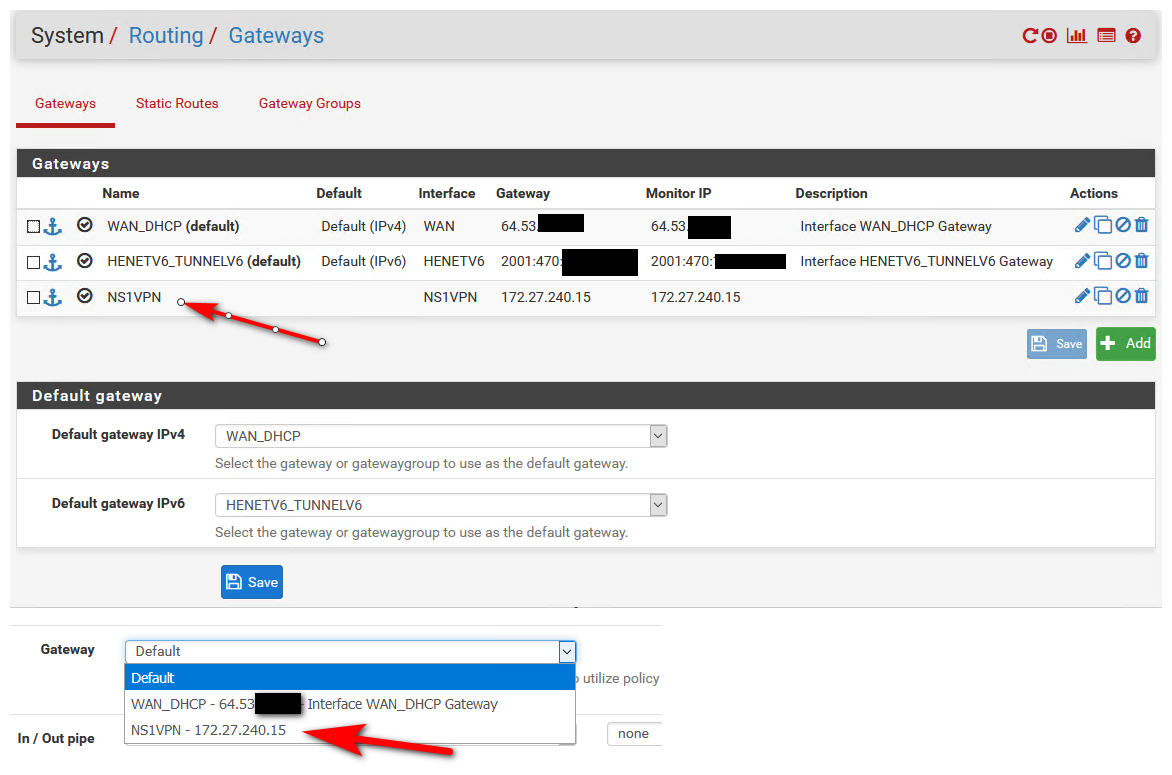
Shows the service up:
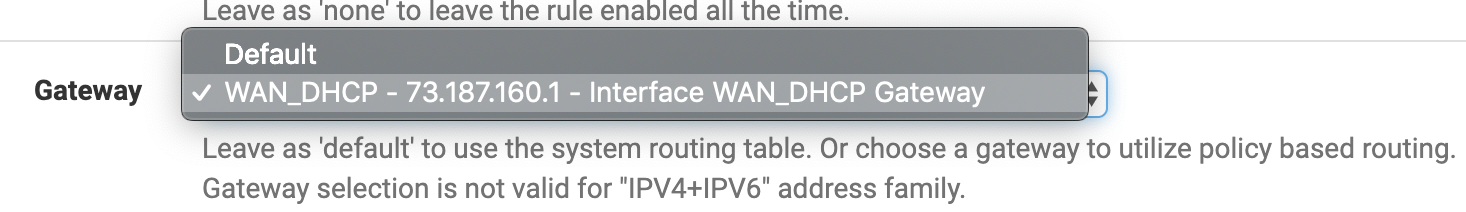
This is where I should be able to see the NordVPN gateway to select

No traffic going through the NordVPN interface
-
Those instructions are just horrible!
If they are not going to provide you a client cert, and have you set username and password for auth then the client cert should be set to NONE (use username password). Not left on the default web gui server cert.
And you shouldn't be pulling routes, if your going to policy route by placing the gateway on your rule.
What is the point of dnssec key prefetch being checked, if they have you uncheck use dnssec because your forwarding which is fine.. But then you don't need the prefetch either.
And you shouldn't be using manual outbound nats, you should just be using hybrid and adding the rule for your vpn interface.
Those are just the ones I spotted in my 20k foot breeze over..
Are we sure this is just not some spam wanting to have a like to have a link to that vpn server for seo purposes?
edit: you on the correct rule, it would not allow you to pick a ipv4 gateway if the rule includes IPv6.. Do you see the gateway listed in your gateways user routing?
-
I am a newbe with this device, where do i find the gateways user routing?
Is there documentation for this setup written by netgate/pfsense?
-
In the system menu item that says routing.
And again what rule are you trying to put the gateway on? If the rule is both ipv4 and ipv6 rule?
Also if your going to put default route from the vpn service, this is little point to create a policy route. How would pfsense/netgate create a guide for vpn service X.. They could have it setup multiple different ways.
There are many guides here on the forums by users of vpn service X..
-
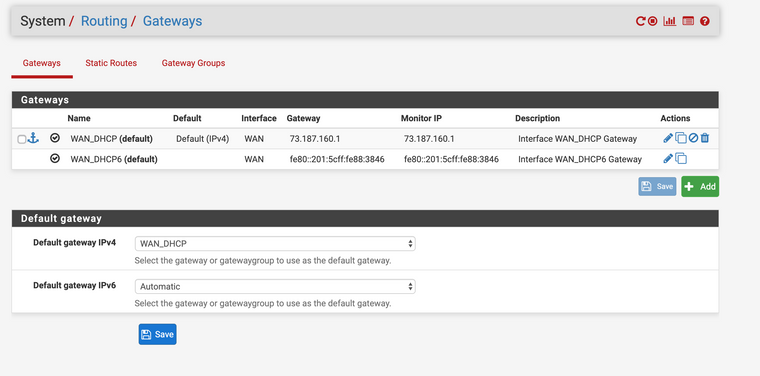
Here are my gateways.
I am trying to get this last part done.
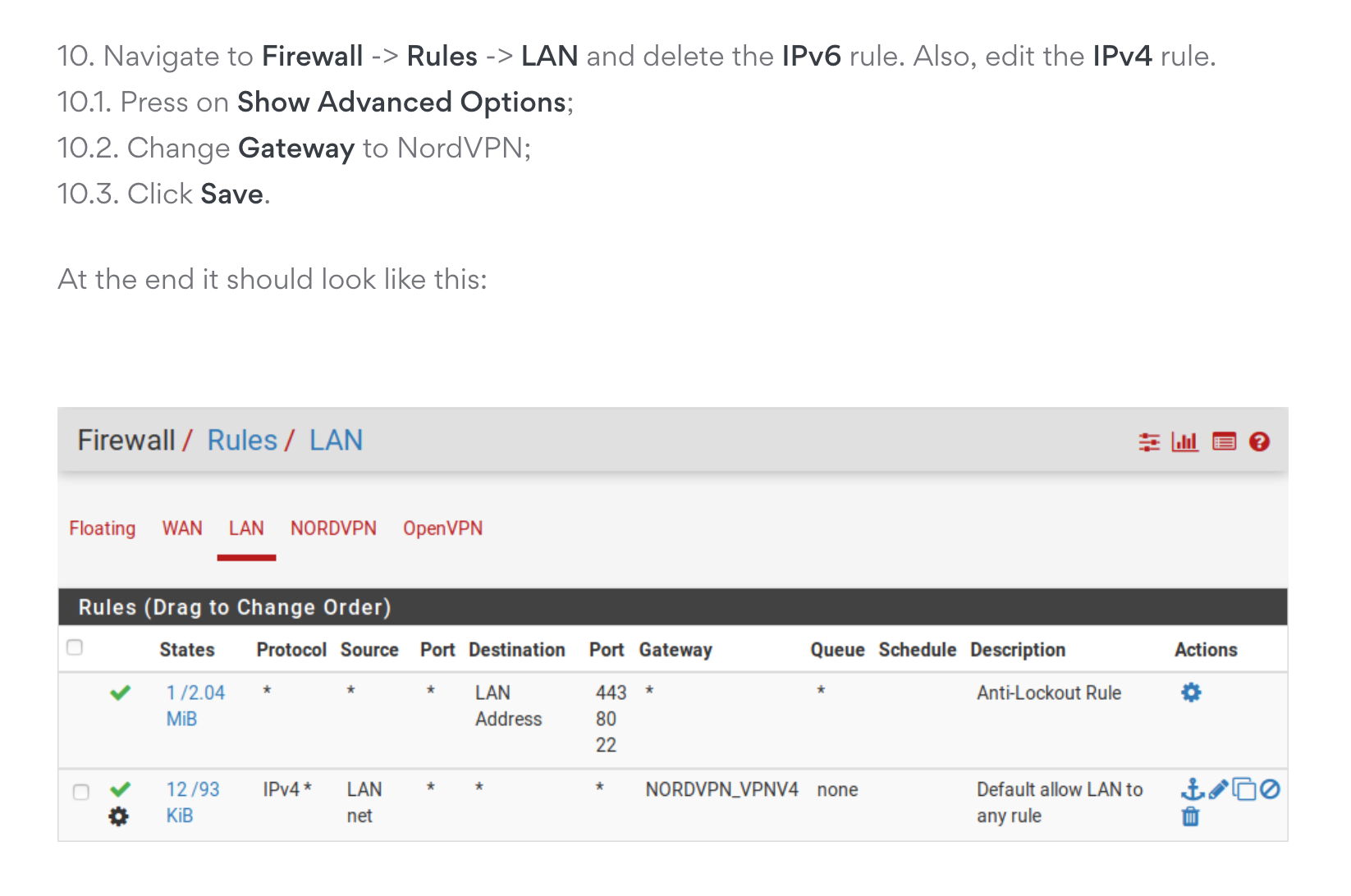
I am going to review forums for the guides you say are here.
-
You have not gateway - so why would you think it would be listed as a dropdown.
For example.. Here is gateway to a vps I run openvpn on.
What I would suggest is watch the hangout of using vpn as wan connection
https://www.youtube.com/watch?v=lp3mtR4j3Lw -
OP you missed the interface part. you either don't have it enabled or you missed that part entirely
-
To be honest if you need to follow a "guide" your prob not to a point where you should be doing this anyway ;)
You should be able to take the information provided for example in the hangout and apply that info to any vpn service with the details of the connection they provide.
If your hoping to follow some bouncing ball, click here, then there without a clue to what any of it does.. Its destined to fail before you get started, and that would be if the guides the vpn service provided were actually valid info to begin with..
They make a point of pointing out that the number your self signed web gui that is the default and would be top in the cert manager, etc. and only reason its listed there will be different. When clearly your not going to be using that cert - and if your going to auth with username and password that selection should be NONE..
So that tells me the person putting that guide together doesn't understand how this is suppose to work either..
A guide is fine for running through to make sure you didn't forget a step, etc. More like a checklist vs a guide.. But I can tell you from 15 second breeze through of that guide is its just junk.
-
Yes thanks. I really used the guide as a checklist to make sure I didn't forget anything, I understood that the certs, usernames and passwords had to comply with the server I chose, and my login credentials for Nord. I went through these steps about three times and could not see where I missed anything, and I could not understand how in the guide the NordVPN gateway could be selected when it wasn't configured.
Anyhow I backtracked, deleted my client, and certificates, and rules and started over using a youtube video by Lawrence systems on setting up a client vpn with pfsense.
I am happy to say that the setup is working now. All of my traffic is being routed through NordVPN, and I must say, his instructions were a lot simpler, with a number of things that were not necessary to do compared to the Nord Instructions.
Thanks again for the assistance and prodding me to look at another more elegant solution.
-
A shitty guide is a sign of a company you don't want to be doing business with... Stupid nonsense in there, turning off unbound from answer version query... WTF??? Only thing that would be able to do that query would be stuff on your network anyway.. What you don't want something to be able to query what version your unbound is?
$ dig @192.168.9.253 version.bind txt chaos ; <<>> DiG 9.14.3 <<>> @192.168.9.253 version.bind txt chaos ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 17406 ;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 4096 ;; QUESTION SECTION: ;version.bind. CH TXT ;; ANSWER SECTION: version.bind. 0 CH TXT "unbound 1.9.1" ;; Query time: 1 msec ;; SERVER: 192.168.9.253#53(192.168.9.253) ;; WHEN: Tue Jul 23 14:28:43 Central Daylight Time 2019 ;; MSG SIZE rcvd: 67Has ZERO!!!! to do with setting up your pfsense to login into their vpn server - ZERO!!!
-
When I am stuck with them for another 2 years. LOL
As you noted, there is a lot of things in there, that configuration wise, should not be. I did not know all of the parameters they needed defined to create a connection. So I had little choice to use what they published.
If you know of a better VPN provider let me know.
-
@amarcino said in NordVPN Setup:
If you know of a better VPN provider let me know.
I do - its the vps you fire up and run yourself ;) You can get a vps for like $15 a year that can provide vpn services to hide your p0rn traffic from the man ;)
If you want my advice - I would re-evaluate the need for vpn in the first place.. I just don't see any use for them in hiding traffic from my isp.. Pretty much all of the traffic these days is inside a https tunnel anyway.. Tracking and fingerprinting vpn doesn't nothing for..
If you want to hide your p2p traffic from your isp, its much cheaper and BETTER to just get a seedbox in some country that is ok with it..
But if what your after is to slow down your connection because your service is too fast from your ISP for what your paying them, and you want to spend more money and get less speed... Then sure pick any old vpn service, that can not even correctly put together instructions on how to connect to them ;) They must be good, they say so right on their website.. And they all state they do not log any of your traffic.. They provide you with gigs and gigs of bandwidth for that price of 29$ for 2 years... No need to sell your info for other ways to actually make a profit, because you know bandwidth and location of services all over the globe are free to run... That fee you paid up front will for sure provide them with all the profit they could want ;)
-
I may go your first route, after my daughters marriage and move. I was thinking of setting up my own VPS between her home and mine, as one of the packages I use is Plex, so she can have access to it in a more secure mode.
I originally got Nord, because wanted to keep my torrent activity hidden from my ISP. I was running this for the past two years on my synology device for just that purpose. Especially after they sent me a statement in the mail about a OS package I downloaded.
I will look into tunneling that traffic only through the VPN and have everything else sent outside the tunnel.
The loss of speed is less important to me then my privacy concerns.
-
If you want to hide your p2p traffic from isp, so any dcma goes to the vpn service vs your isp - sure they are good for that.. But just policy route that traffic out the vpn, not ALL your traffic... They are also good for circumvention of geo restrictions.. To privacy concerns - not so much ;)
Going to be better to just seedbox to be honest ;) Especially if you want to serve up plex to friends or family. And want to use your upload pipe for that vs p2p..
VPS, virtual private server between her home and yours? You mean a vpn between the 2, sure site to site or even just her being a vpn client to your pfsense vpn server.. Sure that would work for plex access.
Or you could much easier just create firewall rule that only allows her IP.. vs the public internet to access your plex.. I did it this way for a while... But now I just have plex behind cloudflare (for free).. I don't have it caching or anything - they have policies against that ;) But you can for sure leverage them as just reverse proxy.
-
This post is deleted! -
Thats no reason for a shitty guide to connect via pfSense, the information is just wrong in the guide.
It doesn't even mention "dont pull routes" forcing the pfSense default gateway to become the NordVPN gateway.
-
This post is deleted!