VLAN OVER VPN
-
@JKnott said in VLAN OVER VPN:
First off, I have no experience with TAP. My take on that is adding VLAN support to the TAP interface, as would be done on an Ethernet interface. Is that correct? Does TAP support bridging from a physical interface? If so, it should be transparent to VLAN tags.
Neither do I but yes, it's about adding VLAN support to TAP interface.
But I think it's OT here...
-
@max33 I'd like to clarify your request.
What do you need?:- translate VLAN id to client-side network (i don't know the reason)
- just need to access to devices behind VPN tunnel from your client device
If 2nd - just give access on VPNserver settings page. You don't need to translate VLAN IDs to tunnel.
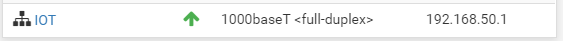
Take a look this:
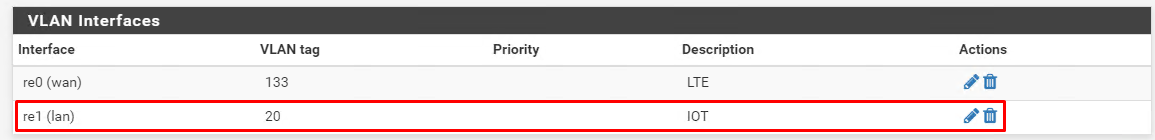
OpenVPN server settings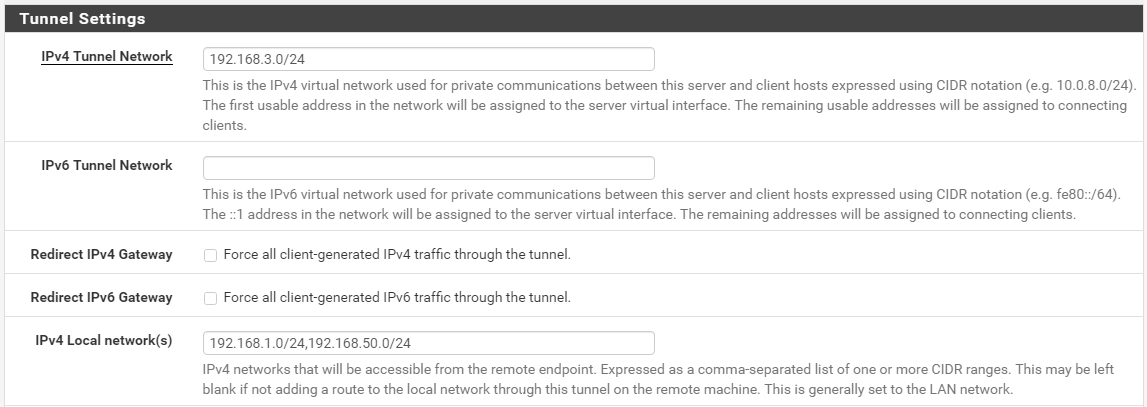
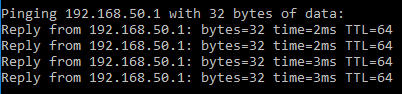
As a result VPN client doesn't even know about tags, vlans etc.
ping from VPN client to VLAN20 gateway (packets between VPN client and VPN server are untagged)
-
Is VLAN over VPN even necessary? VLANs are normally different IP address ranges. Why not just route the traffic from the VLANs to the other end according to address? Similarly, the other end will then forward to the appropriate VLAN.
-
Thanks to all for taking time to respond
I think my question was not clear so i will try to explain : I just want to connect to my switch via vpn client.
I confirm that i correctly set my open vpn (the IVP4 local network range) but unable to reach web interface of the switch .
Currently schema is :
NIC 1 of PFSENSE connected to WAN
NIC 2 of PFSENSE connect to Switch Layer 2Two VLAN interface declared on PFSENSE NIC 2
VLAN 100 for TELEPHONY - 192.168.10.0/24
VLAN 200 for PC - 192.168.0.0/24Switch are on VLAN 200 (Management VLAN 200) on IP 192.168.0.253
PC are connected to Phone devices (YEALINK T46) and phone connected to Switch.
Phone Device tagged packet in order to manage VOIP traffic on VLANN 100 and PC traffic on VLAN 200
All works when i am on local network (connected to switch) but when i am outside in order to manage the network i implemented OPENVPN on pfsense and set the two network on IPV4 Local Network.
I got acces to web interface of phone but not on web interface of switch so i am asking myself if it could be due to vlan.
I will try to perform more test tonight and come back later.
-
Looking at that VLAN feature it sounds like it will be in the OpenVPN tap process - sort of like iroutes in the tun process. If it also integrates with, say, tagged VLANs on an OpenVPN assigned interface that would be...interesting.
All works when i am on local network (connected to switch)
I got acces to web interface of phone but not on web interface of switch so i am asking myself if it could be due to vlan.
Is the default gateway on the switch's management interface set properly?
-
@Derelict
I think this answers that question:
https://github.com/OpenVPN/openvpn/pull/76#issuecomment-493688410 -
Yeah. that would be interesting.
-
One question, what's at the other end of the VPN? With a TAP VPN, the network will have to be in the same subnet as this end.
-
HI
Thanks a lot Derelict you got the point , the issue was coming from wrong gateway setting on the switch.
A stupid simple config......By the way thanks a lot to all people whose taking time to respond....
Have a good day all............
-
@max33 great! have a nice day)